Phishing, Insecure Configuration, XSS, Cross Site Scripting, www.discoverbing.com/Activities/SocialSearch, CWE-79, CAPEC-86, DORK, GHDBReported to MSRC on April 25, 2011 and reported as Resolved on November 11, 2011 | 11260njLoading
Netsparker - Scan Report Summary
|
||||||||||
|
Total Requests1Average Speed1 req/sec. |
3
identified
1
confirmed
0
critical
1
informational
|
||||||||
SCAN SETTINGSScan Settings
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
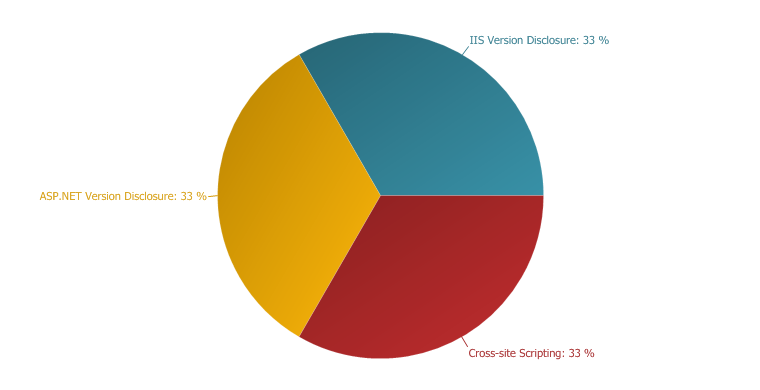 |
IMPORTANT
33 %
LOW
33 %
INFORMATION
33 %
|
|
VULNERABILITY SUMMARYVulnerability Summary
|
||||||||||||||||||
|
||||||||||||||||||
Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
|
- /Activities/SocialSearch
/Activities/SocialSearch CONFIRMED |
Parameters
| Parameter | Type | Value |
| Query Based | QUERYSTRING | "><script>alert(9)</script> |
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Cache-Control: no-cache
Host: www.discoverbing.com
Cookie: ASP.NET_SessionId=10jefv55zgvtlf45j54xiave
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-cache, no-store
Pragma: no-cache
Content-Type: text/html; charset=utf-8
Expires: -1
Server: Microsoft-IIS/7.0
X-AspNet-Version: 2.0.50727
X-Powered-By: ASP.NET
Date: Sat, 23 Apr 2011 14:42:01 GMT
Content-Length: 21887
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html lang="en" xml:lang="en" xmlns="http://www.w3.org/1999/xhtml">
<head>
<title>Bing "Likes" Facebook - Discover Bing</title>
<meta name="keywords" content="bing, facebook, social, search, share" />
<meta name="description" content="Find out how Bing can help you find information you need and then share it with whom you want!" />
<!--to set the facebook opengraph/sharer thumb-->
<meta property="og:image" content="http://az10143.vo.msecnd.net/sitecore/dbing/media/Images/bing_logo_fb.png?x=8" />
<meta name="HandheldFriendly" content="true" />
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
<meta name="CODE_LANGUAGE" content="C#" />
<meta name="vs_defaultClientScript" content="JavaScript" />
<meta name="vs_targetSchema" content="http://schemas.microsoft.com/intellisense/ie5" />
<link rel="shortcut icon" href="https://cdndiscoverbing.blob.core.windows.net/sitecore/favicon.ico" />
<link rel="icon" href="https://cdndiscoverbing.blob.core.windows.net/sitecore/favicon.ico" />
<script type="text/javascript" src="http://ajax.microsoft.com/ajax/jquery/jquery-1.4.2.min.js"></script>
<script type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/Scripts/socialsearch.js"></script>
<script type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/Scripts/searchbox.js"></script>
<script type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/Scripts/analytics.js"></script>
<script type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/Scripts/unsupported.js"></script>
<link rel="stylesheet" href="http://az10143.vo.msecnd.net/sitecore/dbing/css/default.css"/>
<link rel="stylesheet" href="http://az10143.vo.msecnd.net/sitecore/dbing/css/VisitorIdentification.css"/>
<link rel="stylesheet" href="http://az10143.vo.msecnd.net/sitecore/dbing/css/styles.css"/>
<link rel="stylesheet" href="http://az10143.vo.msecnd.net/sitecore/dbing/css/searchbox.css"/>
<!--[if lte IE 6]>
<script type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/Scripts/ie6.js"></script>
<![endif]-->
<!--to set the facebook opengraph/sharer thumb - it appears that it's necessary that these live below the meta description in order for FB to pull the correct description -->
<meta property="og:title" content="Look what I discovered on Bing." />
<meta property="og:type" content="website" />
<meta property="og:url" content="http://www.discoverbing.com" />
<meta property="og:image" content="http://az10143.vo.msecnd.net/sitecore/dbing/media/Images/bing_logo_fb.png" />
<meta property="og:site_name" content="Discover Bing" />
</head>
<body class="activity">
<div id="page">
<script type="text/javascript">
function searchFocus() {
if (jQuery('#bingSearch').attr('value') == 'Bing and decide') {
jQuery('#bingSearch').css('color', '#333');
jQuery('#bingSearch').val('');
jQuery('#bingSearch').onfocus = function () { };
}
}
jQuery(document).ready(function () {
jQuery('#bingSearch').css('color', '#D0D0D0');
});
</script>
<div class="header" style="z-index: 5000;">
<div id="search-box">
<div id="searchmodule">
<a href="#" class="share">Share this page</a>
<div id="shareslide">
<ul>
<li class="title">Share this page</li>
<li id="global-nav-share-facebook" class="fb" style="position: relative;">
<iframe scrolling="no" frameborder="0" allowtransparency="true" style="border: medium none;
overflow: hidden; width: 90px; height: 21px;" src="http://www.facebook.com/plugins/like.php?href=http%3A//www.discoverbing.com/%23fbid%3D4MpDs9R4xdg%26wom%3Dtrue&layout=button_count&show_faces=true&width=90&action=like&colorscheme=light&height=21">
</iframe>
</li>
<li><a id="global-nav-share-facebookshare" href="http://www.facebook.com/sharer.php?u=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>&fbshare=true&t=Look+what+I+discovered+on+Bing"
target="_blank">Facebook</a></li>
<li><a id="global-nav-share-twitter" target="_blank" href="http://twitter.com/home?status=Look+what+I+discovered+on+Bing+@bing+http://bit.ly/ifR5hh">
Twitter</a></li>
<li><a id="global-nav-share-email" href="mailto:?subject=Look%20what%20I%20discovered%20on%20Bing&body=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>">
E-mail</a></li>
<li><a id="global-nav-share-stumbleupon" target="_blank" href="http://www.stumbleupon.com/submit?url=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>&title=Look+what+I+discovered+on+Bing">
StumbleUpon</a></li>
<li><a id="global-nav-share-delicious" target="_blank" href="http://del.icio.us/post?url=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>%23fbid%3D4MpDs9R4xdg%26wom%3Dtrue%26title=Look+what+I+discovered+on+Bing">
Delicious</a></li>
<li><a id="global-nav-share-digg" target="_blank" href="http://digg.com/submit?phase=2%26url=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>%23fbid%3D4MpDs9R4xdg%26wom%3Dtrue%26title=Look+what+I+discovered+on+Bing">
Digg</a></li>
<li><a id="global-nav-share-reddit" target="_blank" href="http://www.reddit.com/submit?url=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>%23fbid%3D4MpDs9R4xdg%26wom%3Dtrue%26title=Look+what+I+discovered+on+Bing">
Reddit</a></li></ul>
</div>
<div id="searcher">
<div class="input-container">
<input type="text" name="search" class="text" id="bingSearch" onkeypress="searchKeyPress(event);"
value="Bing and decide" onfocus="searchFocus();" />
<input type="submit" id="submit" onclick="submitBing();">
</div>
</div>
<div class="makelinks">
Make Bing your: <a href="/get/set-bing-as-your-default-browser-search-1/index.html"
target="_blank">Search</a> | <a href="http://www.discoverbing.com/get/set-bing-as-your-homepage-1/" target="_blank">
Homepage</a> | <a href="/mobile/" target="_blank">Mobile app</a>
</div>
</div>
</div>
<!-- #searchbox -->
<!-- #search-box -->
<a href="/">
<h1 class="logo">
Discover Bing</h1>
</a>
<div class="tab-nav">
<ul>
<li><a href="/DidYouKnow" >
Did You Know?</a></li>
<li><a href="/Features/Entertainment/Games" class="active">
Explore Bing</a></li>
<li><a href="/GetBing" >
Get Bing</a></li>
<li><a href="/BingRewards" >
Bing Rewards</a></li>
<li><a href="/BingGives" >
Bing Gives</a></li>
</ul>
</div>
<!-- #tab-nav -->
</div>
<!-- #header -->
<div id="hero">
<div class="feature" style="background: #fff url('http://az10143.vo.msecnd.net/sitecore/dbing/media/Images/features/features_Social.jpg') top right no-repeat;">
<div class="info">
<h4></h4>
<p></p>
<a class="cta" href="" style="display:none ;"></a>
</div>
</div>
<!-- .feature.possum -->
</div>
<!-- #hero -->
<div id="content">
<h2>
<div class="share">
Spread the word <a href="http://twitter.com/home?status=+@bing+http://bit.ly/ifR5hh%23fbid%3DyOhyqtH41mn%26wom%3Dfalse" class="twitter" target="_blank"> </a><a href="http://www.facebook.com/sharer.php?u=http://www.discoverbing.com/Activities/SocialSearch?"><script>netsparker(9)</script>/&fbshare=true&t=" class="fb" target="_blank"> </a>
</div>
<!-- .share -->
Check out Bing <small>By <a href="/Features/Entertainment/Games">Feature</a> or Activity</small>
</h2>
<div class="left">
<ul id="main-nav">
<li><a href="/Activities/BeEntertained" >What? Bored Again?<small>Be entertained.</small></a></li>
<li><a href="/Activities/MakeLocalPlans" >Make Local Plans<small>Plan a night out.</small></a></li>
<li><a href="/Activities/BePrepared" >Start Your Day<small>Be prepared.</small></a></li>
<li><a href="/Activities/BeHealthy" >Be Healthy<small>Know more. Feel better.</small></a></li>
<li><a href="/Activities/FindFlights" >Plan a Beach Holiday<small>Find flight deals.</small></a></li>
<li><a href="/Activities/SocialSearch" class = active>Bing "Likes" Facebook<small>Social Search</small></a></li>
</ul>
</div>
<div class="right">
<script language="javascript" type='text/javascript' src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/silverlight.js"></script>
<script language="javascript" type='text/javascript' src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/wmvplayer.js"></script>
<script language="javascript" type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/tools.js"></script>
<script language="javascript" type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/xaml.js"></script>
<script language="javascript" type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/jwplayer.js"></script>
<script language="javascript" type="text/javascript" src="http://az10143.vo.msecnd.net/sitecore/dbing/videoPlayer/flashver.js"></script>
<div class="feature">
<div class="intro">
<h3>
Bing "likes" Facebook</h3>
<p>
Bing has connected with Facebook to make searching on Bing more social. Together, Bing and Facebook offer you better search results—and a more personalized experience with a little help from your Facebook friends. Your friends introduce you to new music, restaurants, movies and more. Now Bing helps you discover what they have "liked" and shared on the web.
</p>
<p><span style="margin-right: 30px;"><a href="http://www.bing.com/social/?FORM=MFEHPG&PUBL=DBING&CREA=SC_MFEHPG__15620110215-1_SearchMoreSocial_1x1" class="cta" target="_blank" onclick="trackitAuto('event54', 'e', 'UserEd:en-US:Dbing:/Home/Activities/SocialSearch/Feature:Feature', 'Activities', 'SocialSearch', 'Feature', 'Feature');">Bring your friends: Search more social</a></span>
<a href="http://g.msn.com/1me10IE8enus01/114" class="cta" target="_blank" onclick="trackitAuto('event13', 'e', 'UserEd:en-US:Dbing:/Home/Activities/SocialSearch/Feature:Feature', 'Activities', 'SocialSearch', 'Feature', 'Feature');">Make Bing your default search</a>
</p>
</div>
<!-- .intro -->
<div class="video-player">
<div class="videoPlayer">
<div name="silverlight" id="silverlight" style="display: none;">
</div>
<div name="nonsilverlight" id="nonsilverlight" style="display: none;">
</div>
<div id="errorLocation"></div>
<script type="text/javascript">
//<![CDATA[
var isSafari = (jQuery.browser.safari && navigator.userAgent.toLowerCase().indexOf("chrome") === -1);
if (typeof isSafari == "undefined") isSafari = false;
var mediaSource = 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/facebook.mp4';
createSilverlight();
Silverlight.isInstalled(this);
var ieFlash = false;
try {
var obj = new ActiveXObject('ShockwaveFlash.ShockwaveFlash');
ieFlash = true;
}
catch (e) {
ieFlash = false;
}
if (mediaSource != '' && (((Silverlight.isInstalled() || navigator.plugins["Silverlight Plug-In"]) && !isSafari) || ((navigator.mimeTypes["application/x-shockwave-flash"] || ieFlash) && DetectFlashVer(8, 0, 0)))) {
//if (false) {
if ((Silverlight.isInstalled() || navigator.plugins["Silverlight Plug-In"]) && !isSafari) {
playSilverlight('silverlight', 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/facebook.mp4', 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/Thumbnails/Activity_SocialSearch_preview.png', '680', '400', false);
}
else {
playNonSilverlight('nonsilverlight', 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/facebook.mp4', 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/Thumbnails/Activity_SocialSearch_preview.png', '680', '400', false);
}
}
else {
showhide('nonsilverlight');
var imageSrc = 'http://az10143.vo.msecnd.net/sitecore/dbing/media/Videos/Thumbnails/Activity_SocialSearch_preview.png';
jQuery('#nonsilverlight').append("<img src=\"" + imageSrc + "\"/ width='680' height='400'>");
}
//]]>
</script>
</div>
</div>
<!-- .video-player -->
</div>
<!-- .feature -->
<div class="white-box">
<img alt="" class="greyborder" src="http://az10143.vo.msecnd.net/sitecore/dbing/media/Images/socialsearch/module1.jpg" /> <h3>Facebook profile search</h3><p>Find old friends or discover new ones through Facebook Profile Search on Bing. When you search for people ..
ASP.NET Version Disclosure
X-AspNet-Version banner of HTTP response or default ASP.NET error page.
Impact
Remedy
web.config file to prevent information leakage by using custom error pages and removing X-AspNet-Version from HTTP responses.
<System.Web>
< httpRuntime enableVersionHeader="false" />
<customErrors mode="On" defaultRedirect="~/error/GeneralError.aspx">
<error statusCode="403" redirect="~/error/Forbidden.aspx" />
<error statusCode="404" redirect="~/error/PageNotFound.aspx" />
<error statusCode="500" redirect="~/error/InternalError.aspx" />
</customErrors>
</System.Web>
Remedy References
|
- /Activities/SocialSearch
/Activities/SocialSearch |
Extracted Version
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Accept: netsparker/check
Cache-Control: no-cache
Host: www.discoverbing.com
Cookie: ASP.NET_SessionId=o04paa45fehuheqp0nv0s2qk
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-cache, no-store
Pragma: no-cache
Content-Length: 21656
Content-Type: text/html; charset=utf-8
Expires: -1
Server: Microsoft-IIS/7.0
X-AspNet-Version: 2.0.50727
X-Powered-By: ASP.NET
Date: Sat, 23 Apr 2011 14:41:36 GMT
IIS Version Disclosure
Impact
Remediation
SERVER header of its HTTP response.
|
- /Activities/SocialSearch
/Activities/SocialSearch |
Extracted Version
Request
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Accept: netsparker/check
Cache-Control: no-cache
Host: www.discoverbing.com
Cookie: ASP.NET_SessionId=o04paa45fehuheqp0nv0s2qk
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-cache, no-store
Pragma: no-cache
Content-Length: 21656
Content-Type: text/html; charset=utf-8
Expires: -1
Server: Microsoft-IIS/7.0
X-AspNet-Version: 2.0.50727
X-Powered-By: ASP.NET
Date: Sat, 23 Apr 2011 14:41:36 GMT